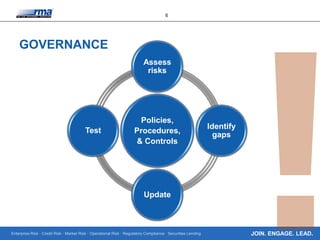
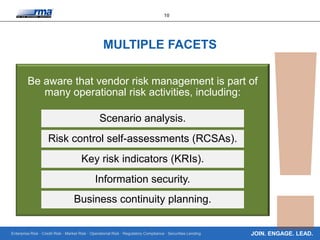
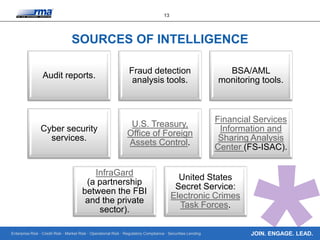
The document discusses the management of cyber security risks in financial institutions, emphasizing the importance of governance, vendor management, and incident response. It highlights the increasing sophistication of cyber attacks and the responsibility of banks to oversee vendor-related risks. Additionally, it provides resources and frameworks for improving cyber security measures and emphasizes ongoing education in risk management.