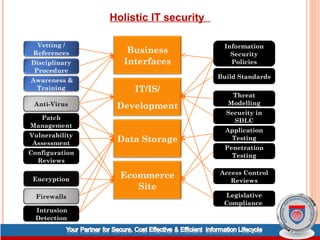
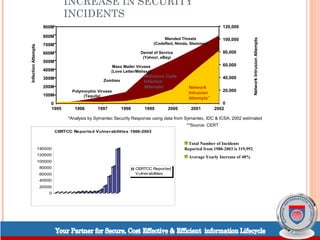
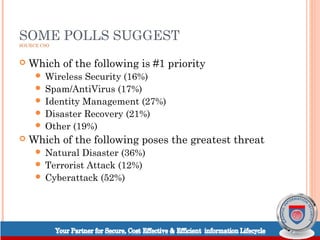
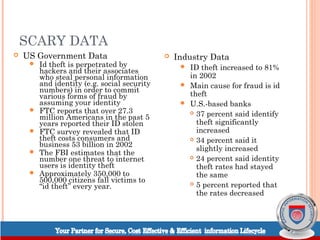
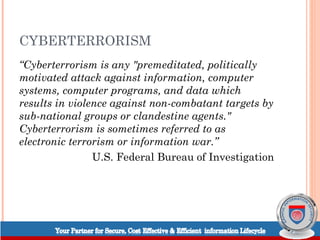
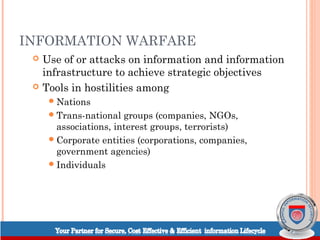
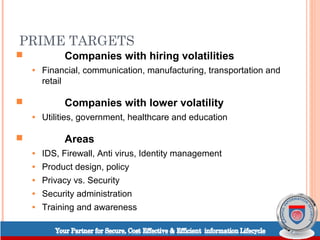
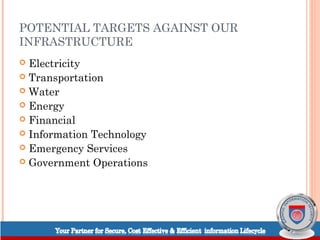
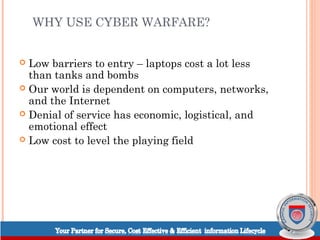
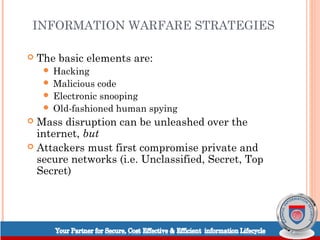
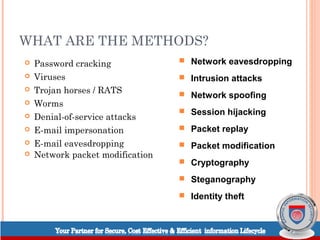
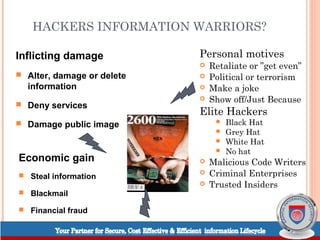
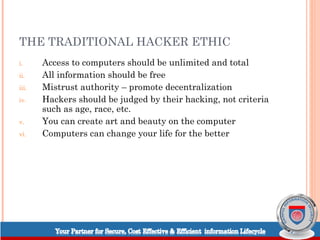
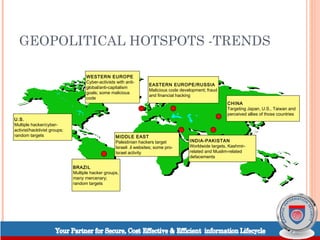
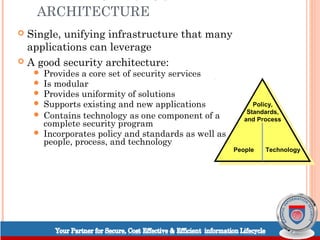
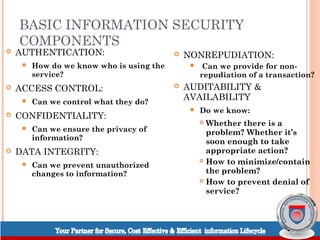
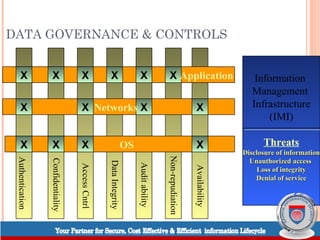
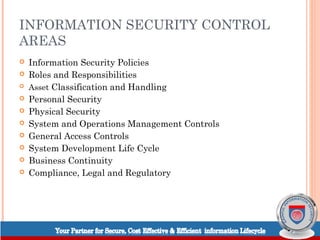
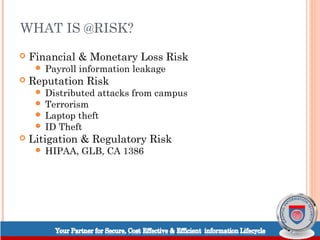
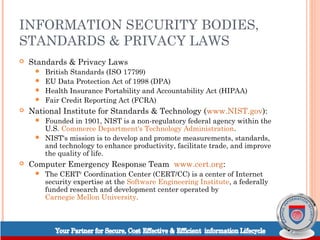
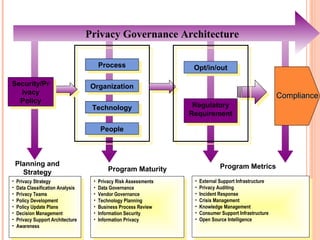
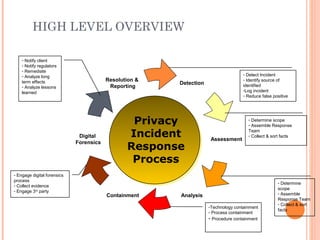
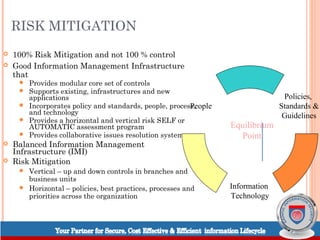
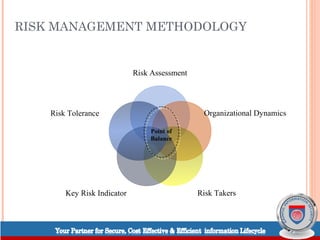
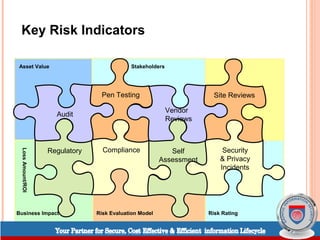
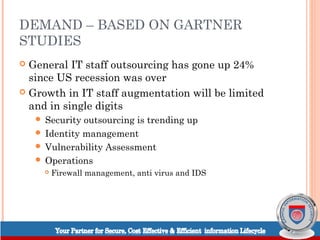
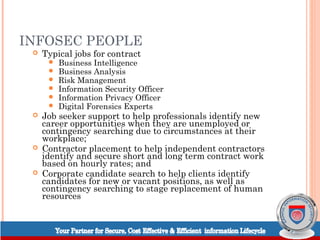
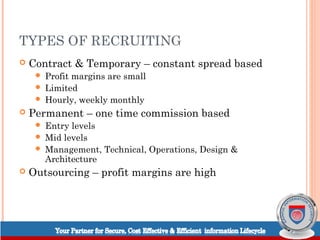
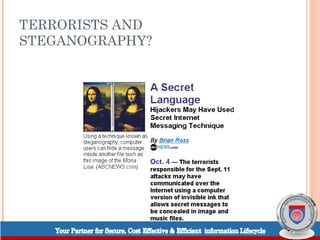
The document outlines critical aspects of information security, emphasizing the rising sophistication of threats such as cyberattacks and identity theft, and the necessity for robust protective measures. It details various security strategies, including risk management, policies, and measures against information warfare and social engineering. The text also discusses trends in information security sectors, job opportunities, and the importance of public awareness and compliance with legal standards.