Embed presentation
Downloaded 546 times

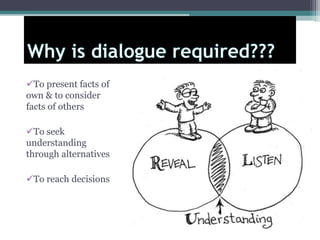



This document provides an overview of dialogue and what constitutes a good dialogue. It defines dialogue as a conversation between two or more people with a purpose, that is civilized, democratic, and constructive. A good dialogue involves presenting one's own facts and considering others' facts to seek understanding through alternatives in order to reach decisions. It should not be a monopoly where conversation is one-sided, but rather ideas and facts should be examined from multiple points of view. A praiseworthy dialogue shows respect for others' opinions and tries to understand their real thoughts, rather than just focusing on mistakes. It takes intelligence to recognize and admit the excellence in others' ideas.