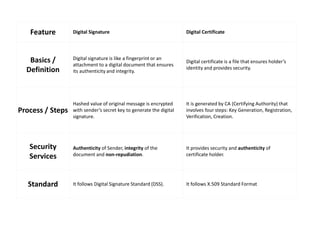
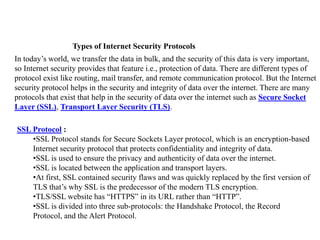
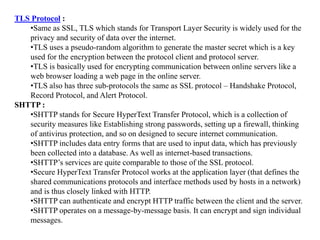
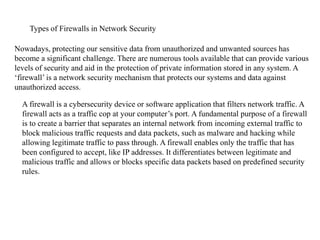
A digital certificate is issued by a certificate authority to verify an individual's or entity's identity, linking their public key with their identification information. It differs from a digital signature, which validates the authenticity and integrity of a message, while both are essential for security. Additionally, various internet security protocols exist, including SSL, TLS, and different types of firewalls, which protect data and networks from unauthorized access and ensure secure communications.