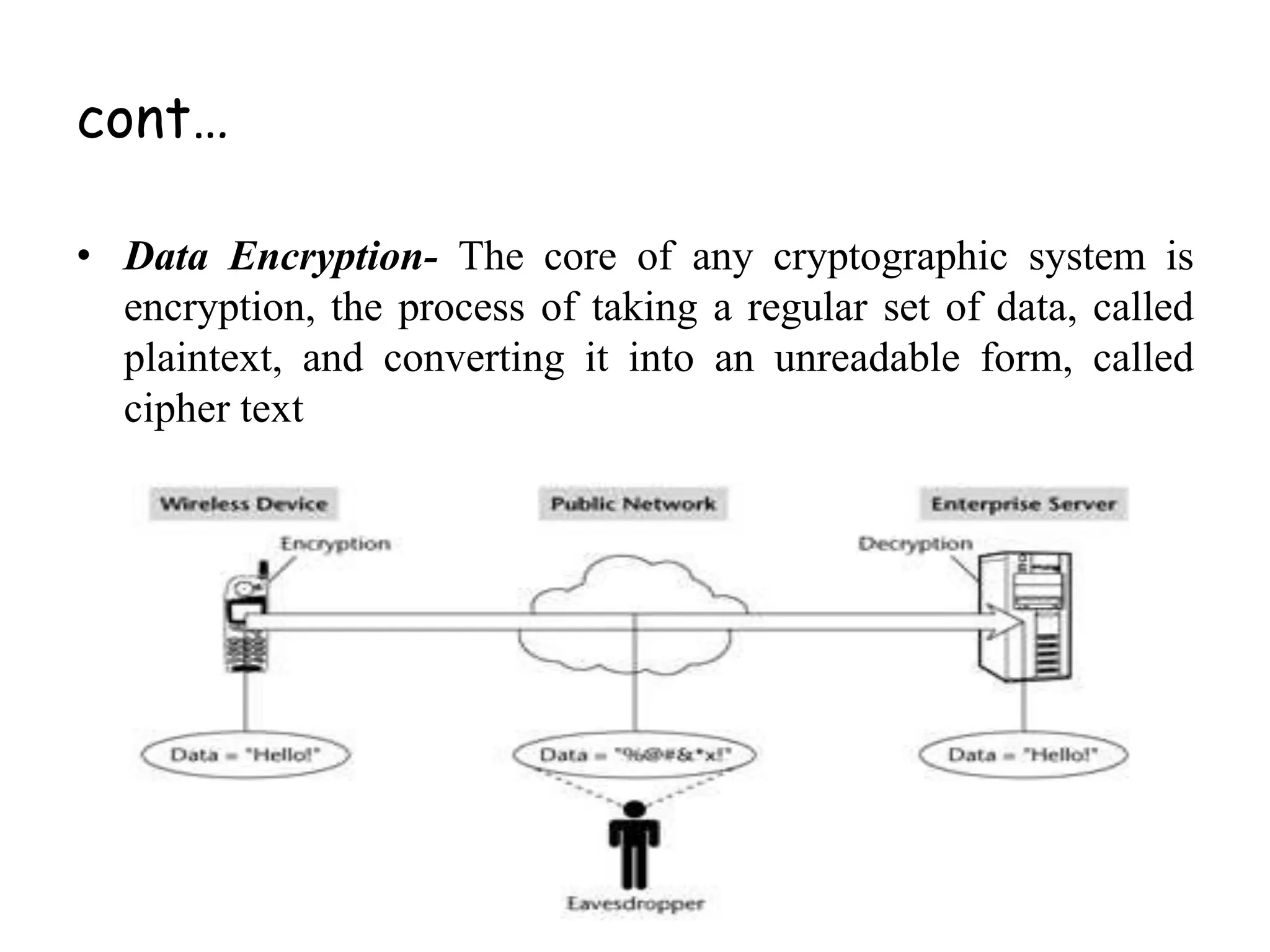
This document provides an overview of mobile and wireless security. It discusses the need for security as wireless networks become more prevalent and outlines some common security threats like spoofing, sniffing, tampering and theft. It then describes various security technologies used to address these threats, including cryptography, digital certificates, digital signatures and public key infrastructure. Specific security protocols like SSL, TLS and IPSec are also mentioned. The document emphasizes that securing wireless networks requires considering authentication, data integrity, confidentiality, authorization and non-repudiation across the entire environment.