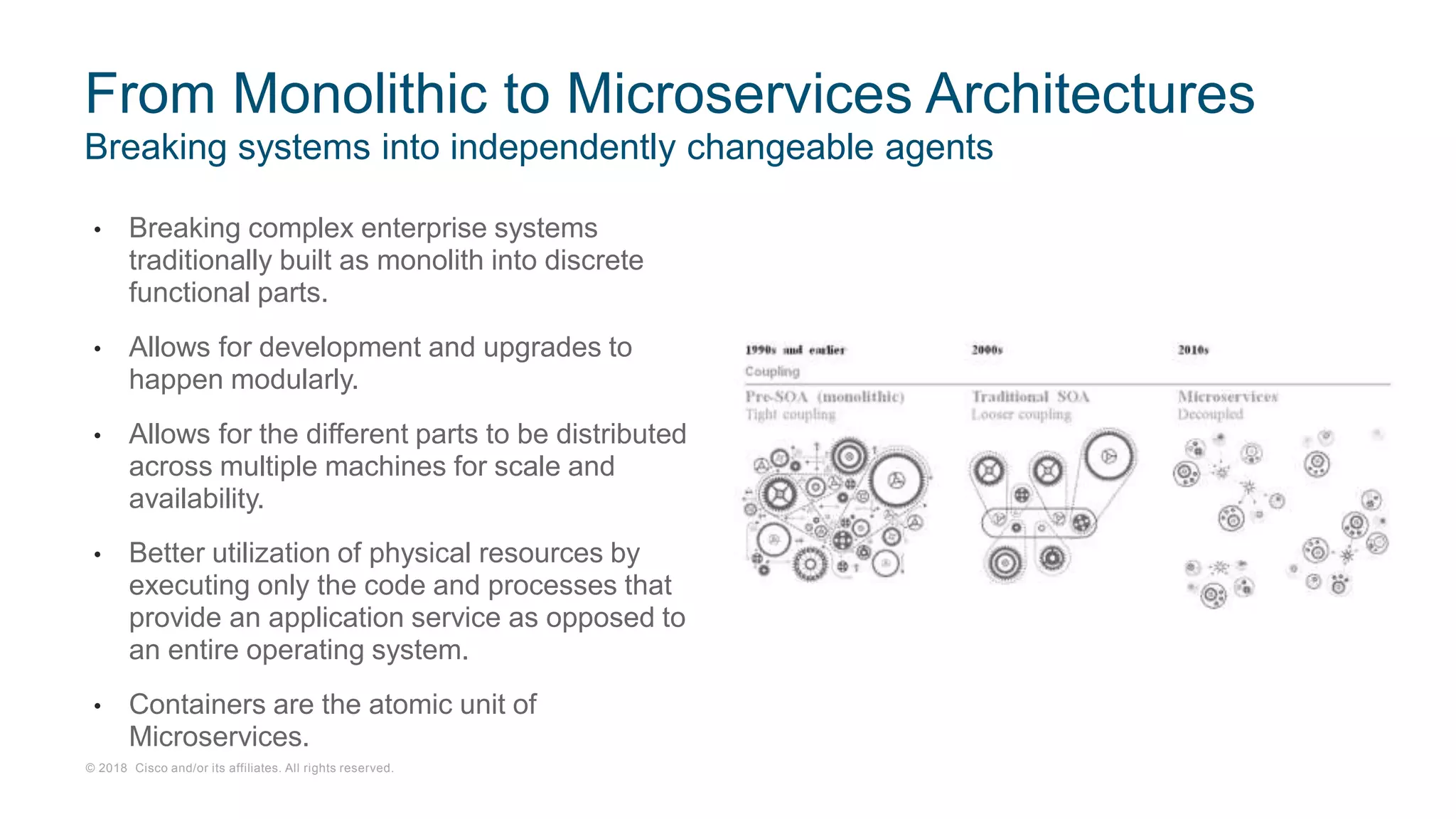
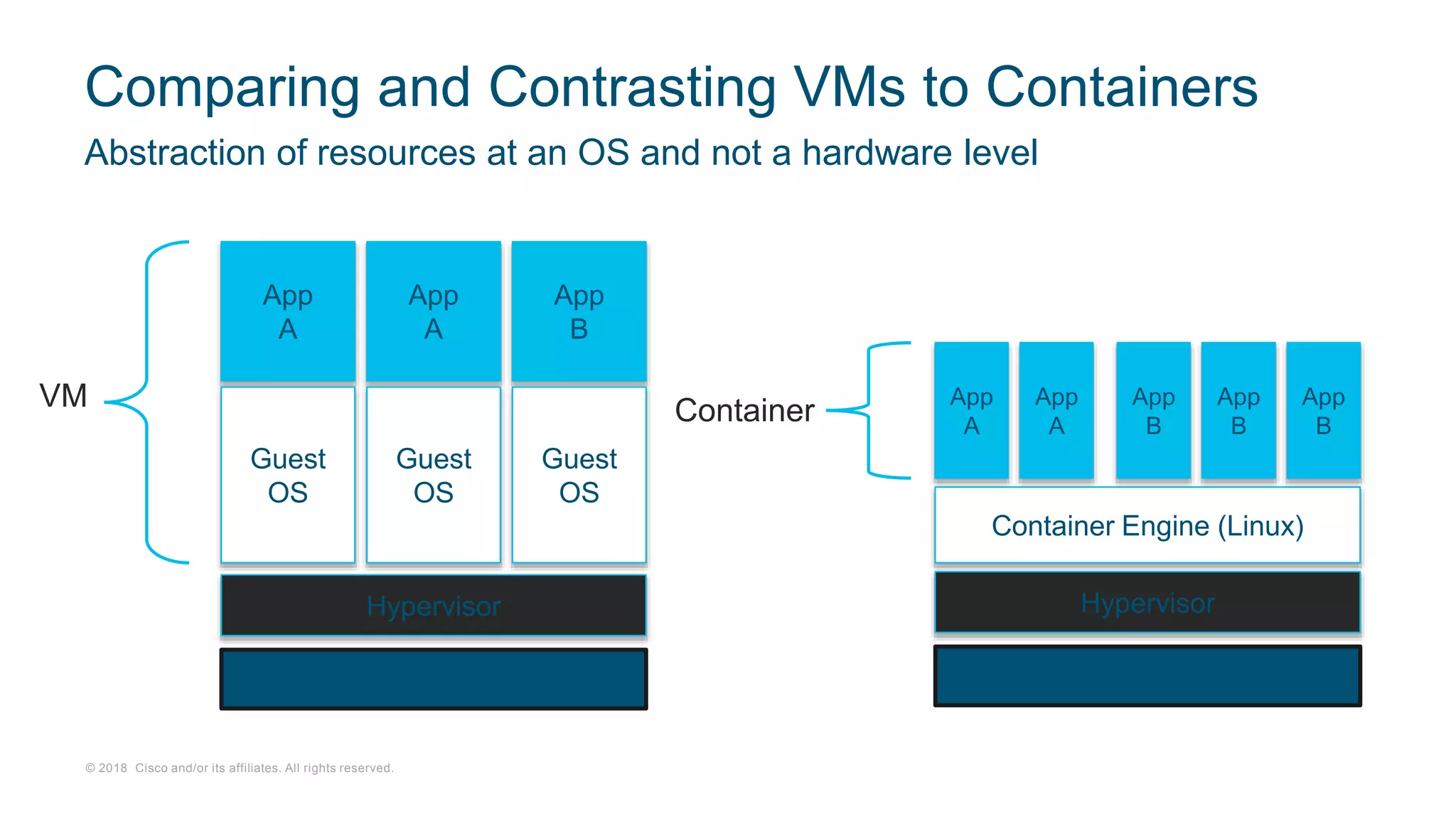
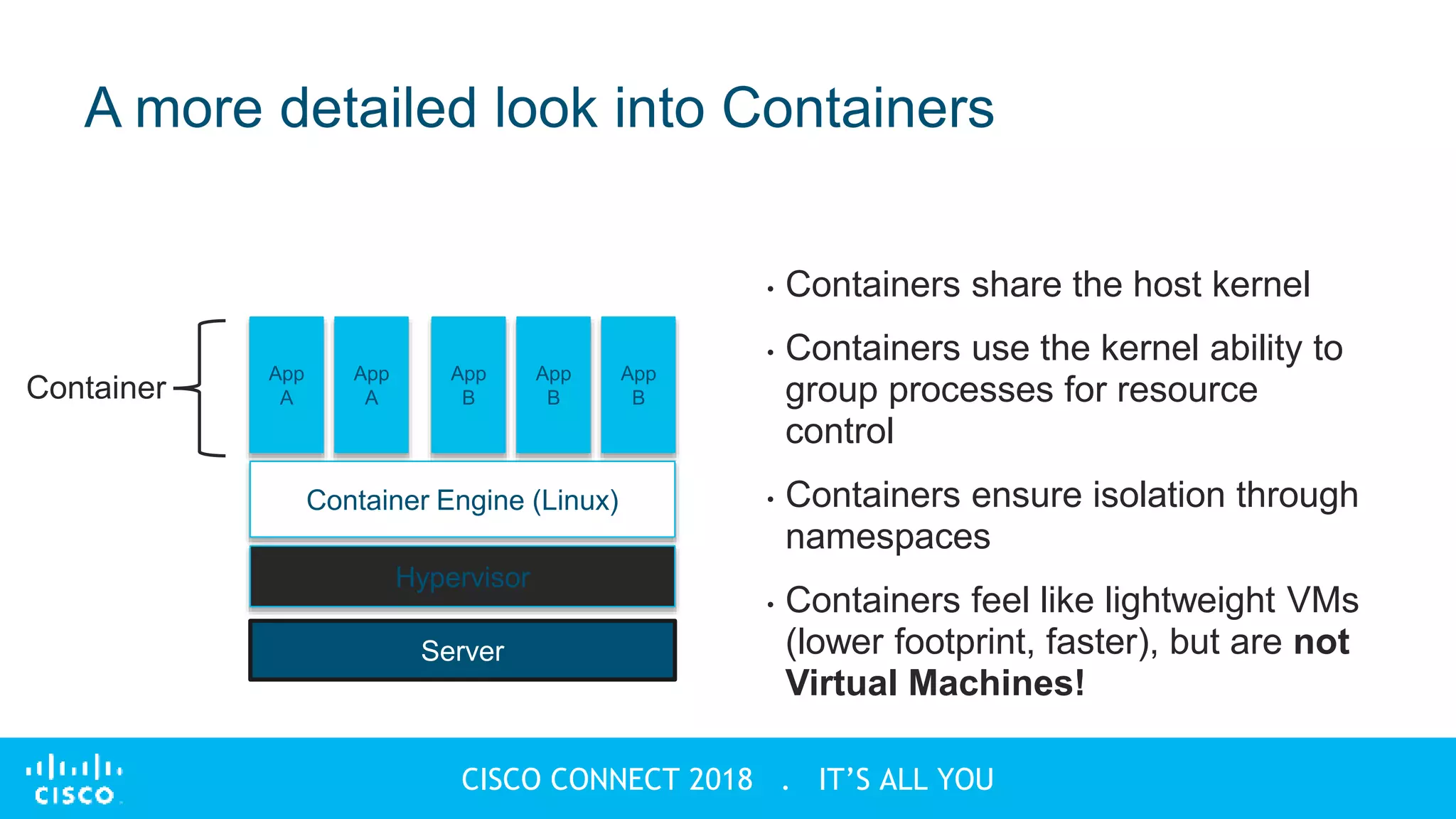
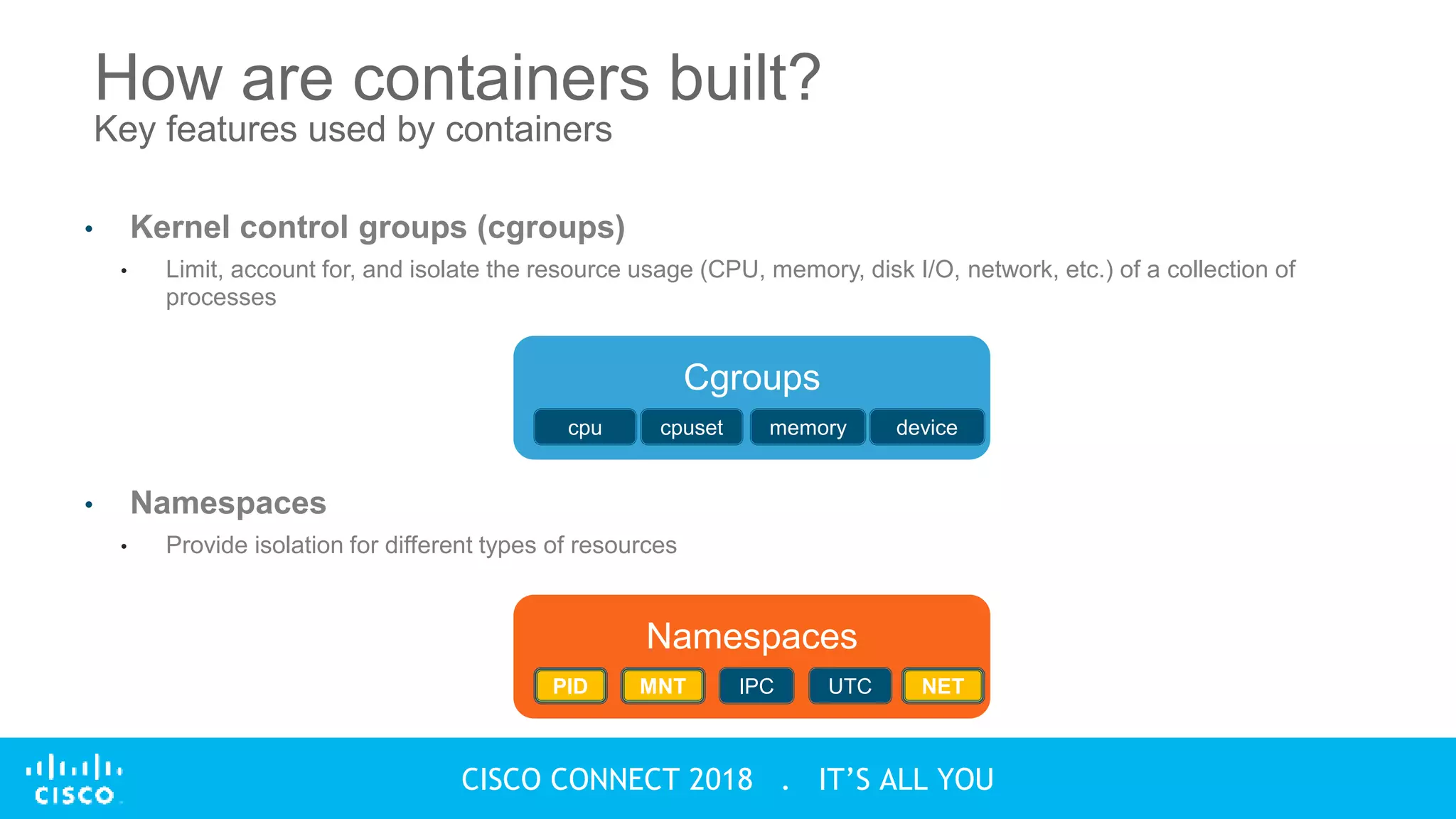
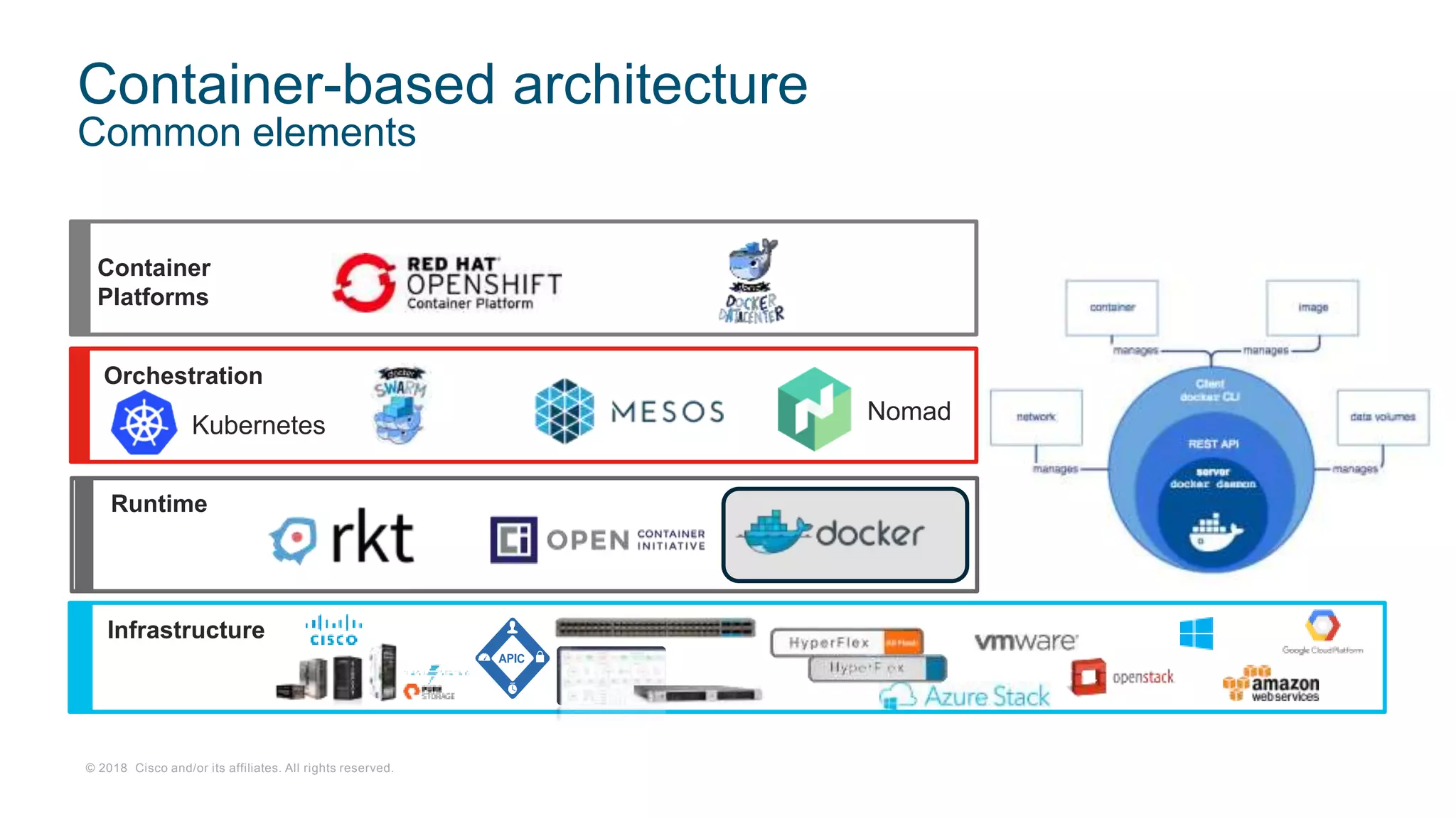
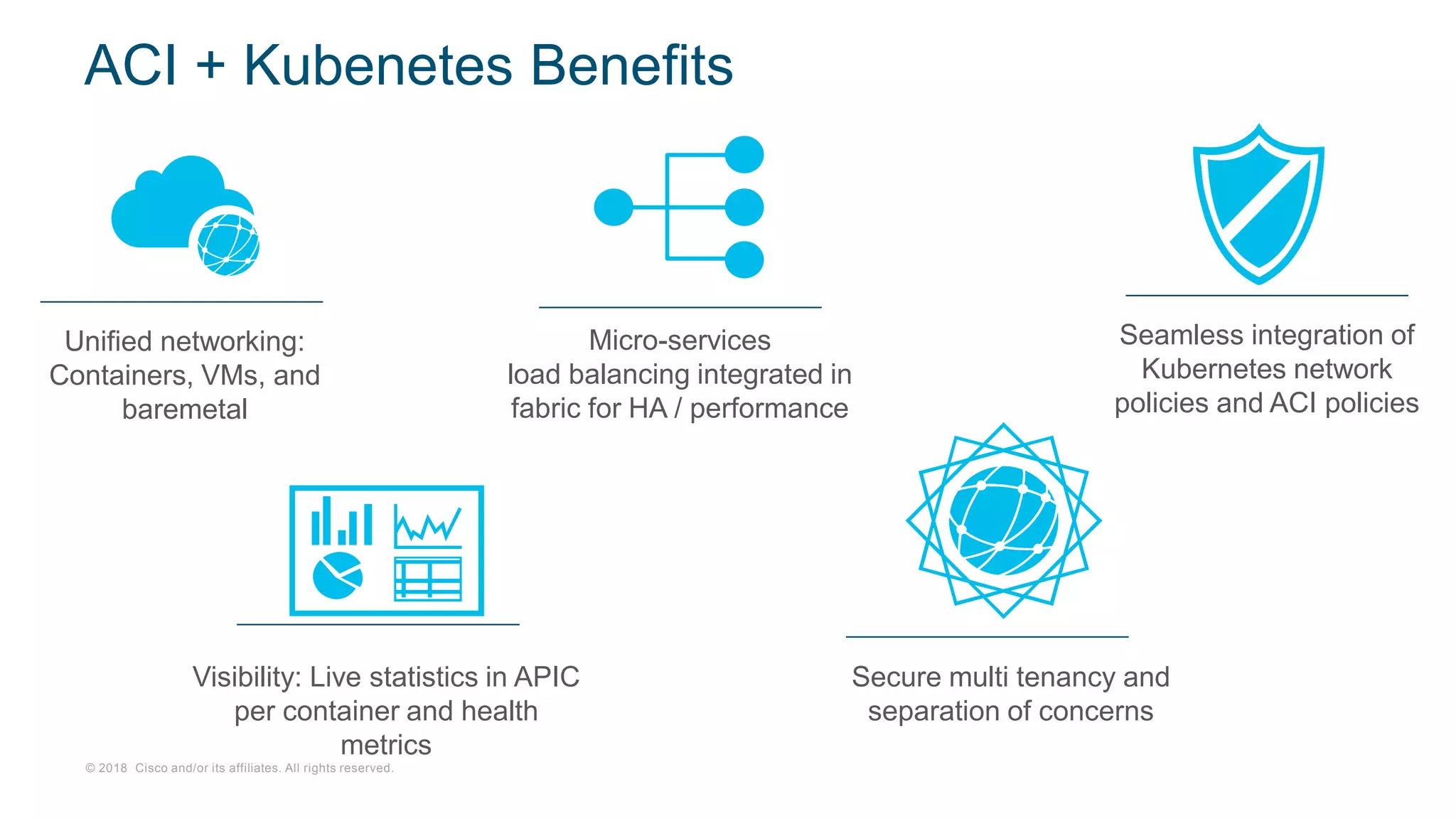
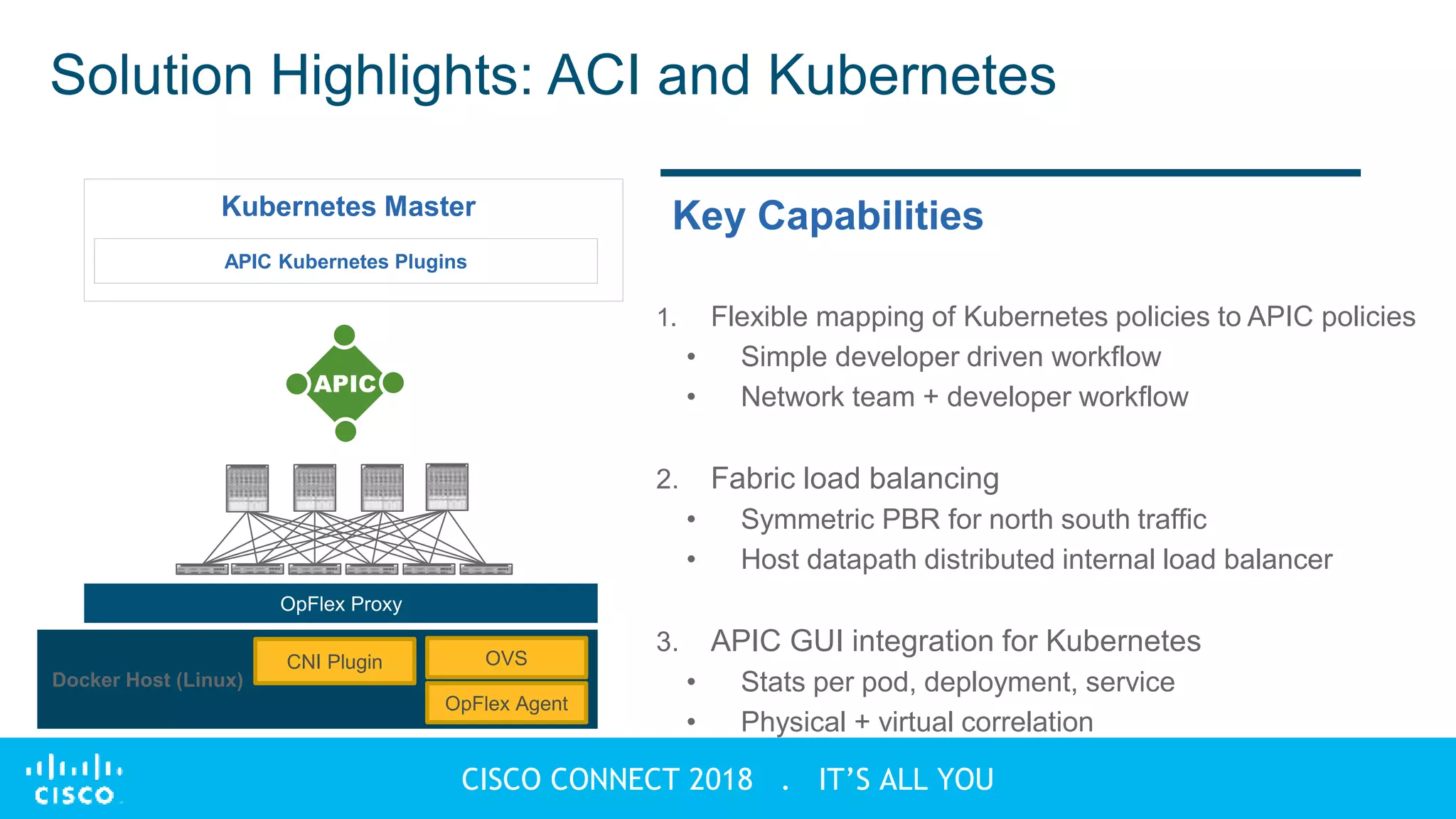
This document discusses containers and container infrastructure. It begins by explaining how containers allow complex systems to be broken into discrete functional parts for modular development and scale. It then contrasts containers with virtual machines, noting that containers share a host kernel and use kernel namespaces for isolation rather than full hardware virtualization. The document goes on to describe how containers use cgroups and namespaces to provide isolation. It stresses that containers are built on and isolated using features of the Linux kernel. It also discusses the need for container orchestration in production for fault tolerance, scaling, resource optimization, service discovery, and rolling updates. Finally, it outlines some benefits of using Cisco Application Centric Infrastructure (ACI) with Kubernetes for container orchestration.