The document discusses the evolution of the ARM architecture, particularly focusing on the transition from ARMv7 to ARMv8, emphasizing improved performance and security features. It provides detailed information on memory layout, compatibility support, and the Linux kernel's integration with ARM64 architecture. Additionally, it includes practical steps for building a Debian root filesystem on ARM64 and addresses various programming considerations for developers transitioning from ARM32 to ARM64.

![3
Trends
That’s really what ARM has to look at when
defining a new architecture. That is the nature of
our business, we need to look a long way forward,
and plan.
Why ARMv8 instead of using ARMv7+ LPAE [11]](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-3-320.jpg)
![5
ARMv7 -> ARMv8 [2]
32-bit ARMv7-A
compatibility
Cryptography support
Dual Instruction set
architecture
Improved support for
virtualization](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-5-320.jpg)
![6
AArch32 (compat) Support [8]
Support ARMv7 Linux EABI for compat tasks
• Different set of system calls (unistd32.h)
• Compat user structures
• No SWP instruction, no unaligned LDM/STM
access
Supports both ARM and Thumb-2 32-bit user
tasks
Supports 32-bit ptrace
Address space limited to 4GB
Emulated vectors page
• ARM Linux EABI expects helper routines in the
vectors page accessible by user tasks](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-6-320.jpg)
![8
ARMv8-A Designed for Efficiency [2]
Enhancement Why it Matters
64-bit architecture Efficient access to large datasets
Increased number and size of general
purpose registers
Gains in performance and code
efficiency
Double the number and size of NEON
registers
Enhanced capacity of multimedia
engine
Cryptography support Over 10x software encryption
performance New security models for
consumer and enterprise](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-8-320.jpg)
![9
ARMv8-A Family [3]
Core Instruction cycle DMIPS/MHz
Processor
Architecture
big.LITTLE role
Cortex-A32 In-order execution 2.0 ~ 2.1 32 Unknown
Cortex-A35 In-order execution 1.78 64 little
Cortex-A53
In-order execution 2.24 64
little
Cortex-A57 Out-of-order
execution
4.6 64
big
Cortex-A72 Out-of-order
execution
4.72 64
big
Cortex-A73 Out-of-order
execution
4.8 64 big](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-9-320.jpg)
![10
The ARM Registers Comparison [4]
AArch32 AArch64 Remarks
32-bit General purpose registers r0 - r14 w0 - w30
aliased to lower half of each
64-bit register in AArch64
64-bit General purpose registers - x0 - x30
Program counter r15 aka. pc PC
not directly accessible in
AArch64
Zero register -
x31 / w31 aka. xzr /
wzr
in most instructions, except
as a base register for address
generation
Stack pointer r13 SP
encoded as x31 on address
generation
Procedure call link register r14 x30](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-10-320.jpg)
![11
ARMv7
name
AArch64/ARMv8
name
Remarks
Monitor mode EL3
highest exception level,
mostly for firmware
HYP mode EL2
exception level for
hypervisors like Xen (or
parts of KVM)
SVC mode EL1
the Linux kernel is
running in this
USR mode EL0 for unprivileged userland
The ARM Execution Mode [4][8]](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-11-320.jpg)
![12
Memory Layout [15]
AARCH64
It allows up to 4 levels of translation
tables with a 4KB page size and up to
3 levels with a 64KB page size.](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-12-320.jpg)
![13
Memory Layout [9][15]
32 bit address space:
• 4GB of virtual addresses
• 1MPages
• Each entry is 4 bytes (a 32 bit physical
address)
• Page size : 4kb](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-13-320.jpg)
![14
Memory Layout [14][15]
AArch64 Linux uses either 3 levels or 4 levels of
translation tables with the 4KB page
configuration, allowing 39-bit (512GB) or 48-
bit (256TB) virtual addresses, respectively, for
both user and kernel.
64 bit address space
• 16 exabytes(1018) of virtual address space
• 4PetaPages (1015)
• Entry is 8 bytes
• Page size : 4kb/ 64kb](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-14-320.jpg)
![15
Memory Layout [14][15]](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-15-320.jpg)
![16
Memory Layout [14]
With 64KB pages, only 2 levels of translation
tables, allowing 42-bit (4TB) virtual address,
are used but the memory layout is the same.](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-16-320.jpg)
![17
The ARM64 with Linux Kernel [5]
First patch in Kernel 3.7
Without real hardware
First ARM64 SoC supported in Kernel 3.11
2013/6
Second ARM64 SoC supported in Kernel 3.18
2014/12
Different assembly code/ ABI between ARM32/64
AArch64 is the name for the 64-bit ARM architecture](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-17-320.jpg)
![18
The ARM64 with Linux Kernel [5]
Device tree
arch/arm64/boot/dts/<vendor>/
Compressed Kernel
arch/arm64/boot/Image.gz
No more “arch/arm64/mach-<soc>” [7]
No more C files, all SoC features should be handled by drivers
Or it can go “drivers/soc” if it cannot fit an existing drivers
No more uImage [7]
Incompatible with multiplatform kernels
Switch to bootz command in bootloader](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-18-320.jpg)
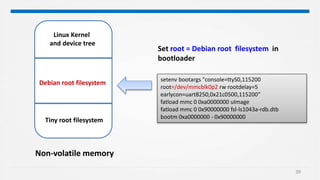
![19
The ARM64 with Debian [6]
First release in Debian 8
AARCH64 Toolchain in Debian
Package: crossbuild-essential-arm64
aarch64-linux-gnu-gcc
Build ARM64 Debian root filesytem via debootstrap](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-19-320.jpg)
![21
The QorIQ® LS1043A reference design board [13]](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-21-320.jpg)
![22
The QorIQ® LS1043A reference design board [13]](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-22-320.jpg)

![27
Build uImage – Failed in ARM64 [17]
> Bringing in uImage as a target on ARM might have
been a mistake, since
> now people want to bring in new targets for whate
ver boot format they
> happen to want. So it's a good idea to keep arm64 f
rom going down the
> same path and stick to the native, raw, formats.
mkimage -A arm64 -O linux -T kernel -C gzip -a 0x80080000 -e 0x80080000 -
n 4.1.0-ltsi-rt+ -d arch/arm64/boot/Image.gz uImage
No, there should be no uImage target on
arm64. Newer u-boots can
already boot an ARM zImage (through the
bootz command), and should be
enhanced as needed to boot a vmlinux if
needed.
However, we can still make uImage manually](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-27-320.jpg)

![42
ARM 64 Programming [16]
What is the different between 32 and 64 bits in C](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-42-320.jpg)
![43
ARM 64 Programming [16]
Pre-defined macros relating to ARMv8 compilation](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-43-320.jpg)
![44
ARM 64 Programming [16]
Bit manipulation operations
Any issue?](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-44-320.jpg)
![45
ARM 64 Programming [16]
Bit manipulation operations
“1” has int type…](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-45-320.jpg)
![46
ARM 64 Programming [16]
Indexes
Any issue?](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-46-320.jpg)
![47
ARM 64 Programming [16]
Indexes
size_t: 64 bit
unsigned int: 32 bit
Infinite loop](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-47-320.jpg)
![48
ARM 64 Programming [16]
Pointers and ints
Is p = q?](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-48-320.jpg)
![49
ARM 64 Programming [16]
Pointers and ints
1. For ARM32
p==q
2. For ARM64
p!=q](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-49-320.jpg)
![50
ARM 64 Programming [16]
Structure padding
What is the size
of structure in C ?](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-50-320.jpg)
![51
ARM 64 Programming [16]
Structure padding
1. For ARM32
int a : 4
long b: 4
int c: 4
Total = 12 bytes
2. For ARM64
int a : 4
long b: 8
int c: 4
Total = 20 bytes](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-51-320.jpg)
![52
ARM 64 Programming [16]
Structure padding
1. For ARM64
int a : 4
long b: 8
int c: 4
Total = 20 bytes
For double-word aligned, it needs to introduce four
bytes of padding between the end of the first ”int” and
the ”long”](https://image.slidesharecdn.com/embeddedlinuxdebianwitharm64platform-170207151853/85/Embedded-Linux-Debian-with-ARM64-Platform-52-320.jpg)