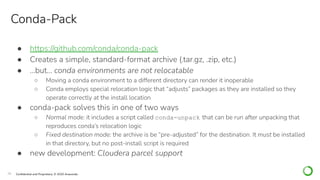
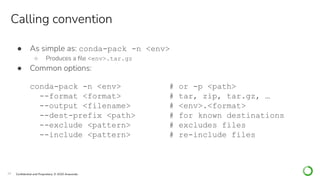
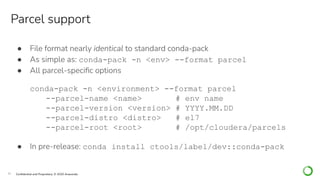
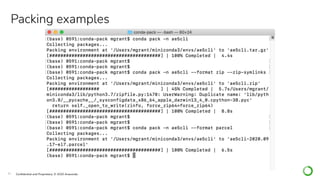
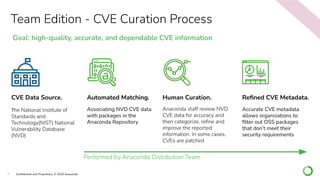
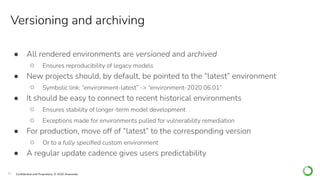
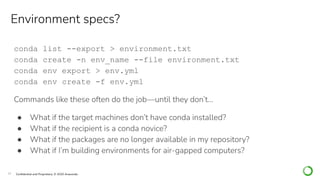
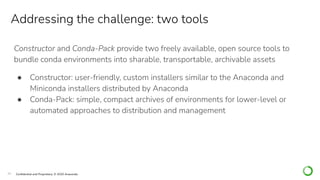
The document discusses Anaconda's tools for managing Python and R environments, focusing on the Conda package management system and Anaconda Team Edition. It highlights the importance of curated CVEs for security, environment standardization, and tools like Constructor and Conda-Pack for distributing customized environments. The document also details versioning, archiving practices, and distribution solutions for both standard and air-gapped systems.







![26 Confidential and Proprietary. © 2020 Anaconda
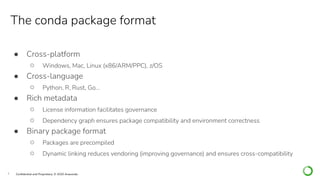
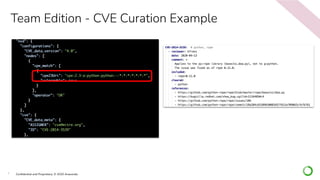
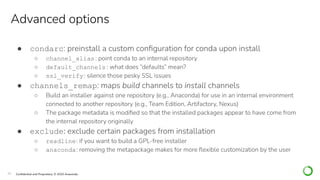
name: Sortaconda
version: 2020.10.01
installer_type: all
channels_remap:
- src: https://repo.anaconda.com/pkgs/main/
dst: https://repo.company.com/api/repo
- src: https://repo.anaconda.com/pkgs/msys2/ # [win]
dst: https://repo.company.com/api/repo/msys2/ # [win]
specs:
- python=3.6.10
- conda=4.8.4
- anaconda=2020.02
exclude:
- anaconda
condarc:
channel_alias: https://repo.company.com/api/re po
The construct.yaml file](https://image.slidesharecdn.com/webinar1-201202204308/85/Elevate-Your-Enterprise-Python-and-R-AI-ML-Software-Strategy-with-Anaconda-Team-Edition-26-320.jpg)