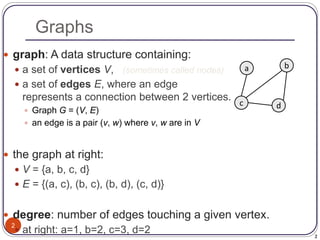
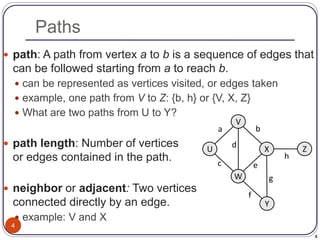
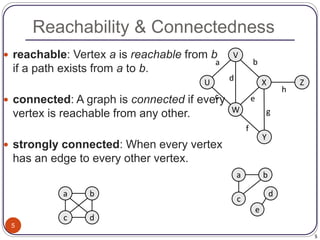
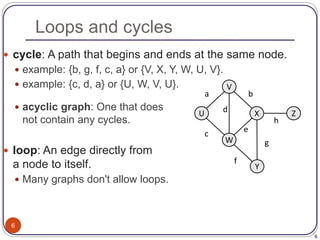
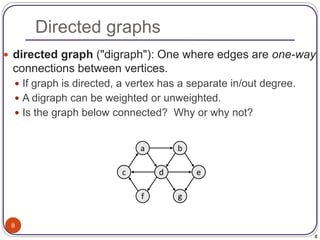
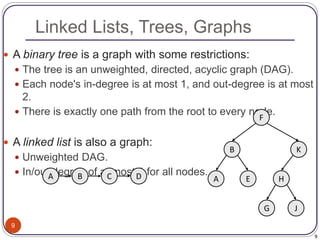
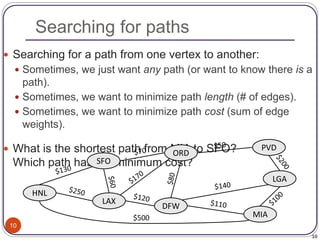
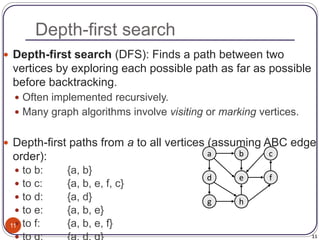
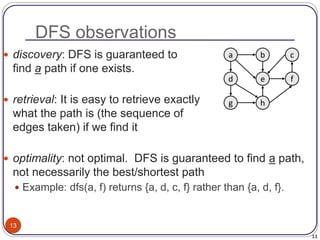
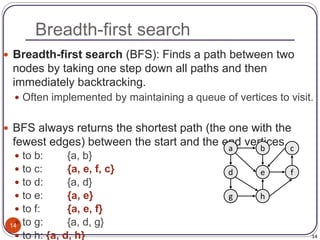
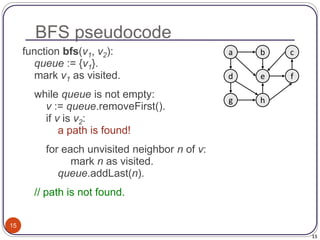
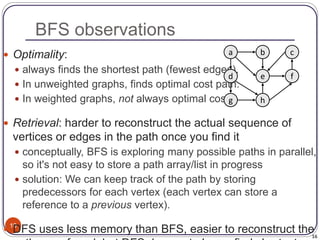
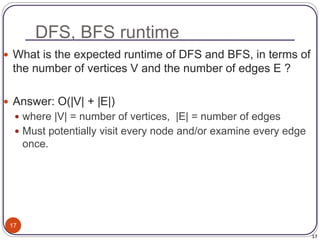
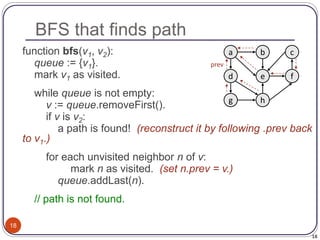
The document defines and provides examples of key concepts related to graphs and graph traversal algorithms. It describes what a graph is comprised of (vertices and edges), common graph types (directed/undirected, weighted/unweighted), graph terminology (degree, path, cycle, connectivity), and graph traversal algorithms like depth-first search (DFS) and breadth-first search (BFS). It provides pseudocode for DFS and BFS algorithms and analyzes their runtime and ability to find optimal paths.