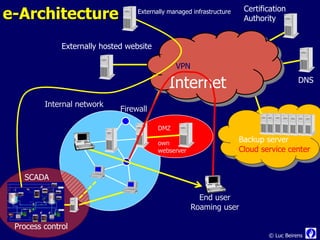
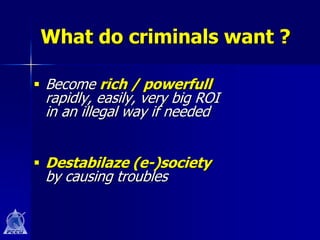
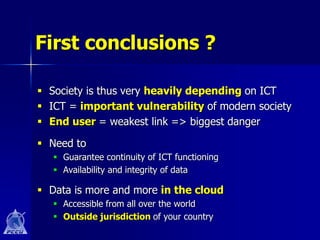
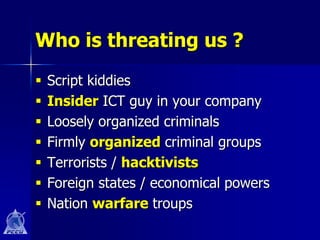
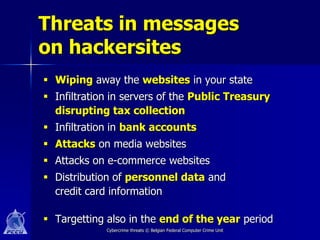
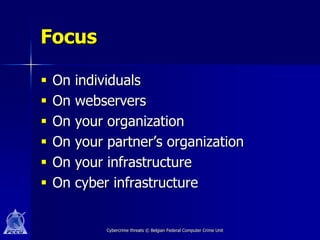
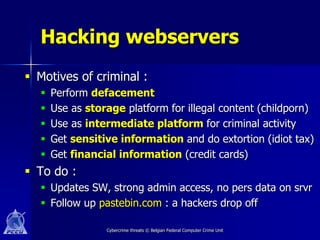
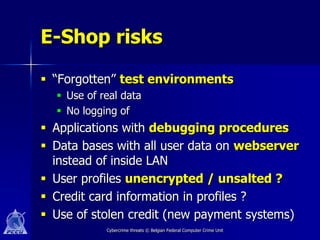
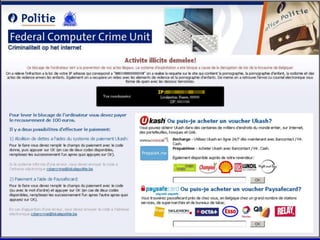
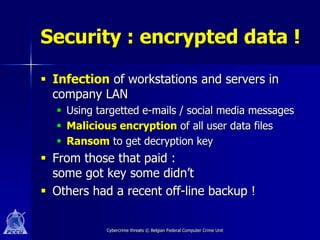
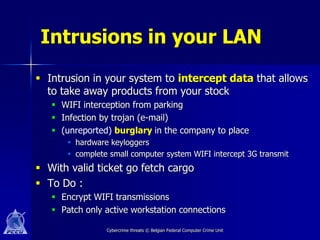
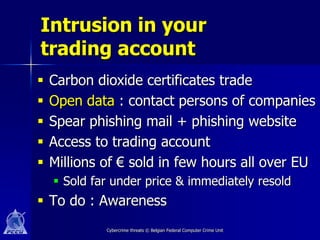
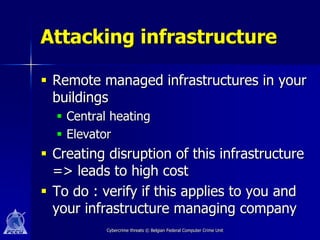
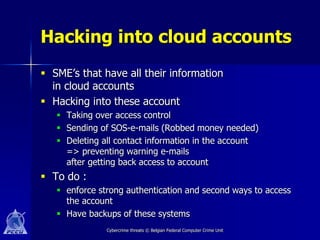
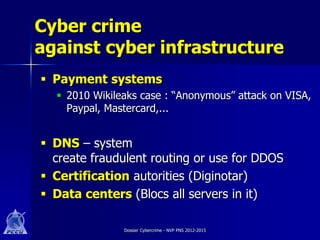
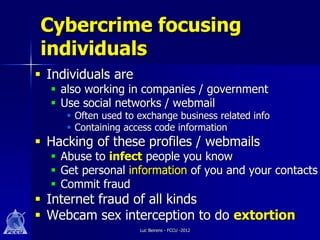
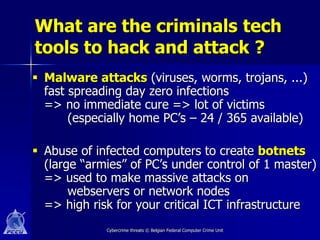
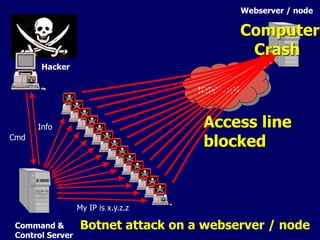
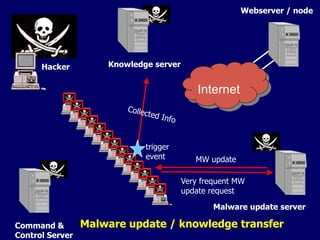
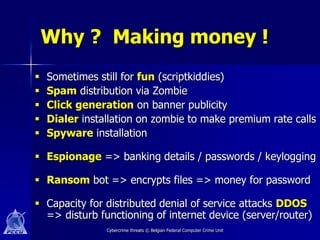
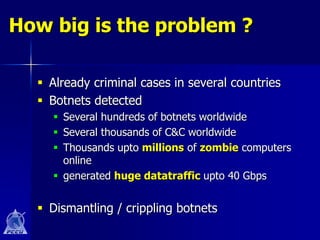
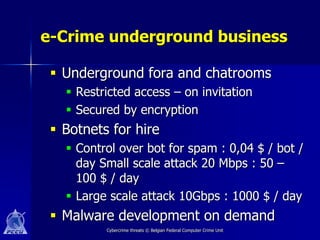
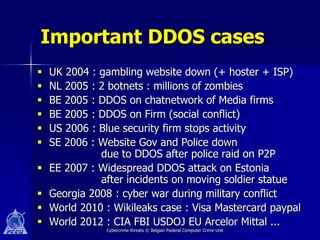
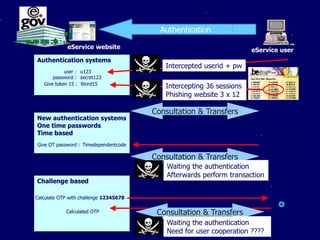
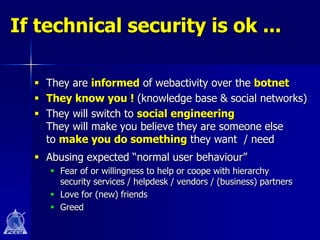
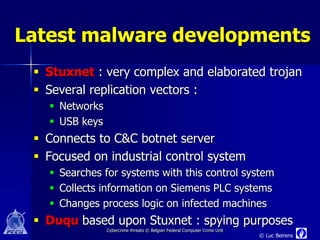
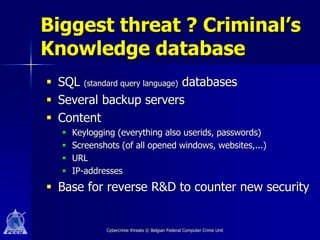
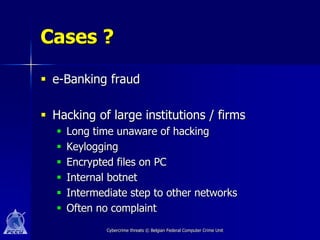
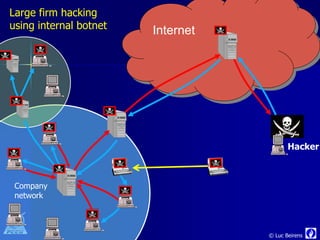
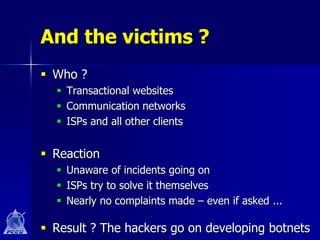
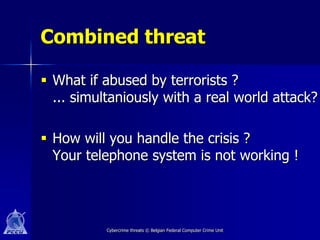
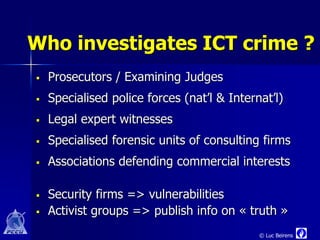
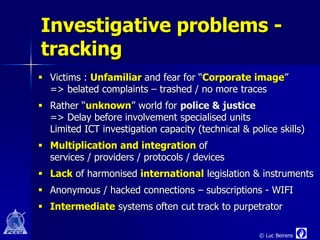
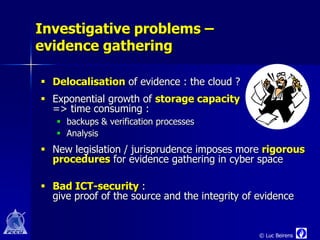
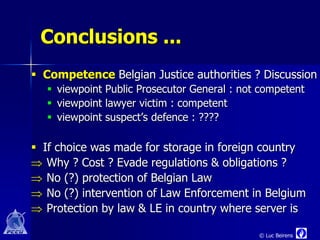
The document discusses various cyber threats including hacktivists, cyber espionage, and internet fraudsters. It notes the increasing reliance on information and communication technologies in modern society and the vulnerabilities this creates. The document outlines specific threats like hacking of web servers and internal networks, malware infections, and botnet attacks that can disrupt critical infrastructure or steal sensitive data. It emphasizes the need for an integrated approach and increased security awareness to address criminal cyber threats in the modern digital era.