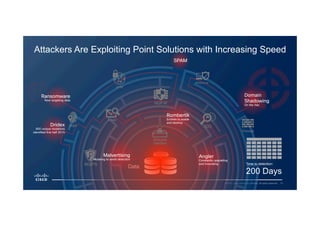
The document discusses the state of cybersecurity based on Cisco's 2015 midyear security report. It covers transitions in the cybersecurity industry and within Cisco. It notes that adversaries are adapting quickly by constantly upgrading exploits and malware to evade detection. The document advocates for an integrated threat defense approach to keep pace with evolving attacks.