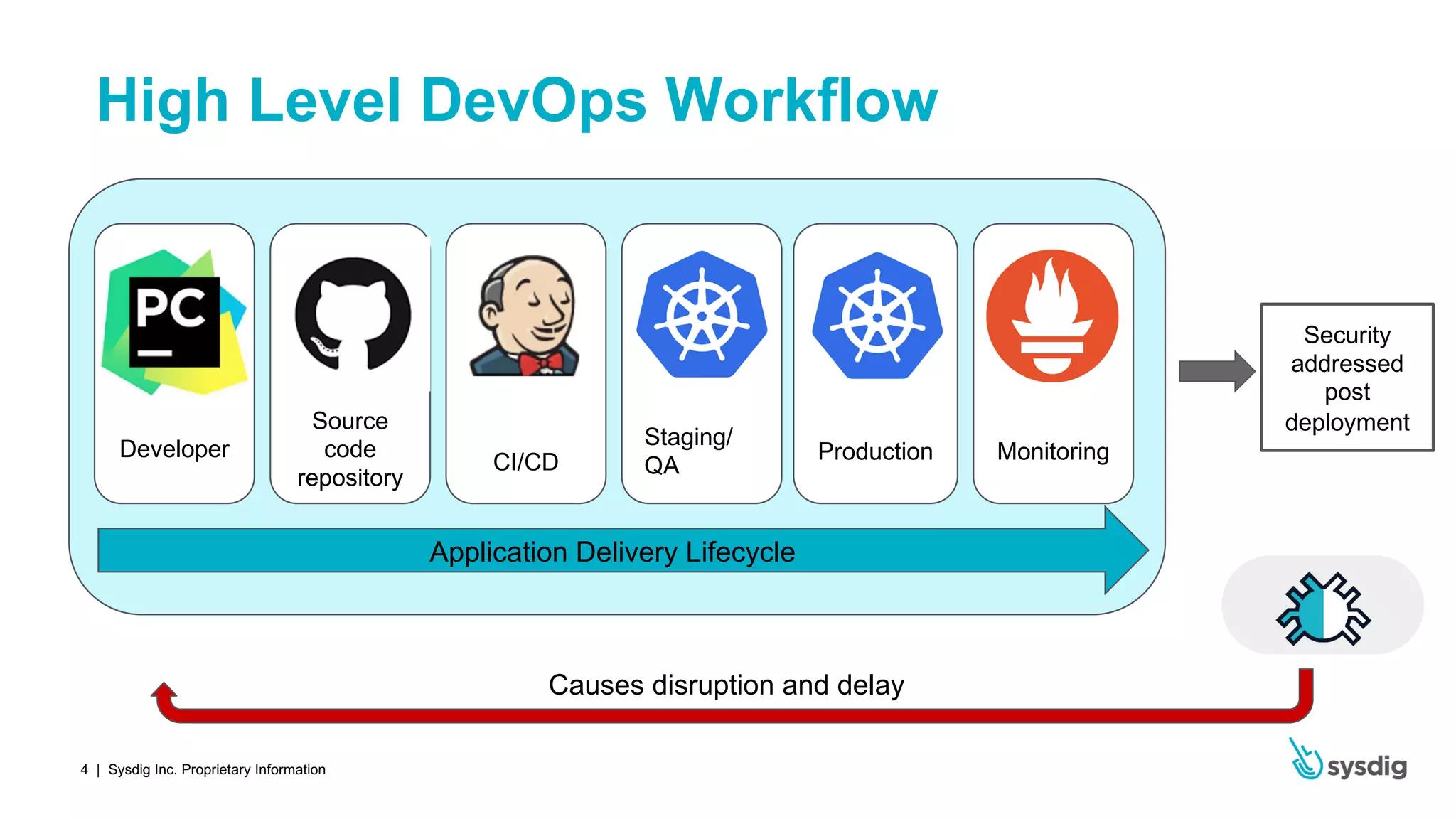
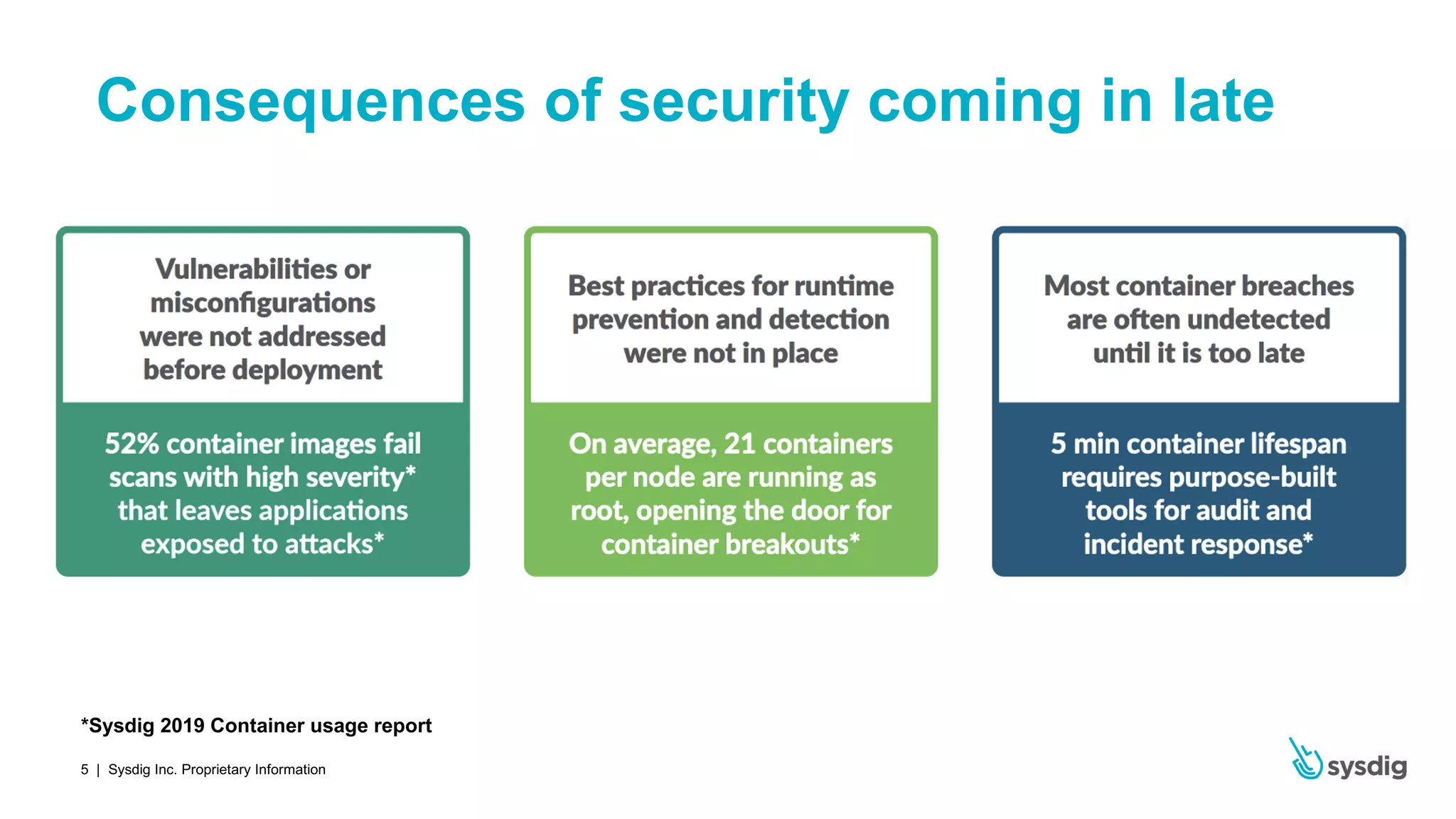
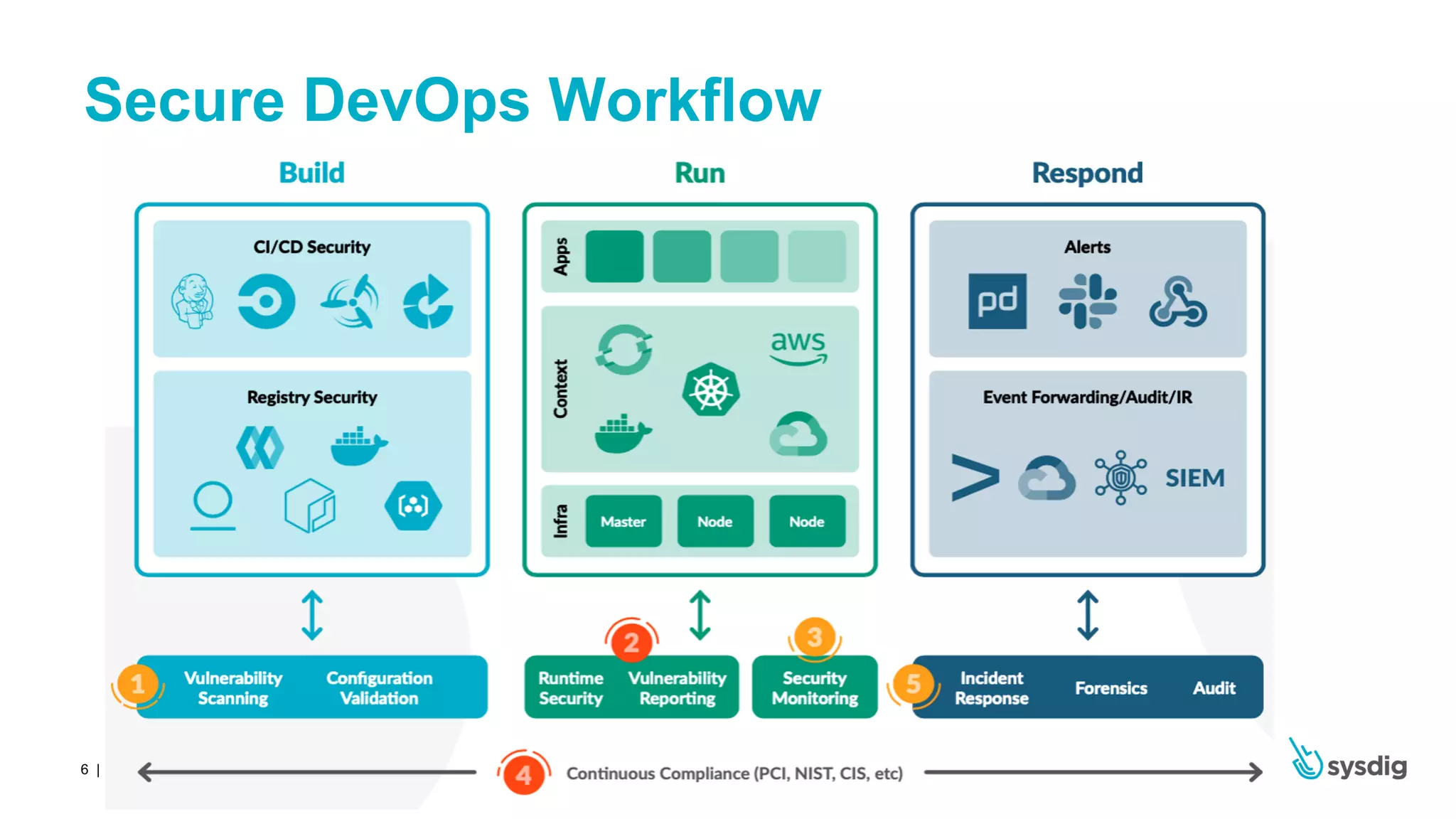
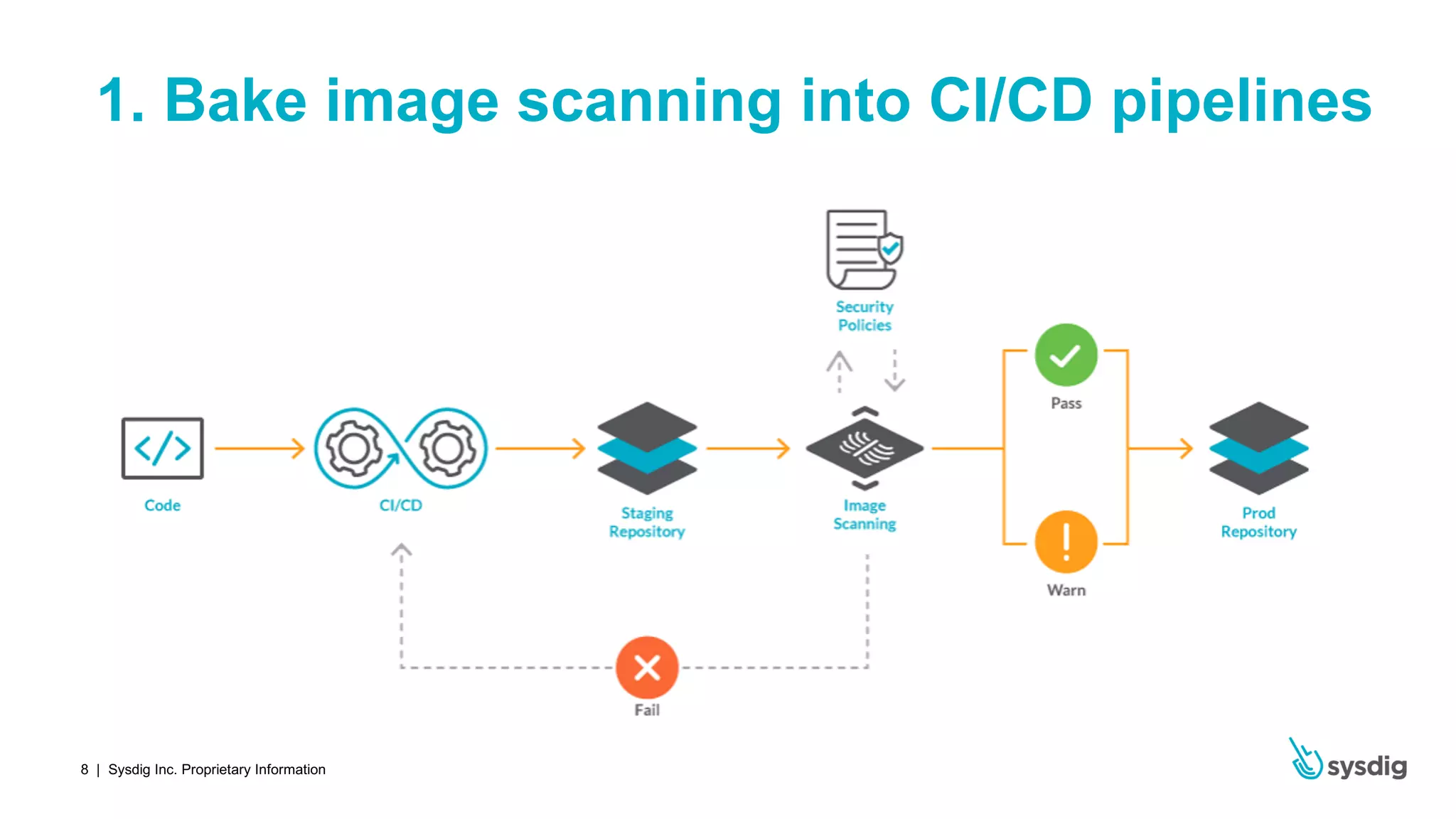
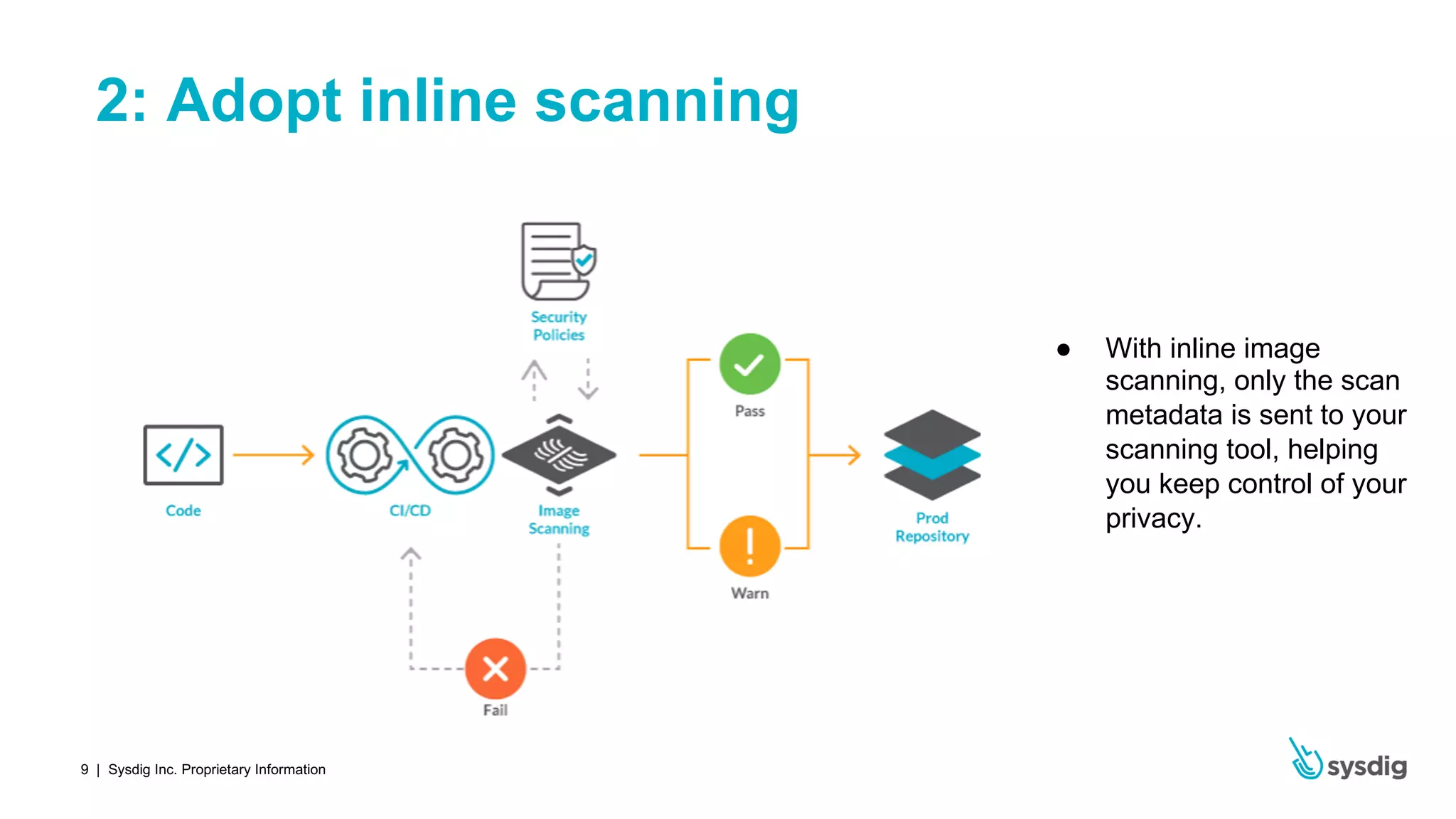
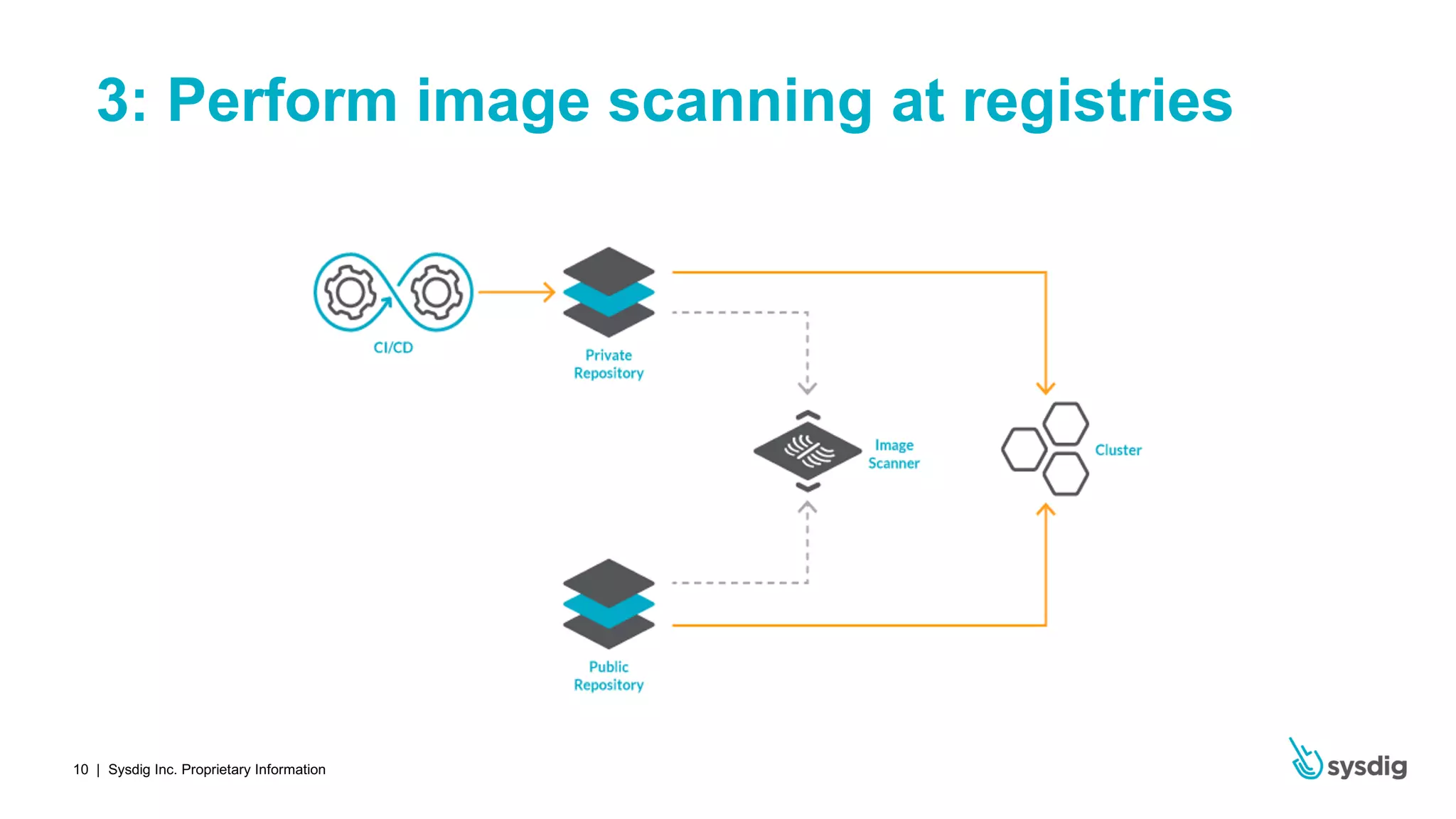
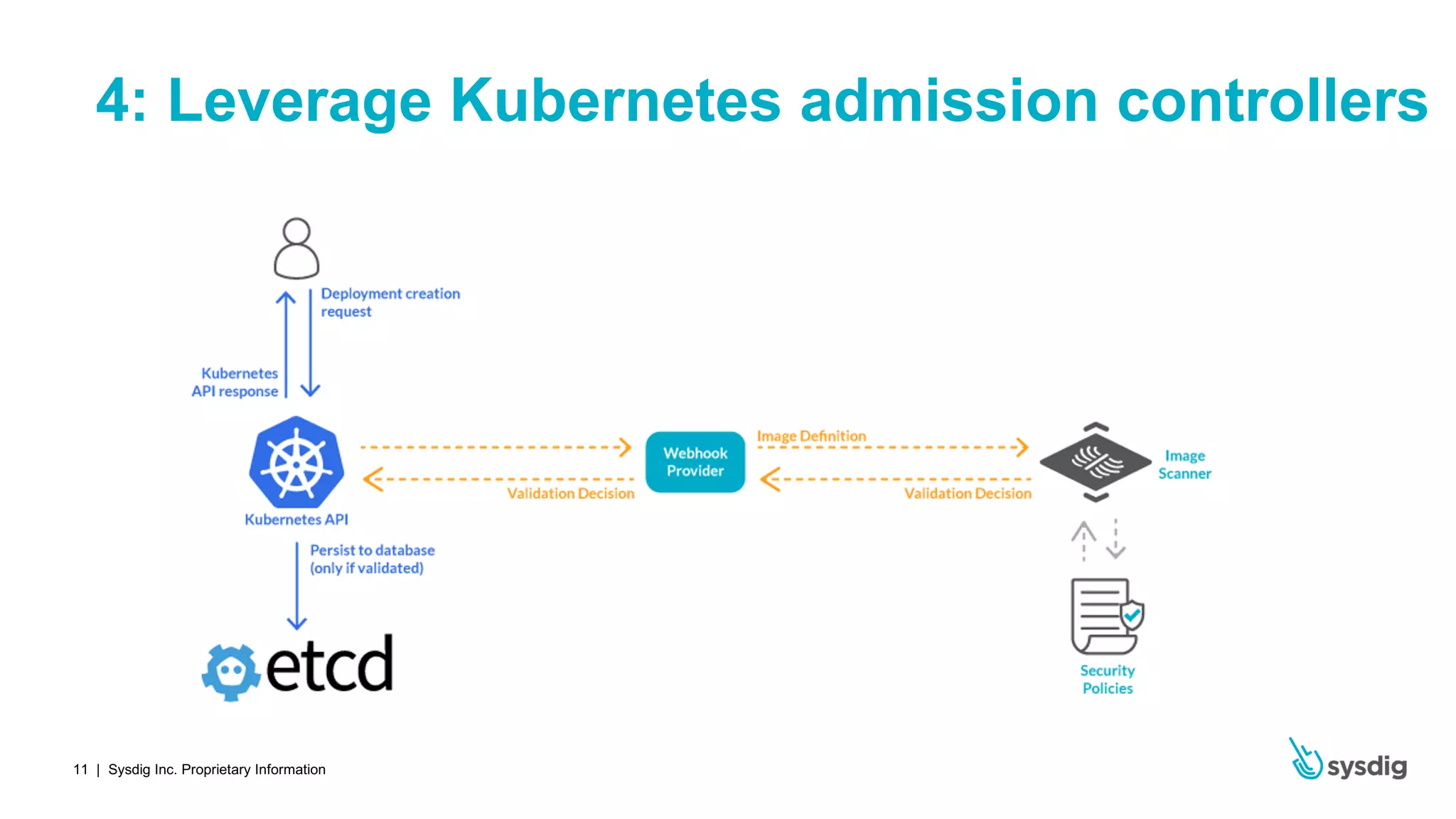
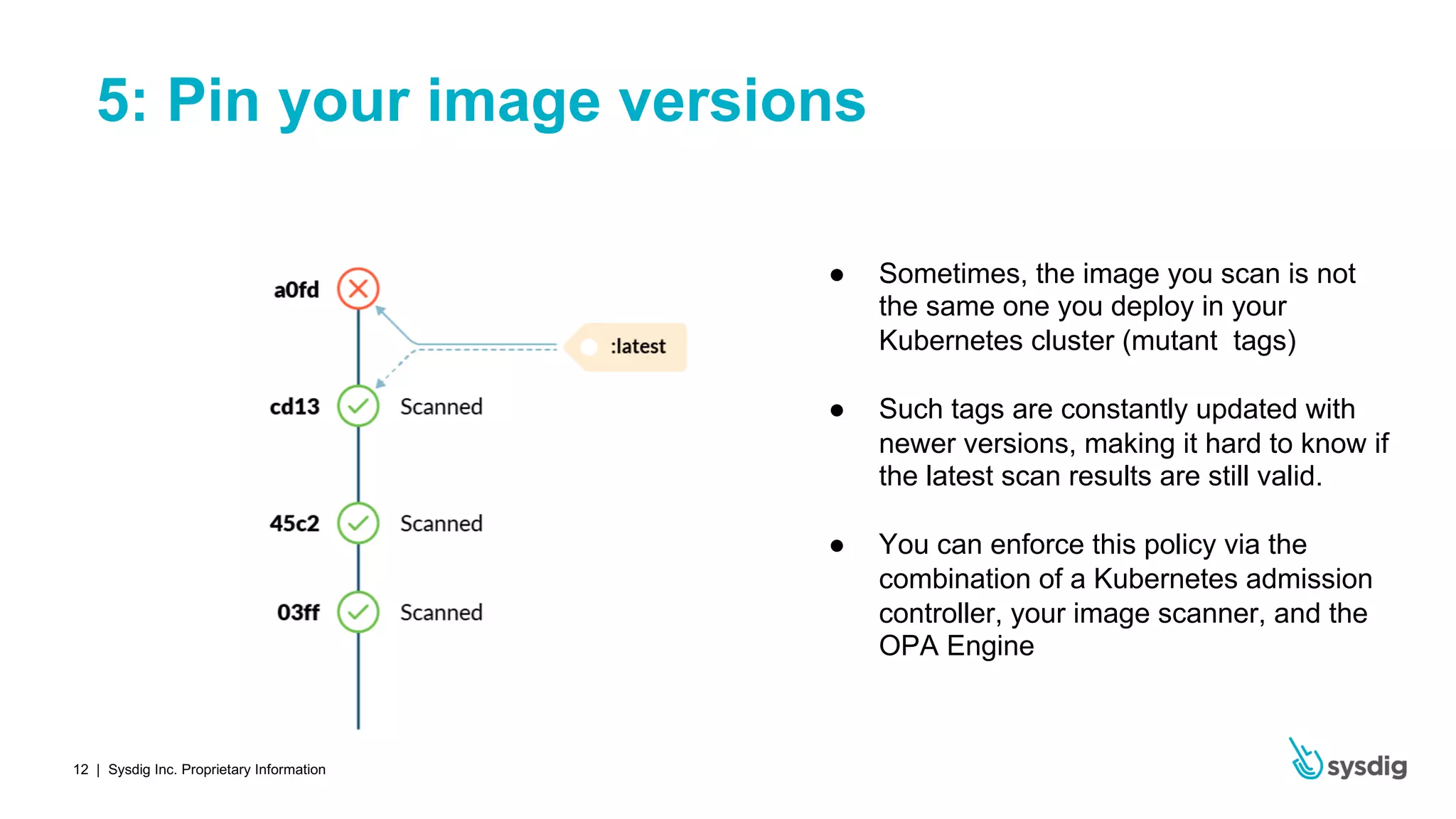
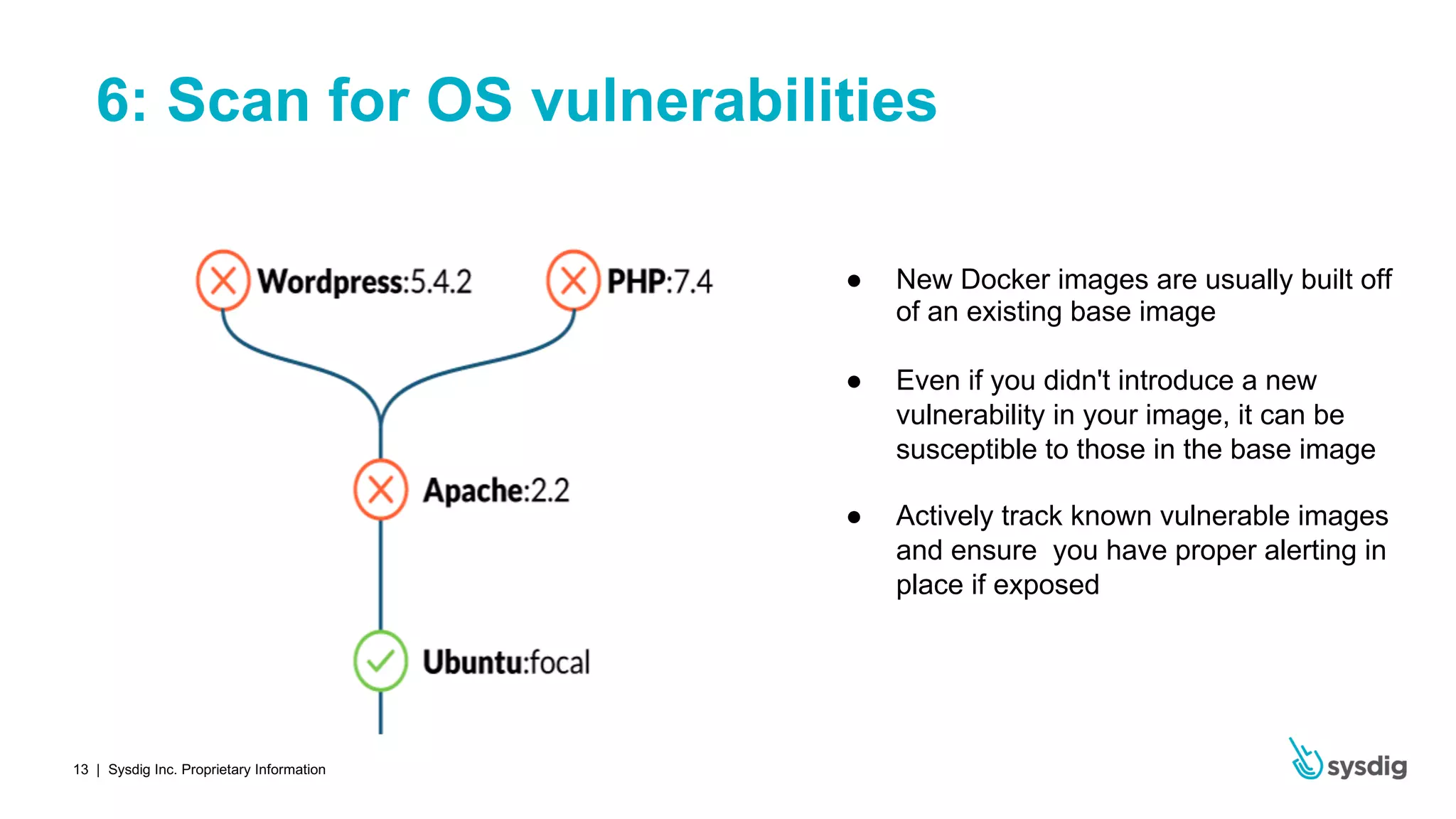
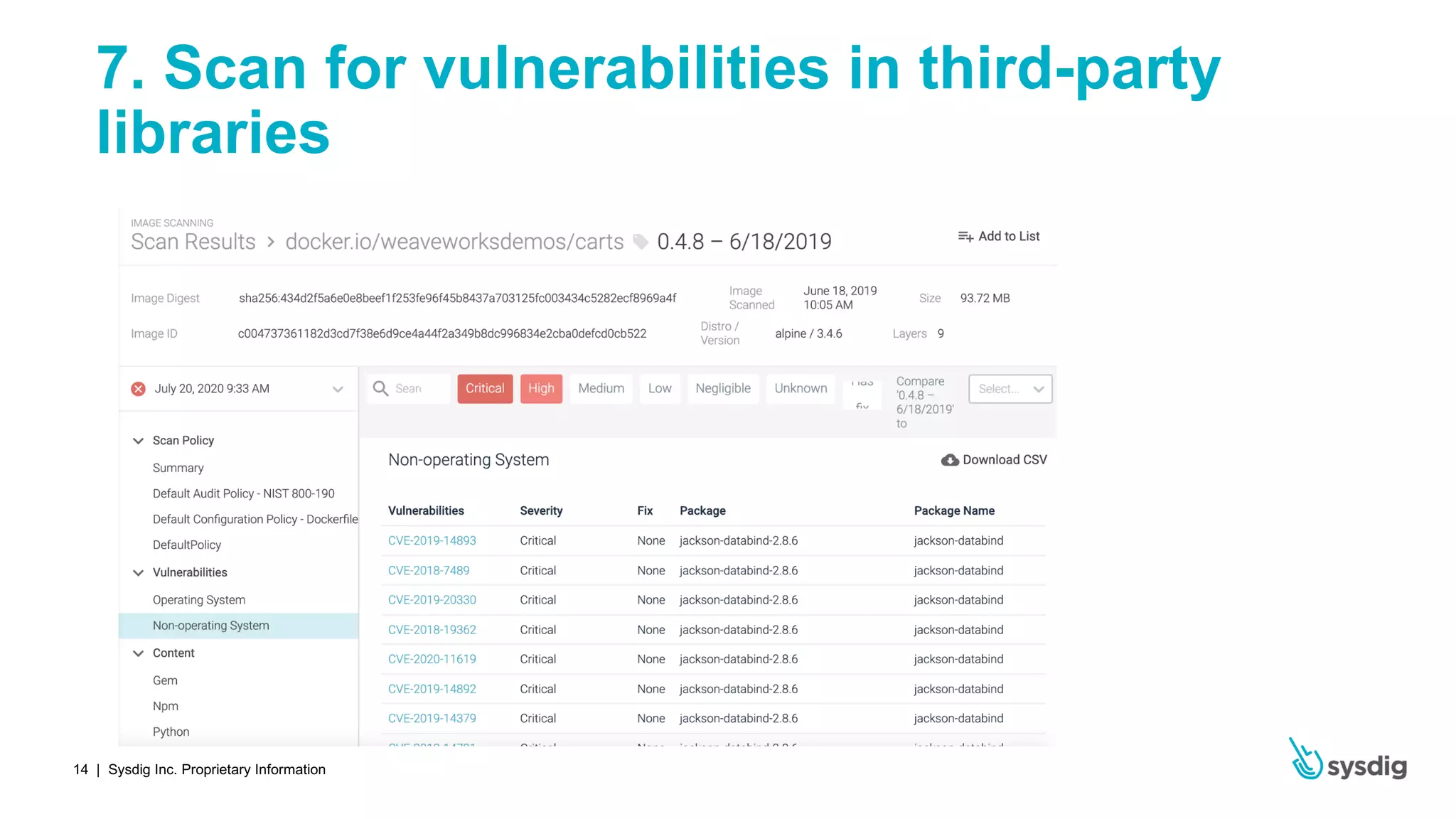
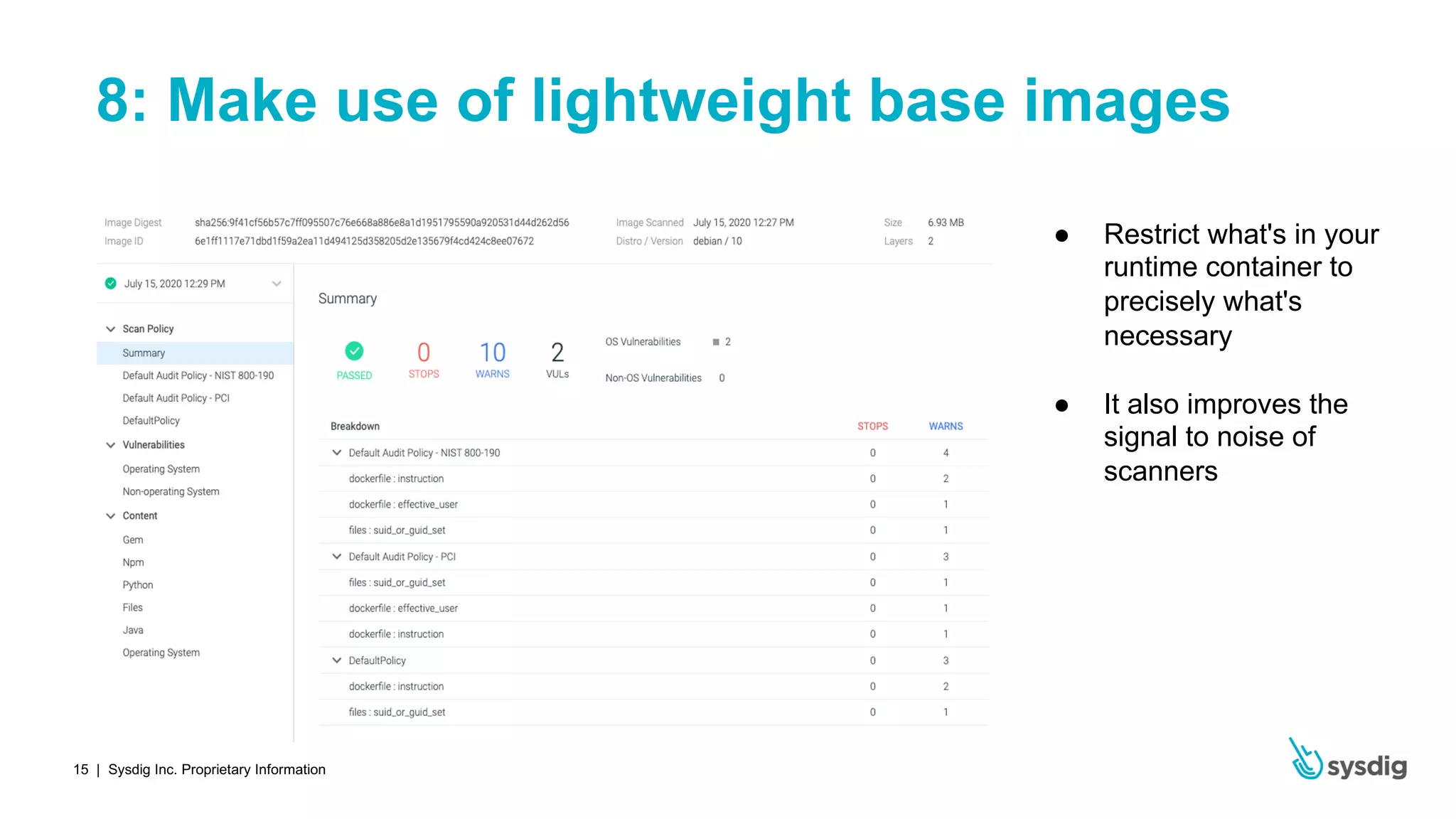
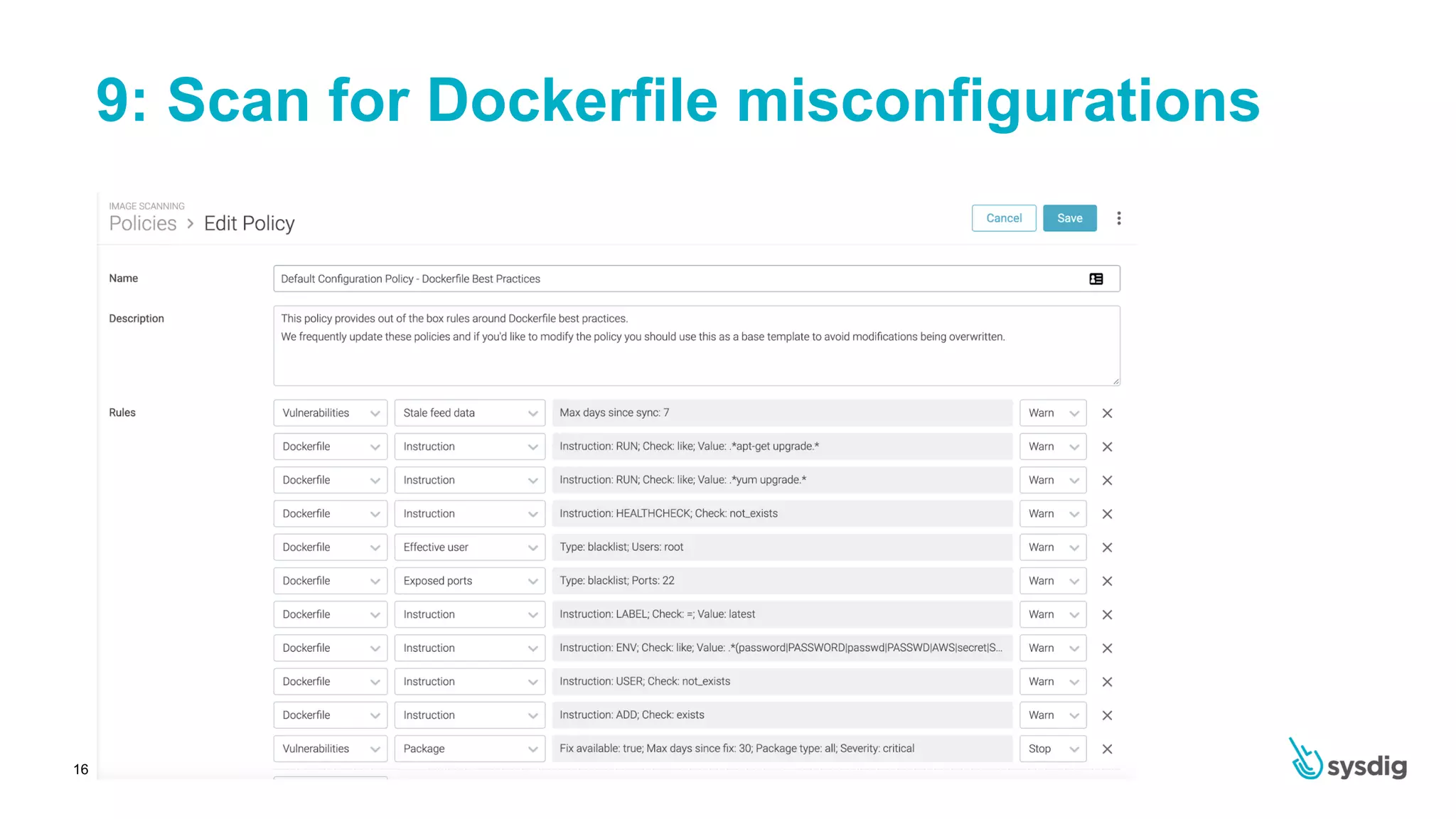
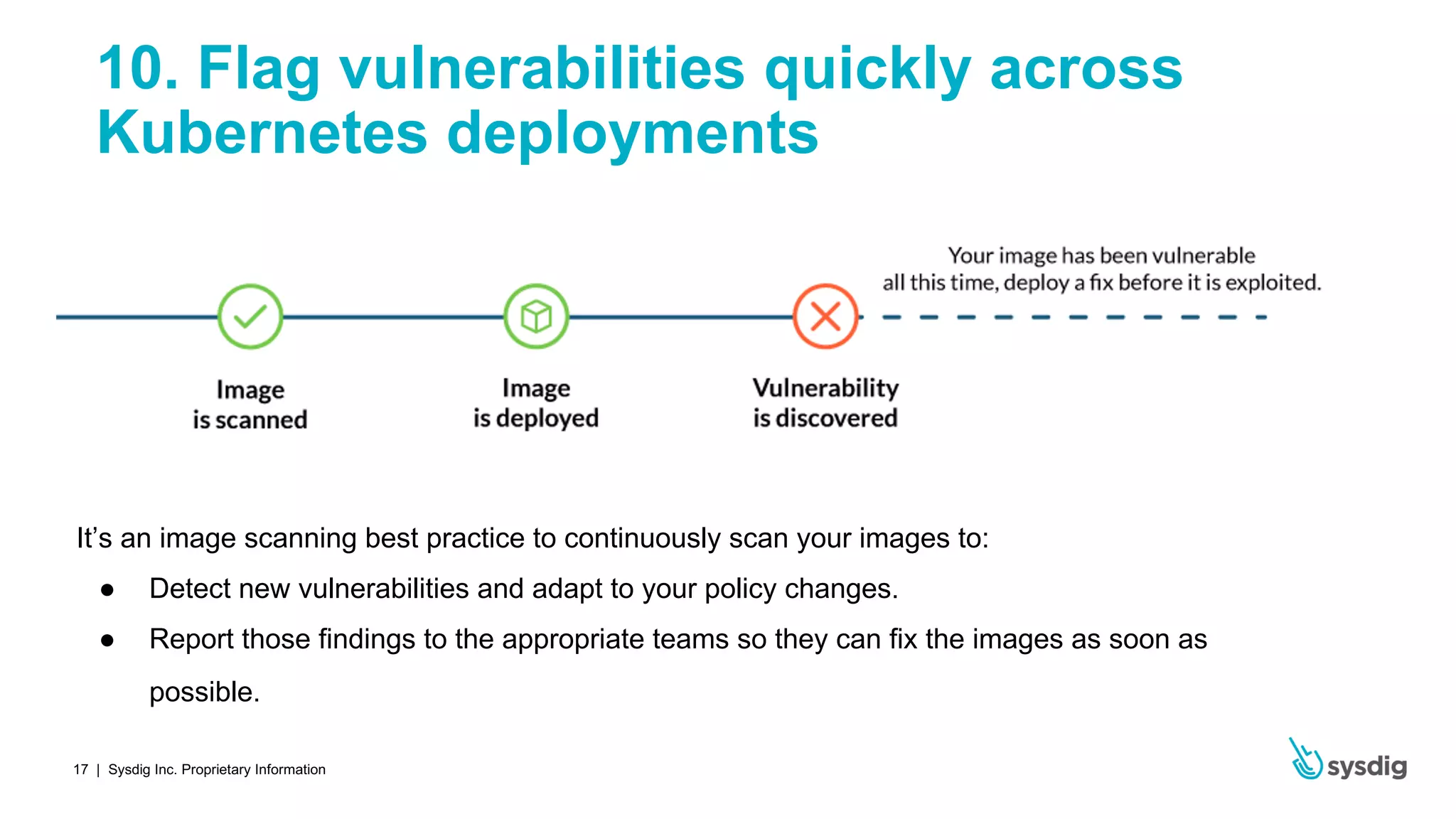
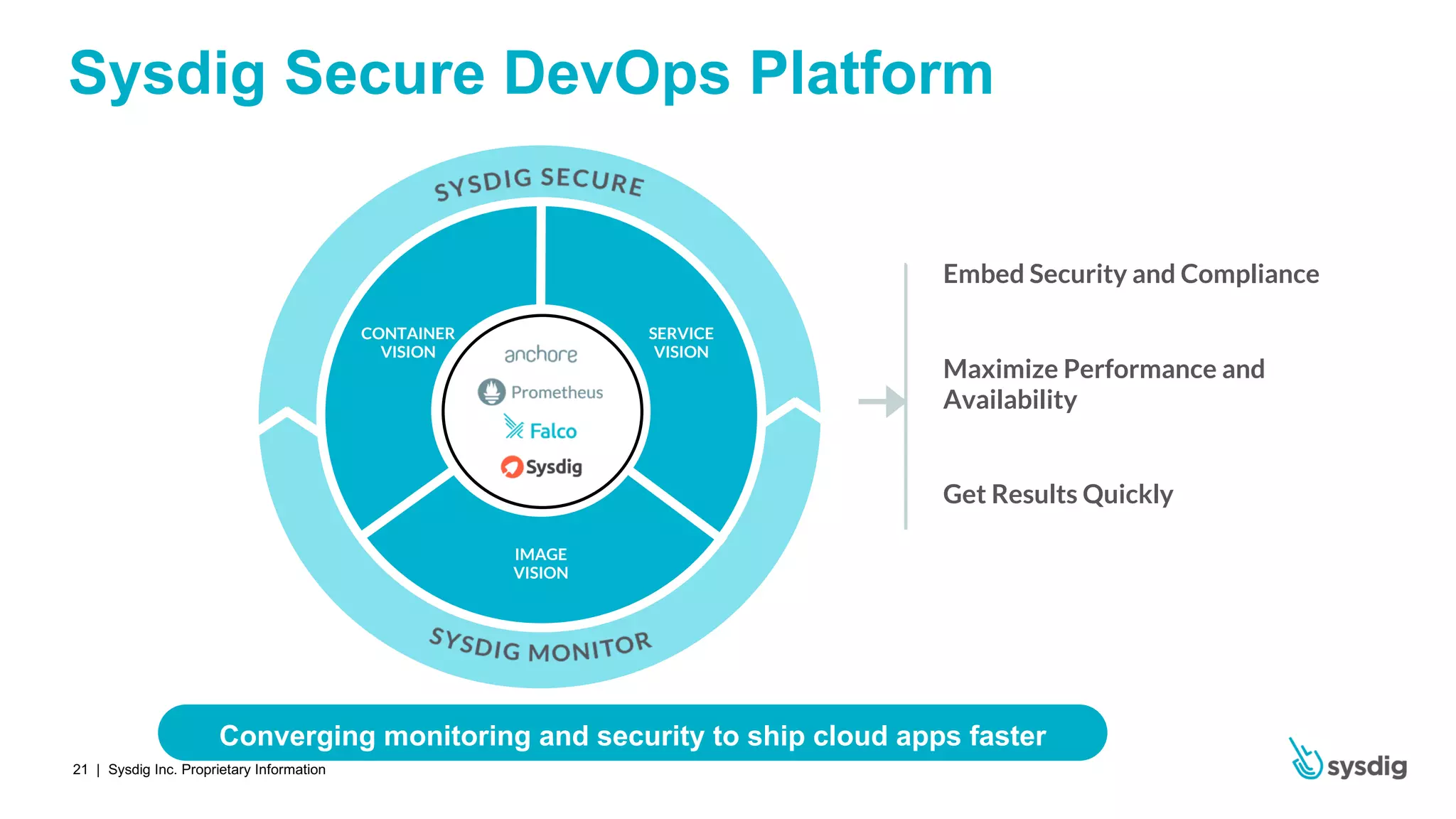
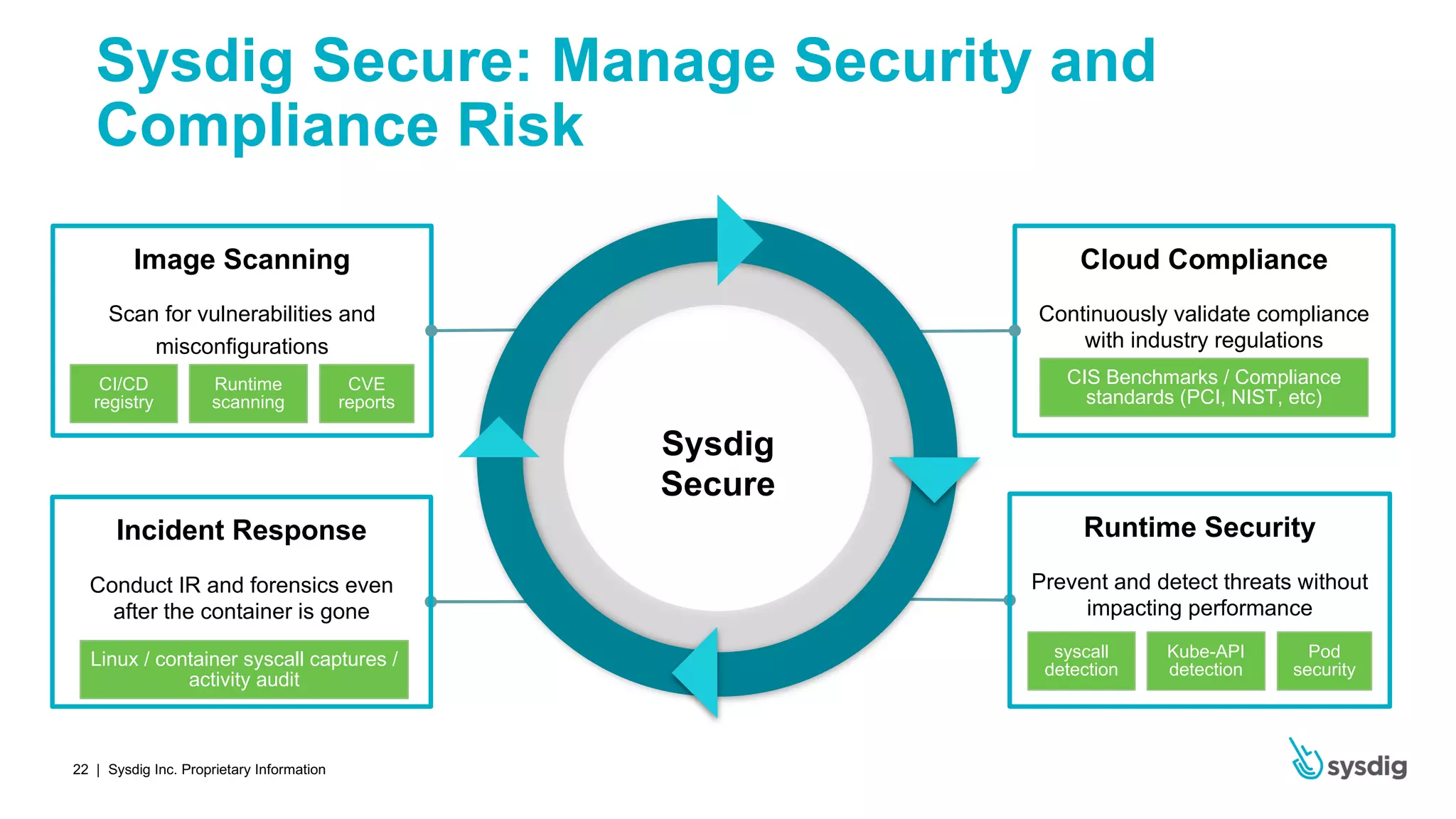
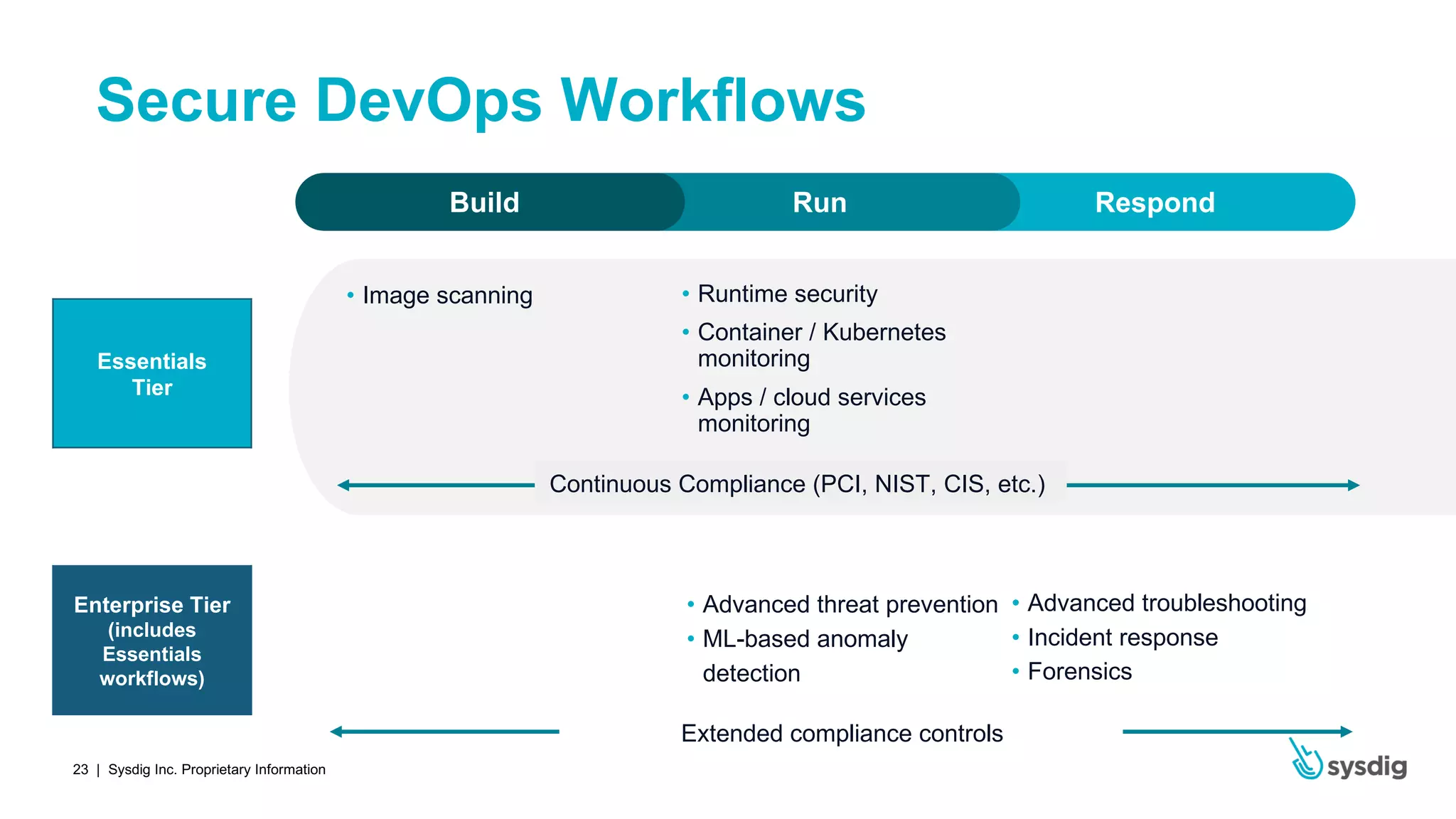
The document outlines best practices for image scanning in containerized environments and Kubernetes to enhance security in DevOps workflows. Key practices include integrating scanning into CI/CD pipelines, performing registry scans, leveraging Kubernetes admission controllers, and ensuring vulnerability detection in OS and third-party libraries. Additionally, it highlights the advantages of using a SaaS approach for image scanning, such as reduced operational overhead and faster implementation.