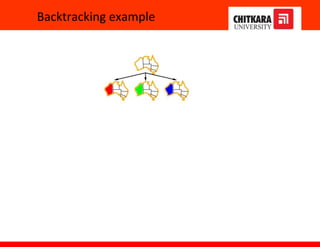
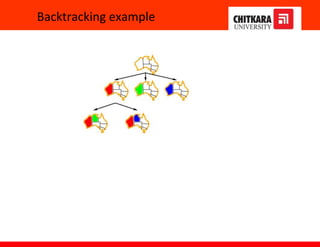
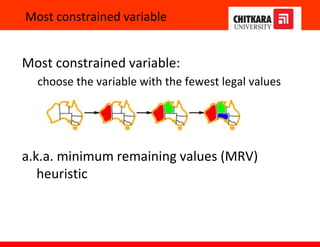
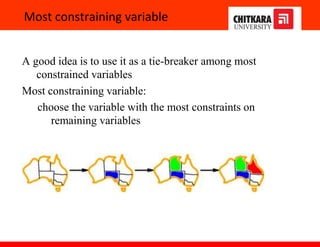
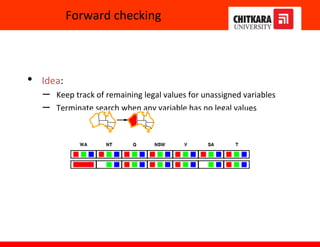
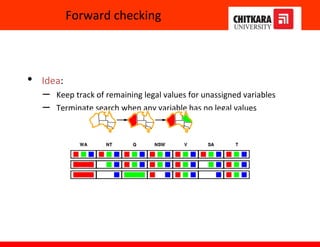
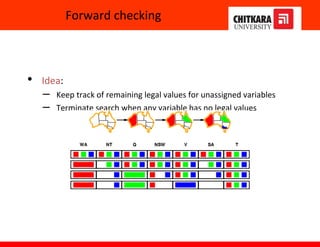
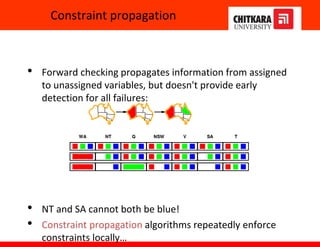
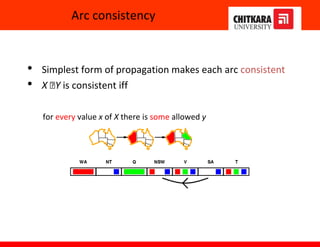
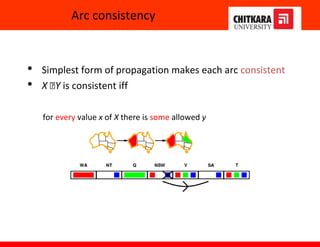
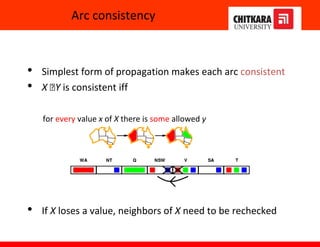
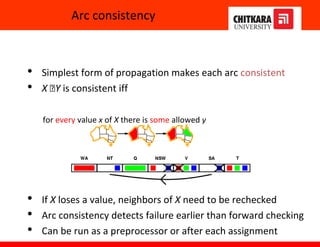
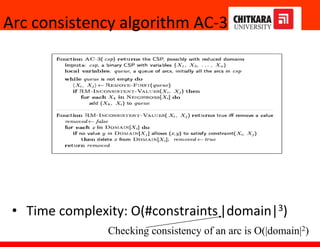
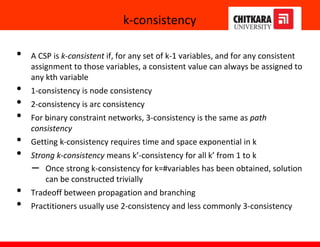
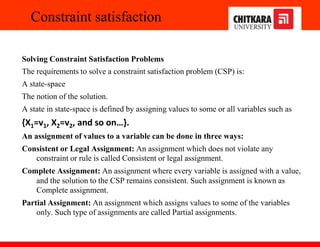
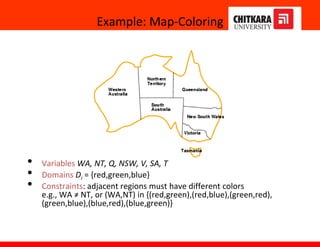
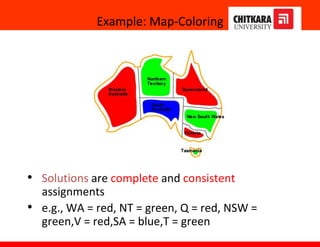
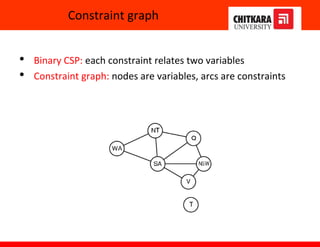
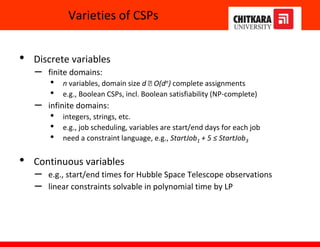
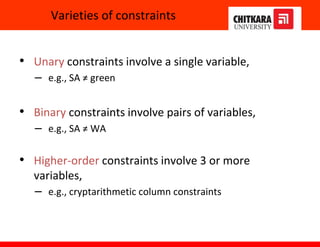
The document discusses constraint satisfaction problems and constraint propagation techniques for solving such problems. It defines constraint satisfaction as solving a problem under certain constraints or rules, where the values assigned to variables must satisfy those constraints. It describes the three main components of a constraint satisfaction problem as the set of variables, their domains, and the constraints. It then discusses solving constraint satisfaction problems using techniques like backtracking search and constraint propagation methods like arc consistency and k-consistency to reduce the search space.
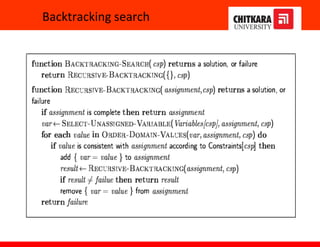
![Backtracking search
Variable assignments are commutative, i.e.,
[ WA = red then NT = green ] same as [ NT = green then WA = red ]
=> Only need to consider assignments to a single variable at each node
Depth-first search for CSPs with single-variable assignments is called
backtracking search
Can solve n-queens for n ≈ 25](https://image.slidesharecdn.com/ch67-230117170012-7598b920/85/CH6-7-pptx-11-320.jpg)