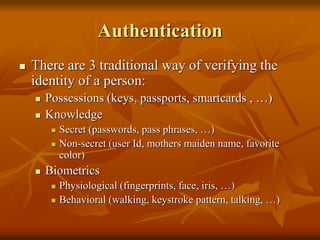
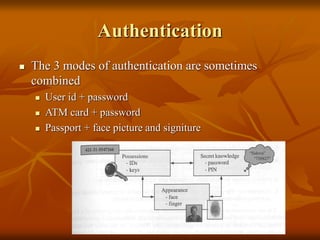
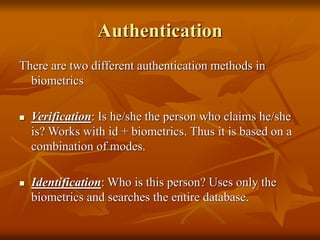
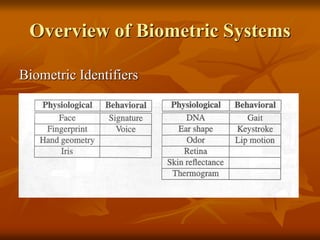
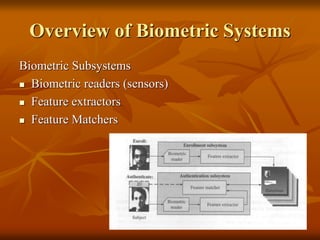
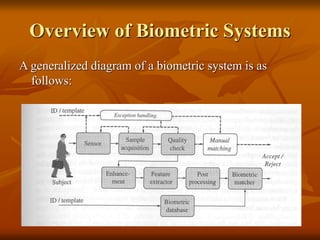
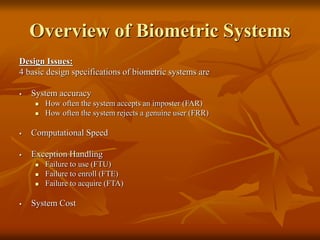
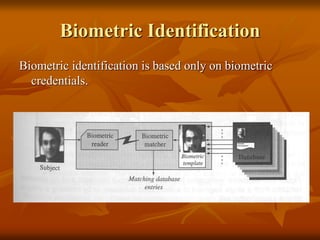
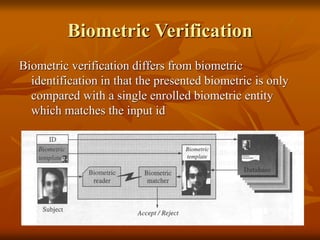
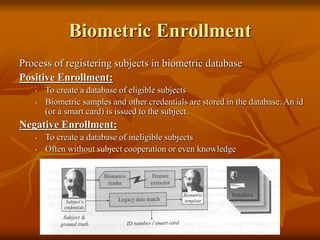
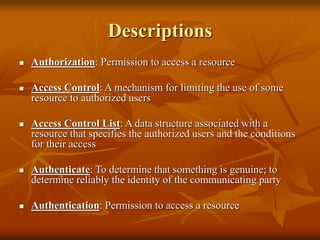
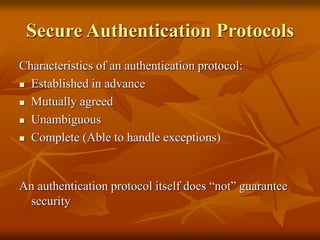
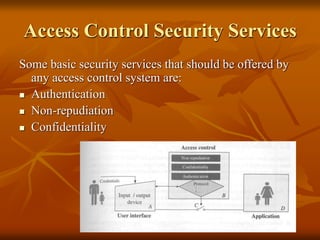
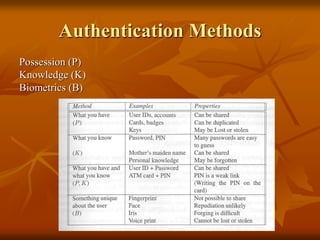
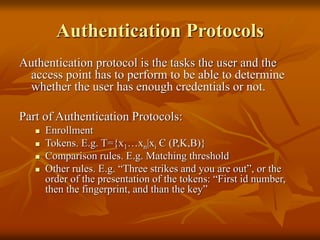
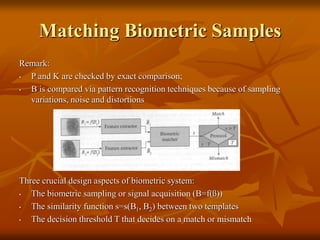
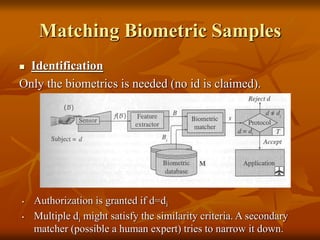
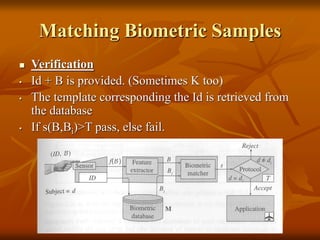
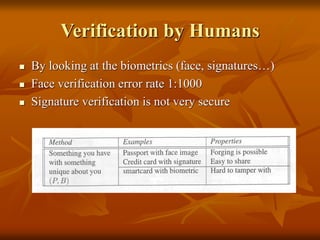
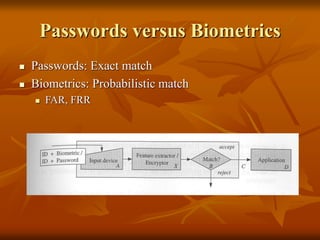
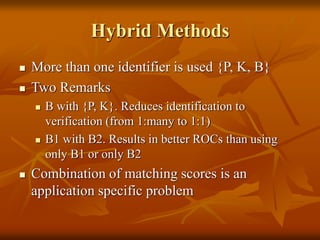
This document provides an overview of biometrics and biometric systems. It discusses authentication methods including possessions, knowledge, and biometrics. Biometric identification works by searching an entire database to identify a person based on their biometrics, while verification compares a biometric to a single enrolled template. Key aspects of biometric systems include enrollment, feature extraction, matching, and system design considerations like accuracy and speed. Security concerns with biometric systems include presenting biometrics when the owner is absent or hacking the system. Hybrid authentication methods that combine multiple factors like possessions, knowledge, and biometrics can provide stronger authentication than single-factor biometrics alone.