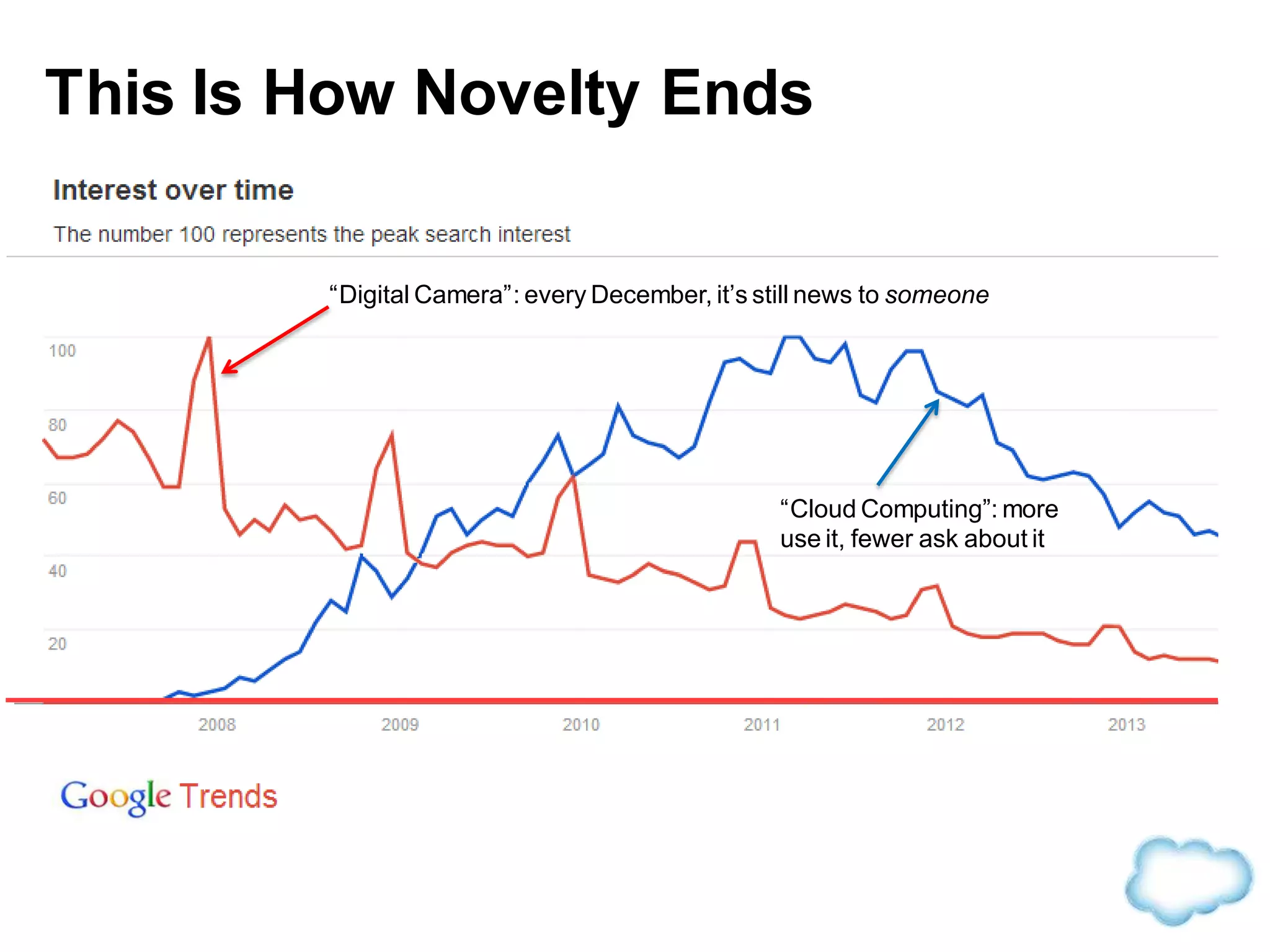
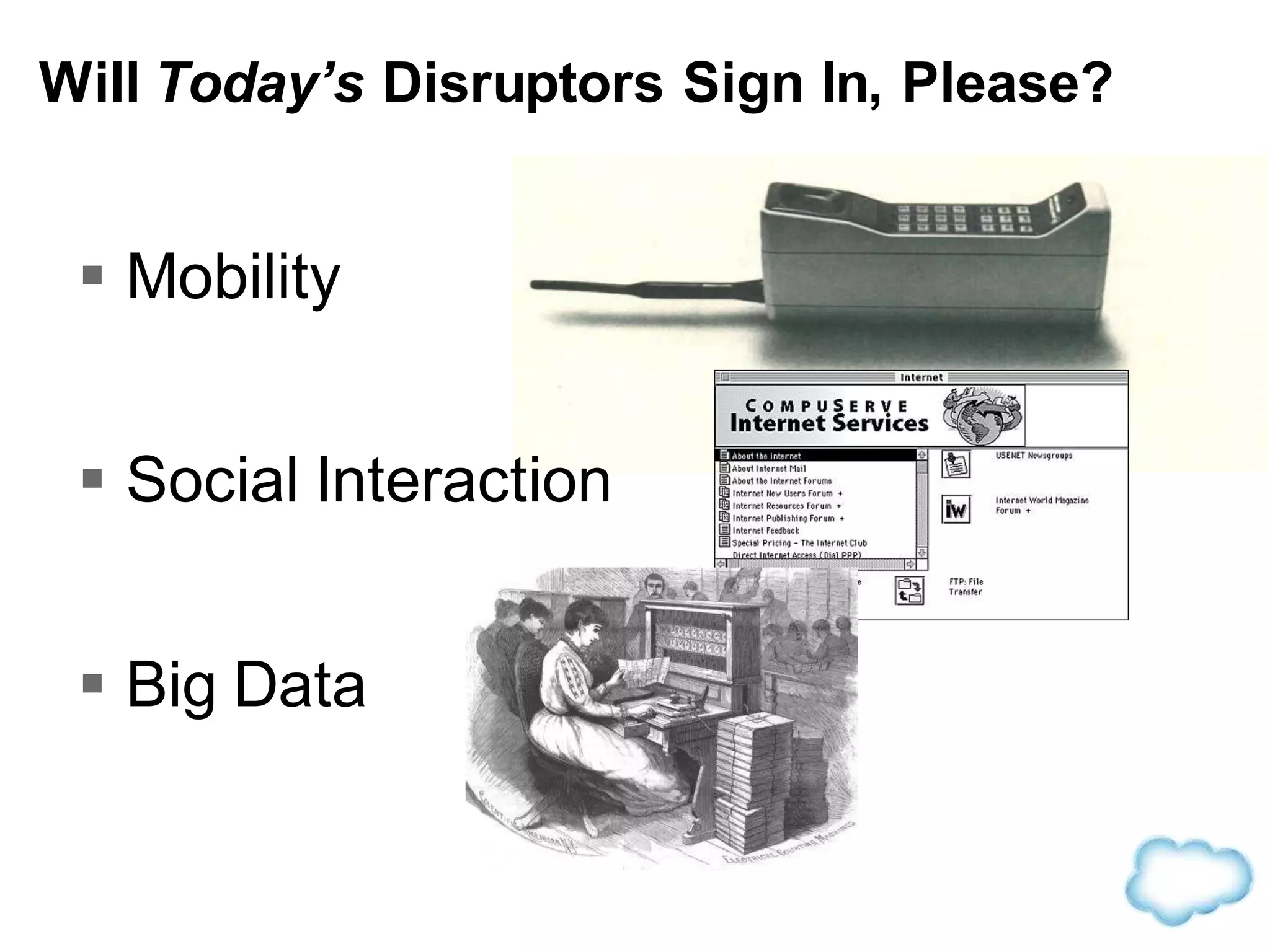
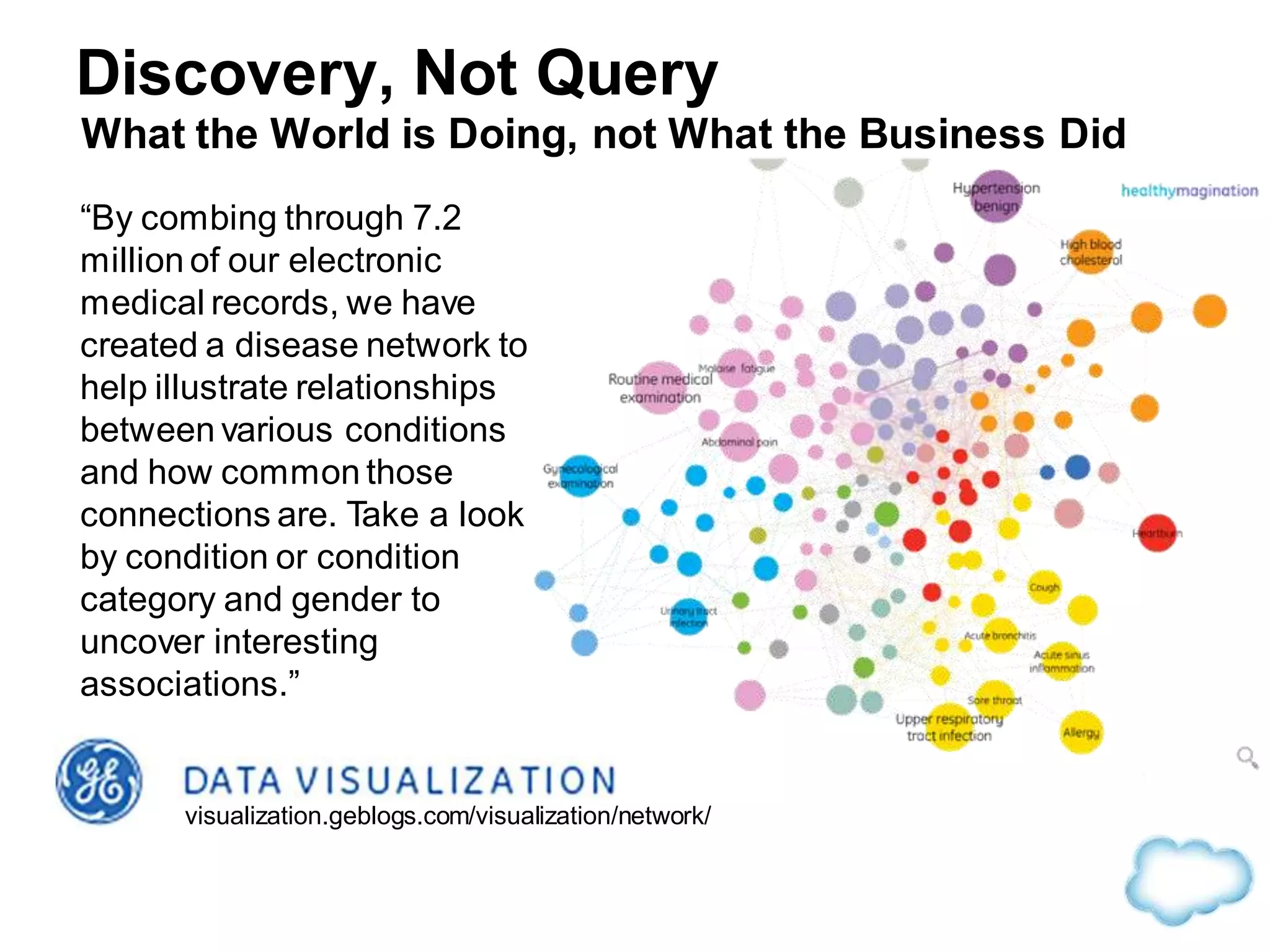
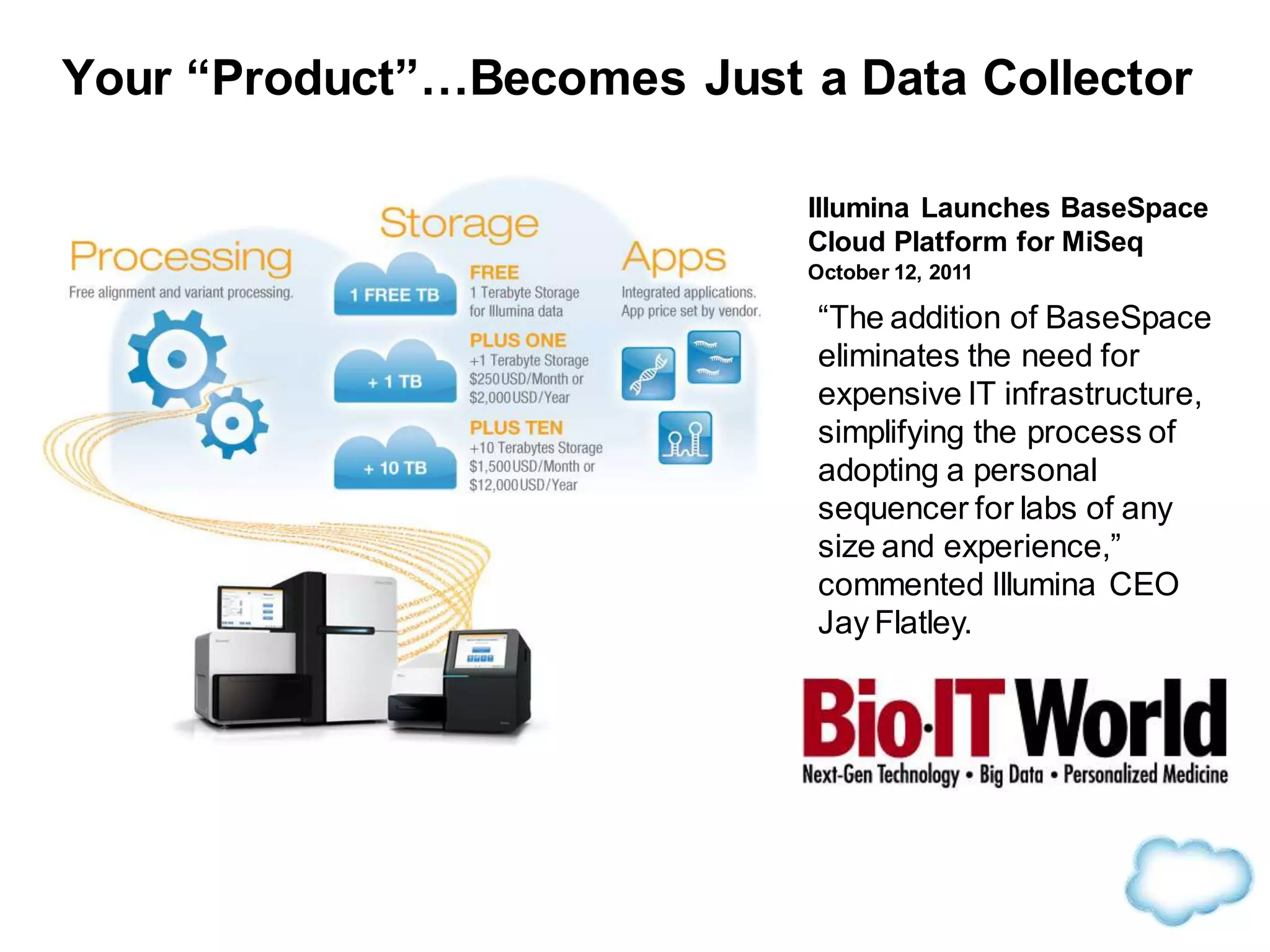
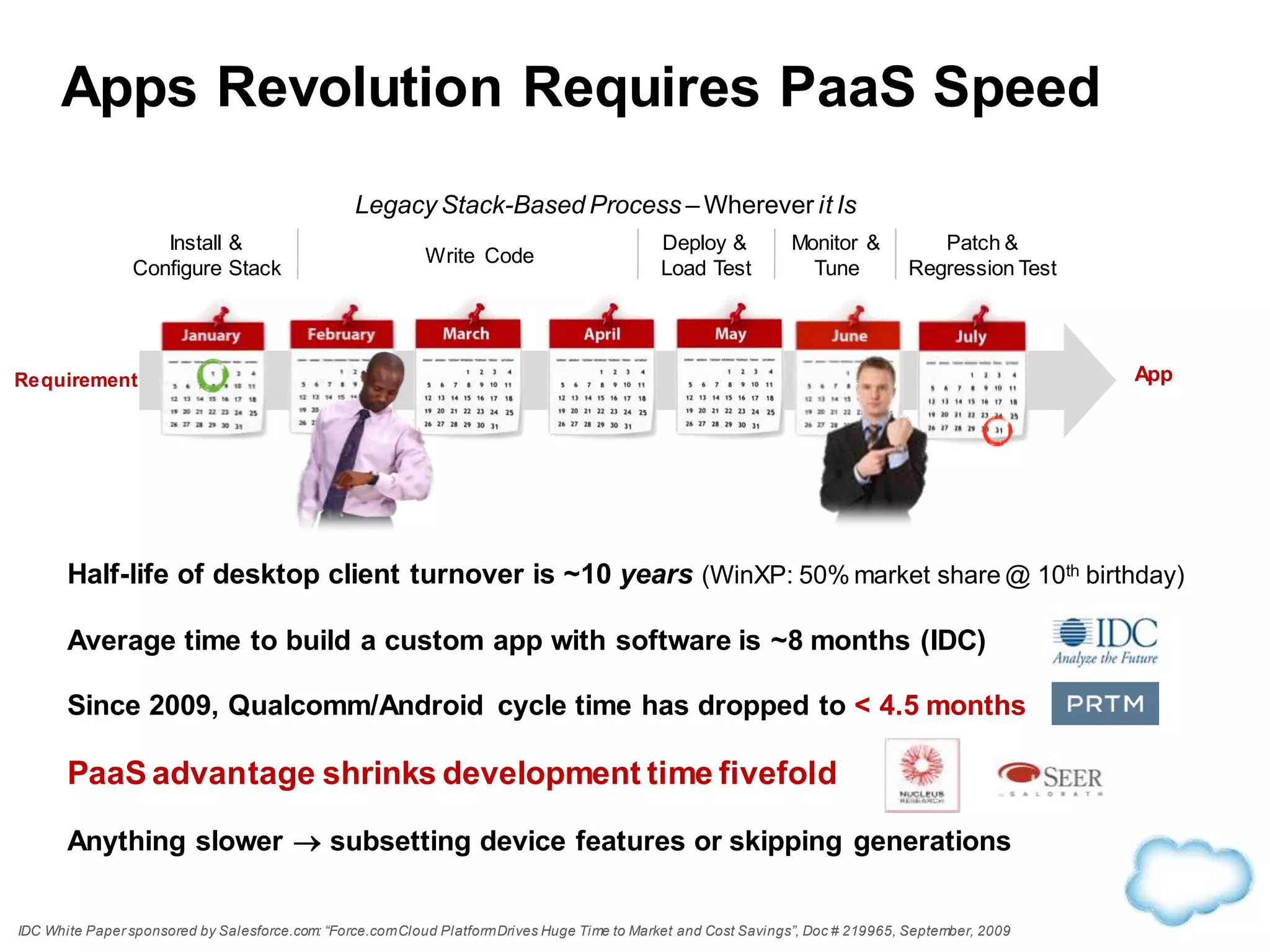
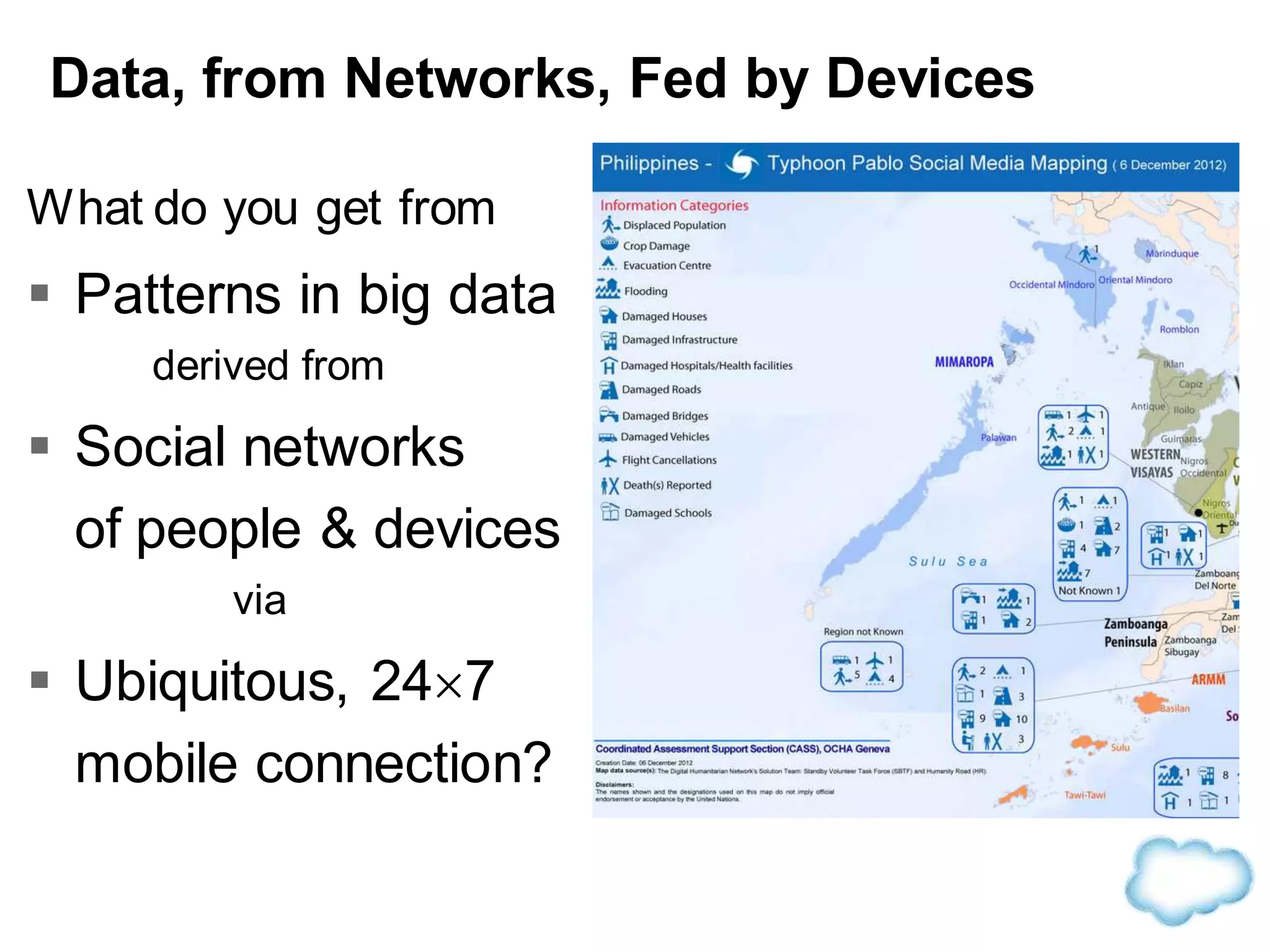
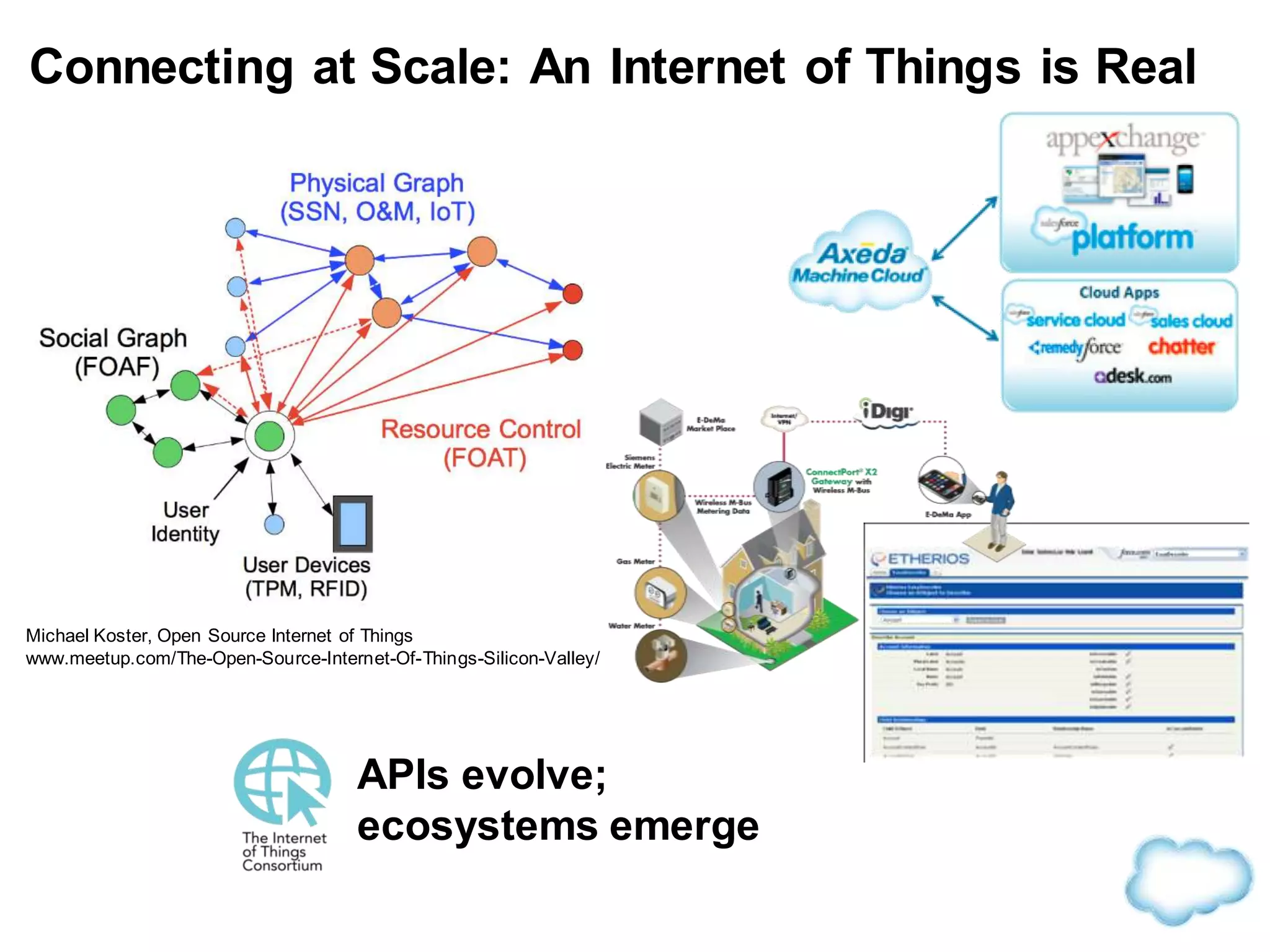
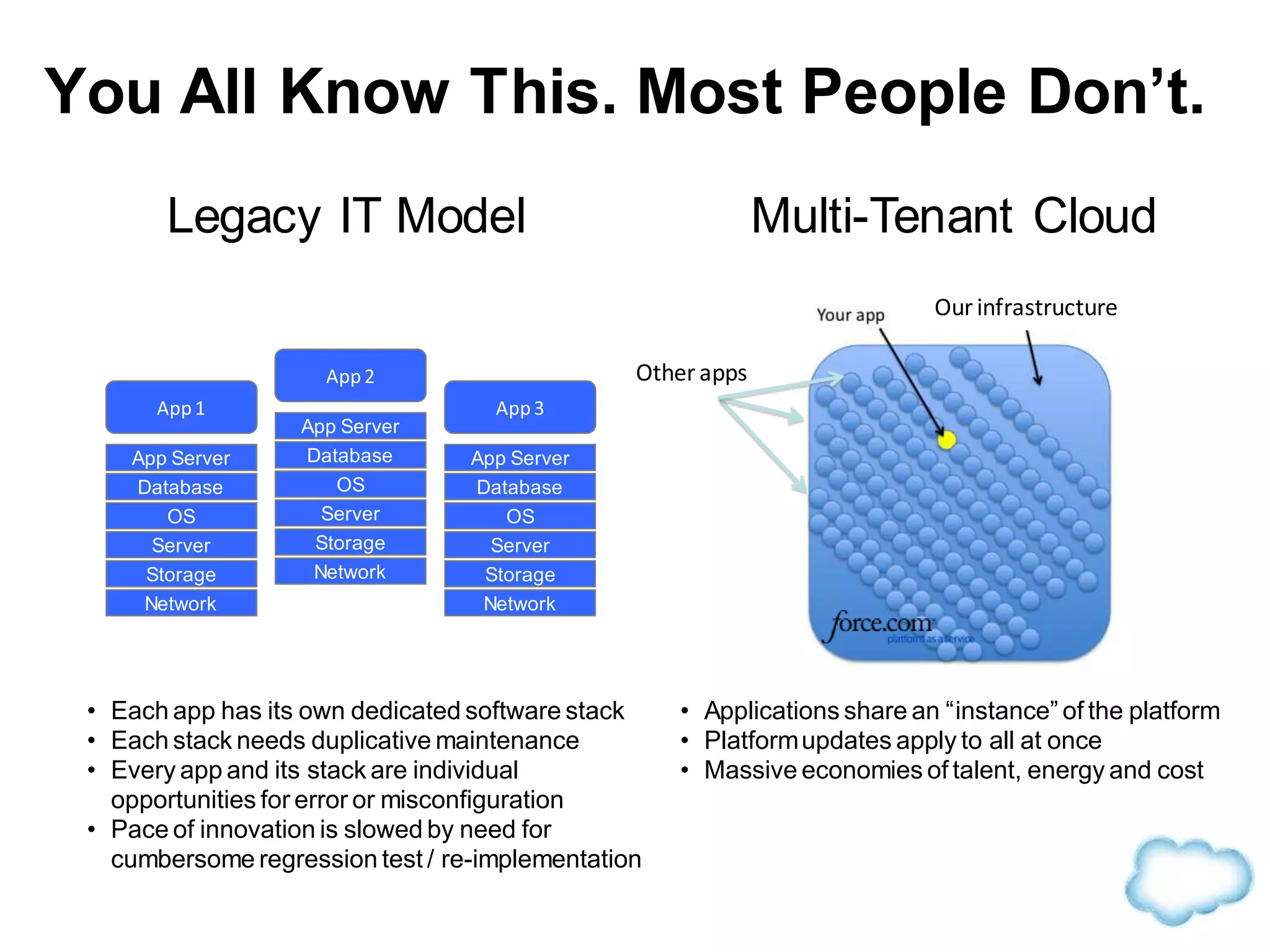
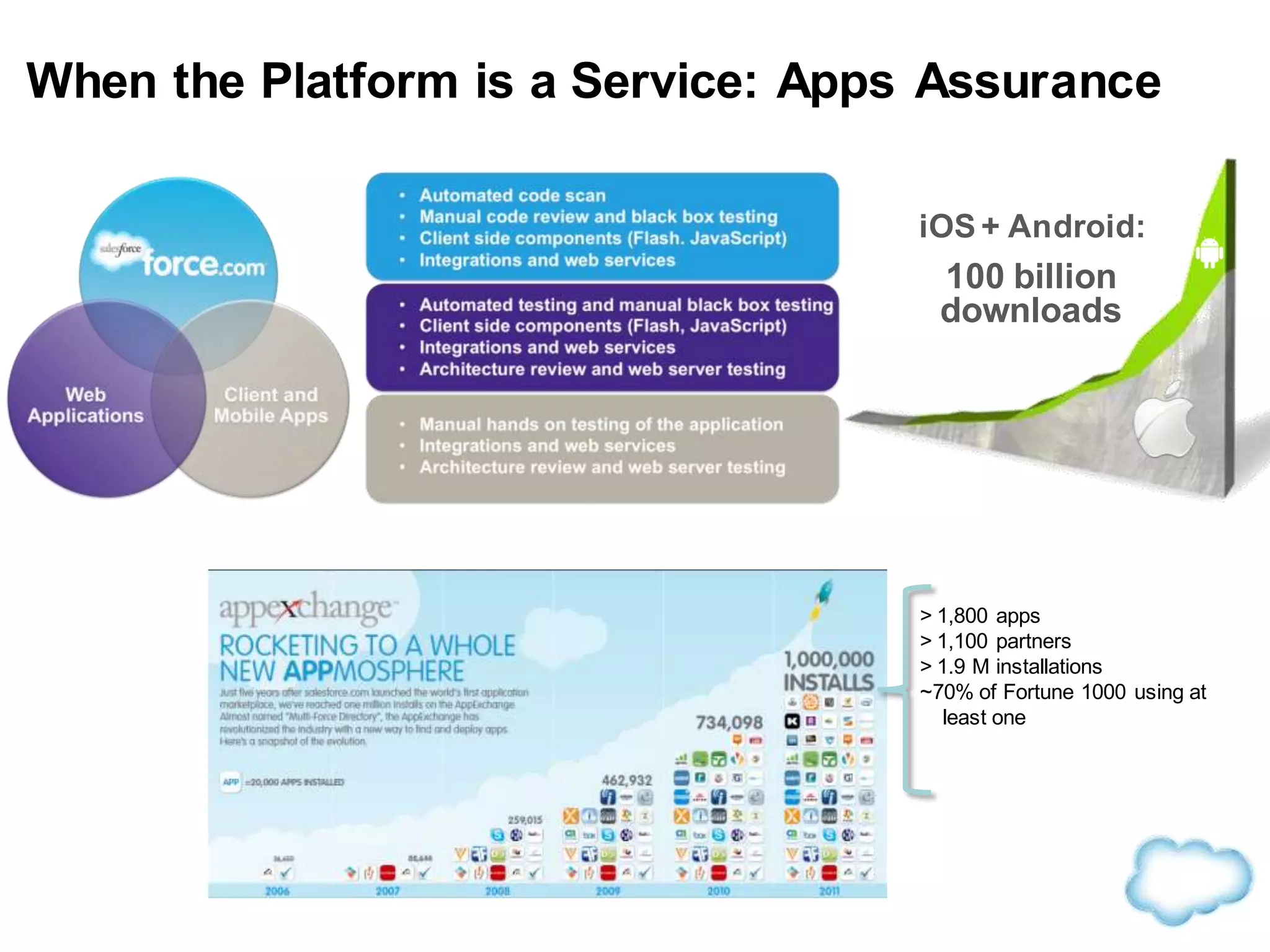
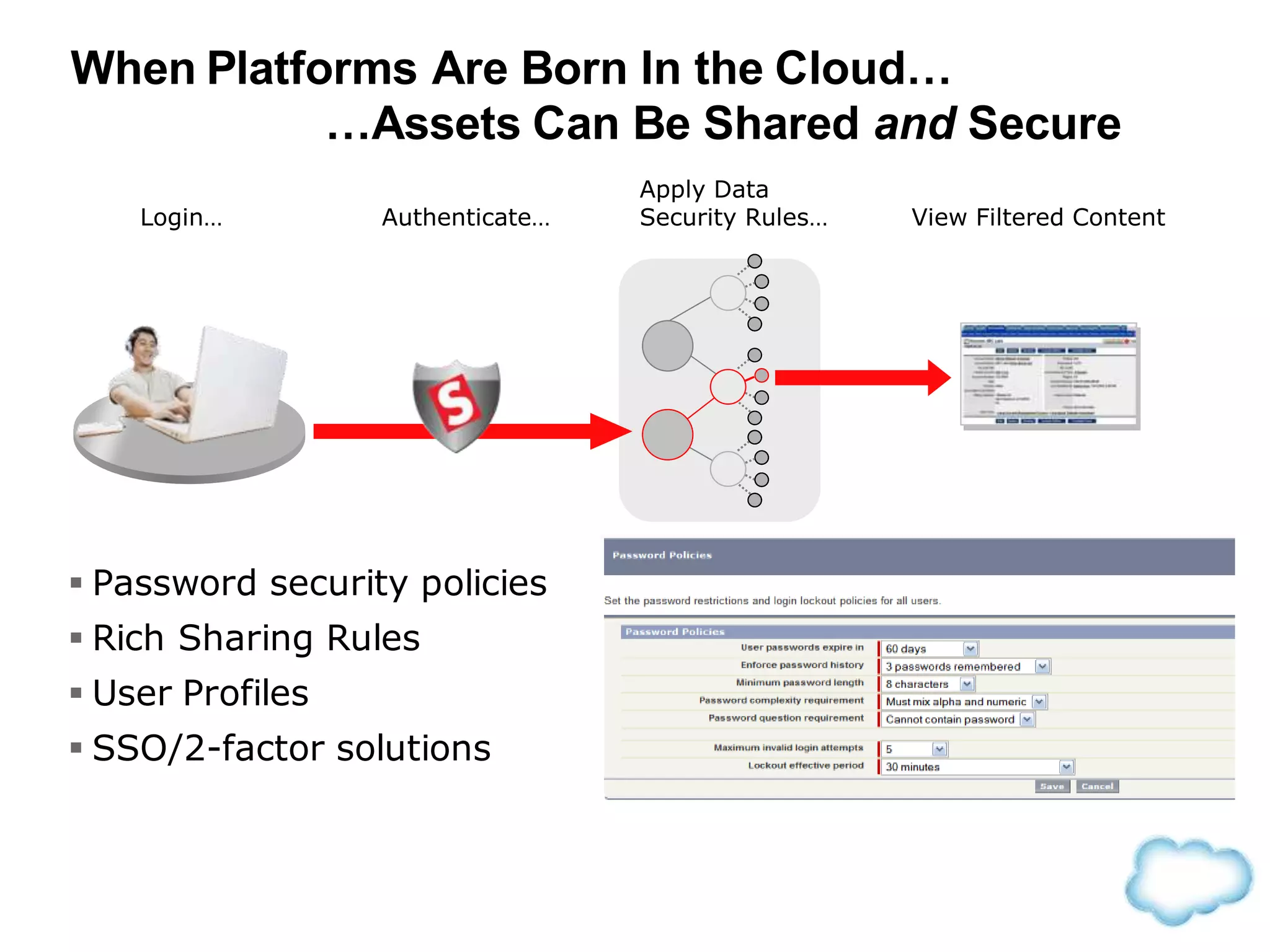
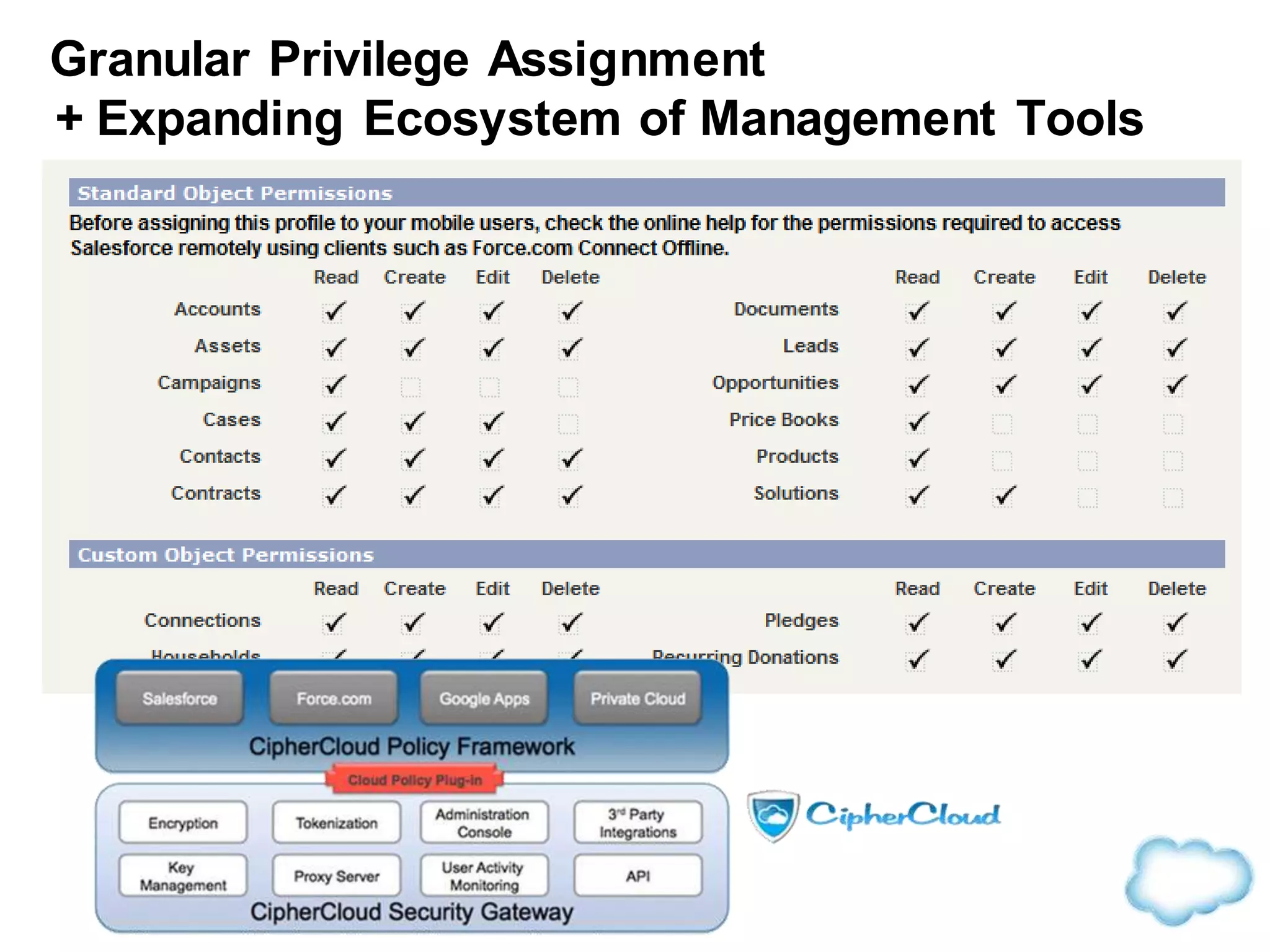
The document discusses how cloud computing is becoming ubiquitous and commonplace. It notes that terms like "digital camera" and "cloud computing" were once novel but are now widely used and understood. It suggests mobility, social interaction, and big data are the new disruptive technologies. The document discusses how the cloud enables elastic capacity and connectivity to real-world data. It envisions a future where data and algorithms provide discovery rather than just responding to queries, and where products become data collectors. The document discusses challenges of data privacy, connectivity enabling new attacks, and how technology trends oppose governance goals. It argues platforms enable massive cost savings over legacy IT models by sharing resources and enabling faster innovation.



![Data Governance Norms are Global
“While the [USA] Patriot Act continues to be invoked as a
kind of shorthand to express the belief that the United
States government has greater powers of access to
personal data in the Cloud than governments elsewhere,
and that ‘local clouds’ are the solution, a recent study we
conducted of the laws of Australia, Canada, Denmark,
France, Germany, Ireland, Japan, Spain, United
Kingdom—and the United States—shows that it is simply
incorrect to assume that the United States government's
access to data in the Cloud is greater than that of the
other advanced economies.
“Law enforcement and national security officials have
broad access to data stored locally with Cloud service
providers in the countries we investigated. Our research
found that that it is not possible to isolate data in the
Cloud from governmental access based on the physical
location of the Cloud service provider or its facilities, and
that Governments' ability to access data in the Cloud
extends across borders.” - http://www.hoganlovells.com](https://image.slidesharecdn.com/aitpcloudconsd2013pcoffeefinalpdf-131003123006-phpapp01/75/Connecting-Above-the-Cloud-28-2048.jpg)