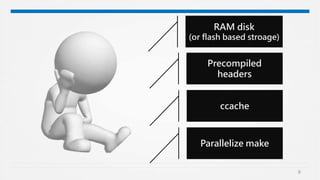
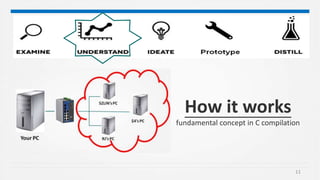
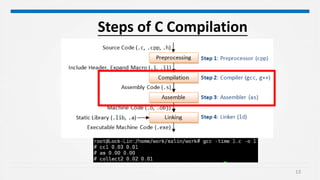
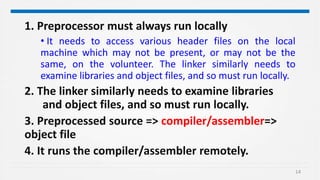
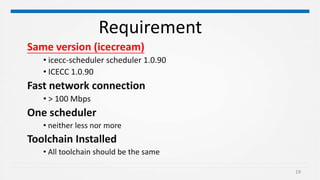
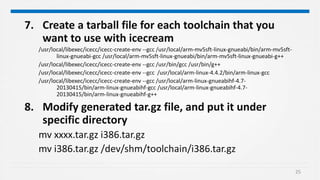
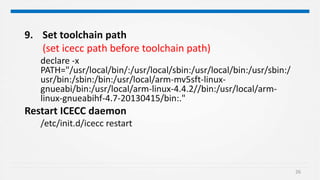
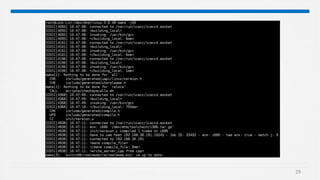
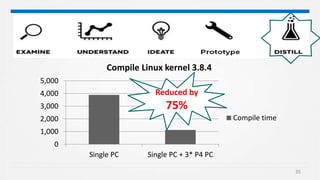
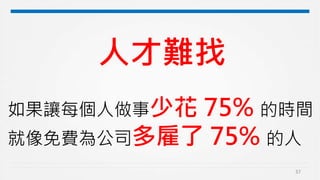
Icecc is a distributed compiler that allows compilation jobs to be distributed across multiple computers to reduce build times. It works by having one computer act as a scheduler that distributes preprocessing, compilation, and assembly jobs to other connected computers. The key requirements are that all computers must have the same toolchain installed and be on a fast network. Setting up Icecc involves configuring one computer as the scheduler, installing Icecc on all computers, and ensuring all toolchains are packaged and accessible in a shared location. Icecc has been shown to reduce Linux kernel compilation time by 75% by utilizing 3 additional computers during the build.