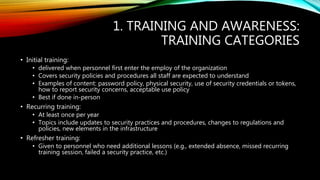
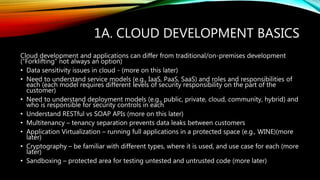
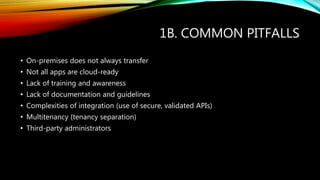
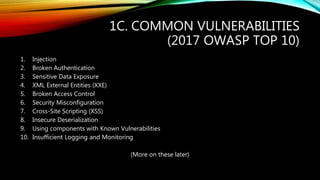
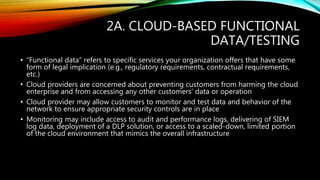
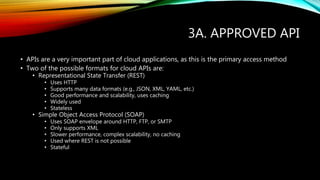
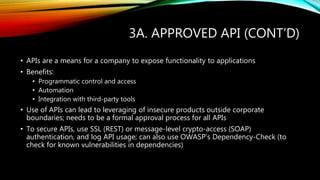
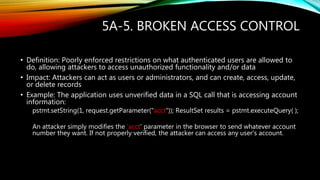
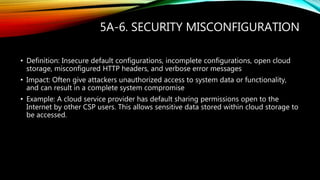
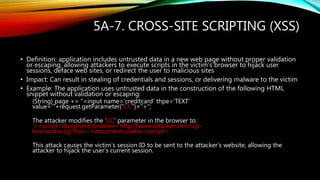
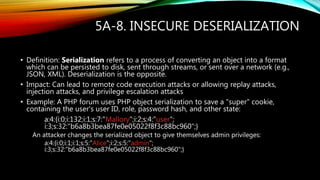
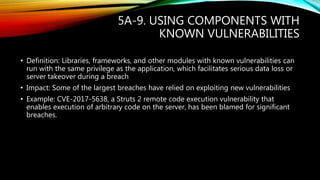
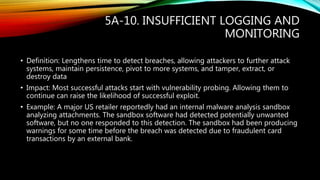
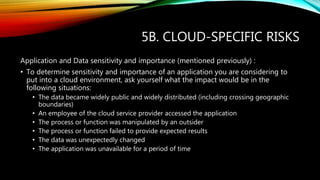
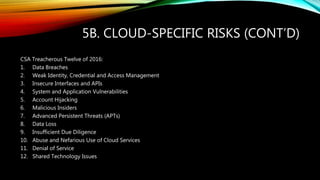
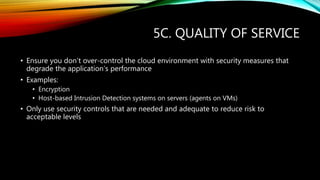
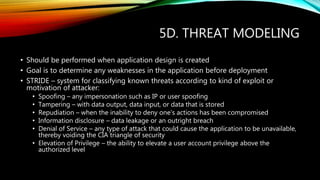
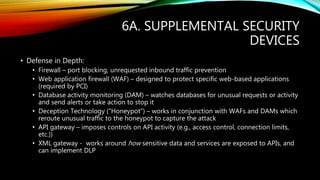
The document outlines key topics for training and awareness in cloud application security, including the importance of secure software development life-cycles and common vulnerabilities faced in cloud environments. It emphasizes the need for ongoing training, understanding various cloud service models, and utilizing secure APIs, along with identifying specific risks associated with cloud deployment, such as identity management and data breaches. Essential methodologies are discussed for ensuring compliance and robust application security within the cloud infrastructure.