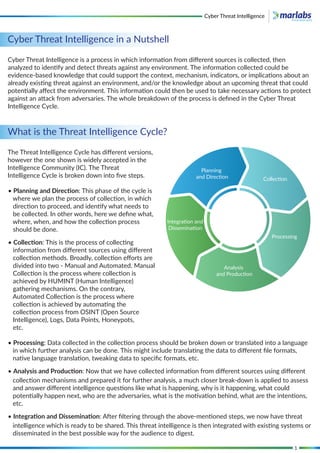
The document provides an overview of the cyber threat intelligence cycle, outlining its five key steps: planning and direction, collection, processing, analysis and production, integration and dissemination. It explains the different sources of threat intelligence, including the clear web, deep web, and dark web, while addressing the challenges organizations face in detecting and mitigating threats. The document also discusses the future of threat intelligence, emphasizing the role of advanced technology, artificial intelligence, and the importance of sharing information to enhance security.