The document outlines instructions for a cybersecurity research paper focusing on the TJX security breach incident, requiring a minimum of five authoritative sources. It details the vulnerabilities that led to the breach, including inadequate wireless security, improper data storage practices, and failure to encrypt customer data. Additionally, the paper emphasizes the lessons learned for auditors and retailers regarding data protection and compliance with industry standards.
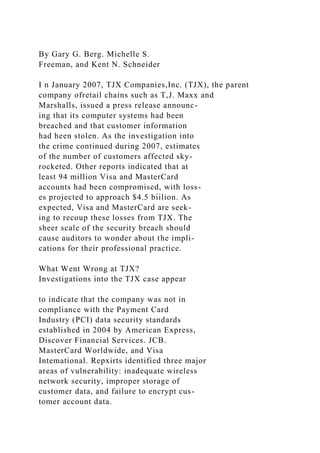


![encrypted, or the hackers stole the encryp-
tion key. In either case, industry standards
were not maintained hy TJX. PCI Data
Sectirity Standard 3.4 i-et]uires that at min-
imum, the customer's "primary account
number" (i.e.. the customer's card number)
be "rendered unreadable.'' Furtheniiore. PCI
Data Security Standards 3.5 and 3.6
nitjuire merchants to pnMect tlie encryption
keys used for protecting customer data from
disclosure and misuse.
How the TJX Breach Affects
Audit Practices
At firNt. the TJX fiasco appears to offer an
object lesson for retailers" IT departments,
rather tkui auditors. After all, aistomeni' cred-
it card numbeis are not the retailer's asset to
protect; rather, the sales transaction itself is
what accounting intentai controls have tradi-
tionally sought to secure. With the atlvent of
Statement on Auditing Standaitl (SAS) 109,
UnderstíUKÜng ¡Iw Entity and ¡ts Envimntnent
and Assessing the Risks of Material
Misstatemctu. internal control clearly
extends beyond protecting one's own assets.
SAS 109 requires auditors to "audit die
business, and not just the books'" when
evaluating the risks of a client's financial
statements containing a material misstate-
ment. Specifically, SAS 109 requires an
understanding of: 1 ) the entity and its envi-
ronment: 2) the entity's intemal control](https://image.slidesharecdn.com/cybersecurityresearchpaperinstructionsselectaresearchtopic-221114172946-00562589/85/Cybersecurity-Research-Paper-instructionsSelect-a-research-topic-docx-5-320.jpg)


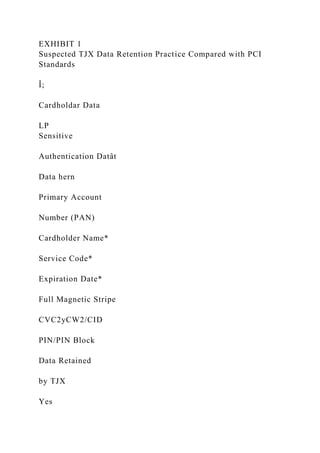
![Yes
Yes
Yes
Yes
Yes
Yes
PCI Retention
Standards
Yes
Yes
Yes
Yes
No
No
No
* Must be protected if stored in conjunction with PAN.
[. t Sensitive authenticaton data must not be stored after
authorization (even if encrypted].
EXHIBIT 2](https://image.slidesharecdn.com/cybersecurityresearchpaperinstructionsselectaresearchtopic-221114172946-00562589/85/Cybersecurity-Research-Paper-instructionsSelect-a-research-topic-docx-12-320.jpg)




![Differentiate yourself from other financial planners:
only a CPA can become a PFS
Access marketing tools to promote yourself and
increase new business
Receive media training and opportunities to participate
in public relations activities
Network with other thought leaders in the industry
:AICPA:
Menlion ptonio code RHX
Questions?
e-mail [email protected]
ISO Certified
AUGUST 2008 / THE CPA JOURNAL 37](https://image.slidesharecdn.com/cybersecurityresearchpaperinstructionsselectaresearchtopic-221114172946-00562589/85/Cybersecurity-Research-Paper-instructionsSelect-a-research-topic-docx-20-320.jpg)