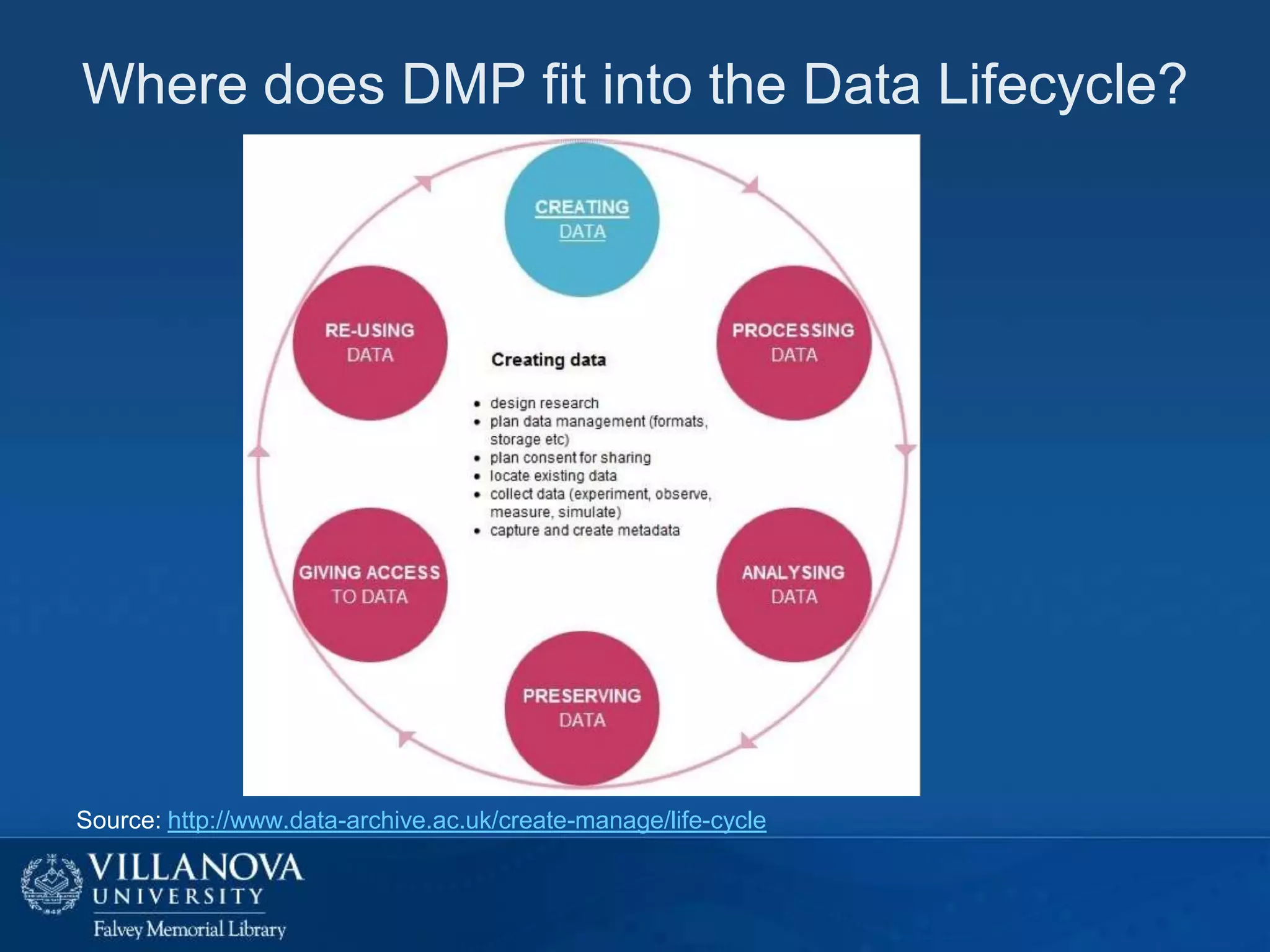
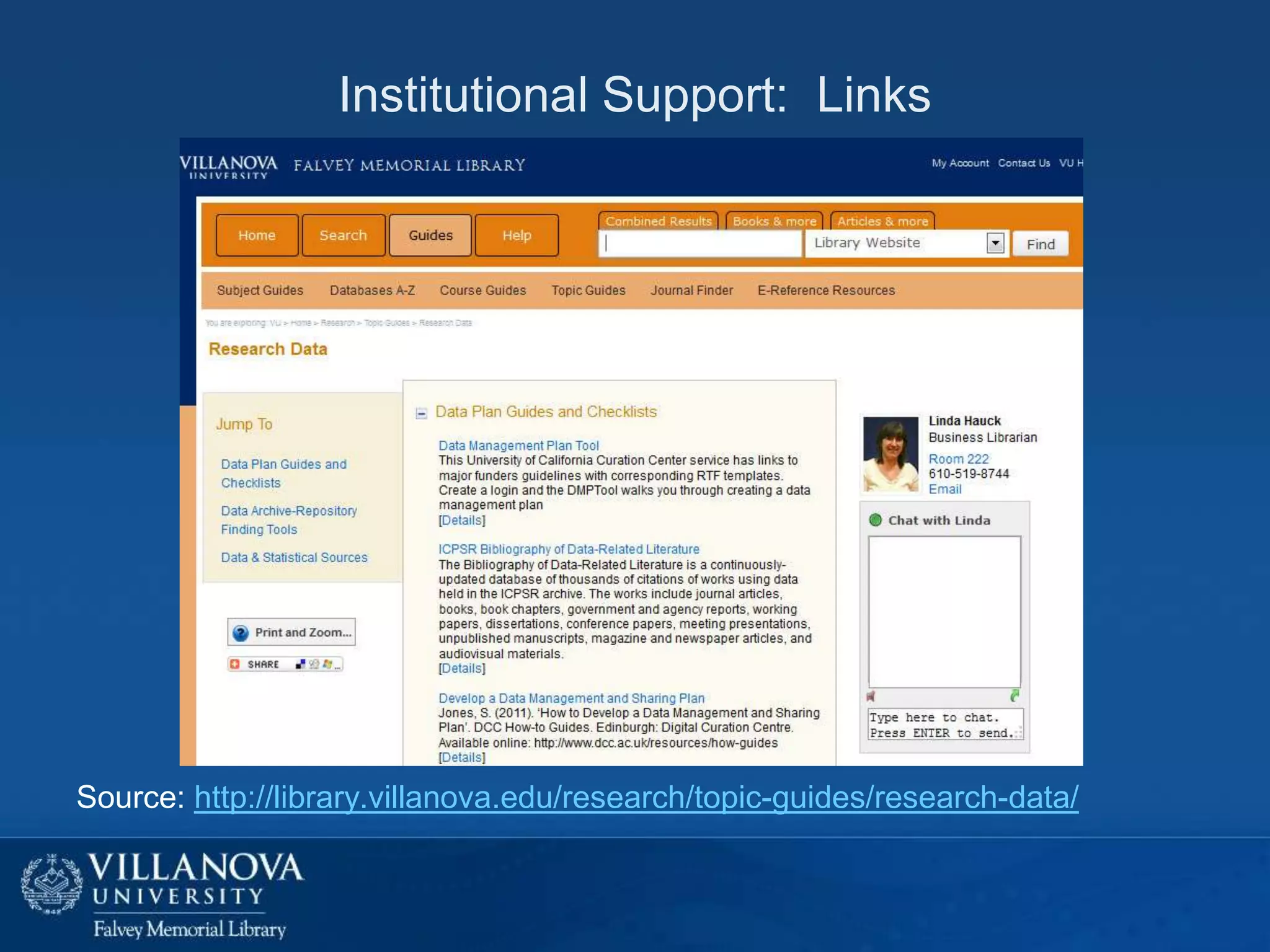
This document provides an overview of data management plans (DMPs), including their purpose, origins, requirements by major funders, and benefits. It discusses key components of DMPs such as the data types and standards, access and sharing policies, and long-term preservation. The document also examines researchers' attitudes toward DMPs and data sharing, which can include fears about misuse or losing competitive advantage. Finally, it poses questions about developing research data management services at Villanova University through collaboration between libraries, support services, and researchers.