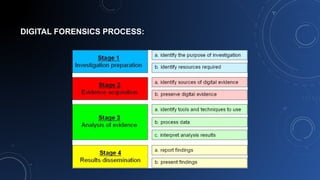
Cyber crime is on the rise globally as criminals shift targets from financial theft to espionage and government information. Governments must collaborate to combat cyber crime through strategies like reporting systems, prevention education, specialized law enforcement units, legislation, and international cooperation. Digital forensics techniques involve collecting and analyzing electronic evidence to investigate cyber crimes while maintaining data integrity and security.