This document provides an overview of information and communication technology (ICT) and discusses its usage, impacts, and related ethical and legal issues.
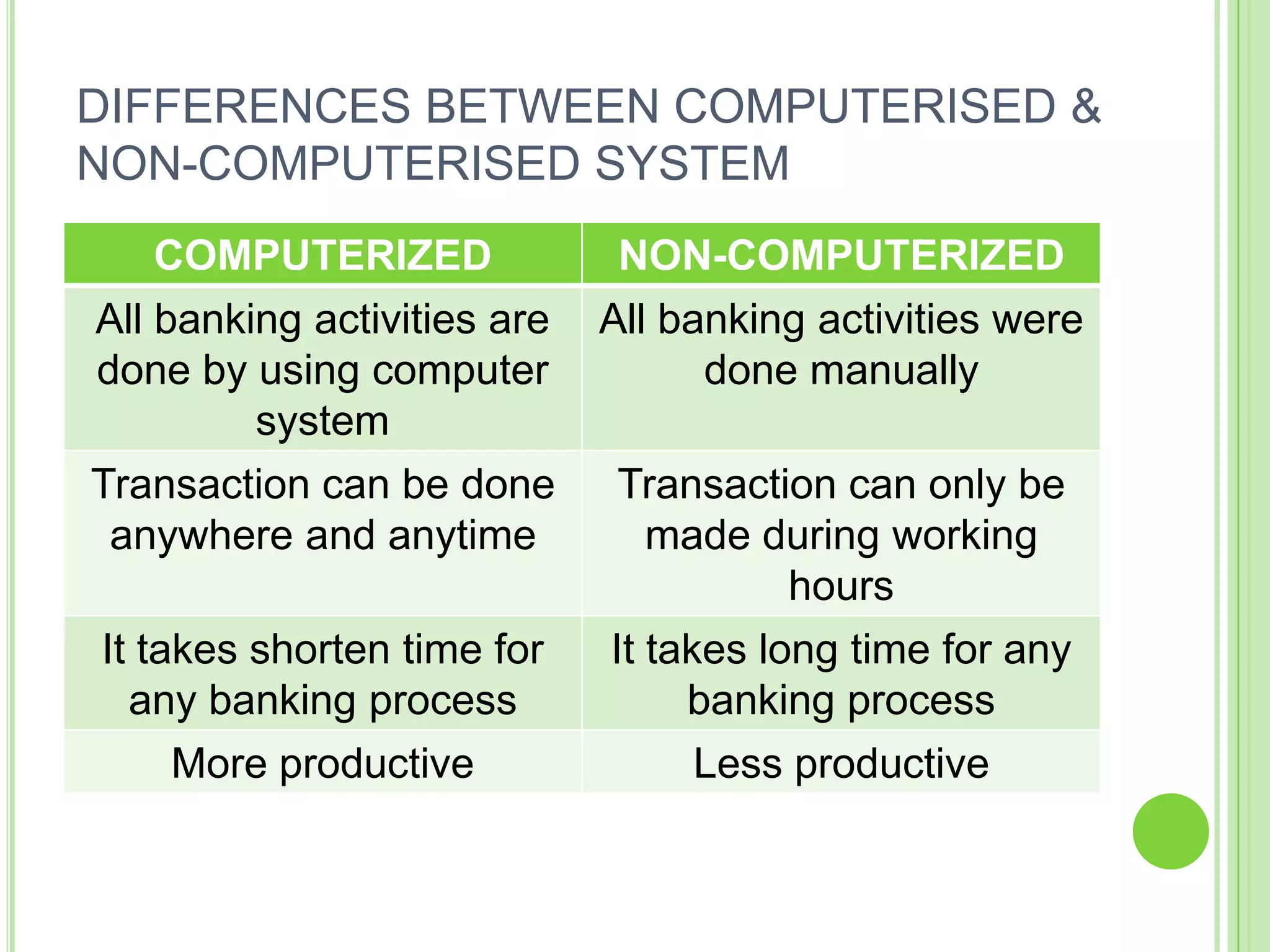
[1] ICT refers to technologies that are used to store, process, transmit and retrieve information electronically. Examples of its everyday usage include education, banking, industry, and e-commerce.
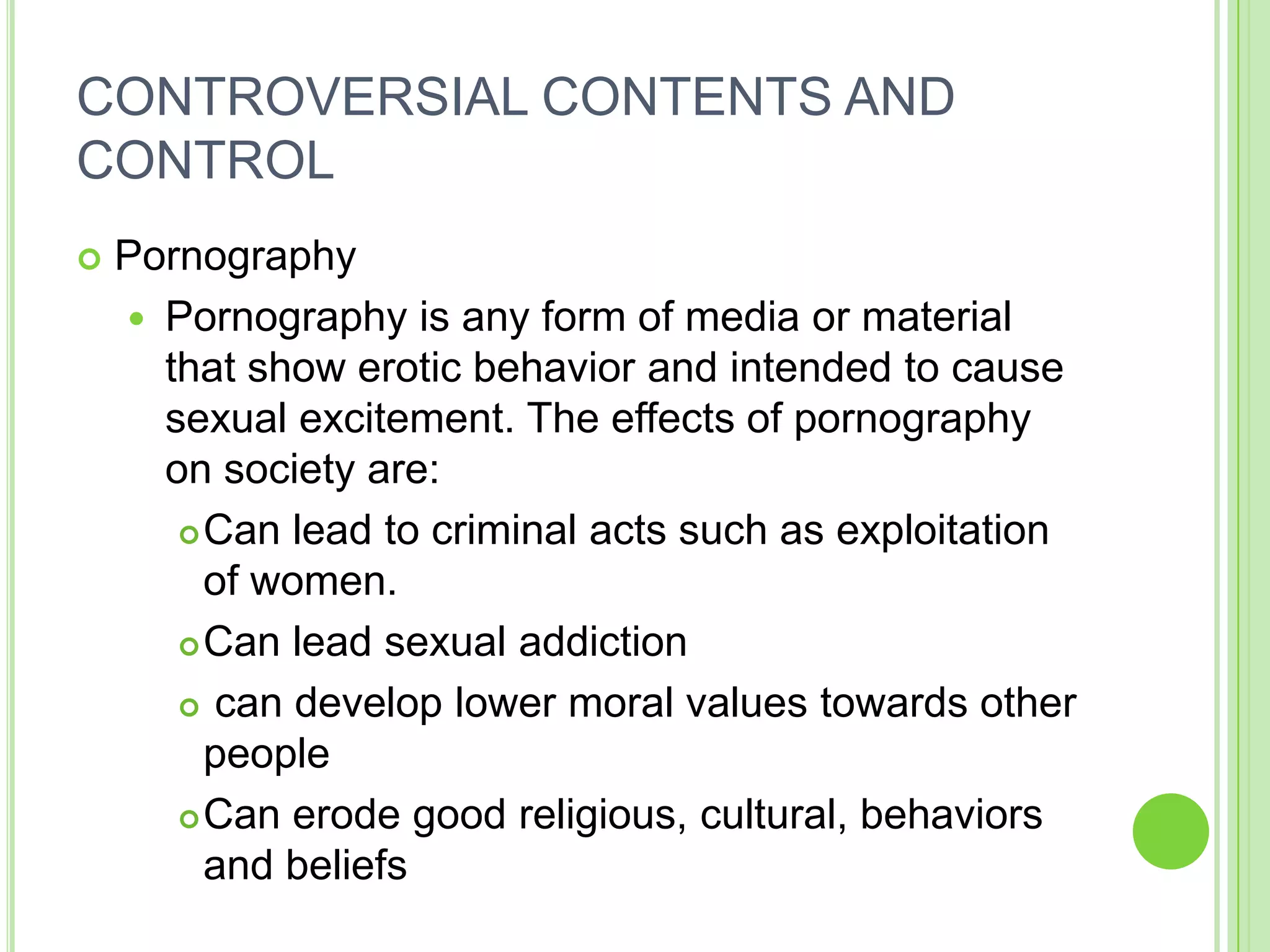
[2] Both positive and negative impacts of ICT on society are discussed. Positively, it enables faster communication, lower costs, and borderless sharing of information. Negatively, it can encourage access to inappropriate content and prolonged computer use can harm health.
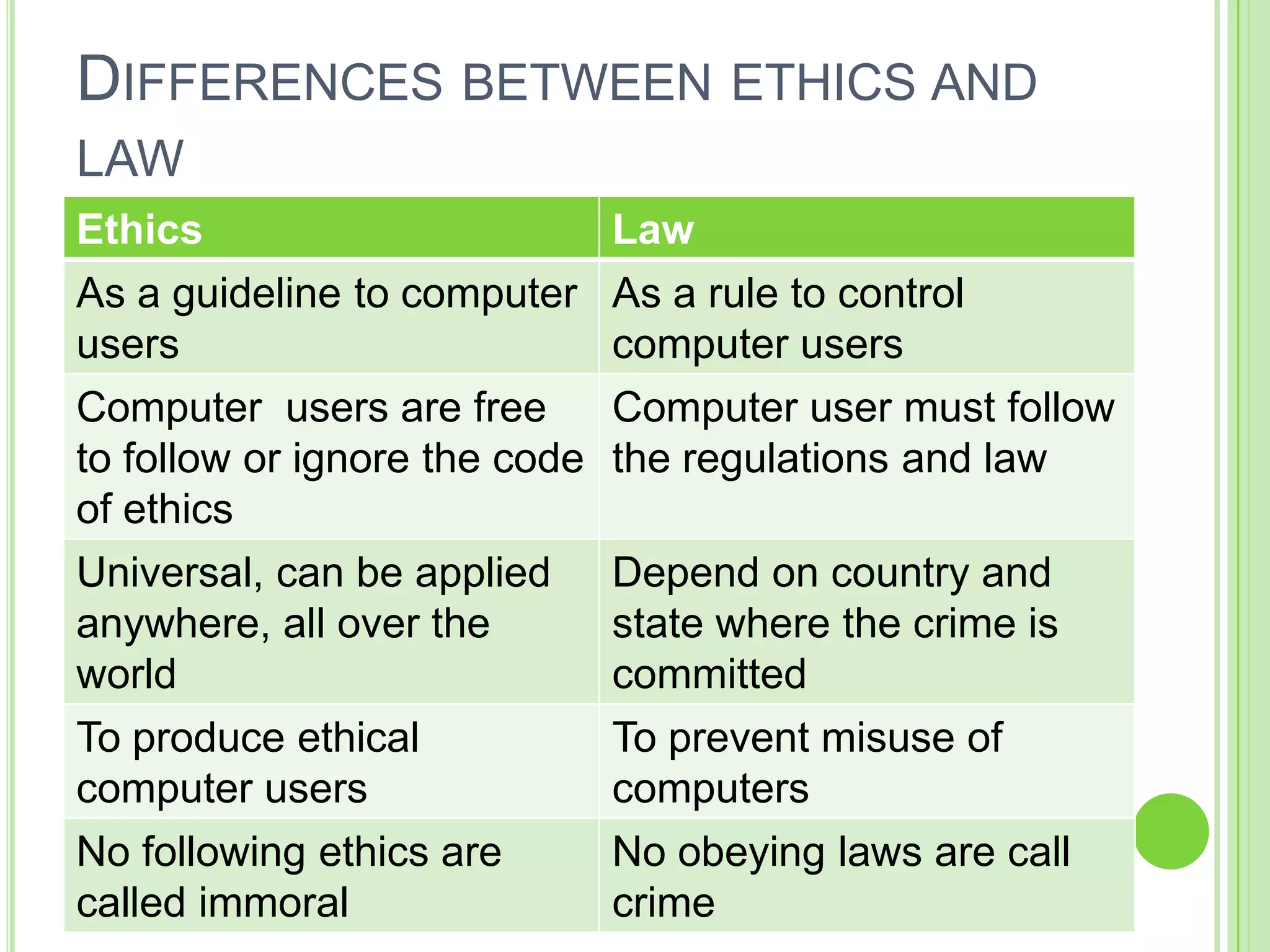
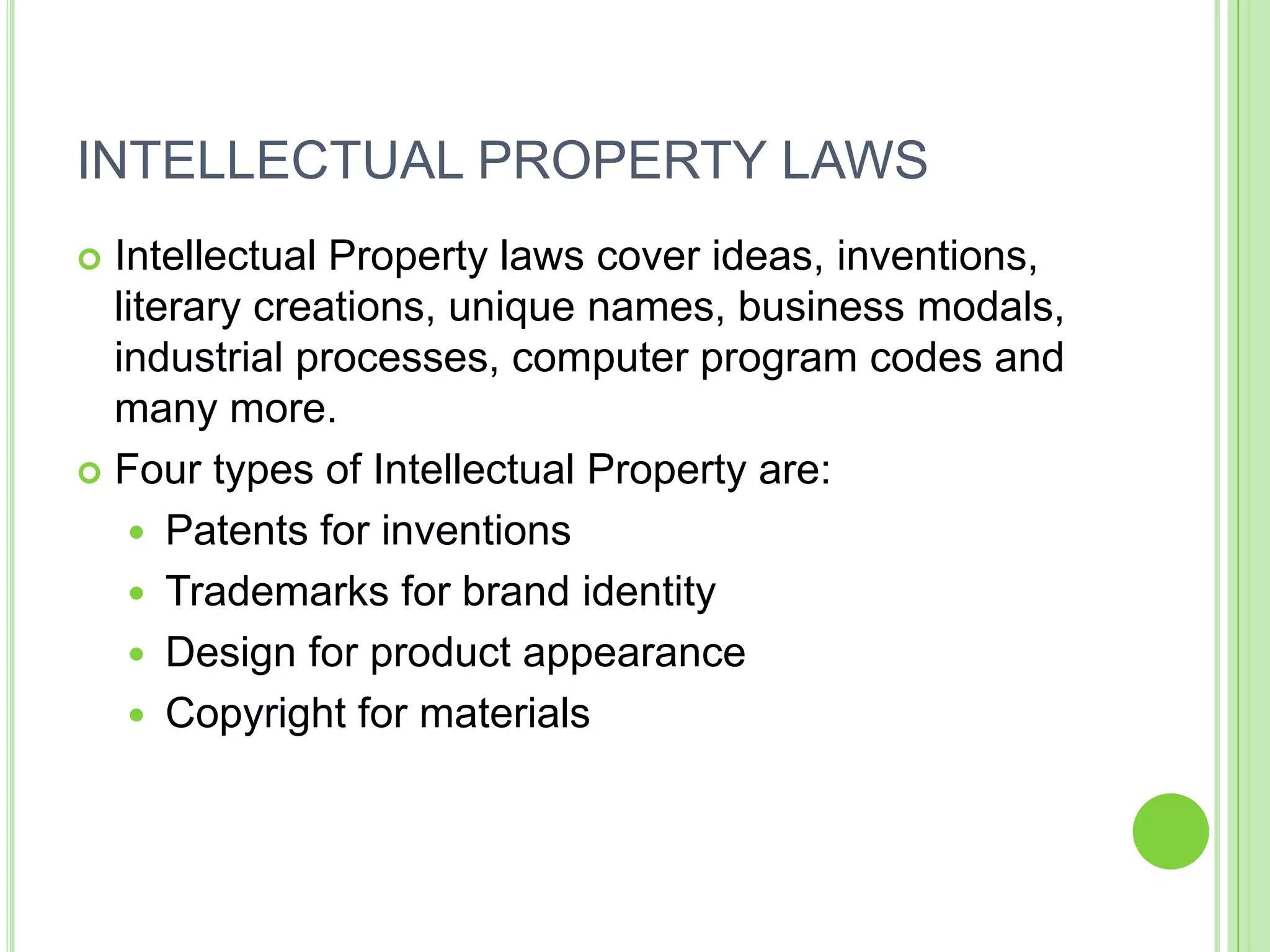
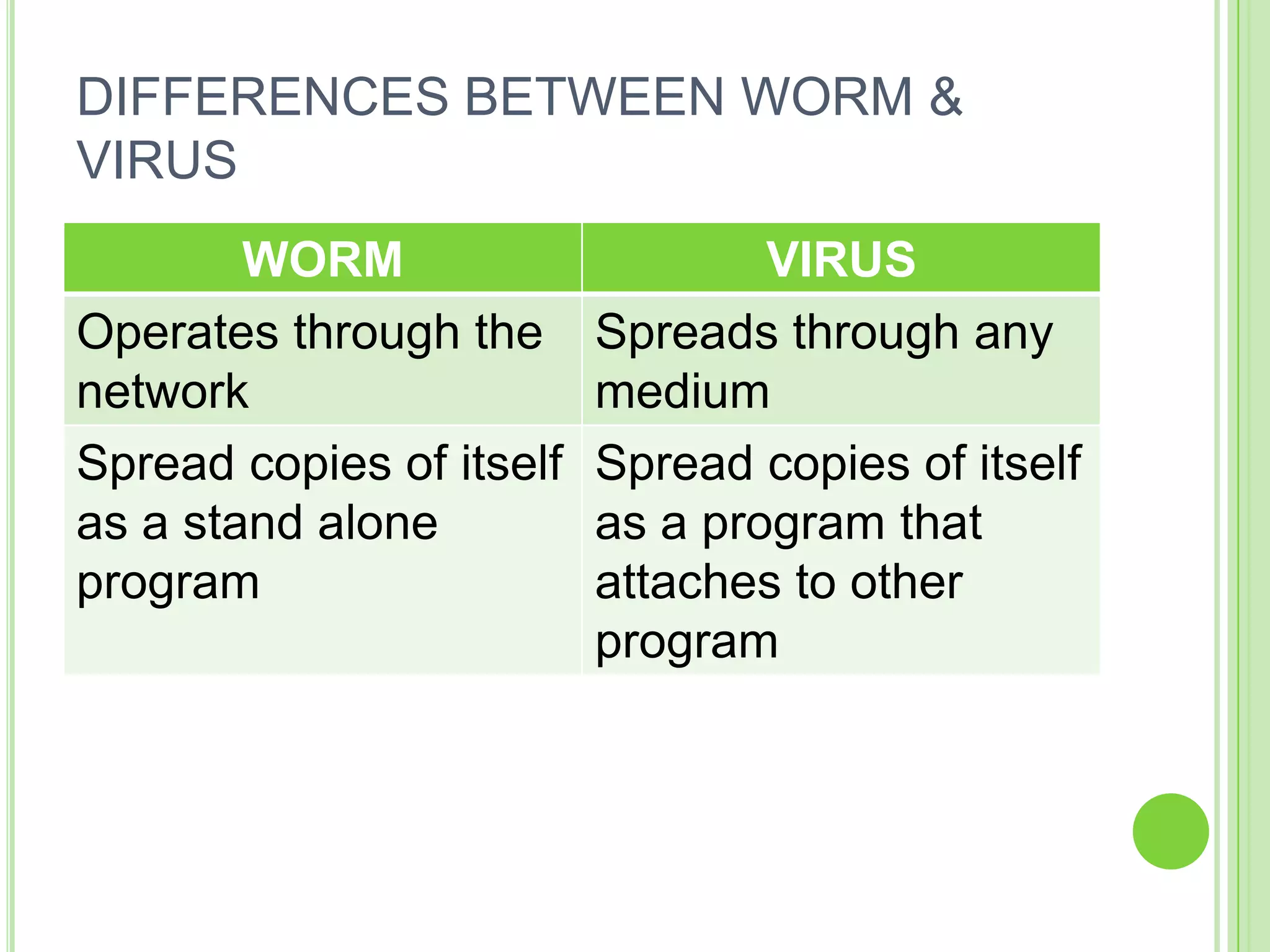
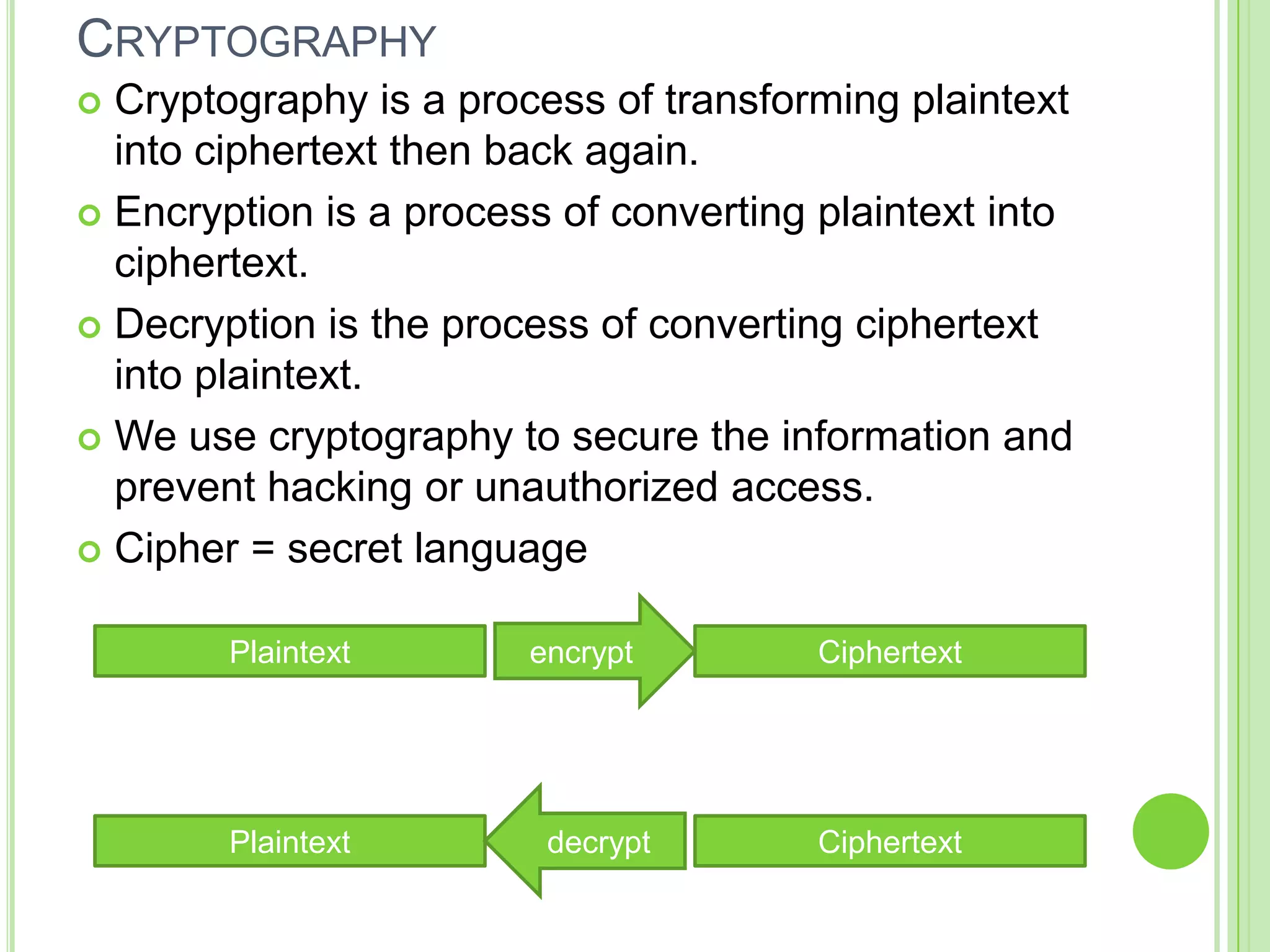
[3] Ethical and legal issues surrounding ICT like privacy, intellectual property, computer crimes