Embed presentation
Downloaded 101 times
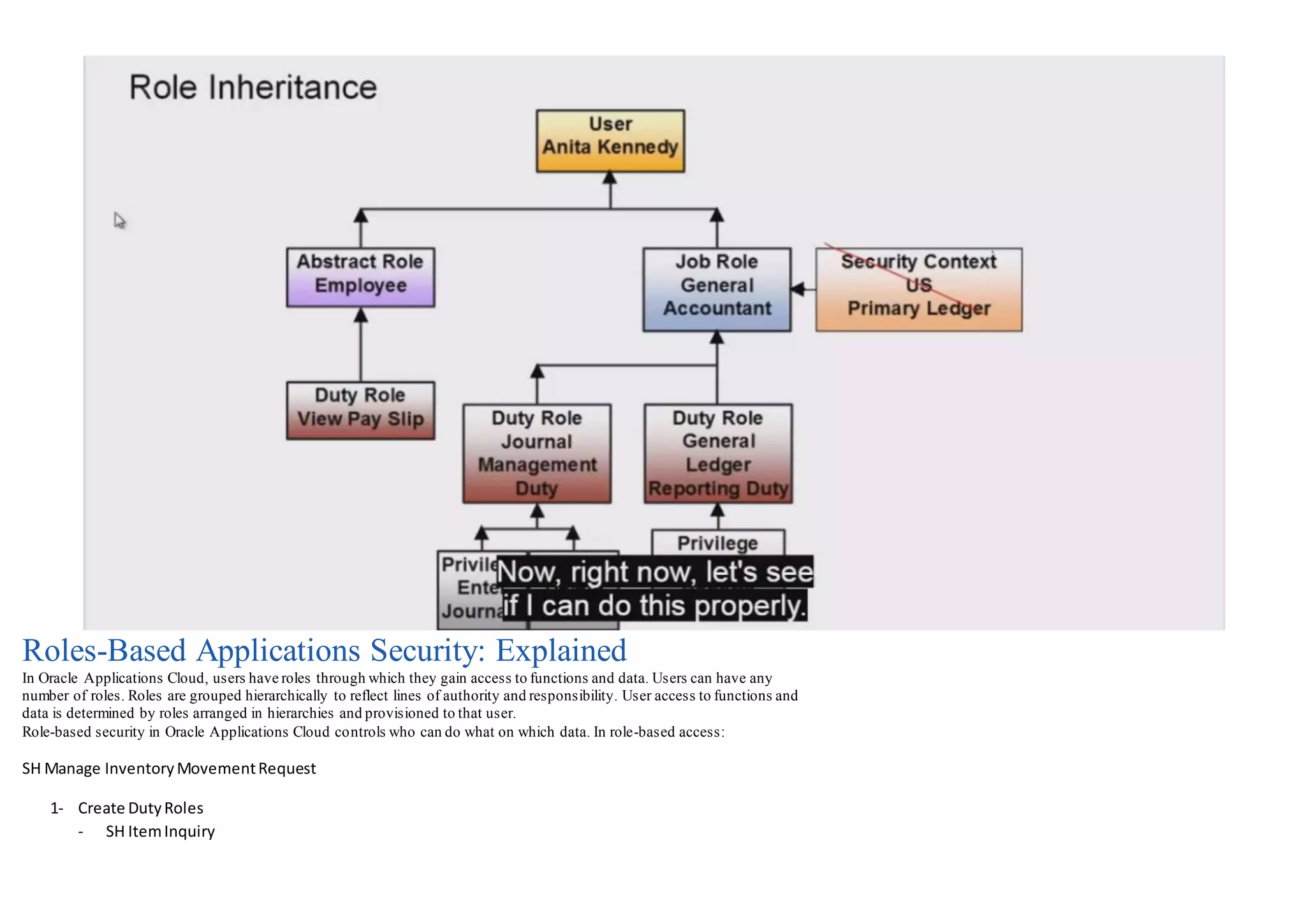

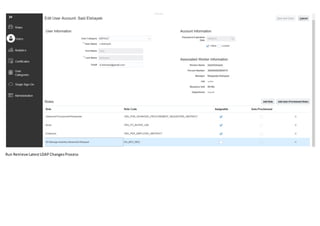
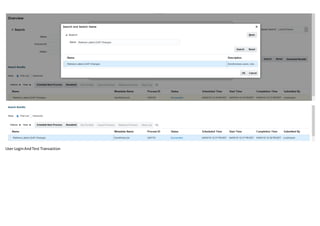
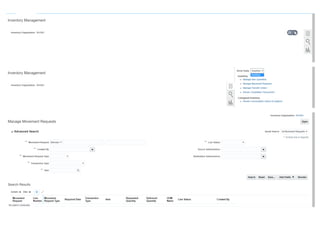


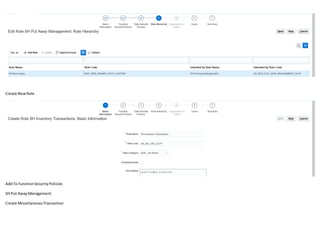

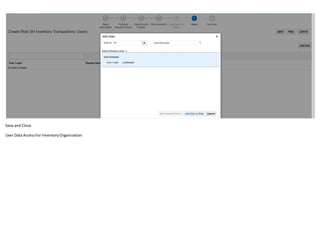
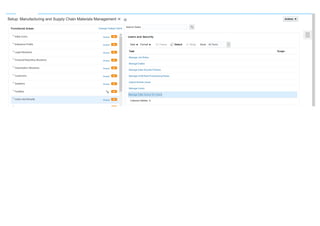
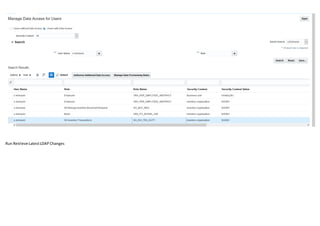

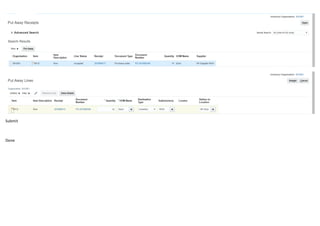

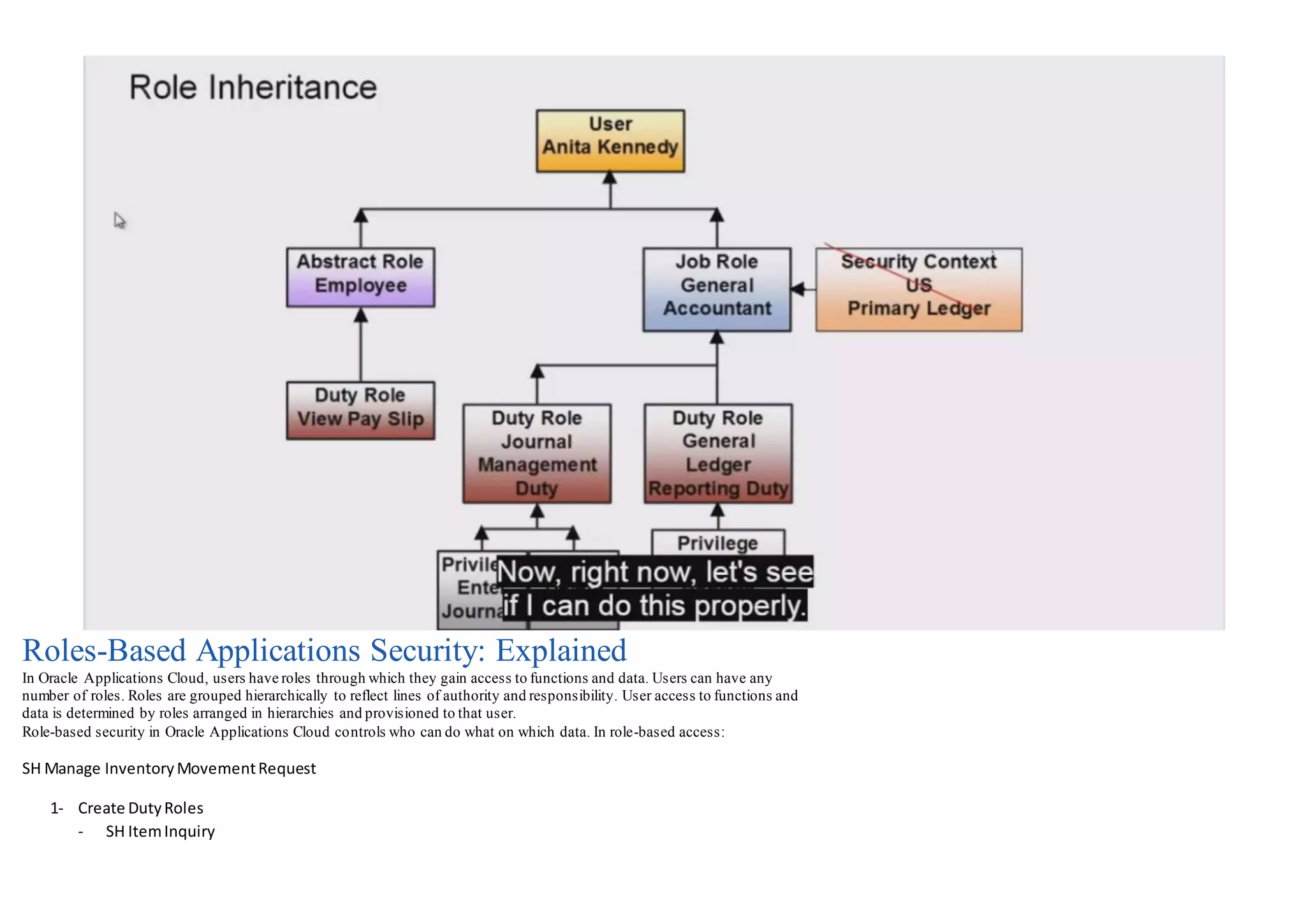
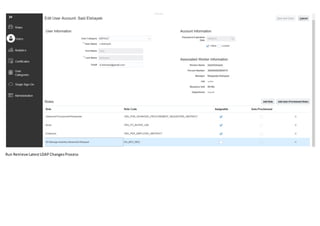
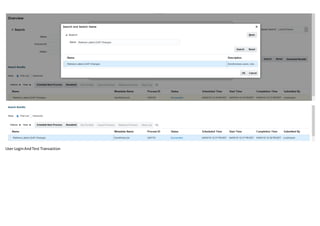
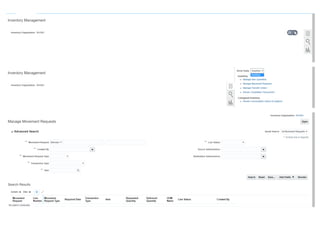
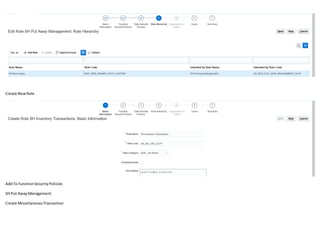
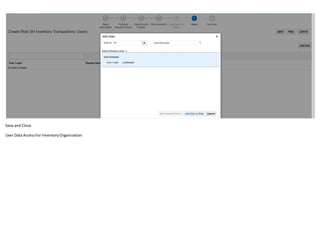
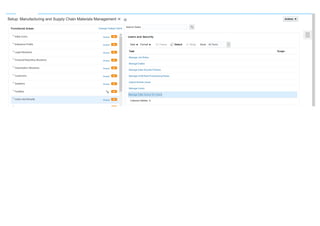
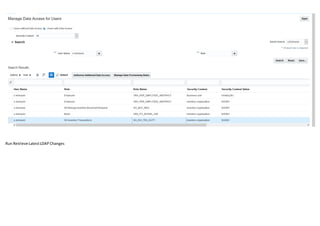
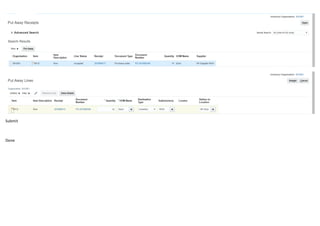
Roles determine user access to functions and data in Oracle Applications Cloud. Roles are arranged hierarchically to reflect lines of authority and responsibility. A user's access is defined by their roles in these hierarchies. Role-based security controls which users can access what data and functions. Roles group permissions and users are provisioned roles to allow access to only the appropriate data and functions.