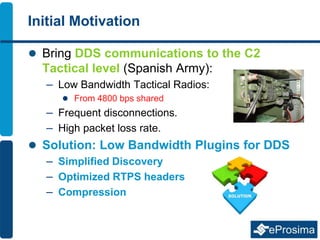
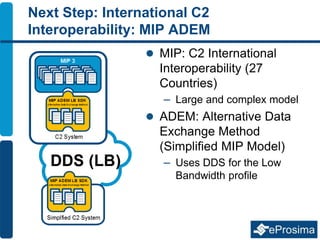
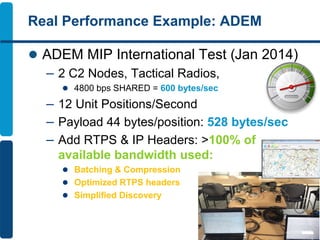
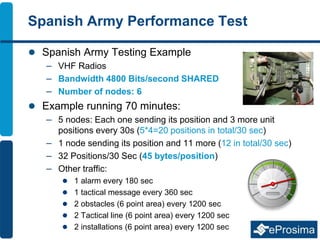
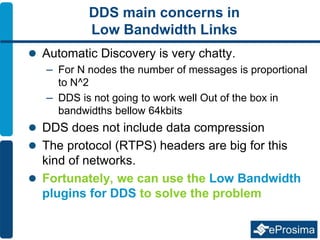
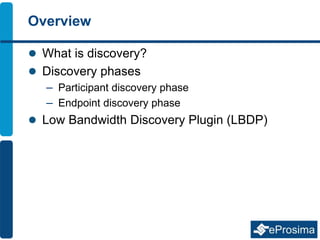
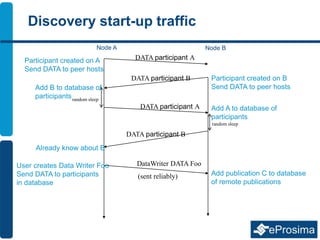
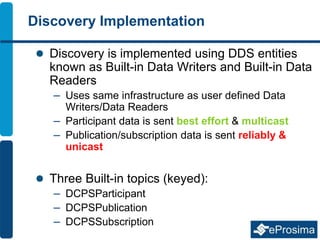
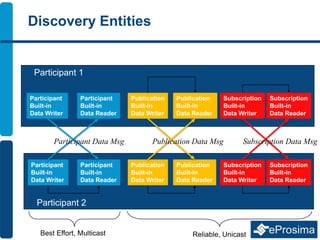
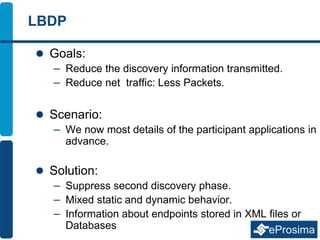
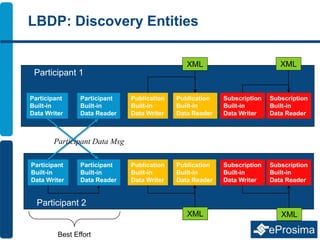
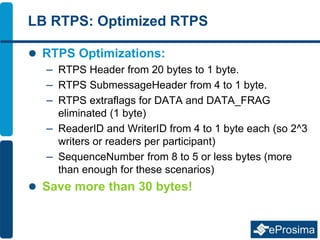
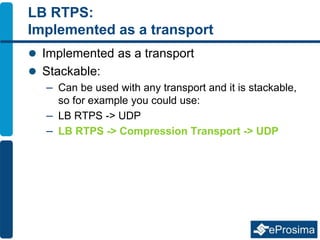
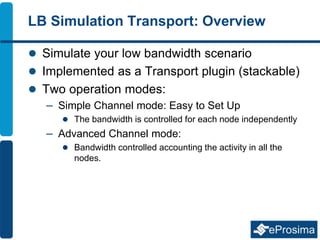
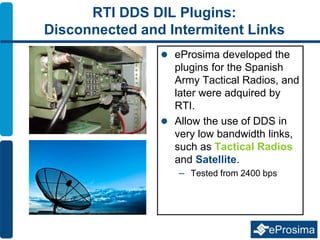
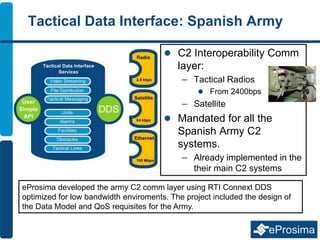
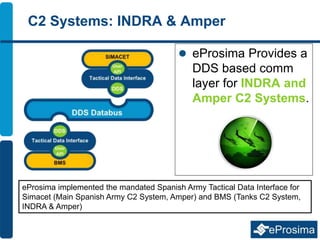
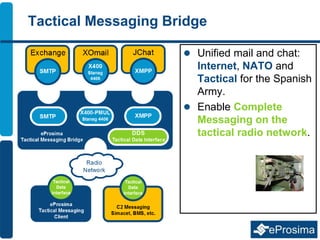
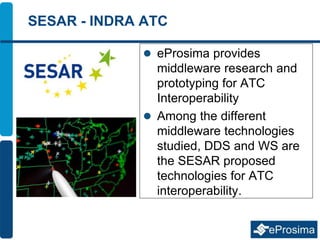
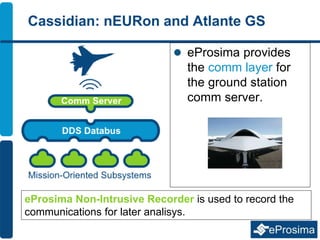
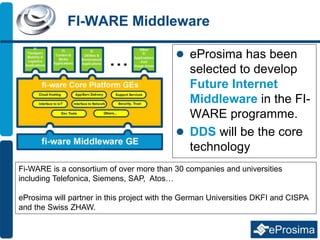
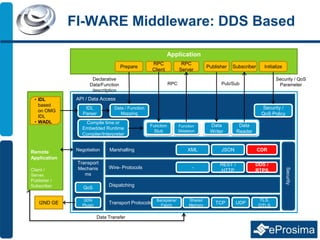
The document discusses Eprosima's expertise in DDS (Data Distribution Service) focused on low bandwidth communications for tactical environments, particularly for the Spanish army. It explains the development and implementation of various low bandwidth plugins to enhance DDS performance in scenarios with limited data transmission capabilities, such as tactical radios and satellites. The document also highlights successful case studies, including interoperability protocols and middleware solutions for command and control systems used by military and aerospace sectors.