Dr. Sam Musa01-01-2017Network LAN Design with VoIP and Wireles.docx
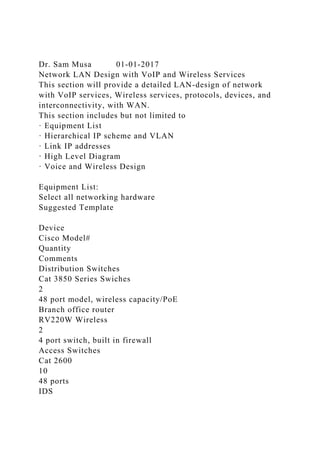
- 1. Dr. Sam Musa 01-01-2017 Network LAN Design with VoIP and Wireless Services This section will provide a detailed LAN-design of network with VoIP services, Wireless services, protocols, devices, and interconnectivity, with WAN. This section includes but not limited to · Equipment List · Hierarchical IP scheme and VLAN · Link IP addresses · High Level Diagram · Voice and Wireless Design Equipment List: Select all networking hardware Suggested Template Device Cisco Model# Quantity Comments Distribution Switches Cat 3850 Series Swiches 2 48 port model, wireless capacity/PoE Branch office router RV220W Wireless 2 4 port switch, built in firewall Access Switches Cat 2600 10 48 ports IDS
- 2. Network Monitoring System Fire wall Cisco Unified Call Manger 2 Voice services Step 2: Now name each device as per naming convention (Since it is new company, make it for them) Suggested template Device Device Configured Name Placement Connection Comments Cat 3850 Series switch Data center Switch 1 Data center Distribution Switch VLAN1, 2, 8 The switch has Inventory server, Payroll server, and VLAN 1, 2, 8 Core Switch 7600 Series CoreRouter1 Room#1014 DSW1 and DSW2
- 3. ISP1 Hierarchical IP scheme and VLAN Create an IP Scheme and VLANS. I suggest use the table below to create your hierarchical IP addressing scheme. Location Number of IP Addresses Required Future Growth Rounded Power of 2 Number of Host Bits Subnet Address Assigned Floor1 1500 200 2048 11 172.20.0.0-172.20.7.254/21 Floor2 200
- 4. 100 500 9 172.20.8.0-172.20.9.254/23 Floor 3 45 20 128 7 172.20.16.0-172.20.16.122/25 Floor4 Create VLAN: In creating VLAN, I will suggest use organizational structure model for simplicity. Examples: VPOPRVLAN1, VPOPRVLAN2 High Level Diagram: Drawing a network topology diagram is the most challenging task. To overcome this challenge, we need to use Cisco modular technology in upgrading the network in other words top down design approach. The top design approach starts with Application, Devices and infrastructure. You will also use the same approach in designing WWTC network. Select all the applications for the network. Then select the devices needed to run these applications. Now you are ready creating network topology diagram. Since, in WWTC network we have one floor,
- 5. so all of our devices, application and infrastructure will reside in one floor. Create subnets. Generally subnet matches organizational structure. Also, in a large network to increase performance or for security reasons, subnets are created. Furthermore to accommodate the need of a department, the subnets can be subnetted further or VLANs are created or both. Every organization have subnets and VLANs. Let us say we need 20 VLANs, which will serve client’s requirements, performance and security of the network. Assign these VLANs to switches. For example; you need 3 switches to host 3 VLANs for VPOPR. The diagram below depict the scenario. Sample Network Diagram For more sample High Level Diagrams, please check these links: LAN Diagrams Templates http://www.conceptdraw.com/diagram/diagram-for-lan A Basic LAN network Architecture http://www.excitingip.net/27/a-basic-enterprise-lan-network- architecture-block-diagram-and-components/ Voice Design: View Slide Show VoIP http://www.topdownbook.com/
- 6. Access to Microsoft Server and other tools: UMUC provides access to MS Dream Spark Premium. Once you register, you will be able to get various Windows and Servers operating systems. Dream Spark also includes VMWare workstation. Here is the link to dream spark: http://e5.onthehub.com/WebStore/Welcome.aspx?vsro=8 &ws=25a1bf0b-bc9b-e011-969d-0030487d8897 VPOPRVLAN1 VPOPRVLAN1 VPOPRVLAN1 V P O P R V L A N 2 V P O P R V L A N 2 V P O P
- 7. R V L A N 2 VPOPRVLAN3 VPOPRVLAN3 ASW1 ASW2 ASW3 DSW1 DSW2 172.16.0.0/30.1 .2 1 7 2 . 1 6 . 0 . 4 / 3 0 .5 .6 Link Addresses Week 1 - Overview Note: The online classroom is designed to time students out after 90 minutes of inactivity. Because of this, we strongly
- 8. suggest that you compose your work in a word processing program and copy and paste it into the discussion post when you are ready to submit it. Learning Outcomes This week students will: 1. Detect the makeup of a school culture. 2. Develop strategies to prepare leaders to create safe schools and functional school culture. Introduction Welcome to the first week of EDU688 – Organizational Management for Student Learning! In this course, you will adopt the perspective of a school or district administrator as you complete the coursework and engage in discussions each week. You will have various opportunities to solve problems as an administrator which will provide the support needed to create the Final Project in Week Six: A campus budget plan proposal. Our course has also been designed around the following five main enduring understandings that relate to the focus of the course: 1. having a school culture that is functional and safe; 2. having an effective recruitment, hiring, and training system that ensures the employment of effective teachers and staff; 3. having assessment and monitoring systems that promotes student learning; 4. having technology and digital systems that can produce the data needed to keep the school functioning; and 5. having the financial impact of programs that are budgeted for that lead to an effective school that meets the needs of students (see Figure 1).
- 9. Figure 1. EDU688 Enduring Understandings Throughout the six weeks of the course, these enduring understandings will provide a framework for the step-by-step process that will lead to the completion of the Campus Budget Plan Proposal, which is the Final Project for this course. During this first week, we begin by investigating the first enduring understanding - school culture and school safety. It is recommended that you take a moment now to review each week in the course, including the other introductions to weeks and their assessments, to get acquainted with the scope and flow of our learning these next six weeks and be aware of the variety of assessments you will complete while achieving the course outcomes and objectives. Additionally, take some time to review each week’s Instructor Guidance. In these sections you will find useful information that will guide you as you progress through the week’s posted resources and assignments. There are also resources and videos posted in the guidance section that address the essential questions that are fundamental to each week of the course. Keep in mind that the primary purpose for this course in your program is to help you to understand how to create goals and an outline for a campus budget plan proposal that encompasses providing for a positive school climate in which students from all subgroups are successful learners. Finally, this course provides you with many opportunities to utilize technology (Prezi, VoiceThread, Present.me, YouTube, ConceptMap, or PowerPoint) to accomplish discussion posts or assignments. Remember, it takes a “village” of collaborative members to promote effective and positive change within an organization; however, foremost it takes a committed leader to get the change moving.
- 10. Required Resources Required Text 1. Sorenson, R. D., & Goldsmith, L. M. (2013). The principal’s guide to school budgeting, (2nd edition). Thousand Oaks, CA: Corwin. · For Week One, read pages 60-63. Articles 1. Heathfield, S. M. (n.d.). How to change your culture: Organizational culture change. Retrieved from http://humanresources.about.com/od/organizationalculture/a/cult ure_change.htm · This article provides strategies as to how to change an organizational culture. 2. Heathfield, S. M. (2010). How to understand your current culture: Artifacts and interactions display your existing culture. Retrieved from http://humanresources.about.com/od/organizationalculture/a/cult ure_create.htm · In this article, Heathfield helps educators look at the culture that exists in their organization, including artifacts and interactions that display the existing culture. Recommended Resources Articles 1. Schein, E. H. (1993). Organizational culture & leadership. Retrieved from http://www.tnellen.com/ted/tc/schein.html · The author of this article defines organizational culture and, discusses the dimensions of culture and how to manage internal integration of culture, and how leaders embed and transmit culture. Websites 1. Present.me. (https://present.me/content/need-convincing/)
- 11. · This web-based software allows you to add a video or audio explanation to your document or presentation. 2. VoiceThread. (http://voicethread.com/) · This web-based software provides a means to enliven presentations with narrated audio comments. 3. YouTube. (http://www.youtube.com) · This is a video-sharing website. Post Your Introduction To post your introduction, go to this week's Post Your Introduction link in the left navigation. This discussion is an opportunity to develop a community with your class peers and your instructor. Though you may already have some acquaintance with fellow learners from prior courses, this is your opportunity to strengthen connections and develop a community with the instructor for promoting deeper conversations and learning throughout our course. The use of technology is an integral part of your learning and teaching. Therefore, in this introduction you have two technology options for presenting your initial post. Select one of the options listed below. · Option 1: Create a presentation using the software of your choice such as PowerPoint, YouTube, or VoiceThread. Include slides, video, audio, documents, or photos as part of your introduction. · Option 2: Create a short video to introduce yourself using the software of your choice such as VoiceThread or YouTube. In your initial post- · Share who you are and your personal interests, including your professional background and experience, especially any dealing with education, and your personal interests. · Identify one leader and describe his or her leadership style. Your chosen leader can also be someone you know or someone who has been influential in education, such as Horace Mann, John Dewey, Booker T. Washington, or W. E. B. Dubois. Then,
- 12. explain why you would like to emulate this person’s leadership style and provide specific examples of how you plan to emulate this leader’s style in your current or a future work setting. · Share one quote and its author, if known, that symbolizes your belief about leadership. Explain why this quote appeals to you and how it informs your decisions about your leadership style. · Describe the type of position you hope to have in the future and/or as a result of your graduate education. What impact do you believe having your master’s degree will have on your future endeavors as a leader? Guided Response - Post replies to at least three peers. In your replies, consider asking questions of your peers about their responses to encourage further conversation. Though three replies is the basic expectation in this discussion, for deeper engagement and community building with peers, you are encouraged to provide responses to any comments or questions others have posted for you (including the instructor) before the last day of the learning week. This continued interaction will further the conversations and provide you with opportunities to network and get to know your instructor and peers for more optimal engagement in the coming weeks! Discussions To participate in the following discussions, go to this week's Discussion link in the left navigation. 1. Detect Components of School Culture The following quote by Sorenson and Goldman (2013) reveals the components of a functional school culture (collegial spirit, shared values, beliefs, and traditions) and the best way (through enthusiasm, energy, and motivation) to have a school where all students succeed as learners: “The integrated budget model requires a school culture receptive to collaboration. Schools, which possess a collegial spirit, shared values, beliefs, and traditions are more apt to spawn the required collaborative environment that in turn increases enthusiasm, energy, and
- 13. motivation.” To prepare for this discussion you will read the “Culture, Data, and Celebrating Success” section of Chapter 3 of the required text by Sorenson and Goldman (2013), the Healthfield (2011, 2010) articles, and the Schein (1993) article. These authors discuss how to understand and change school culture. When you understand the culture of your school, you can make sure that it is sufficient to successfully provide optimum learning for all the subgroups of students in the school. Initial Post - In your initial response construct at least one succinct yet descriptive paragraph for each point listed below. · Discuss what school culture is and identify what the typical components of a functional school culture are using Sorenson and Goldman (2013, pp. 60-63) and the Healthfield (2010) article as resources to support your discussion. · Describe strategies that can be used to facilitate a school meeting the components of a functional school culture. · Explain how knowing what the components are of the school culture can inform your ability to detect the makeup of a school culture and select strategies for implementing a functional school culture. Guided Response - Respond to at least two peers. In your replies, consider asking questions of your peers about their responses to encourage further conversation. Consider selecting a peer whose school culture differs from your own and one that is similar. Provide feedback regarding your peers’ reasons for the value of knowing one’s school culture. Though two replies is the basic expectation, for deeper engagement and learning, you are encouraged to provide responses to any comments or questions others have given to you (including the instructor) before the last day of the learning week. This will further the conversation and provide you with opportunities to demonstrate your content expertise, critical thinking, and real-world experiences with this topic.
- 14. 2. Determine Functionality of School Culture Functionality refers to whether the culture of an organization aids in meeting the mission of the organization as well as serves in promoting an environment of respect between members of the organization and in accomplishing successful learning for all subgroups of the students. Initial Post - Determine the functionality of your school by holding an informal discussion with at least three employees, preferably a school leader, a teacher, and a para-educator. Discussions can be conducted through face-to-face, email correspondence, or telephone conversation. If you are not currently employed in a school setting but you know people who are, you may use them as contacts. Use the questions below to determine the functionality of your school. Be sure to include the positions and first names only of the person with whom you had your conversation with. · What would you tell a friend about your school if he or she was about to start working there? · What is the one thing you would most like to change about this school? · How are decisions made at this school? · What is your favorite characteristic that is present in your school? · What does it take for the adult professional to be successful in your school? · What is your favorite question to ask a candidate for a leadership position in your school? Based on the results of your discussions, identify and share in detail how functional your school is. The traits you identify as needing to be changed will be considered the dysfunctional traits. *If you do not have direct access to a school, or do not know anyone who does and could support you in these conversations, there are several options for completing this discussion. Please communicate proactively with your instructor to discuss these
- 15. options prior to the due date.* Guided Response - Respond to at least two peers. In your replies, consider asking questions of your peers about their responses to encourage further conversation. Consider selecting a peer whose school culture differs from your own and one that is similar. Provide feedback regarding your peers’ reasons for the value of knowing one’s school culture. Though two replies is the basic expectation, for deeper engagement and learning, you are encouraged to provide responses to any comments or questions others have given to you (including the instructor) before the last day of the learning week. This will further the conversation and provide you with opportunities to demonstrate your content expertise, critical thinking, and real-world experiences with this topic. Assignment To complete the following assignment, go to this week's Assignment link in the left navigation. Changing School Culture Construct your assignment to meet the content and written communication expectations below. Content Expectations · Dysfunctional School Culture Traits: Analyze the dysfunctional traits of your school. These are the ones that need to change. Use Healthfield (2011, 2010) and Schein (1993) as resources to support your analysis. · Dysfunctional School Culture Explanation: Explain the potential harm done to the school’s effort to ensure that all students succeed as learners as a result of the dysfunctional school culture traits. Use Healthfield (2011, 2010) and Schein (1993) as resources to support your explanation. · Develop Strategies for Changing School Culture: Develop at least three strategies for improving the previously identified
- 16. dysfunctional traits. · Rationale for Changes to School Culture: Explain the rationale for the changes you would like to make drawing on Healthfield (2011, 2010) and Schein (1993) for support for the strategies you develop. · New School Culture: State your school’s mission and vision and explain how the changes made in the school culture will better serve the mission and vision of the school. Use Healthfield (2011, 2010) and Schein (1993) as support for your explanation. · School Success: Evaluate the extent to which the new school culture is able to ensure that all subgroups of the students are successful learners. Use Healthfield (2011, 2010) and Schein (1993) as support for your evaluation. Written Communication Expectations · Page Requirement: Your paper must be two to three pages in length, not including title and references pages. · APA Formatting: Use APA formatting consistently throughout the paper. It is recommended you use the content area labels as headings for each section of your content for the paper. For information regarding APA, including samples and tutorials, visit The Ashford Writing Center. · Syntax and Mechanics: Display meticulous comprehension and organization of syntax and mechanics, such as spelling and grammar. Your written work should contain no errors and be very easy to understand. · Source Requirement: Use at least three scholarly sources in addition to the course textbook, providing compelling evidence to support ideas. All sources on the reference page need to be used and cited using APA standards within the body of the assignment. Next Steps: Review and Submit the Assignment Review your assignment with the Grading Rubric to be sure you have achieved the distinguished levels of performance for each criterion. Next, submit the assignment for evaluation no later
- 17. than Day 7. Changing School Culture PLEASE DO NOT SUBMIT A BID FOR THIS ASSIGNMENT IF YOU DO NOT UNDERSTAND EDUCATION TERMS AND CONCEPTS. ALL DIRECTIONS MUST BE FOLLOWED AND NO PLAGARIASM. MY SCHOOL USES SOFTWARE TO DETECT COPIED MATERIAL. Please read these assignment instructions before writing your paper, and re-read them often during and after the writing process to make sure that you are fulfilling all of the instructions. Please also utilize the assignment guidance below and the template provided. The links to the required sources is below. In addition to the sources below, you’ll need to research and use at least 1-2 more. Please let me know if you have any questions. Construct your assignment to meet the content and written communication expectations below. Content Expectations · Dysfunctional School Culture Traits: Analyze the dysfunctional traits of your school. These are the ones that need to change. Use Healthfield (2011, 2010) and Schein (1993) as resources to support your analysis. · Dysfunctional School Culture Explanation: Explain the potential harm done to the school’s effort to ensure that all students succeed as learners as a result of the dysfunctional school culture traits. Use Healthfield (2011, 2010) and Schein (1993) as resources to support your explanation. · Develop Strategies for Changing School Culture: Develop at least three strategies for improving the previously identified dysfunctional traits. · Rationale for Changes to School Culture: Explain the rationale
- 18. for the changes you would like to make drawing on Healthfield (2011, 2010) and Schein (1993) for support for the strategies you develop. · New School Culture: State your school’s mission and vision and explain how the changes made in the school culture will better serve the mission and vision of the school. Use Healthfield (2011, 2010) and Schein (1993) as support for your explanation. · School Success: Evaluate the extent to which the new school culture is able to ensure that all subgroups of the students are successful learners. Use Healthfield (2011, 2010) and Schein (1993) as support for your evaluation. Written Communication Expectations · Page Requirement: Your paper must be two to three pages in length, not including title and references pages. · APA Formatting: Use APA formatting consistently throughout the paper. It is recommended you use the content area labels as headings for each section of your content for the paper. · Syntax and Mechanics: Display meticulous comprehension and organization of syntax and mechanics, such as spelling and grammar. Your written work should contain no errors and be very easy to understand. · Source Requirement: Use at least three scholarly sources in addition to the course textbook, providing compelling evidence to support ideas. All sources on the reference page need to be used and cited using APA standards within the body of the assignment. Resources for Assignment Articles 1. Heathfield, S. M. (n.d.). How to change your culture: Organizational culture change. Retrieved from http://humanresources.about.com/od/organizationalculture/a/cult ure_change.htm 2. Heathfield, S. M. (2010). How to understand your current culture: Artifacts and interactions display your existing culture. Retrieved from
- 19. http://humanresources.about.com/od/organizationalculture/a/cult ure_create.htm 3. Schein, E. H. (1993). Organizational culture & leadership. Retrieved from http://www.tnellen.com/ted/tc/schein.html APA Made Easy: A Student’s Guide to APA Formatting Ashford Writing Center June 2014* *Revised bi-annually for clarity and modification. Adapted by the AWC from original, created by Dr. Stephanie Lassitter, College of Education, and Jennifer Richardson, Curriculum and Innovation Division
- 20. 2 Table of Contents The Mechanics of APA Style ............................................................................................... .......... 4 In-Text Citations ............................................................................................... .......................... 4 Citing Page or Paragraph Numbers ............................................................................................. 5 Quoting, Paraphrasing, and Summarizing ...................................................................................... 6 Quotation ............................................................................................... ...................................... 6 Block Quotation ............................................................................................... ........................... 6 Signal Phrases ............................................................................................... .............................. 7
- 21. Paraphrase ............................................................................................... .................................... 7 Secondary Sources: Citing a Source Within a Source .................................................................... 8 Author Citations ............................................................................................... ............................... 8 One Author ............................................................................................... ................................... 8 Two Authors ............................................................................................... ................................. 9 Citing Three to Five Authors ............................................................................................... ....... 9 Six or More Authors ............................................................................................... ..................... 9 Heading Levels ............................................................................................... .............................. 10 Tables and Figures ............................................................................................... ......................... 11
- 22. Tables ............................................................................................... ......................................... 11 Figure ............................................................................................... ......................................... 11 Appendices ............................................................................................... ..................................... 12 Seriation (Using Lists in a Paper) ............................................................................................... 133 Numerical List ............................................................................................... ............................ 13 3 Bulleted List ............................................................................................... ............................... 13 A Seriated List Within a Paragraph................................................................................ ......... 134
- 23. General Formatting Guidelines ............................................................................................... .... 144 Peer-Reviewed Articles ............................................................................................... ................. 16 What Are Peer-Reviewed Articles? .......................................................................................... 16 What Are Non Peer-Reviewed Publications? ......................................................................... 166 Annotated Bibliography ............................................................................................... ............... 177 Books: Hard Copy and Digital.................................................................................... ................ 177 Digital Copy: Vital Source ............................................................................................... .......... 188 ConstellationTM Textbook .................................................................................. ............. ............ 188 Online Sources ............................................................................................... ............................... 19 Online Scholarly Journal Article with
- 24. DOI............................................................................... 19 Online Scholarly Journal Article Without DOI......................................................................... 19 Online Newspapers or Magazines ............................................................................................. 19 Web Article, No Author ............................................................................................... ............. 20 Citing an Entity or Organization ............................................................................................... 20 Citing All Other Online, Unauthored Articles .......................................................................... 20 Instructor Guidance in an Ashford Online Course .................................................................... 20 Reports ............................................................................................... ........................................... 21 Federal Government Agency ............................................................................................... ..... 21 Blogs………………………………………………………………… …………………………21 Audiovisual Materials ...............................................................................................
- 25. .................... 22 4 Personal Communication ............................................................................................... ............... 22 Personal Communications: Interviews, Personal Correspondences, Emails ........................... 22 Please cite this document as follows: ........................................................................................ 23 The Mechanics of APA Style The American Psychological Association (APA) is one of the largest scientific and professional associations in the United States. APA style is a set of rules and guidelines provided by this association to ensure a professional standard of scholarly writing. APA Style is the required citation style in all Ashford University courses. As students and researchers, it is important that we give credit to those whose ideas have
- 26. contributed to our own work. As academic writers, we draw from and build on the work of previous scholars and professionals. When we present our writing, we want to show our readers that we are knowledgeable about our topics and that we have become informed by seeking out works written by others who are experts on these topics. When we document our sources, we share with our readers the research we have done to develop the balanced and reasoned positions that we present in our writing. To demonstrate our credibility as writers and professionals, we use APA style—an agreed upon set of rules and guidelines—to lead our readers to the original source material that we have used in preparing our work. These rules and guidelines comprise the formal conventions for writing that are respected in our professional fields and help us to communicate professionally with colleagues and peers. APA citation style focuses on both the author and the date the article or study was published. This focus on the date is important since things change rapidly in our fields of study. In-Text Citations In-text citations are also referred to as parenthetical citations. In-text citations are citations used within the body of the paper, whereas the term reference refers to the complete citation, which is typically listed on the references page. Why use in-text citations? In-text citations are considered trails on a map to show sources you consulted and used in your journey during the
- 27. research phase of the writing process. 5 Citations signal for the reader whose ideas belong to the writer and whose ideas belong to an outside source. For example, the in-text citation for a reading from Hibel, Farkas, and Morgan (2010) would be cited as follows: "Certain groups of students are routinely found to be overrepresented (compared to their share in the school-aged population) in special education classrooms" (Hibel, Farkas, & Morgan, 2010, p. 313). The same quotation could also be presented as follows: According to Hibel, Farkas, and Morgan (2010), “Certain groups of students are routinely found to be overrepresented (compared to their share in the school- aged population) in special education classrooms” (p. 313). Citing Page or Paragraph Numbers The APA prefers that writers include page numbers in citations
- 28. for direct quotes. If page numbers are not available or are inconsistent, cite paragraph numbers. Citation for a text with page numbers: (Zirkel, 2011, p. 262). 6 Citation for a range of pages within a text: (Zirkel, 2011, pp. 262–263). Citation for a text without page numbers: (Zirkel, 2011, para. 4). Writing tip: Using a variety of citation techniques will enhance the flow and readability of your paper. For example: “Teachers must create a learning environment that is emotionally and psychologically safe because English Language Learners are very sensitive to the classroom setting” (Allison & Rehm, 2011, p. 23). Allison and Rehm (2011) noted, “Teachers must create a learning environment that is emotionally and psychologically safe because English Language Learners are very sensitive to the classroom setting” (p. 23).
- 29. Note: The author’s last name and date of publication always remain together. The paragraph or page number in parentheses indicates when you leave the ideas of an outside source and return to your own. Quoting, Paraphrasing, and Summarizing Quotation A quotation is made by using the original wording from an outside source and incorporating those words into your own writing. The words from the outside source will be clearly marked as belonging to another and enclosed in quotation marks. When quoting fewer than 40 words, place quotation marks around the entire passage, followed by the citation, such as: “Technology can take on several roles in education, such as role of resources, role of delivery system, or productivity” (Lee et al., 2013, p. 134). Block Quotation Quotations that are more than 40 words in length should be indented a half inch (the same length as a paragraph’s indentation). Quotation marks are not placed around the cited material; rather, the indentation signifies that the material is a direct quote. Lastly, the period is placed at the end of the quoted material (not at the end of the citation) as shown here:
- 30. 7 Signal Phrases In order to give your reader a signal that you will be integrating information borrowed from another source, use a signal phrase. A signal phrase introduces the passage and tells something about the source and author. Think of this signal as a way to lead into the quote by preparing readers for what they're about to read. Here are some examples: • Lee, Waxman, Wu, Wichko, and Lin (2013) explained the multi-layered dynamic of technology in education: • Tess (2013) discussed social media trends… • According to Johnson (2009), there are various studies dedicated to issues in education… • Phillips and Lyons (2011) argued for the need for yearly peer reviews among faculty… Without a signal phrase and clear citation, the reader might assume that your excellent ideas all came from an outside source. Paraphrase
- 31. A paraphrase is taking the ideas of an outside source and putting those ideas into your own words. Paraphrases do not need quotation marks, but they do need to be cited similarly to a 8 direct quotation by placing the author's last name, year of publication, and paragraph or page number at the end of the paraphrased passage (strongly preferred by APA style guide). The table below shows a side-by-side comparison of a quote, paraphrase, and summary using the same scholarly source: Original Quotation Paraphrase Summary Tess (2013) noted that “Researchers have been examining the role that social media plays in the higher education classroom. Some of the work has highlighted the affective outcomes of SNS integration. A few studies investigated learning outcomes and student achievement in relationship to the educational use of social media in college courses. While the
- 32. majority of studies reported positive affordances, there was evidence of drawbacks as well” (p. A62). Tess (2013) discussed the popularity of social media within higher education, noting that studies have investigated and reported both positive and drawbacks (p. A62). Tess (2013) analyzed the usage and impact of social media in the college classroom. Note: When summarizing, you do not need to include the page or paragraph number—just the author's name and date of publication. Secondary Sources: Citing a Source Within a Source If you find a quote in a source (secondary source) that cites content or ideas presented in another source (primary source), consider locating the original source. The use of secondary sources in your paper should be kept to a minimum. For example, if you found a quote by Eijkman (2008) in Tess’s (2013) publication, but could not find Eijkman’s original piece, here is how you would cite Eijkman (2008) as a secondary source: Eijkman (2008) argued that social media allows for “’non-
- 33. foundational network-centric learning spaces’” (as cited in Tess, 2013, p. A62). Author Citations One Author 9 When citing a work written by a single author, refer to the last name, year of publication, and page number, and separate each element with a comma. For example: “Textbooks are rapidly becoming a thing of the past” (Williams, 2012, p. 34). Or Williams (2012) noted, “Textbooks are rapidly becoming a thing of the past” (p.34). As a reminder, if page numbers are not available, use paragraph numbers. Two Authors When providing a parenthetical citation for a work by two authors, use an ampersand (&)
- 34. between the authors’ last names, followed by date of publication, and page number: “Part of the reason that business educators may be hesitant to interject discussions of the public policies and how they came about into their lectures and class discussions is a long-standing hesitancy to bring politics into the classroom” (Cornwall & Dennis, 2012, p. 13). As illustrated below, an ampersand would not be used in the signal phrase. Cornwall and Dennis (2012) argued, “Part of the reason that business educators may be hesitant to interject discussions of the public policies and how they came about into their lectures and class discussions is a long-standing hesitancy to bring politics into the classroom” (p. 13). Citing Three to Five Authors When providing in-text citations for works by three to five authors, cite all authors in the first citation. However, in subsequent citations, simply cite the first author’s last name followed by the Latin abbreviation et al (not italicized and with a period after al), which means “and others.” First citation in your paper: Hay, Hodgkinson, Peltier, and Drago (2004) Subsequent citations in your paper: (Hay et al., 2004) Six or More Authors
- 35. When citing a source written by six or more authors, reference the first author’s last name, followed by et al. For example, an article written by Strongin, Cole, Bullock, Banthia, Craypo, Sivasubramanian, Samuels, Garcia, and Lafleur (2004) would be cited as follows: 10 First and subsequent citations as part of a signal phrase: Strongin et al. (2004) First and subsequent parenthetical citations: (Strongin et al., 2004) If you secure a source that does not have an author’s name or organization listed, determine the entity responsible for the content. Don’t guess! For example, if citing a definition from an electronic version of the dictionary, cite as follows: (Merriam- Webster's Collegiate Dictionary, 2013). The dictionary entry will be listed on the references page beginning with the term in the author position: Pollinate. (2013). In Merriam-Webster’s online dictionary.Retrieved from http://www.merriam- webster.com/dictionary/pollinate
- 36. Heading Levels Students sometimes confuse the terms running head with heading level. The running head, as previously discussed, is placed within the top margin of your paper. Heading levels, however, can be placed anywhere in your paper as a way to classify or organize your paper into sections. There are five levels: the first three levels are more commonly used in Ashford University assignments, whereas levels four and five may be used in longer papers (e.g., a master’s thesis). As a general rule, check with your instructor about formatting expectations. Please note: Headings are not used for Introductions, and Conclusion heading formats depend entirely on your instructor or college preference. Heading Level Template Example 1 Centered, Boldface, Uppercase and Lowercase Heading Choosing the Right University 2 Flush Left, Boldface, Uppercase and Lowercase Heading Program Offerings 3 Indented, boldface, lowercase paragraph heading ending with a period. Reputation of programs. 4 Indented, boldface, italicized, lowercase paragraph heading ending with a period. Virtual programs. 5 Indented, italicized, lowercase paragraph heading ending with a period. Hybrid courses.
- 37. 11 Tables and Figures When used correctly, tables and figures offer visual illustrations of your paper’s findings. Make sure to incorporate tables and figures into your paper if they were requested by your professor and if they support the main point(s) in your paper. If you determine that they serve as more of a supplement to your paper, insert these elements as appendices (see the next topic on organizing appendices). Tables Data presented in rows or columns is considered a table, and should be referred to as such. Refer to a table placed within your paper by number: (see Table 2). Include a general overview (not a specific, point-by-point analysis of the table) as illustrated below. Note: The words Adapted from should be used only if you have modified the table in some way. If you are simply reproducing a table from another source, use
- 38. the words Reprinted from. Figure Data provided as an illustration (e.g., a chart or photo) is referred to as a figure. Refer to a figure placed within your paper by number: (see Figure 1). 12 Appendices Appendices are “inserts” with additional information that add to the paper without disrupting the “flow” of the paper; for example, tables, graphs, or other information that support or supplement your paper’s focus. Appendices are placed after the references page in order of mention within the paper. If the paper includes one appendix, label it Appendix (without italics), centered. Then, include the title of the appendix underneath, centered and boldfaced. When including more than one appendix, organize each appendix after the references page in order mentioned in the paper: Appendix A, Appendix B, and so on. Under the title “Appendix,” center and bold the descriptive title for the material. The
- 39. appendix is inserted after the references page. The above example illustrates Appendix E, assuming that the student included Appendix A, Appendix B, and so on. 13 Seriation (Using Lists in a Paper) Seriated lists are often used in a paper for the purpose of organization and clarity. However, as a writing tip, avoid the overuse of seriated lists in a paper. Here are the three types of seriated lists: Numerical List Numerical lists are used to establish a process, a hierarchy, or a chronological order of events, as illustrated below. Students were asked to complete the following steps: 1. Register online using their student identification number. 2. Log into the site with their new usernames and passwords.
- 40. 3. Complete the survey. Note: The seriated list should include a period when a complete sentence, or semicolon when considered part of the signal sentence above; if so, the last point on the list should include a period to conclude the list and the preceding sentence. Bulleted List Bulleted lists do not have a specific order, as illustrated below. Dillon’s (2012) research concluded that successful leadership of virtual teams is achieved by: • establishing positive immediacy behaviors when replying to emails from virtual colleagues; • creating a listserv group to share relevant news; and • hosting weekly meetings via Skype, Google Meet, or other web-friendly programs. A Seriated List Within a Paragraph Brief seriated lists may also be used within a paragraph organized by (a), (b), and so on, as illustrated below. Dillon’s (2012) research concluded that successful leadership of virtual teams is achieved by: (a) establishing positive immediacy behaviors when replying to emails from virtual colleagues; (b)
- 41. 14 creating a group listserve to share relevant news; and, (c) hosting weekly meetings via Skype, Google Meet, or other web-friendly programs. Note: When using seriation within a paragraph, remember to separate elements with a semicolon (not a period). General Formatting Guidelines • The title, “References” should be centered (no bold). • Double space the references page just like the rest of your paper. • Do not use underlining, no bold. • Italics should be used for journal, book, and film titles. • Leave out professional credentials (i.e. EdD, PhD). • Personal communications (i.e., emails, interviews) are not listed on the references page. • The first line of each citation should be left aligned, but the subsequent lines in the citation are indented (choose “hanging indent” in paragraph formatting in Microsoft Word), as shown in this example: To access an example of a completed References page, click here. A partial example is available on the next page.
- 42. https://awc.ashford.edu/PDFHandouts/APA_References_List_Sa mple.pdf 15 16 Peer-Reviewed Articles What Are Peer-Reviewed Articles? Peer-reviewed or scholarly articles are sources that have been evaluated by the author’s peers (members of the discipline) before being published. When doing research on a topic, writers should be able to trust these sources and the information given. Peer-reviewed publications are first closely scrutinized by other experts in the field, meaning that if a researcher publishes an article on Alzheimer's disease treatment in a journal, for example, other scholars would have reviewed the article closely before the article would be
- 43. recommended for publication. What Are Non Peer-Reviewed Publications? Newspaper articles, wikis (such as Wikipedia), blogs, editorials, and trade magazine articles are not peer-reviewed or scholarly. We refer to these sources as "popular" sources. They may offer correct and useful information; however, writers in these genres are not required to cite their sources and are not held to the same standards of research as those who write for scholarly and/or peer-reviewed publications. Whenever outside sources are borrowed and used in your paper, you must include in-text citations and a references page. The in-text citations should appear in the main body of your paper, and the references page is inserted at the end of your paper. When asked to provide peer-reviewed sources in your assignment, begin your search using the Ashford Online Library. Depending on the database used, you will see that there is an option to limit your search to peer-reviewed articles and full-text offerings only. Limiting your search will provide you with only those articles that are peer-reviewed and fully available through our library (see below). Keep in mind that limiting your search to "full-text articles only" saves time by filtering out dozens of articles that may not be available via the Ashford University Library. For example, if you wish to search for peer-reviewed, full-text articles via the EBSCOhost
- 44. database, limit your search for both, as shown below: 17 Annotated Bibliography An annotated bibliography is a list of works that you may use to research a topic. It is similar to a references page; however, the main difference is you will include a brief summary of each source beneath each citation entry, which means that you will summarize the source in your own words rather than directly quoting the source. Depending on what your instructor asks of you, a summary may include just an overview of the source, and/or an evaluation of the source’s worth and reliability. Click here for a sample Annotated Bibliography. Books: Hard Copy and Digital Hard Copy Template: Author, A. A., & Author, B. B. (Year of publication). Title of book: Not capitalized. City, State (with abbreviated initials): Publisher.
- 45. Example: Brown, A., & Green, T. (2011). The essentials of instructional design: Connecting https://awc.ashford.edu/PDFHandouts%5CA%202_Sample_Ann otated_Bibliography_final.pdf 18 fundamental principles with process and practice (2nd ed.). Upper Saddle River, NJ: Pearson. Sample Quote: Brown and Green (2011) noted: “…people represent information in their minds as single or aggregated sets of symbols” (p. 30). Digital Copy: Vital Source Template: Author, A. A. (Year of publication). Title of book: Not capitalized [e-delivery platform]. City, State abbreviation: Publisher. Example: Armstrong, D., Henson, K., & Savage, T. (2009). Teaching today: An introduction to education (8th ed.) [Vital Source digital version]. Upper Saddle River, NJ: Pearson.
- 46. Sample Quote: “Your professional development as a teacher did not begin when you entered your teacher-preparation program” (Armstrong, Henson, & Savage, 2009, p. 30). ConstellationTM Textbook Print Copy: Author, A. (Year of publication). Title of book. City, State: Publisher. Example: Lefrancois, G.R. (2012). Children’s journeys: Exploring early childhood. San Diego, CA: Bridgepoint Education, Inc. Sample “In practice, research methods are determined by the questions researchers want Quote: to answer” (Lefrancois, 2012, p. 28). Electronic Copy: Author, A. (Year of publication). Title of book: Subtitle of book [Electronic version]. Retrieved from https://content.ashford.edu/ Example: Witt, G. A., & Mossler, R. A. (2010). Adult development and life assessment [Electronic version]. Retrieved from https://content.ashford.edu/ In-Text Citation: “Quote” (Witt & Mossler, 2010, Section 0.0, “Section Title,” para. #).
- 47. Reprinted Material in an Anthology or Collection When using an article or story from a collection of works (such as an anthology), look to see if the article is a reprint. This information is usually found in the table of contents, and/or at the beginning of the paper, article, or story. If the year is listed, cite both the original publication year and the year of the published collection within the citation, and in the in-text citation, as shown: 19 Template: Author, A. (Anthology Publication Date). Title of article, not capitalized. In A. Editor & B. Editor (Eds.), The title of anthology (pp. xx–xx). City, State Abbreviation: Publisher. (Original work published in YEAR). Example: King, S. (2010). Why we crave horror movies. In J. Nadell, J. Langan, & E. A. Comodromos (Eds.), The Longman reader: Rhetoric, reader, research guide & handbook (12th ed.) (pp. 402-403). Boston, MA: Houghton Mifflin. (Original work published 1982) Sample
- 48. Quote: “I think that we’re all mentally ill: those of us outside the asylums only hide it a little better—and maybe not all that much better, after all” (King, 1982/2010, p. 402). Online Sources Online Scholarly Journal Article with DOI DOI stands for digital object identifier, which is a unique alpha- numeric code (usually starting with the number 10 and containing a suffix and a prefix assigned to a published article). When a DOI is available, use this code instead of the URL. This information is important to consider as you cite sources retrieved from the Ashford University Library. Template: Author, A. A. (Year of publication). Title of article. Title of Periodical, Volume (issue number if available), page range/number. doi: xx.xxxx/x.xxx- xxxx.xxxx.xxx.x Example: Sanderson, C., Lobb, E. A., Mowll, J., Butow, P. N., McGowan, N., & Price, M. A. (2013). Signs of post-traumatic stress disorder in caregivers following an expected death: A qualitative study. Palliative Medicine, 27(7), 625–31. doi: 10.1177/0269216313483663 Sample Quote:
- 49. “The power of the experience is suggested by frequent use of words connoting physical impact, and sometimes associated expressions of pain” (Sanderson et al., 2013, p. 627). Online Scholarly Journal Article Without DOI Template: Author, A. A. (Year of publication). Title of article. Title of Periodical, Volume (issue number if available), xx–xx. Retrieved from URL (no end punctuation) Example: Eggerton, J. (2013). Chris Dodd takes his battle to the people. Broadcasting & Cable, 143(23), 8–9. Retrieved from http://heathnet.org Sample Quote: “We need to frame the debate more about the positive things we do and why piracy really hurts [consumers], in addition to whatever damage it does to our industry, to independent http://heathnet.org/ 20 filmmakers maybe more so than even the studios, as rough as it is on them” (Eggerton,
- 50. 2013, p. 8). Online Newspapers or Magazines When using an online article from the Internet that is accessible to the general public, include the direct URL. Template: Author, A. (Year, Month and Day of publication). Title of internet article. Title of Newspaper or Magazine. Retrieved from URL Example: Egan, S. (2009, July 8). Using a robot to ease a child’s pain. The New York Times. Retrieved from http://well.blogs.nytimes.com/2013/07/09/using- a-robot-to-ease-a- childs-pain/?hp Sample Quote: Egan (2009) noted, “Health care workers have a new tool to ease needle anxiety in children: a talking robot” (para. 1). Web Article, No Author This section is important because you may be asked to research articles related to current events, using a general web search (non-library based). To understand how to cite articles without authors listed, consider both examples: Citing an Entity or Organization If an author is not listed, cite the organization or entity that
- 51. authored the article. In some cases, the author and entity cannot be determined, therefore, place the organization or entity in the author position. For example, organizations can include the Centers for Disease Control and Prevention, the American Cancer Society, American Heart Association, etc. Template: Entity or Organization. (Year of publication). Title of article. Retrieved from URL Example: Centers for Disease Control and Prevention. (2013). Prescription painkiller epidemic among women. Retrieved from http://www.cdc.gov/media/dpk/2013/dpk- Prescription%20drug%20overdose.html Sample Quote: According to the Centers for Disease Control and Prevention (2013), “Women are dying from prescription painkiller overdoses at rates never seen before, according to a new CDC Vital Signs” (para. 1). Citing All Other Online, Unauthored Articles http://well.blogs.nytimes.com/2013/07/09/using-a-robot-to- ease-a-childs-pain/?hp http://well.blogs.nytimes.com/2013/07/09/using-a-robot-to- ease-a-childs-pain/?hp http://www.cdc.gov/media/dpk/2013/dpk- Prescription%20drug%20overdose.html
- 52. http://www.cdc.gov/media/dpk/2013/dpk- Prescription%20drug%20overdose.html 21 As noted, if the author and entity cannot be determined, place the title of the article in the author position. Template: Title of article. (Year of publication). Retrieved from URL Example: Egypt gets new prime minister. (2013). Retrieved from http://news.msn.com/world/egypt- gets-a-new-prime-minister-billions-in-aid Sample Quote: “Egypt named an interim prime minister on Tuesday and rich Gulf states poured in $8 billion in aid, as the biggest Arab nation sought ways out of a crisis a day after troops killed dozens of Islamists” (“Eygpt gets new prime minister,” 2013, para. 1). Instructor Guidance in an Ashford Online Course Template: Instructor, A. A. (Year of upload). Course ID: Week X Title of module. Retrieved from
- 53. URL Example: Lienau, M. (2013). EDU 623: Introduction to teaching and learning: Week 1 instructor guidance. Retrieved from myeclassonline.com Sample Quote: “NCLB sets forth a framework of accountability for all schools in four areas. Schools must meet the required accountability level in each of the four areas to ‘meet the criteria’ for the year” (Lienau, 2013, para. 22). Note: Provide the general URL “myeclassonline.com” because AUO’s eCollege courses are password protected, and therefore not available to the general public. Reports Federal Government Agency Template: Author, A. A., Author, B. B., & Author, C. C. (Year). Title of report (Report number, if applicable). Retrieved from [website information and URL or database]. Example: Lingenfelter, P. E., Wright, D. L., & Bisel, T. M. (2005). State higher education finance, FY 2004 (SHEF Report). Retrieved from http://www.sheeo.org Sample
- 54. Quote: “The Consumer Price Index for All Urban Consumers (CPI-U) in the Chicago-Gary- Kenosha area increased 0.5 percent in May, the U.S. Bureau of Labor Statistics reported” (Bureau of Labor and Statistics, 2013, para. 1). http://news.msn.com/world/egypt-gets-a-new-prime-minister- billions-in-aid http://news.msn.com/world/egypt-gets-a-new-prime-minister- billions-in-aid http://www.sheeo.org/ 22 Blogs Blogs are not considered scholarly sources, but on occasion, you may find a blog written by an expert who contributes to your research. If the author’s name is not listed (a practice common in blogs) include the screen name, as illustrated below: Template: Blog Title (Year, Month and Day of publication). Title of article [Blog post]. Retrieved from URL Example: Internet Time Blog (2013, July 08). I wouldn’t call it informal learning [Blog post].
- 55. Retrieved from http://www.internettime.com/ Sample Quote: “Better I should have talked about Experiential Learning, for that’s the informal learning with the most impact. People learn by doing” (Internet Time Blog, 2013, para. 4). 23 Audiovisual Materials If the video is embedded in the course and is retrieved from an outside resource that AU has an account for but students cannot directly access (e.g., Intelecom videos), include the name of the database or video library in the retrieval element and provide context for students on the line below the reference that states “This video is available [can be accessed] through your online course.” Personal Communication Personal Communications: Interviews, Personal
- 56. Correspondences, Emails Personal communications such as interviews, personal correspondences (phone call, meetings), and emails are considered non-published sources because the material cannot be retrieved; therefore, do not list personal communication on the references page. List the individual providing the quote (i.e., interviewee), the words personal communication, and the date the discussion took place, as shown here: Example: (D. Williams, personal communication, August 1, 2012). Please cite this document as follows: Lassitter, S., & Richardson, J. (2013). APA made easy. Unpublished manuscript, College of Education, Ashford University, Clinton, IA. Template: Producer, A. (Producer). (Year). Title of video [Description]. Retrieved from [URL or database]. Examples: American Psychological Association. (Producer). (2000). Behaviorism [Video file]. Retrieved from http://www.xxx Bodrova, E. (Writer) & Davidson, F. W. (Producer). (2000). Building literacy competencies in early childhood [Video file]. Retrieved from the Films On Demand database.
- 57. Note: If students can readily access the material online, the URL would appear in the retrieval element of the reference. If they cannot readily access online, the database information would be stated in the retrieval element of the reference (e.g., Films On Demand). APA Made Easy:A Student’s Guide to APA FormattingAshford Writing CenterJune 2014**Revised bi-annually for clarity and modification.Adapted by the AWC from original, created by Dr. Stephanie Lassitter, College of Education, and Jennifer Richardson, Curriculum and Innovation DivisionCenters for Disease Control and Prevention. (2013). Prescription painkiller epidemic among women. Retrieved from http://www.cdc.gov/media/dpk/2013/dpk- Prescription%20drug%20overdose.htmlLingenfelter, P. E., Wright, D. L., & Bisel, T. M. (2005). State higher education finance, FY 2004 (SHEF Report). Retrieved from http://www.sheeo.org 1 ESSAY TITLE Magazine, online edition Online journal article, with DOI Entry from edited anthology, print YouTube video
- 58. Photograph, no date, no photographer Photograph, with photographer References Apsolon, M. [markapsolon]. (2011, September 9). Real ghost girl caught on Video Tape 14 [Video file]. Retrieved from http://www.youtube.com/watch?v=6nyGCbxD848 Batchelder, A. (2010, July 6). Students brains are being digitally rewired [Web log post]. Retrieved from http://literacyispriceless.wordpress.com/ Cayman Islands. (2008). The world factbook. Retrieved from http://www.bartleby.com/br/151.html Cendrowicz, L. (2010, July). Will Europe's bank stress tests bring calm or spread more fear? Time. Retrieved from http://www.time.com/time/business/article/0,8599,2005557,00.h tml Diaz-Rico, L. T. (2008). A course for teaching English learners. Boston, MA: Pearson. Florian, R. V. (2010). Challenges for interactivist-constructivist robotics. New Ideas in Psychology, 28(3), 350–353.
- 59. doi:10.1016/j.newideapsych.2009.09.009 Guthrie, W. (2007). This land is your land. In R. DiYanni (Ed.), Literature: Reading fiction, poetry, and drama (6th ed.) (pp. 897–898). New York, NY: McGraw-Hill. Kulbis, M. (Photographer). (2006). Men pray [Photograph]. Retrieved April 12, 2006, from: http://accuweather.ap.org/cgi-bin/aplaunch.pl Lessard v. Schmidt, 349 F. Supp. 1078 (E.D. Wis. 1972). Mawson, C. O. S. (Ed.). (n.d.). Roget's international thesaurus of English words and phrases. Retrieved from http://www.bartleby.com/br/110.html McLaren, M., Thomas, J. (Producers), & Linklater, R. (Director). (2006). Fast food nation [Motion picture]. United States: Fox Searchlight. Nelson Mandela [Photograph]. (n.d.). Retrieved January 10, 2014, from: http://www.nobelprize.org/nobel_prizes/peace/laureates/1993/m andela-bio.html Web log / Blog Online encyclopedia Book, print
- 60. Online dictionary Film Court decision 2 ESSAY TITLE Online journal article, without DOI Magazine, print Newspaper, online edition Website entry, corporate/government author Santovec, M. (2008). Easing the transition improves grad retention at Trinity U. Women in Higher Education, 17(10), 32. Retrieved from http://www.wihe.com/ Sloan, C., Booth, S., & Tate, A. (2010, July). Why I became an American. Real Simple, 186– 192. Tobin Ramos, R. (2010, July 22). UPS profit nearly doubles in second quarter. The Atlanta Journal-Constitution. Retrieved from http://www.ajc.com
- 61. U.S. Department of Labor, Bureau of Labor Statistics. (2008). Police and detectives. Retrieved from http://www.bls.gov/oco/pdf/ocos160.pdf Witt, G. A., & Mossler, R. A. (2010). Adult development. Retrieved from https://content.ashford.edu/books/4 Ashford textbook, online Running head: TITLE 1 TITLE 3 Title Name Course Instructor
- 62. Title References Authentic Assessment Project (AAP) Jan 2017 Background Information for World-Wide Trading Company World-Wide Trading Company (WWTC) is a large online broker firm in the Hong Kong. The trading company has a staff of 9,000 who are scattered around the globe. Due to aggressive
- 63. growth in business, they want to establish a regional office in New York City. They leased the entire floor of a building on Wall Street. You were selected as a contractor (your group) to build a state of the art high availability, secure network. The President of the company asked you to set up the state of the art network by end of this year. He shared with you the organizational structure and a list of the 100 employees. The current floor of the new site is solid and gigabit network can be set up on existing network wiring. Also, the existing power supply will meet the client’s current and future demand. The President has required these business goals: Business and Technical Goals · Increaserevenue from 10 billion to 40 billion in three to four years · Reduce the operating cost from 30 to 15 percent in two to three years by using an automated system for buying and selling. · Provide secure means of customer purchase and payment over Internet. · Build a high availability, moderate confidentiality and moderate integrity unclassified network (based on The National Institute of Standards and Technology- NIST) · Build a classified network with high confidentiality, moderate integrity, and moderate availability (based on NIST) · Allow employee to attach their notebook computers to the WWTC network and wireless Internet services. · Provide state of the art VoIP and Data Network · Provide Active Directory, DNS, and DCHP services · Provide faster Network services · Provide fast and secure wireless services in the lobby, conference rooms (100x60), and the cubical areas. On the basis of these business goals, your group is responsible for designing, configuring, and implementing fast, reliable and secure networks (classified and unclassified).
- 64. WWTC LAN/WLAN/VoIP · Propose a secure network design that solves the network and security challenges, to meet business needs, and the other technical goals. You are also required to provide a modular and scalable network. Provide redundancy at building core layer, building distribution layer, and access layer to avoid single point of failure. For Building Access layer provide redundant uplinks connection. · Select appropriate Cisco switch model for each part of your enterprise campus model design from the Cisco Products Link, and use the following assumptions in your selection process: 1. Selecting the Access layers’ switches: 0. Provide one port to each device 0. Make provision for 100% growth 1. Server farm switches a. Assume 6 NIC cards in each server and one NIC card uses one port of switch b. Dual processors and dual power supply · Propose an IP addressing redesign that optimizes IP addressing and IP routing (including the use of route summarization). Provide migration provision to IPv6 protocol in future. · Propose a High Level security plans to secure key applications and servers but encryption of all application is not acceptable. Develop security policy to stop sniffing and man-in-the-middle attack. Your security plan must be based on current industry standards. Multilayer security or defense-in-depth.
- 65. · Integrate voice and data network to reduce cost. For dialing outside, the World-Wide Trading Company proposes a plan for 100% connectivity with a minimum number of outside lines. For telephone requirements, see the Organization Chart and Telephone Equipment Table. · Provide state of the art VoIP and Data Network. · Provide aggregate routing protocols with hierarchal IP scheme. · Centralize all services and servers to make the network easier to manage and more cost-effective. · Provide LAN speed minimum 100 MB and Internet speed minimum 54 MB. · Provide wireless network access to network users and guest users with a minimum 54 Mbps of bandwidth. (You can assume that site survey is done and no sources of interference or RF were discovered.) · Provide provisions for video conference and multicast services. · Standardize on TCP/IP protocols for the network. Macintoshes will be accessible only on guest notebook but must use TCP/IP protocols or the Apple Talk Filling Protocol (AFP) running on top of TCP. · Provide extra capacity at switches so authorized users can attach their notebook PCs to the network · Configure DHCP on notebook PCs · The World-Wide Trading Company will use the following
- 66. applications/services: · Microsoft Office 365 plan (Office 2016, Exchange, Active Directory, SharePoint, One Drive, and Skype for Business) · Sending and receiving e-mail · Accessing the library card-catalog · File Server application. · Adobe Pro · Secure Zip · Associate will use the following Custom Applications · Market Tracking Application. This application will provide real-time status of stock and bond market to brokers and their clients. · Stock and Bond Analytical Application. This application will provide analysis of stock and Bond to Brokers only. · On Line Trading. The Company wishes to train new clients in online trading to attract new customer. The Company will sign up new client to receive streaming video and instructions Assume any information (with proper justification) which you think is missing and critical to the development of the design. WWTC Security WWTC has strong security requirements to ensure strong authentication, data confidentiality and separations between internal protected server and public server. Classified Network In addition to the required unclassified network, WWTC is requiring a classified network: 0. The classified network must be physically separated from the unclassified network. 0. Only VPs and Department heads are allowed to access the classified network
- 67. 0. Control should be put in place to prevent local users from accessing the classified network or removing data in any way. This includes removing media, AV recorders, pen and paper, and any form of printer. 0. All data transmitted on the classified network must be cryptographically protected throughout the network (Crypto devices are highly recommended). 0. All classified data must be centrally stored and secured in a physically separate area from the unclassified network. 0. The classified network is used for classified email only. WWTC needs to be able to send classified email from the NYC office to their HQ office. 0. No redundancy, AD, Wireless, or VoIP required for the classified network – just a simple network for classified email only. Unclassified Network: The security design must ensure: · Confidentiality, Integrity, and Availability of the data · Physical, Logical, and Administrative security controls · Secure e-mail used to communicate business sensitive information. · Confidential business information and public data are not connected to the same physical network. · the use of two-factor authentication mechanism is enabled. · Sensitive business information must not be transmitted in clear text between server and client. Secure WAN Connectivity In addition to the cryptographic protections of the data within the classified network, all data crossing wide-area links should undergo another layer of cryptographic protection such as IPSec/VPN/SSL.
- 68. Public Servers All public servers must be configured HTTPS connections and accept all requests that are on valid IP addresses and pass through firewall. Server must ask some identity of the connecting party. Site-to-site VPN tunnels All devices must be mutually authenticated and cryptographic protection should be provided. User Education All users should undergo periodic user awareness security training program on network threats and good security practices. Other Security Deliverables: 1. Determine the most important assets of the company, which must be protected 1. Determine general security architecture for the company 1. Develop a list of 12 specific security policies that could be applied. 1. Write specific details along with the rationale for each policy 1. Integrate and write up the final version of the Security Policy Document for submittal 1. Develop a High availability secure design for this locations addressing above considerations and mitigating 4 primary networks attacks categories mentioned below. Protect the Network from Four Primary Attack Categories: 1. Reconnaissance attacks: An intruder attempts to discover and map systems, services, and vulnerabilities. 2. Access attacks: An intruder attacks networks and systems to retrieve data, or gain access, or escalate access privileges 3. Denial of Service attacks: An intruder attacks your network
- 69. in a way that damages or corrupts your computer system or denies you and others access to your networks, system, or services. 4. Worms, viruses, and Trojan horses: Malicious software is inserted onto a host in order to damage a system, corrupt a system, replicate itself, or deny services or access to networks, system or services. Sample Security Policies: 1. Policies defining acceptable use 2. Policies governing connections to remote network 3. Polices outlining the sensitivity level of the various types of information held within an organization 4. Policies protecting the privacy of the network’s user and any customer data 5. Policies defining security baselines to be met by devices before connecting them to the network. 6. Policies for incident response handling WWTC Active Directory Design WWTC office at New York is largely autonomous and few IT personnel to take care of day-to-day IT support activities such as password resets troubleshoot virus problems. You are concerned about sensitive data store in this location. You want to deploy a highly developed OU structure to implement security policies uniformly through GPO automatically at all domains, OU, and workstations. At this location Windows Server 2012 R2 is required providing the following 10 AD features: 1. Use BitLocker encryption technology for devices (server and Work station) disc space and volume. 2. Enables a BitLocker system on a wired network to automatically unlock the system volume during boot (on capable Windows Server 2012 R2 networks), reducing internal help desk
- 70. call volumes for lost PINs. 3. Create group policies settings to enforce that either Used Disk Space Only or Full Encryption is used when BitLocker is enabled on a drive. 4. Enable BranchCache in Windows Server 2012 for substantial performance, manageability, scalability, and availability improvements 5. Implement Cache Encryption to store encrypted data by default. This allows you to ensure data security without using drive encryption technologies. 6. Implement Failover cluster services 7. Implement File classification infrastructure feature to provide automatic classification process. 8. IP Address Management (IPAM) is an entirely new feature in Windows Server 2012 that provides highly customizable administrative and monitoring capabilities for the IP address infrastructure on a corporate network. 9. Smart cards and their associated personal identification numbers (PINs) are an increasingly popular, reliable, and cost- effective form of two-factor authentication. With the right controls in place, a user must have the smart card and know the PIN to gain access to network resources. 10. Implement Windows Deployment Services to enables you to remotely deploy Windows operating systems. You can use it to set up new computers by using a network-based installation. Other AD Deliverables: · Create Active directory infrastructure to include recommended features · Create OU level for users and devices in their respective OU · Create Global, Universal, Local group. Each global group will contain all users in the corresponding department. Membership in the universal group is restrictive and membership can be assigned on the basis of least privileged principle. (For design
- 71. purpose, you can assume that WTC as a Single Forest with multiple domains). · Create appropriate GPO and GPO policies and determine where they will be applied. Reference: WWTC Organization Chart VP of Operation (CIO, CFO, CHRO) Regional VPs: VP NW USA, VP SW USA, VP NE USA, VP SE USA, VP M USA Note: WWTC is opening an office only at New York location. Please do not confuse Office holder’s title (VP NW USA) with the location. Table: -1 Sample Equipment Inventory (this is just a sample; you would need to insert your own equipment and comments) Subnet Offices Telephone Devices Comment VP OPR VP OPR Office 2 1 Work Stations CEO IT
- 72. 2 1 Work Stations CEO FIN 2 1 Work Stations CEO HR 2 1 Work Stations CEO IT’s Staff 2 1 Work Stations CEO FIN’s Staff 2 1 Work Stations CEO HR’s Staff 2 1 Work Stations VP NW USA, VP Office 2
- 73. 2 Work Stations Manager 1 2 2 Work Stations Manager 2 2 2 Work Stations Broker 1 2 2 Work Stations Broker 2 2 2 Work Stations Broker 3 2 2 Work Stations Broker 4 2 2 Work Stations Staff 2 2
- 74. Work Stations VP SW USA VP SW Office 2 2 Work Stations Manager 1 2 2 Work Stations Manager 2 2 2 Work Stations Broker 1 2 2 Work Stations Broker 2 2 2 Work Stations Broker 3 2 2 Work Stations
- 75. Broker 4 2 2 Work Stations Staff 2 2 Work Stations VP NE USA VP NE Office 2 2 Work Stations Manager 1 2 2 Work Stations Manager 2 2 2 Work Stations
- 76. Broker 1 2 2 Work Stations Broker 2 2 2 Work Stations Broker 3 2 2 Work Stations Broker 4 2 2 Work Stations Staff 2 2 Work Stations VP SE USA VP SE Office 2 2 Work Stations Manager 1
- 77. 2 2 Work Stations Manager 2 2 2 Work Stations Broker 1 2 2 Work Stations Broker 2 2 2 Work Stations Broker 3 2 2 Work Stations Broker 4 2 2 Work Stations Staff 2 2 Work Stations
- 78. VP M USA VP M Offices 2 2 Work Stations Manager 1 2 2 Work Stations Manager 2 2 2 Work Stations Broker 1 2 2 Work Stations Broker 2 2 2 Work Stations Broker 3 2 2
- 79. Work Stations Broker 4 2 2 Work Stations Staff 2 2 Work Stations Printer 20 At various offices. Exact location to be determined. Server WLC and AP ordering Guide Table 4. Sample Ordering Information for Cisco Wireless LAN
- 80. Controllers (you need to provide your own list) Product Features Customer Requirements Part Number Wireless LAN Controllers Cisco 4400 Series Wireless LAN Controller • Modular support of 12, 25, 50, or 100 Cisco Aironet access points • The Cisco 4402 with 2 Gigabit Ethernet ports supports configurations for 12, 25, and 50 access points • The Cisco 4404 with 4 Gigabit Ethernet ports supports configurations for 100 access points • IEEE 802.1D Spanning Tree Protocol for higher availability • IPSec encryption • Industrial-grade resistance to electromagnetic interferences (EMI) • For midsize to large deployments • High availability • AIR-WLC4402-12-K9 • AIR-WLC4402-25-K9 • AIR-WLC4402-50-K9 • AIR-WLC4404-100-K9 See the Cisco Wireless LAN Controllers Data Sheet for more information. Cisco 2100 Series Wireless LAN Controller • Supports up to 6, 12 or 25 Cisco Aironet access points • Eight Ethernet ports, two of which can provide power directly to Cisco APs • Desk mountable • For retail, enterprise branch offices, or SMB deployments • AIR-WLC2106-K9 • AIR-WLC2112-K9 • AIR-WLC2125-K9 See the Cisco 2106 Wireless LAN Controller Data Sheet for
- 81. more information. Cisco Catalyst® 6500 Series /7600 Series Wireless Services Module (WiSM) • Wireless LAN Controller for Cisco Catalyst 6500 or Cisco 7600 Series Router • Supports 300 Cisco Aironet access points • IPSec encryption • Industrial-grade resistance to electromagnetic interferences (EMI) • Intrachassis and interchassis failover • Interoperable with Cisco Catalyst 6500 Series Firewall and IDS services modules • Embedded system for the Cisco Catalyst 6500 Series and Cisco 7600 Series Router infrastructure • For large-scale deployments • High availability • WS-SVC-WISM-1-K9 • WS-SVC-WISM-1-K9= (spare) See the Cisco Catalyst Wireless Services Module Data Sheet for more information. Cisco Catalyst 3750G Integrated WLAN Controller • Cisco Catalyst 3750G Series Switch with wireless LAN controller capabilities • Modular support of 25 or 50 Cisco Aironet access points per switch (and up to 200 access points per stack*) • IPSec encryption • Industrial-grade resistance to electromagnetic interferences (EMI) • For midsize to large deployments • High availability • WS-C3750G-24WS-S25 • WS-C3750G-24WS-S50 See the Cisco Catalyst 3750G Integrated Wireless LAN Controller Data Sheet for more information. Cisco Wireless LAN Controller Module for Cisco Integrated Services Routers
- 82. • Wireless LAN controller integrated into Cisco integrated services routers • Supports 6, 8, 12, or 25 Cisco Aironet access points • Embedded system for Cisco 2800/3800 Series and Cisco 3700 Series routers • For retail, small to medium-sized deployments or branch offices • NME-AIR-WLC6-K9 • NME-AIR-WLC6-K9= (spare) • NME-AIR-WLC8-K9 • NME-AIR-WLC8-K9= (spare) • NME-AIR-WLC12-K9 • NME-AIR-WLC12-K9= (spare) • NME-AIR-WLC25-K9 • NME-AIR-WLC25-K9= (spare) See the Cisco WLAN Controller Modules Data Sheet for more information. Please refer to the Cisco Wireless LAN Controller Ordering Guide supplement to learn when to add the following SKUs to track the deployment of voice and context-aware mobility applications. Table 2. Cisco Aironet Indoor Rugged, Indoor, Wireless Mesh, and Outdoor Rugged Access Points Product Features Customer Requirements Part Number Indoor Rugged Access Points Cisco Aironet 1250 Series • Industry's first business-class access point based on the IEEE 802.11n draft 2.0 standard • Provides reliable and predictable WLAN coverage to improve the end-user experience for both existing 802.11a/b/g clients and new 802.11n clients
- 83. • Offers combined data rates of up to 600 Mbps to meet the most rigorous bandwidth requirements • Designed for both office and challenging RF environments • Especially beneficial for environments with the following characteristics: • Challenging RF environments (for example, manufacturing plants, warehouses, clinical environments) • Bandwidth-intensive applications (for example, digital imaging, file transfers, network backup) • Real-time, latency-sensitive applications such as voice and video • Need to support existing 802.11a/b/g and new 802.11n wireless clients Access point platform with pre-installed radio modules: • AIR-AP1252AG-x-K9: 802.11a/g/n-draft 2.0 2.4/5-GHz Modular Autonomous Access Point; 6 RP-TNC • AIR-AP1252G-x-K9: 802.11g/n-draft 2.0 2.4-GHz Modular Autonomous Access Point; 3 RP-TNC • AIR-LAP1252AG-x-K9: 802.11a/g/n-draft 2.0 2.4/5-GHz Modular Unified Access Point; 6 RP-TNC • AIR-LAP1252G-x-K9: 802.11g/n-draft 2.0 2.4-GHz Modular Unified Access Point; 3 RP-TNC See the Cisco Aironet 1250 Series Ordering Guide for more information. Cisco Aironet 1240AG Series • Second-generation 802.11a/g dual-band indoor rugged access point • 2.4-GHz and 5-GHz antenna connectors for greater range or coverage versatility and more flexible installation options using the broad selection of Cisco antennas available • Ideal for challenging indoor RF environments • Recommended for offices and similar environments • Ideal for deployments above suspended ceilings • Recommended for outdoors when deployed in a weatherproof NEMA-rated enclosure • AIR-AP1242AG-x-K9: 802.11a/g Nonmodular Cisco IOS
- 84. Software- Based Access Point; RP-TNC • AIR-LAP1242AG-x-K9: 802.11a/g Nonmodular LWAPP Access Point; RP-TNC See the Cisco Aironet 1240AG Series 802.11a/b/g Data Sheet for more information. Indoor Access Points Cisco Aironet 1130AG Series Low-profile, enterprise-class 802.11a/g access point with integrated antennas for easy deployment in offices and similar RF environments Ideal for offices and similar environments • AIR-AP1131AG-*X-K9 See the Cisco Aironet 1130AG Series Ordering Guide for more information. Wireless Mesh Access Points Cisco Aironet 1520 Series • Next-generation outdoor wireless mesh access point • Integrated dual band 802.11 a/b/g radios, Ethernet, fiber and cable modem interface • Provides easy and flexible deployments for outdoor wireless network • Available in a lightweight version only • Ideal for outdoors • Recommended for industrial deployments and local government, public safety, and transit agencies • AIR-LAP1522AG-X*-K9: See the Cisco Aironet 1520 Series Lightweight Outdoor Mesh Access Point Ordering Guide for more information. Cisco Aironet 1500 Series • Mesh access point that enables cost-effective, scalable deployment of secure outdoor wireless LANs for metropolitan networks or enterprise campuses • Available in a lightweight version only • Ideal for outdoors • Recommended for providing wireless services and applications to local government, public safety, and transit agencies
- 85. • AIR-LAP1510AG-*X-K9: • Cisco Aironet 1510AG Lightweight Outdoor Mesh Access Point, FCC configuration See the Cisco Aironet 1500 Series Ordering Guide for more information. Outdoor Rugged Access Points Cisco Aironet 1400 Series • High-speed, high-performance outdoor bridging solution for line-of-sight applications • Offers affordable alternative to leased-line services • Available in a standalone version only • High-speed building-to-building or campus connectivity • Share LAN/Internet access between two or more sites • Fast installation • AIR-BR1410A-*X-K9: With integrated antenna • AIR-BR1410A-A-K9-N: With N-Type connector for use with external antennas See the Cisco Aironet 1400 Series Bridge Data Sheet for more information. Cisco Aironet 1300 Series Outdoor access point/bridge offers high-speed and cost- effective wireless connectivity between multiple fixed or mobile networks and clients Ideal for outdoor areas, network connections within a campus area, temporary networks for portable or military operations, or outdoor infrastructure for mobile networks ● AIR-BR1310G-X-K9: With integrated antenna ● AIR-BR1310G-X-K9-R: With RP-TNC connector for use with external antennas ● AIR-BR1310G-A-K9-T: For transportation applications See the Cisco Aironet 1300 Series Ordering Guide for more information. *X = regulatory domain (Source: Curtsy Cisco Web site http://cisco.com/en/US/prod/collateral/wireless/ps5679/ps6548/
- 86. prod_brochure0900aecd80565e00_ps2706_Products_Brochure.h tml) WLC and AP Placement Templates Suggested Placement Table Wireless Network Building Access Point Requirements Wireless LAN Controller Requirements Total AP Total WLC Building Lobby Cafeteria Conference room
- 87. Suggested Product Table (WLC) WLC Cisco Part Number Quantity Cost Cisco 2100 Series Wireless LAN Controller AIR-WLC2106-K9 2 Suggested Product Table (AP) AP Cisco Part Number Quantity Cost Cisco Aironet 1250 Series
- 88. AIR-AP1252AG-x-K9: 802.11a/g/n-draft 2.0 2.4/5-GHz Modular Autonomous Access Point; 6 RP-TNC 20 VP OPER 10 staff CEO IT 20 Staff CEO HR 20 staff CEO FIN 2 Staff VP Operational Office President Manager 2 Manager 1 VP NW USA CEO HR CEO FIN CEO IT VPOPR Manager 2 Manager 1 VP SW USA Manger 2
- 89. Manager 1 VP M USA Manager 2 Manager 1 VP SE USA Manager 2 Manger 1 VP NE USA World-Wide Trading Company Organizational Chart VP Broker 4 Broker 3 Broker 2 Broker 1 3 staff Manager 2 Broker 4 Broker 3 Broker 2 Broker 1 3 Staff Manager 1 2 Staff Vice President Office