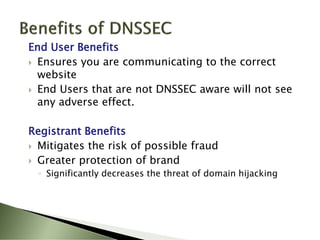
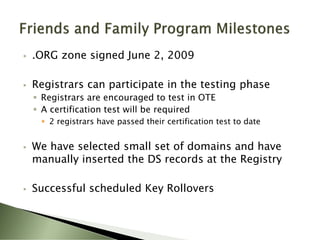
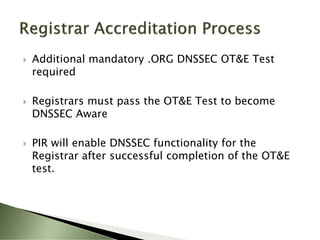
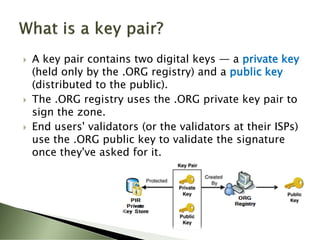
The document summarizes an upcoming webinar on DNSSEC hosted by .ORG, The Public Interest Registry and Afilias. The webinar will provide an introduction to DNSSEC including how it adds security and authentication to the Domain Name System to prevent forged DNS data. It will also discuss PIR's implementation timeline and test program for DNSSEC in the .ORG top-level domain.