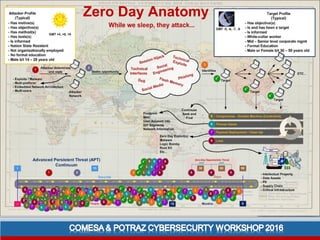
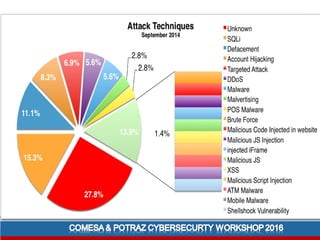
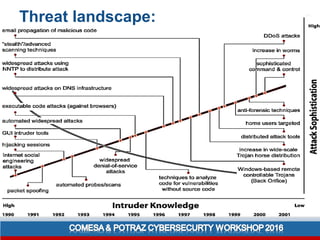
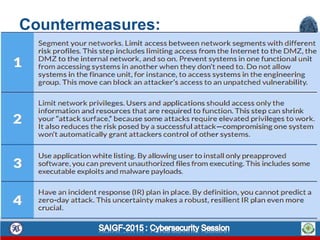
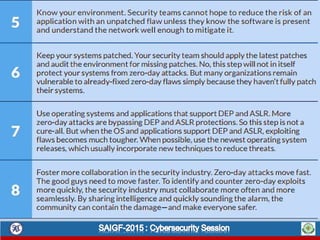
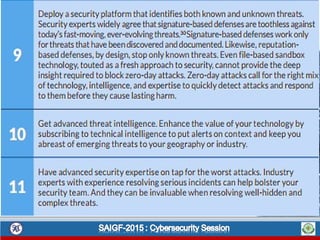
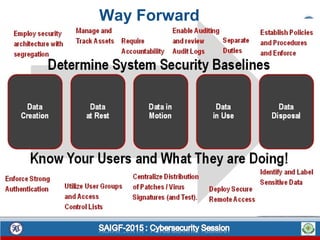
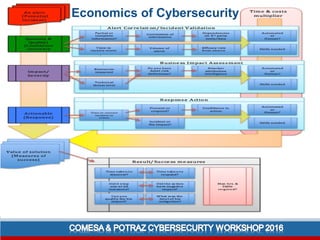
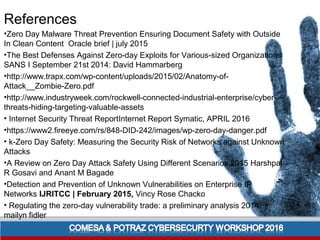
This document discusses zero-day attacks, which exploit unknown vulnerabilities that have no patch. It begins with key terms, then describes the anatomy and methodology of zero-day attacks. Countermeasures are discussed, as well as the economics of cybersecurity and questions from attackers. On average, zero-day attacks last 8 months, allowing theft of valuable assets before detection. They are heavily used in targeted attacks due to the advantage over targets. Overall the document provides an overview of zero-day attacks and potential strategies to secure against unknown threats.