The document outlines a plan for a new client/server network for Waterfront Tele-Support. Key points include:
- The current 10base2 network needs replacing with a new up-to-date infrastructure.
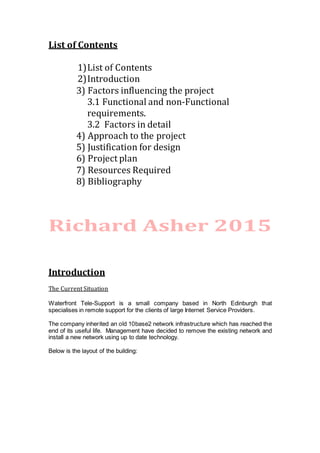
- An extended star topology is proposed using switches, servers, firewall and wireless access.
- The server will run Windows Server 2008 and provide file storage, web hosting, remote access, backups and more.
- Security measures like firewalls, filtering and permissions are included to protect the network.
- Budget is £30,000 and all new equipment will be purchased within this budget.

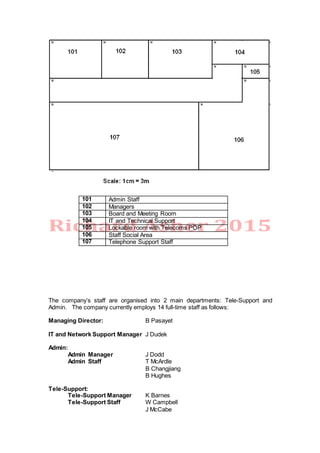





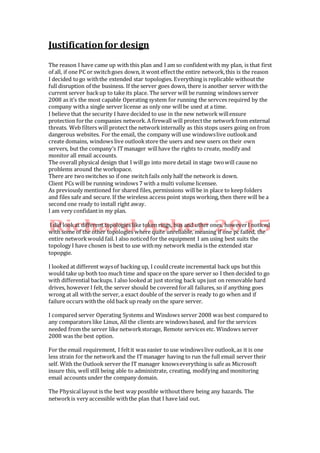


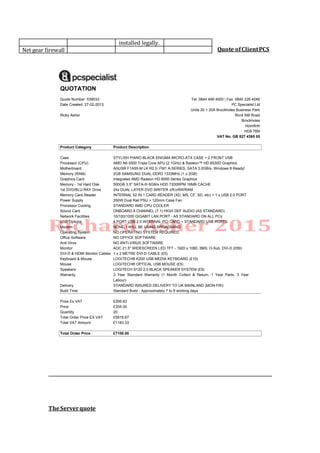
![27/ 02/ 2013 01:43The Dell Online Store: Build Your System
Page 1 of 3http:/ / configure.euro.dell.com/ dellstore/ print_summary_details_po…c= svt110ii&s= bsd&vw= classic&leadtime= 05/ 03/ 2013&showleadtime= True
DELL PowerEdge™ T110
II
Price £1,122.00
Discount £208.00
Subtotal £914.00
Estimated Delivery Times
Save an extra £120 when you spend
over £800 on Dell PowerEdge
Servers.
Add coupon code
QK1FTTZ7KSQDFG to your basket to
claim savings.
Offer ends 1st March 2013.
Recycle your old Dell Server and on
purchases of over £700
claim £250 cash back
Ex. VAT & Shipping
36 months lease from only £35 per
month
Why lease? Find out more.
Discount Details
Preliminary Ship Date: 05/03/20131
DELL PowerEdge™ T110 II
Date
26/02/2013 19:36:52 Central Standard
Time
Catalog Number 202 Retail ukbsdt1
Catalog Number / Description Product Code Qty SKU Id
Base:
PowerEdge T110 II Tower Chassis, Up to 4x 3.5"
Cabled HDDs
509987 1 [210-35874] 1
Processor:
Intel® Core™ i3-2100, 2C/4T, 3.10GHz, 3M
Cache, 65W TDP
509996 1 [213-13586] 146
Memory:
2GB Memory, DDR3, 1333MHz (1x2GB Single
Ranked LV UDIMM)
509798 1 [370-20355] 3
Operating System:
Windows Server 2008 R2 SP1, Standard Edition,
English, Incl. 5 CALs, Including Media
727822 1
[617-10338]
[618-10616]
285
Shipping Documents:
T110II EMEA1 Ship Docs No Power Cord
(English/French/German/Spanish/Russian/Hebrew)
509989 1 [340-25318] 21
RAID Connectivity:
My Selections All Options](https://image.slidesharecdn.com/f821b533-e862-4bd9-8e87-33972dff6dc2-150308195443-conversion-gate01/85/Cilent-to-server-network-plan-18-320.jpg)
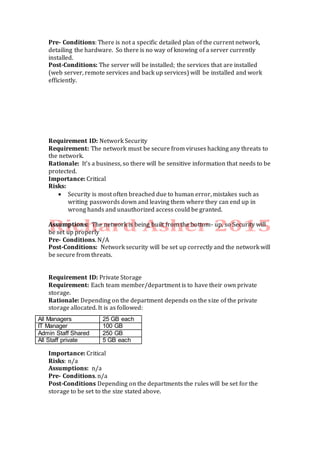
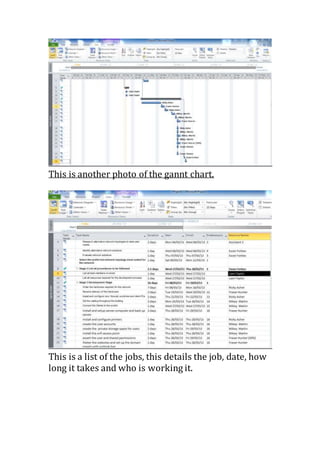
![27/ 02/ 2013 01:43The Dell Online Store: Build Your System
Page 2 of 3http:/ / configure.euro.dell.com/ dellstore/ print_summary_details_po…c= svt110ii&s= bsd&vw= classic&leadtime= 05/ 03/ 2013&showleadtime= True
C1 4HD - No RAID with On-board SATA Controller,
Requires 1-4 SATA HDDs
510002 1 [780-12786] 1009
Primary Hard Drive:
1TB, SATA, 3.5-in, 7.2K RPM Hard Drive (Cabled)
305583 1 [400-18492] 1209
Power Cord:
UK 250V 2M Power Cord 10A
256929 1 [450-13370] 207
Server Management Card:
Embedded Baseboard Management Controller
256923 1 [565-10165] 1314
Network Cards:
Intel® PRO/1000PT GbE Single Port Server
Adapter, Cu, PCIe-1
60757 1 [540-10371] 1230
Optical Devices:
16X DVD-ROM Drive with SATA Cable
569529 1 [429-15949] 16
Mouse:
Dell MS111 USB Optical Mouse
425997 1 [570-11091] 12
Monitor:
Display Not Included
5931 1 [480-10611] 5
Systems Management:
PE T110II Electronic System Documentation and
OpenManage DVD
510021 1 [631-10807] 49
Gedis Bundle Reference:
SVT110II
581097 1 [200-87266] 22
Order Information:
PowerEdge Order - United Kingdom
32396 1 [800-10511] 111
Base warranty:
1Yr Basic Warranty - Next Business Day -
Minimum Warranty
315107 1
[709-10513]
[709-10514]
29
Support Services:
1Yr Basic Warranty - NBD Included - No Upgrade
Selected
315183 1 [710-18105] 30
Dell Services: Installations:
No Installation Service Selected (Contact Sales rep
for more details)
58267 1 [683-11870] 1290
Remote Advisory Service:
Declined Remote Advisory
691639 1 [715-10838] 735
Proactive Maintenance:
Declined Proactive Maintenance (info)
135789 1 [713-10026] 140
Print
How to Contact Dell
SMALL BUSINESS Phone Fax Email/ Web
Companies with fewer than 200 employees
General Sales 0870 907 5819
Software & Peripherals Sales 0870 907 5083
Order Status (system orders only) 0870 907 4712
Customer Care General Order Enquiries 0870 906 0010
Technical Support Queries 0870 908 0800
Address
Dell Computer Corporation
Dell House
The Boulevard](https://image.slidesharecdn.com/f821b533-e862-4bd9-8e87-33972dff6dc2-150308195443-conversion-gate01/85/Cilent-to-server-network-plan-19-320.jpg)
![Bibliography
1. Wikipedia, [online] Available at < http://www.wikipedia.org > [Accessed
1st February]
2. Ehow, [online] Available at http://www.ehow.co.uk > [Accessed 28th
february]
3
Windows live domain email , [online] Available at
http://www.domains.live.com
3. > [Accessed 29th february](https://image.slidesharecdn.com/f821b533-e862-4bd9-8e87-33972dff6dc2-150308195443-conversion-gate01/85/Cilent-to-server-network-plan-20-320.jpg)