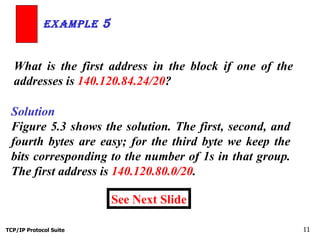
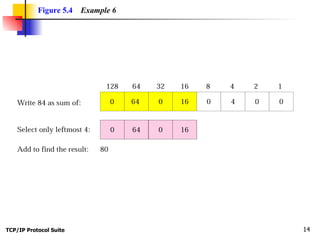
This document discusses classless addressing and variable-length subnetting. It begins by explaining that in classless addressing, variable-length blocks of IP addresses are assigned without class boundaries. It then provides examples of how to determine the network address, broadcast address, and number of addresses given a classless IP address and prefix length. The document also describes how organizations can create subnets within a granted address block to meet their needs using variable-length subnetting.