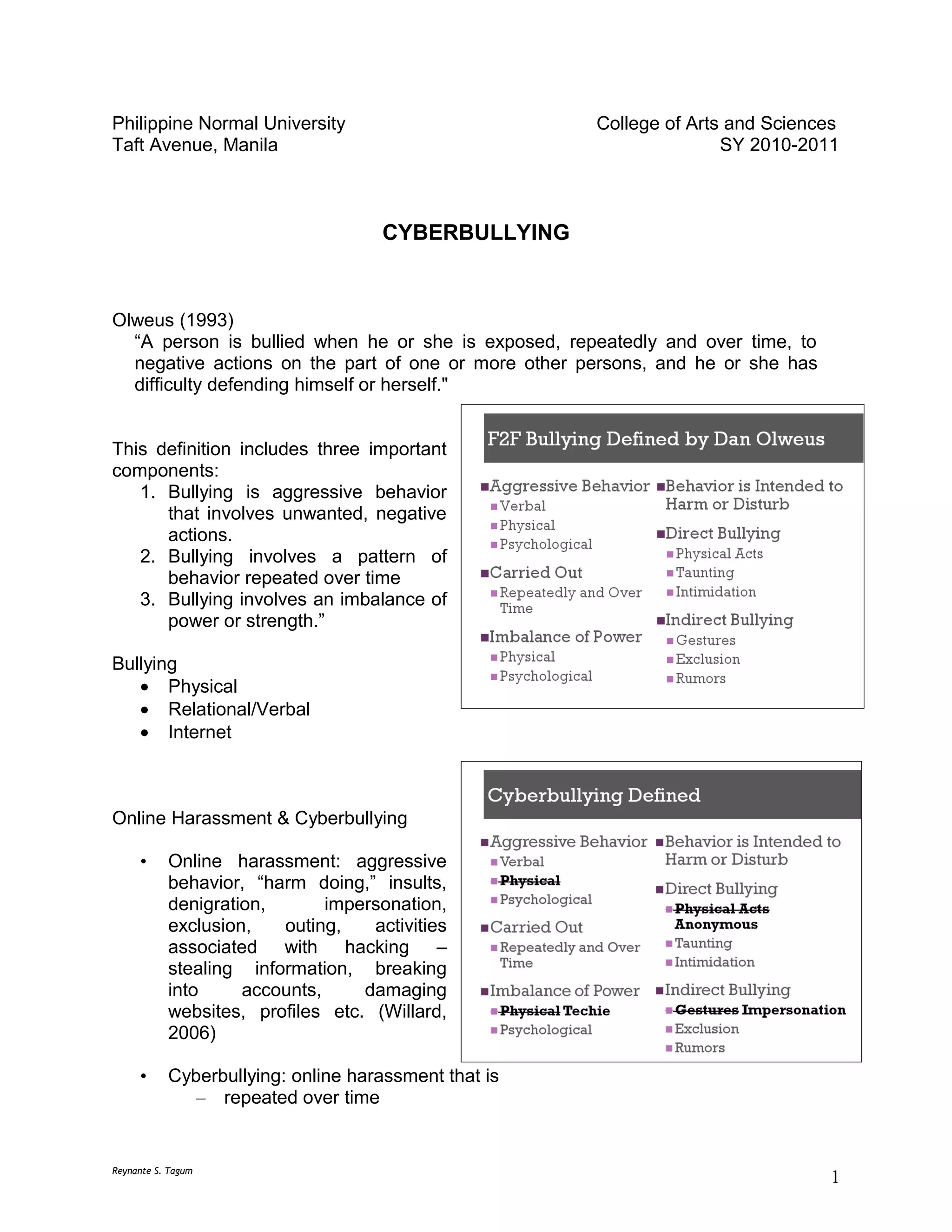
This document discusses cyberbullying and provides definitions and examples. It defines cyberbullying as repeated, hostile behavior online intended to harm others. Examples of different forms of cyberbullying are given such as flaming, harassment, denigration, impersonation, outing, trickery, exclusion, and cyberstalking. The impact of cyberbullying on victims is discussed, noting it can cause psychological harm. Ways to prevent cyberbullying are presented such as protecting private information online and finding new friends. The document also mentions bills in the Philippines aimed at addressing bullying in schools through policies. Experts recommend preventing bullying at the community level rather than just reacting to incidents.