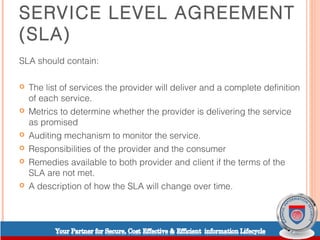
This document discusses cloud computing and service level agreements. It begins by defining different types of cloud computing models like SaaS, PaaS, and IaaS. It then discusses how cloud computing differs from traditional on-premise storage by addressing issues like data location, custody, and multi-tenancy. The document outlines important considerations for service level agreements including security, data encryption, privacy, regulatory compliance, and transparency. It emphasizes that SLAs should define metrics and responsibilities to ensure the cloud provider delivers the promised level of service. Finally, it cautions that moving to the cloud requires understanding issues like security, portability, accessibility, and data location laws.