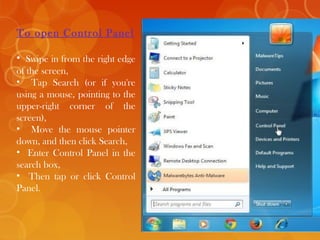
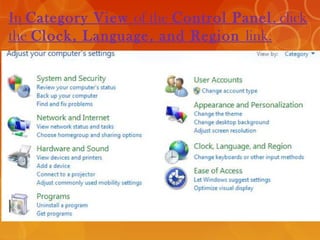
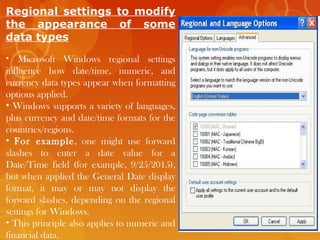
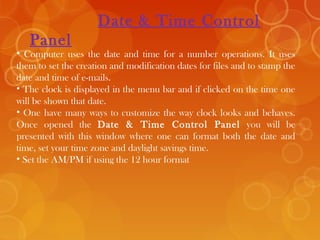
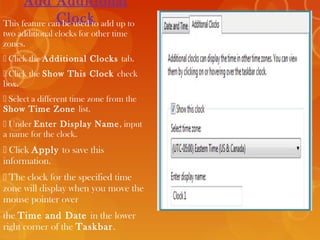
The document provides information about computer parts, the control panel, and date/time settings. It defines a computer and its main parts like the monitor, keyboard, mouse, CPU, and printer. It describes the control panel as allowing users to view and change basic system settings through applets. The date/time section explains how to change the format, time zone, and add additional clocks in the Date and Time control panel.