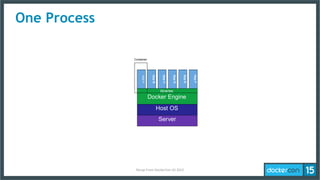
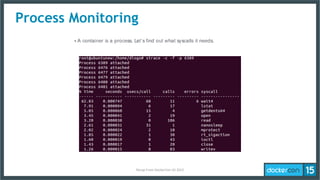
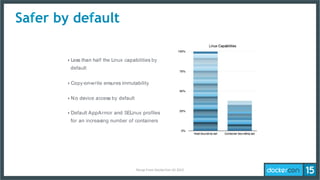
This document summarizes a presentation on Docker security and least-privilege microservices from DockerCon US 2015. It discusses the history and principles of least-privilege, how Docker supports fine-grained access controls for containers through features like namespaces, capabilities, and security profiles. It also covers making containers more secure by default and tools like Docker Bench for assessing container security. The conclusion is that Docker allows least-privilege microservices and better tools are still needed to define per-container security profiles.