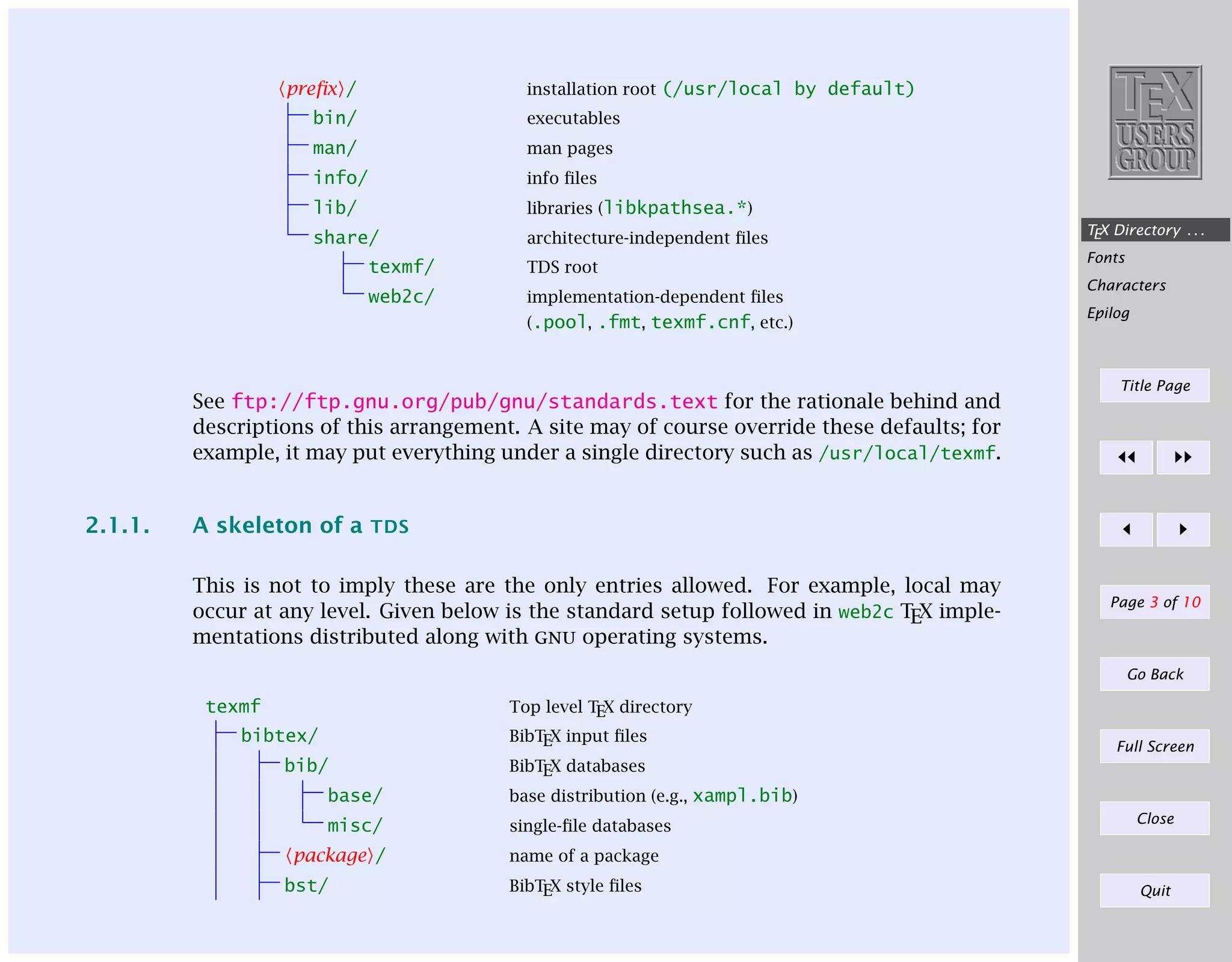
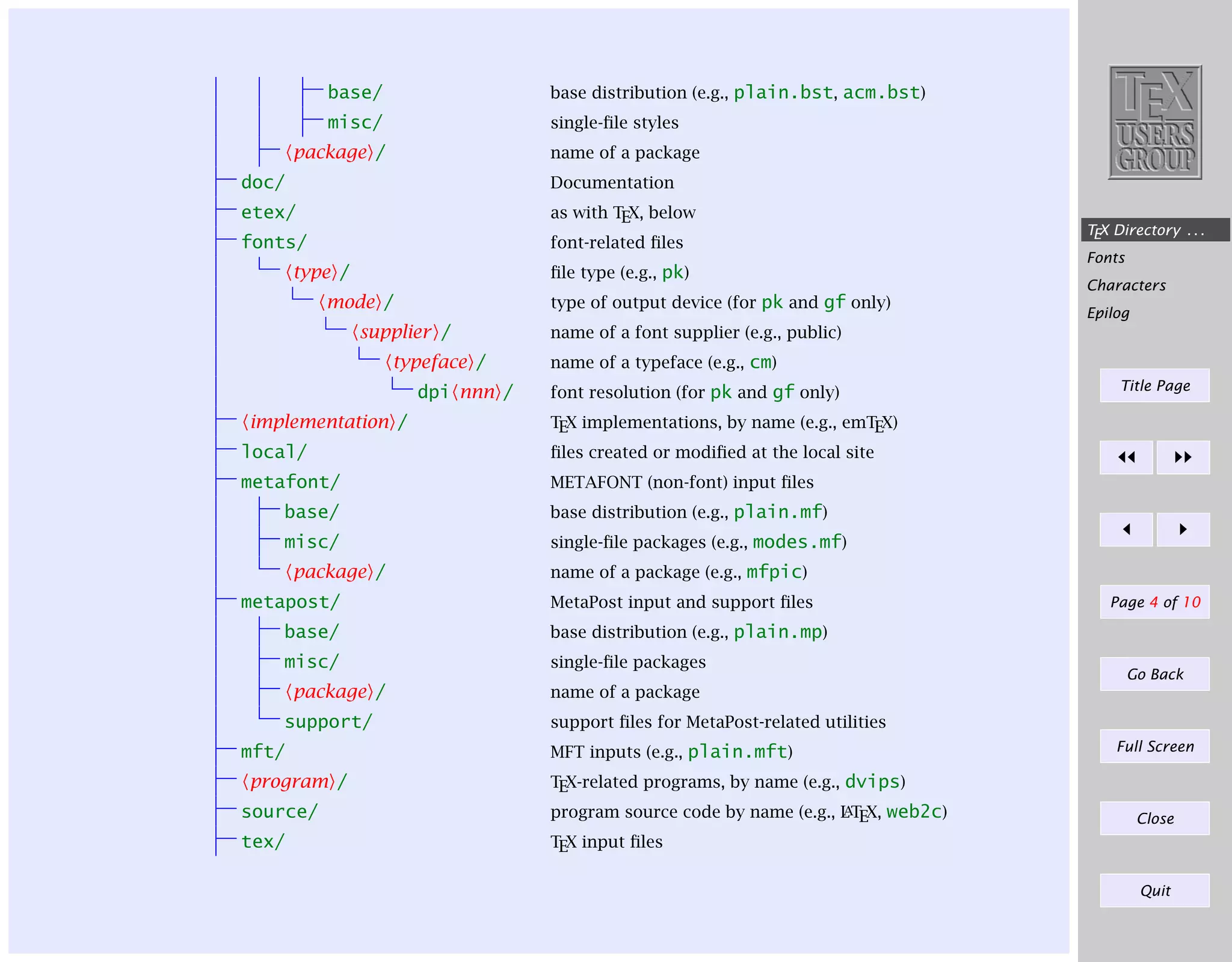
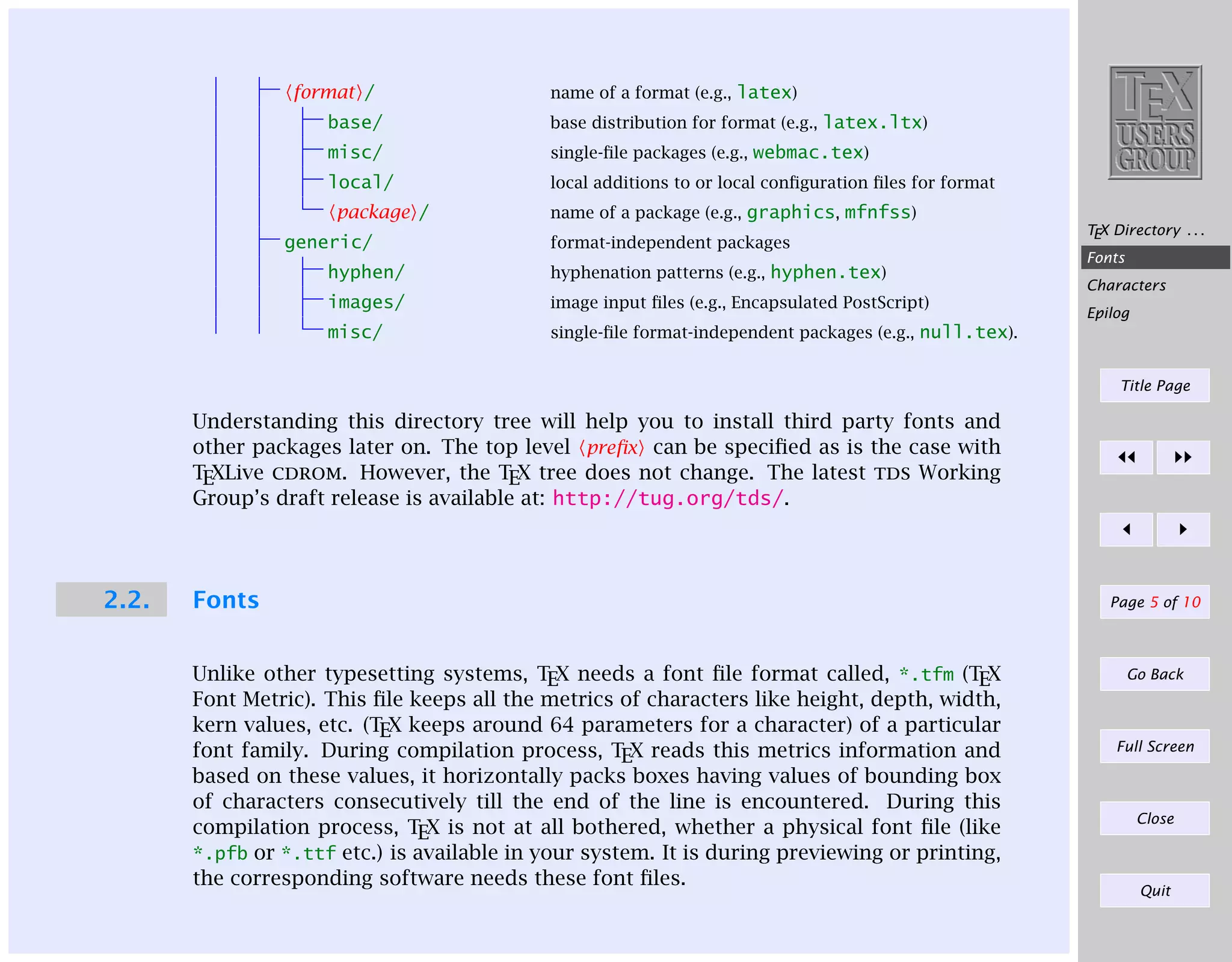
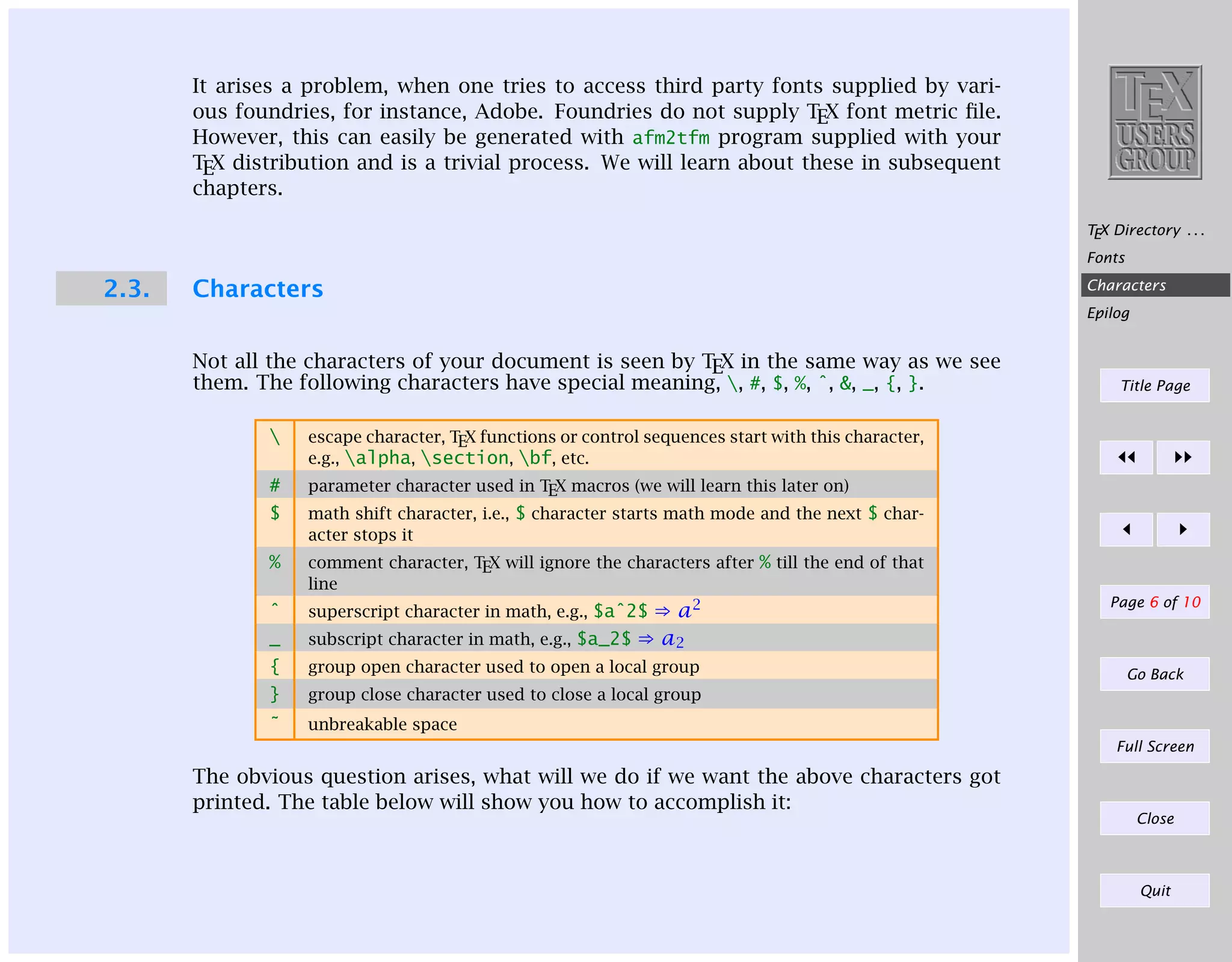
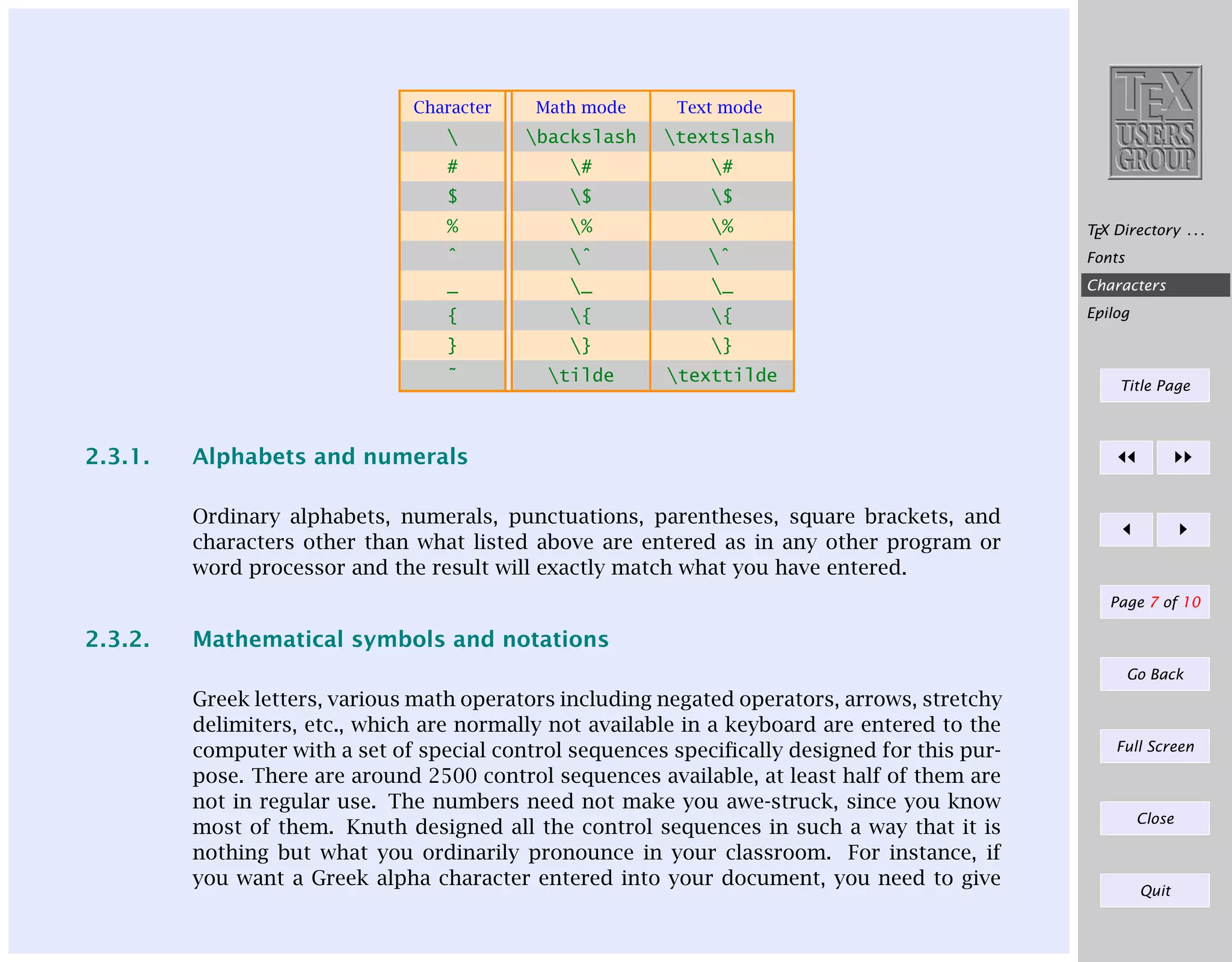
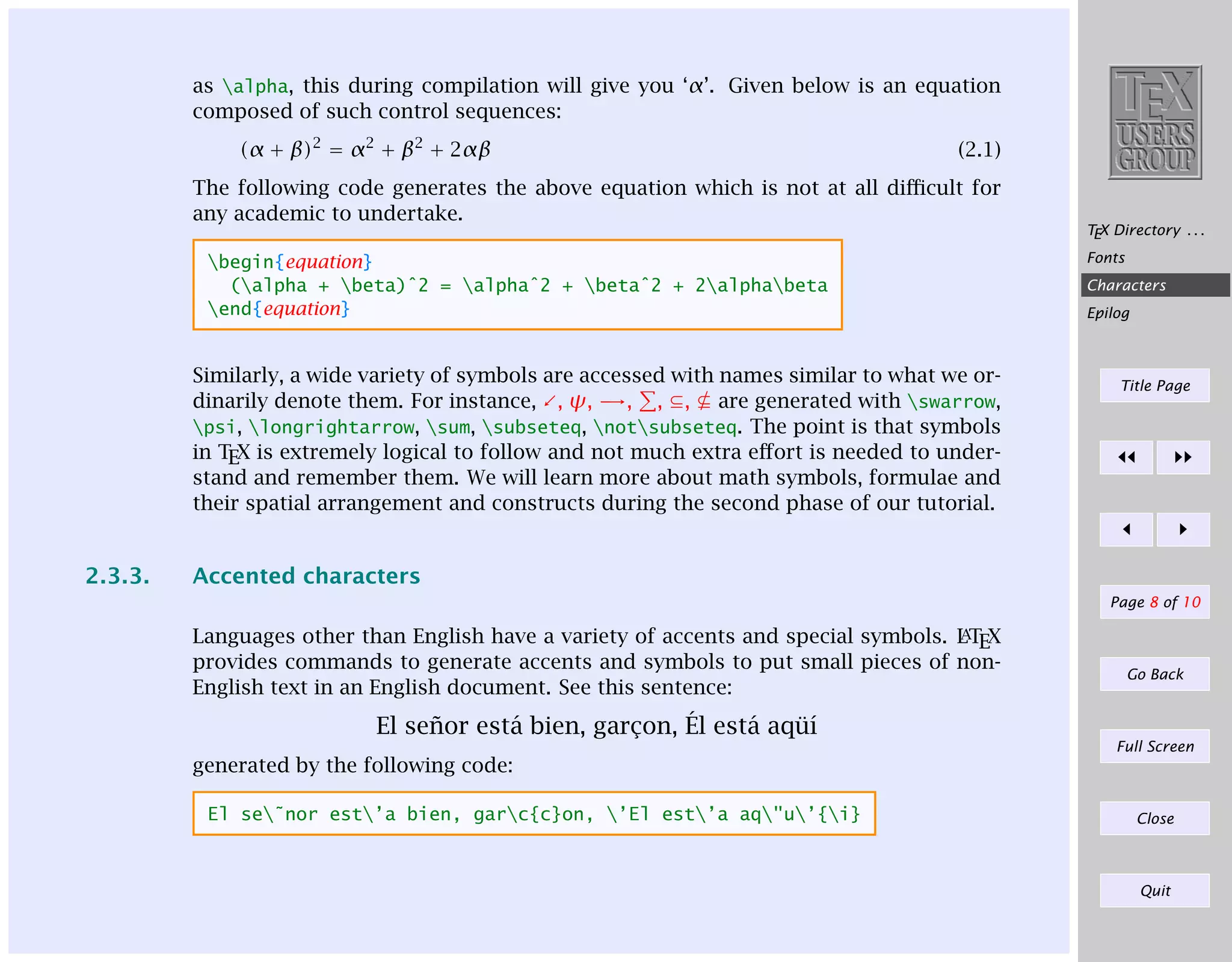
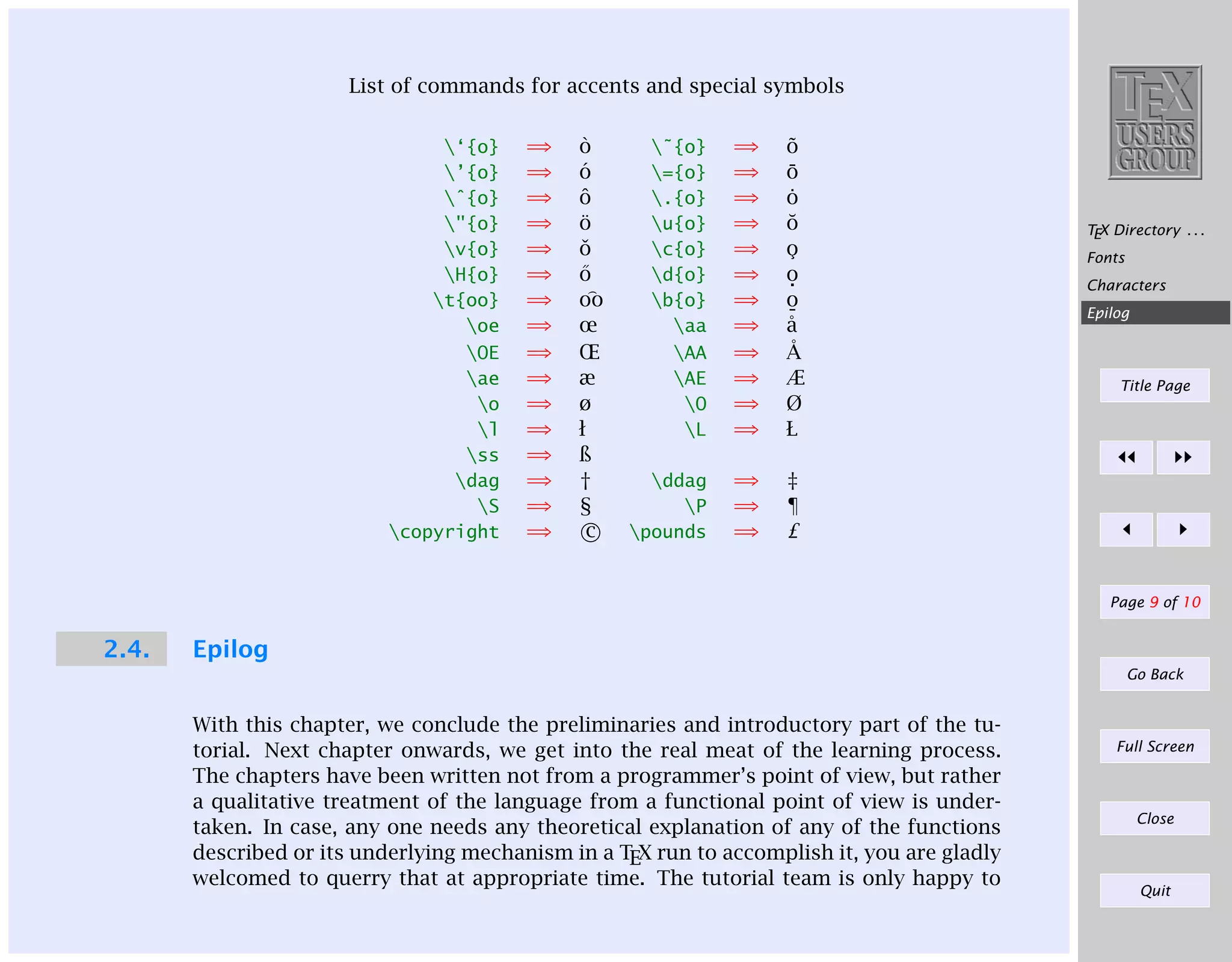
This document provides an overview of some key conventions in LaTeX, including the TeX Directory Structure (TDS) that organizes TeX-related files in a structured folder hierarchy. It describes the standard locations for files like documentation, fonts, packages, and programs. It also discusses TeX's treatment of special characters and how they are displayed, as well as how to input mathematical symbols, Greek letters, and accented characters. The document is intended as an introductory tutorial on LaTeX conventions.