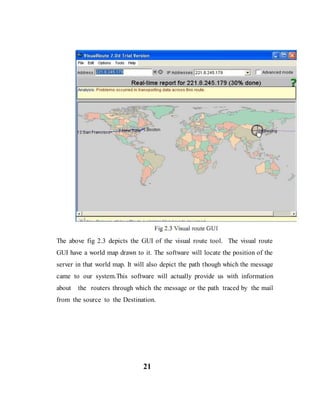
This document is a colloquium report on ethical hacking presented by Khushboo Aggarwal to the Department of Information Technology at ABES Engineering College in Ghaziabad, India in 2014-2015. The report provides an introduction to ethical hacking, describing what it is and its purpose. It discusses the different types of hackers, the methodology used in hacking, and some important ethical hacking tools. The report aims to increase understanding of ethical hacking and how systems can be better secured against vulnerabilities.