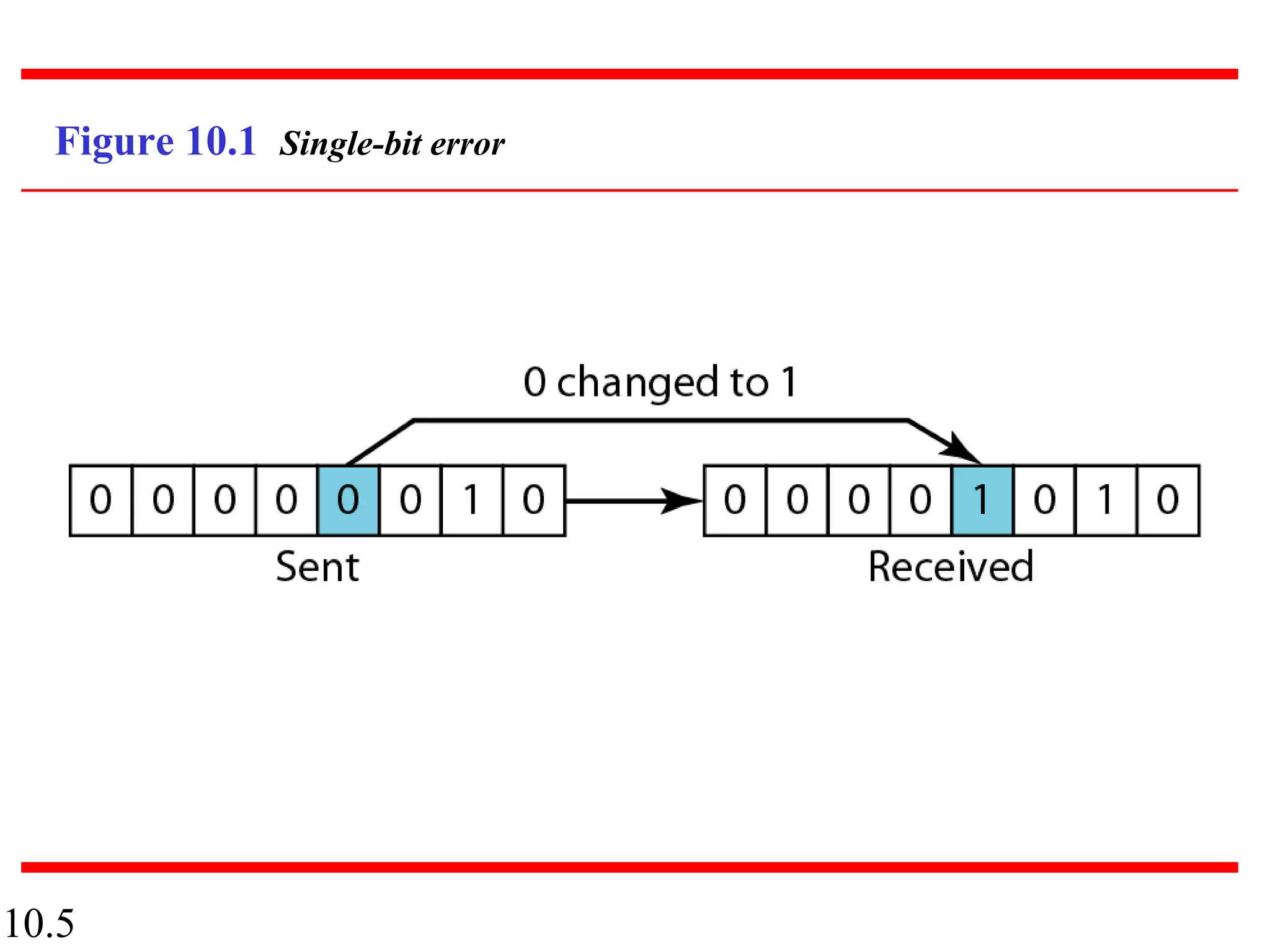
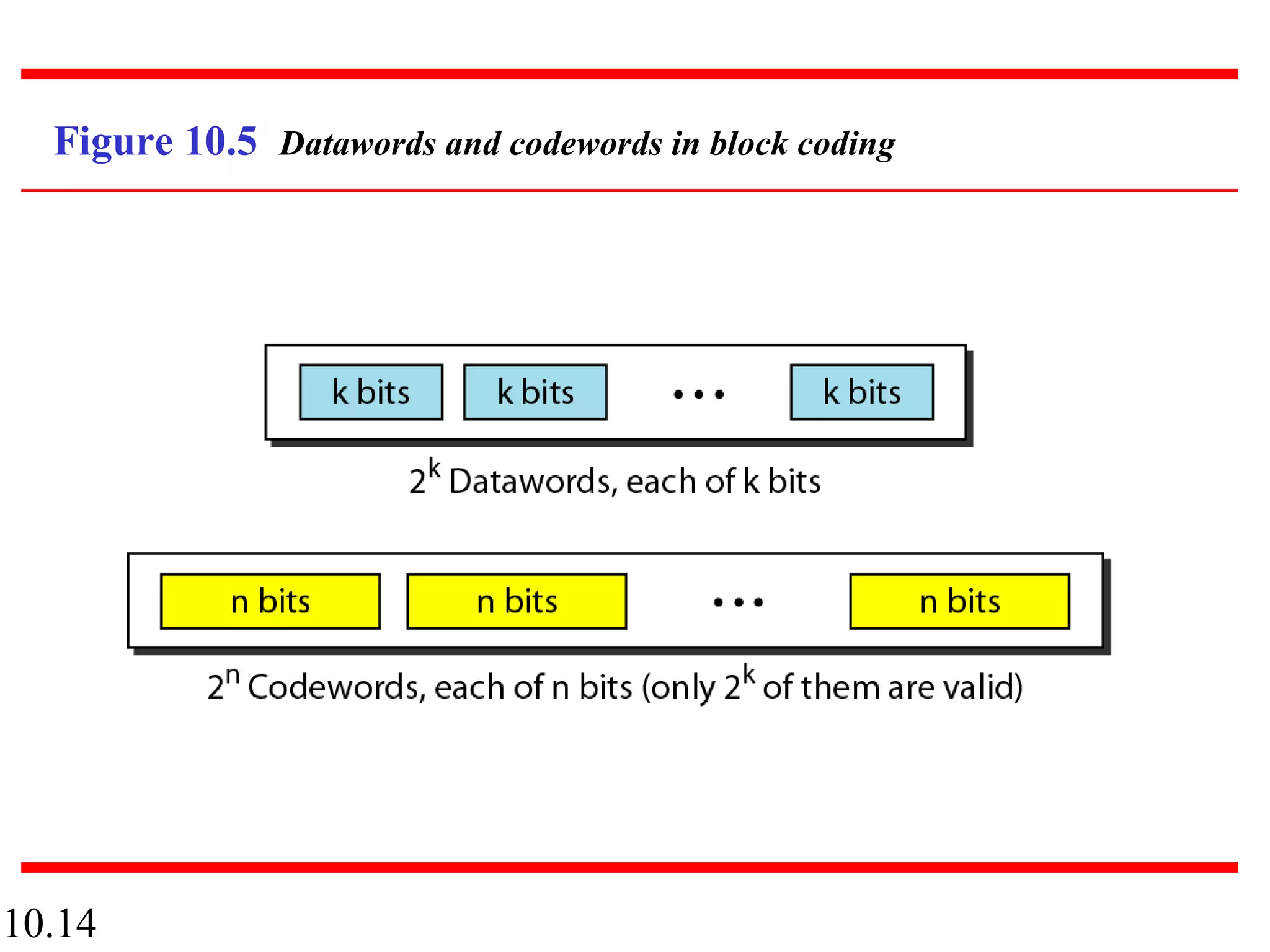
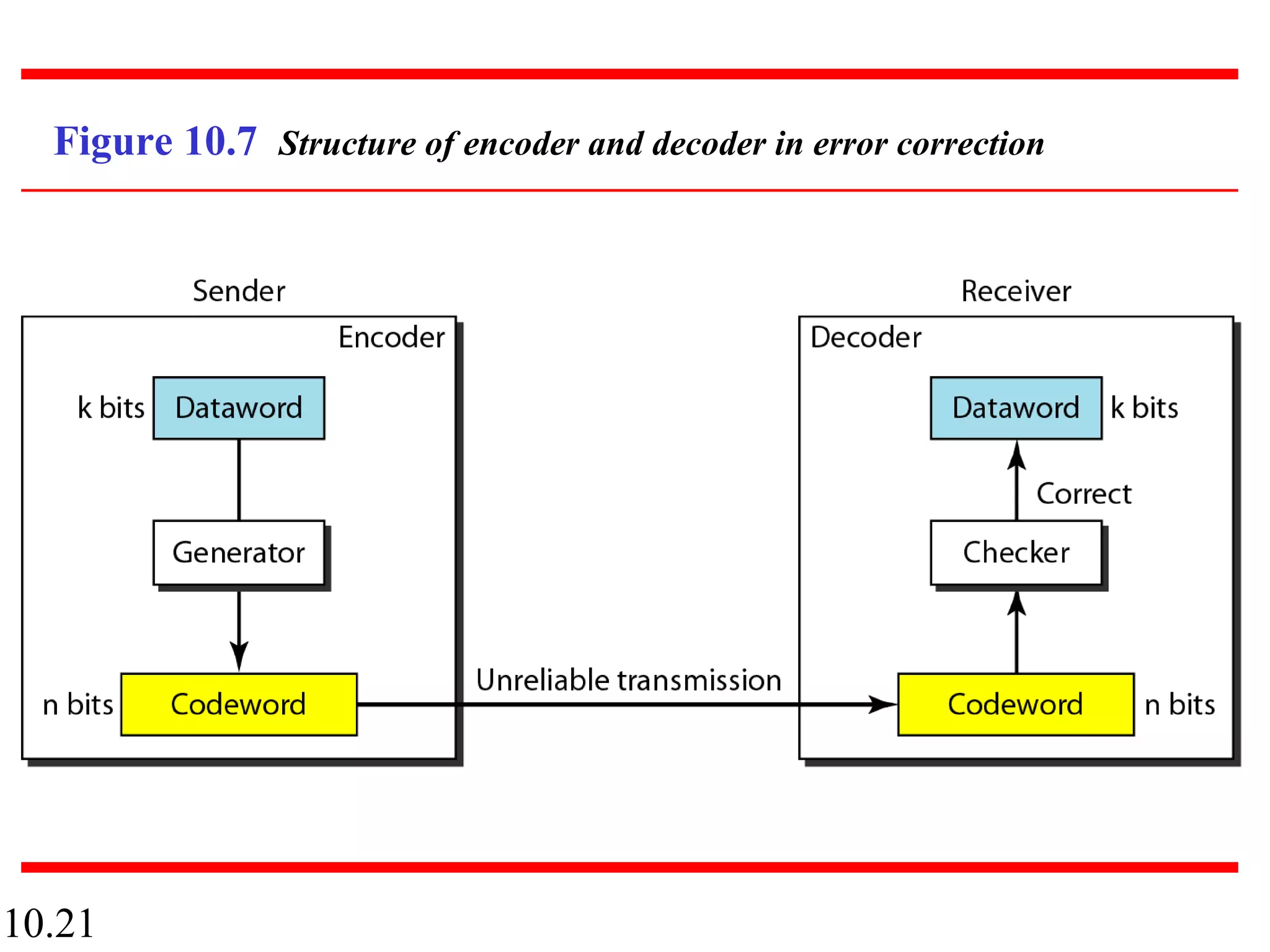
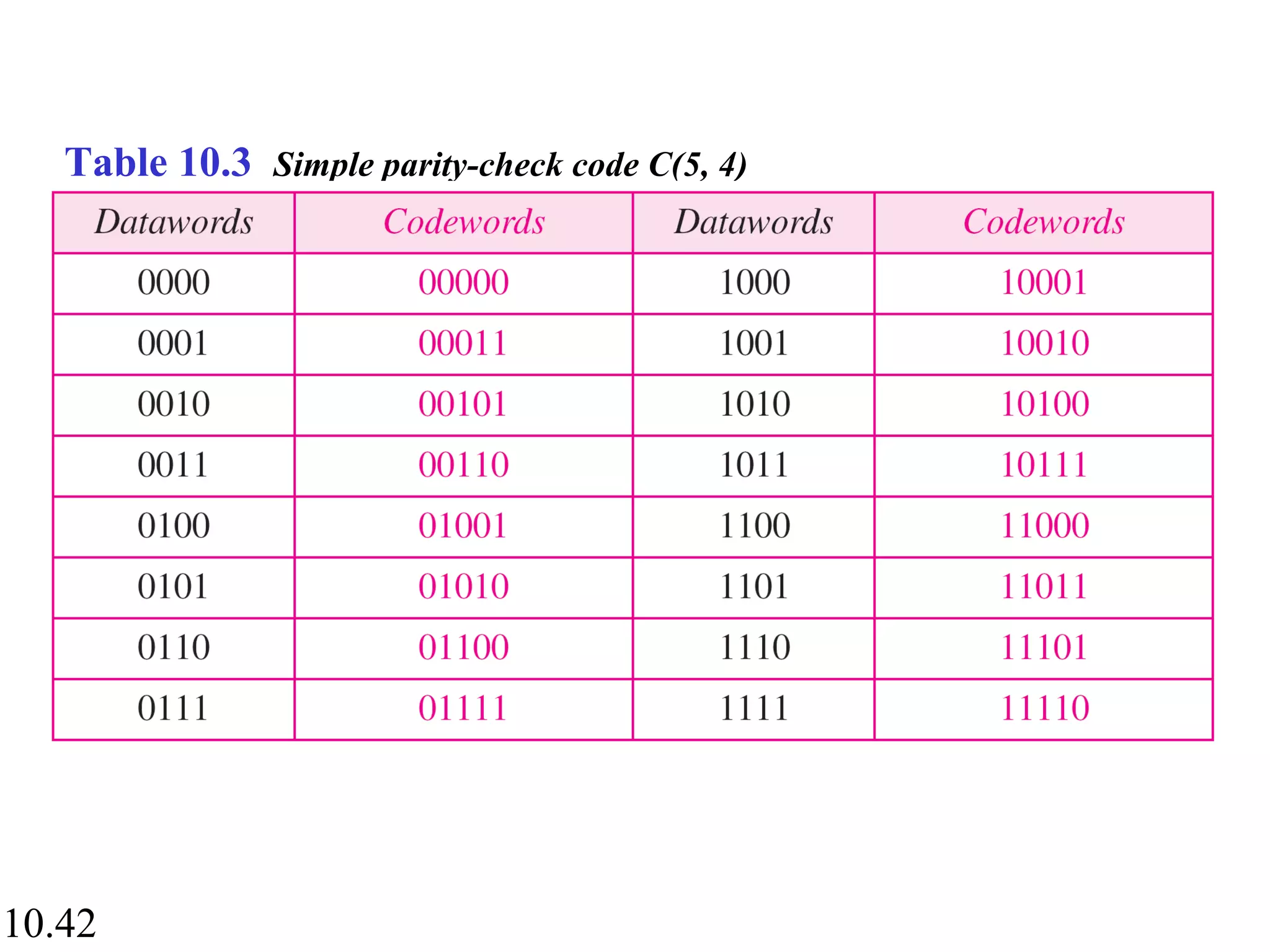
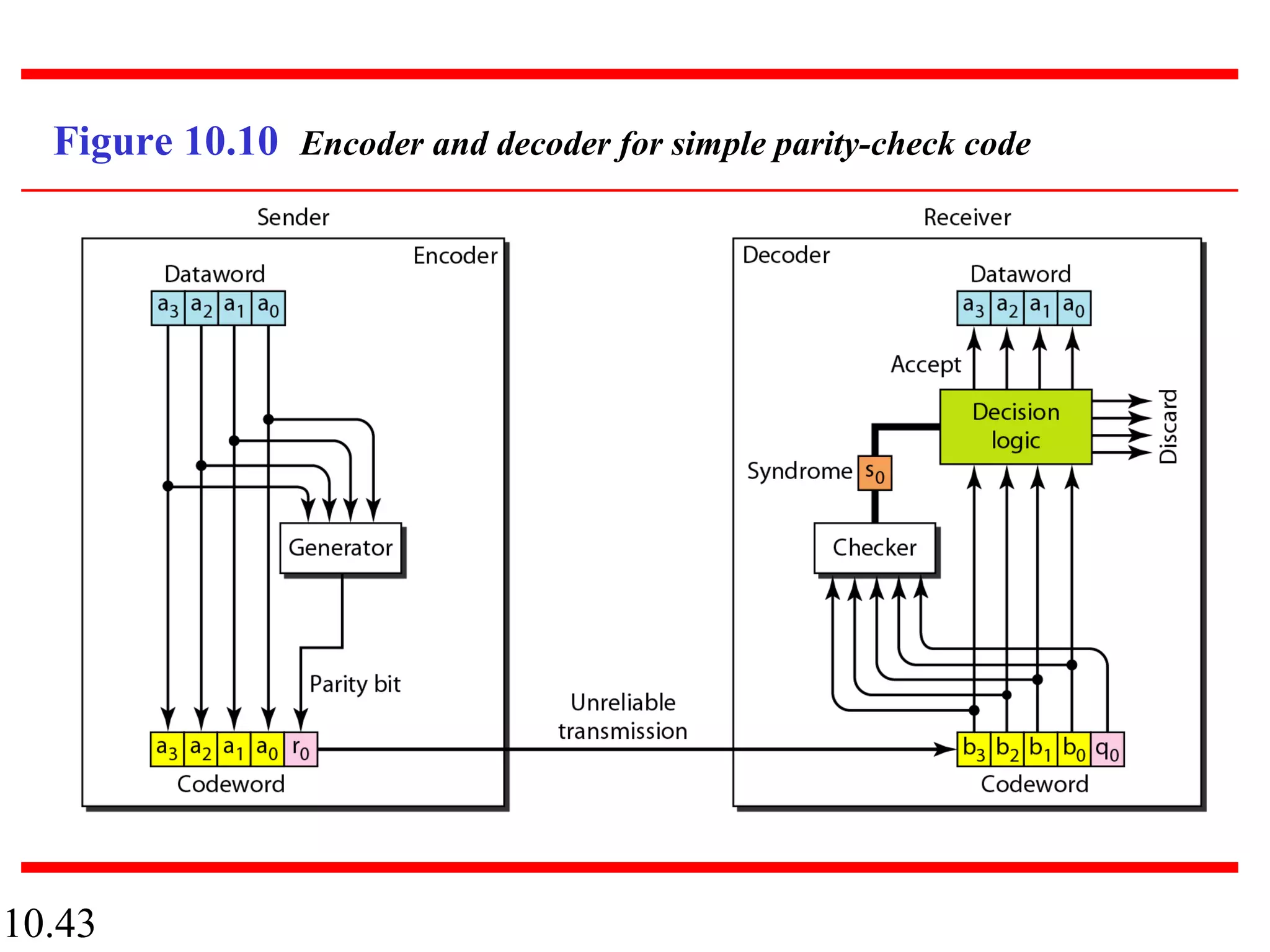
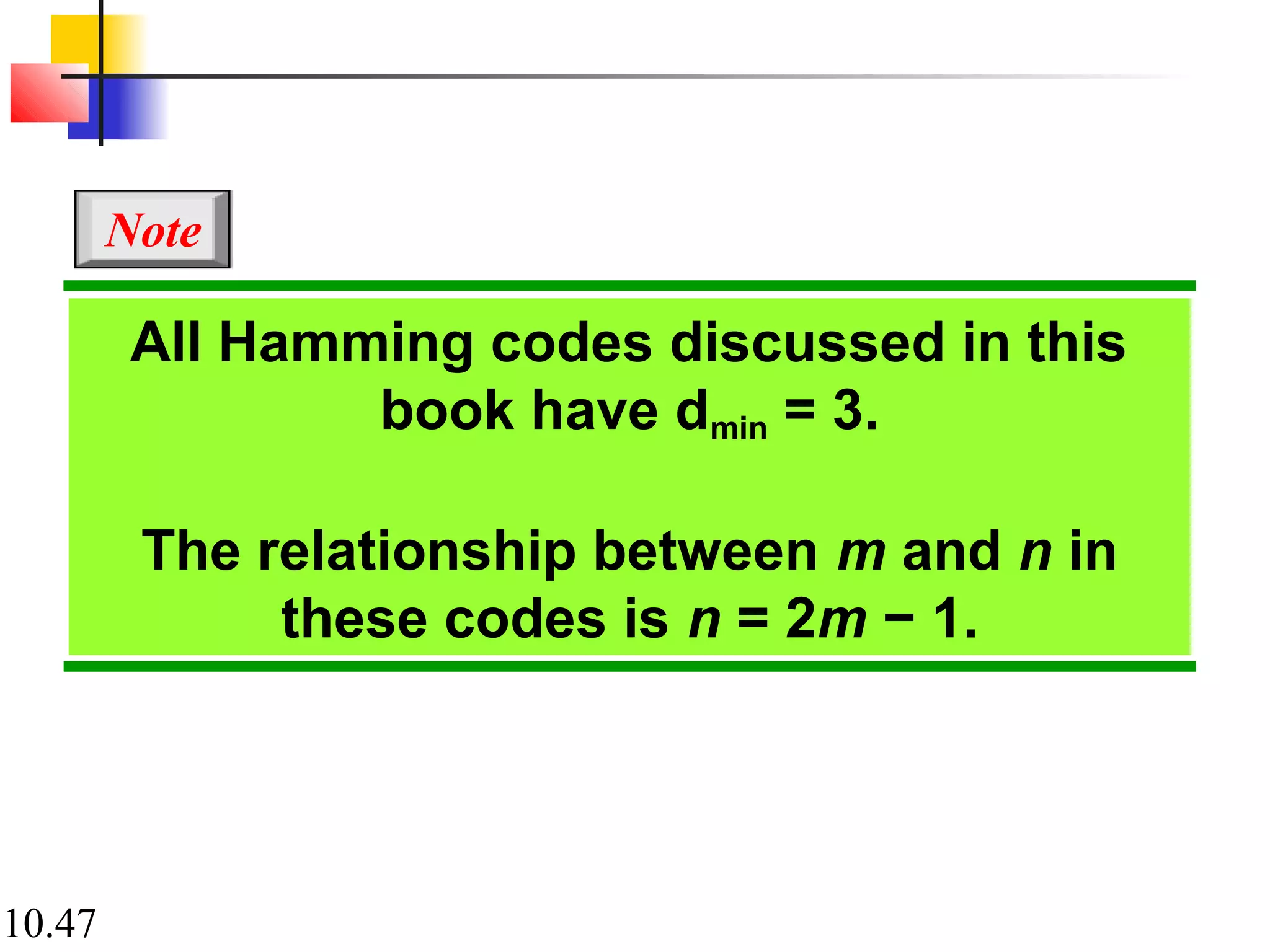
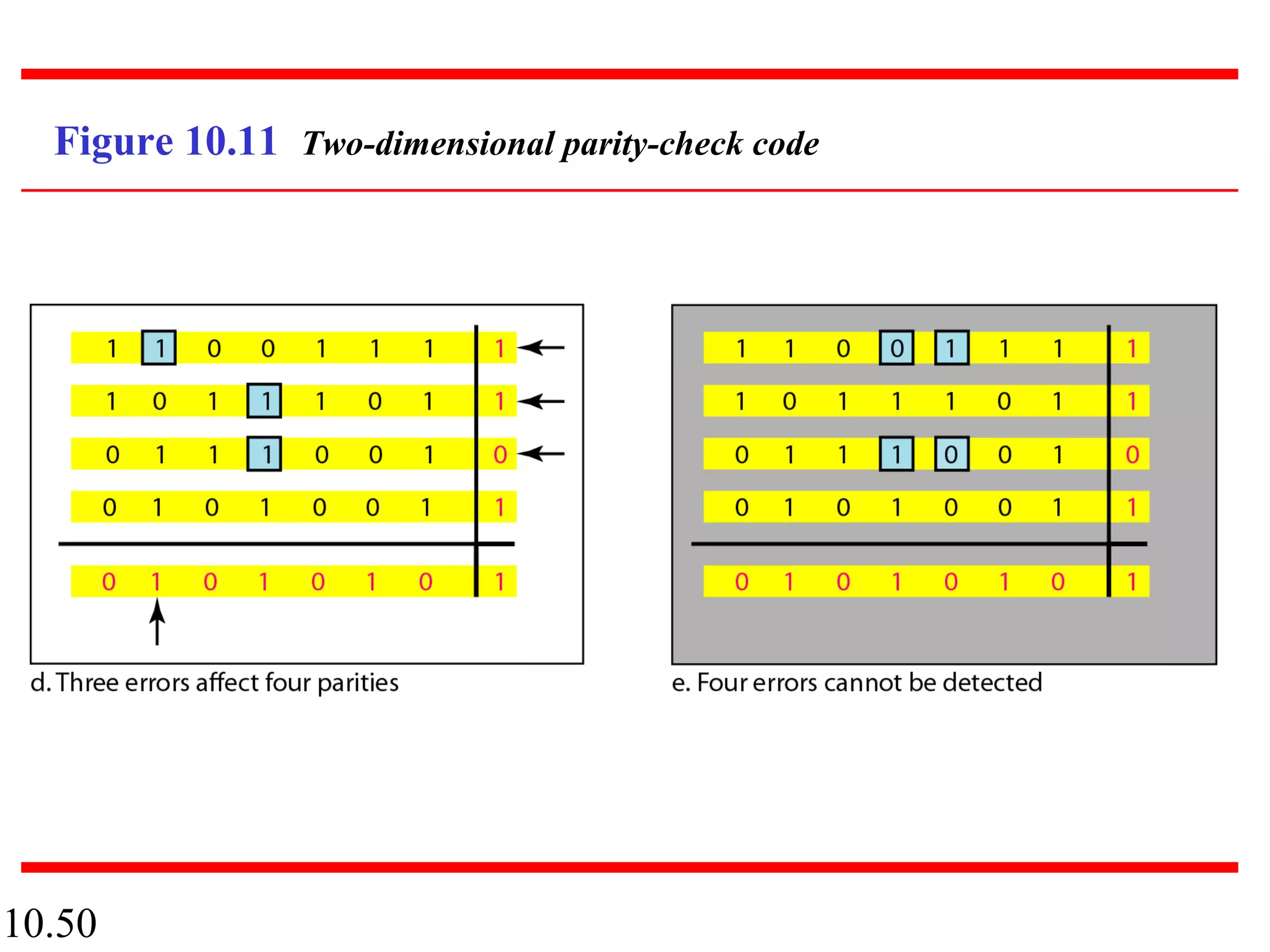
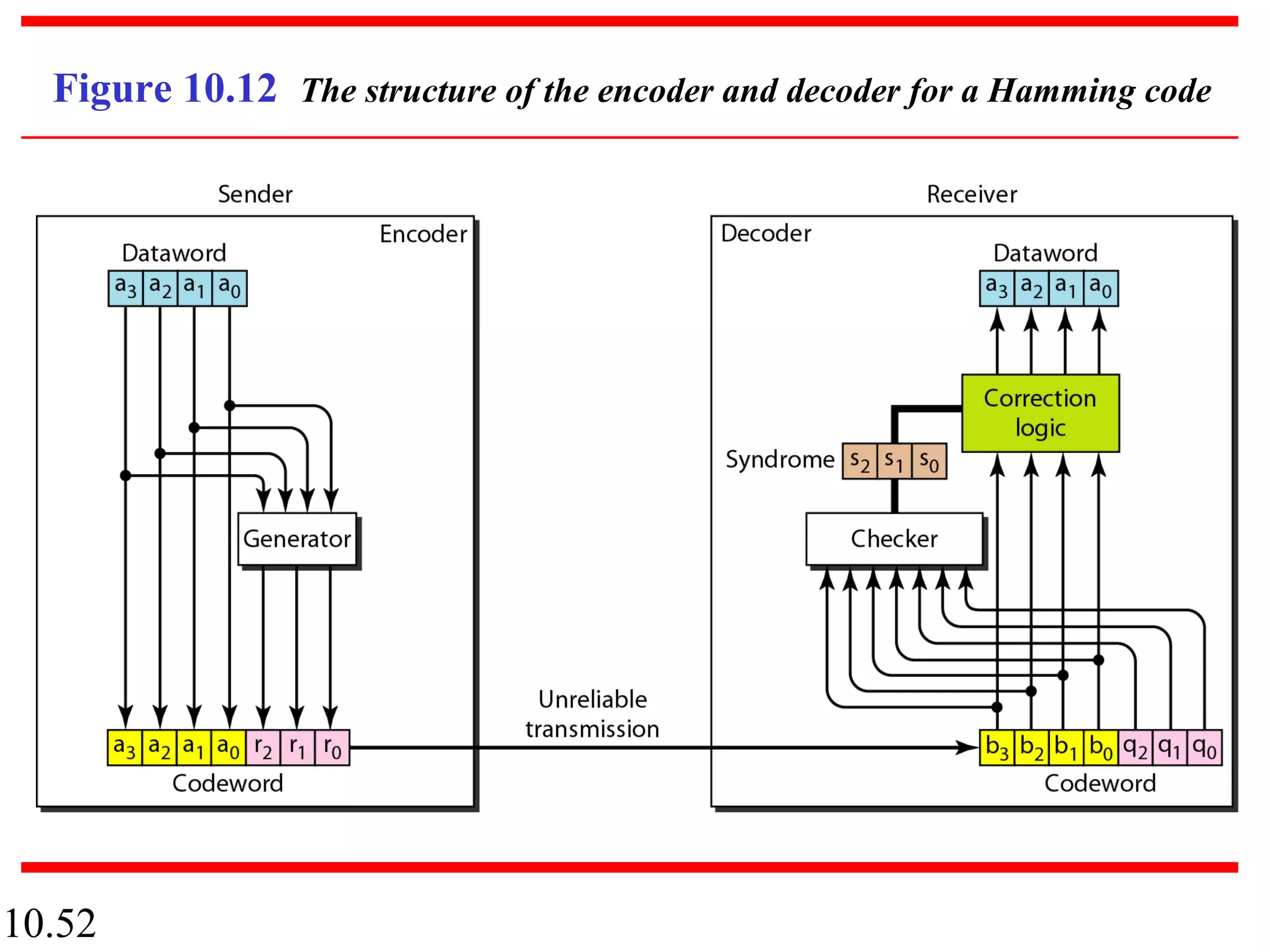
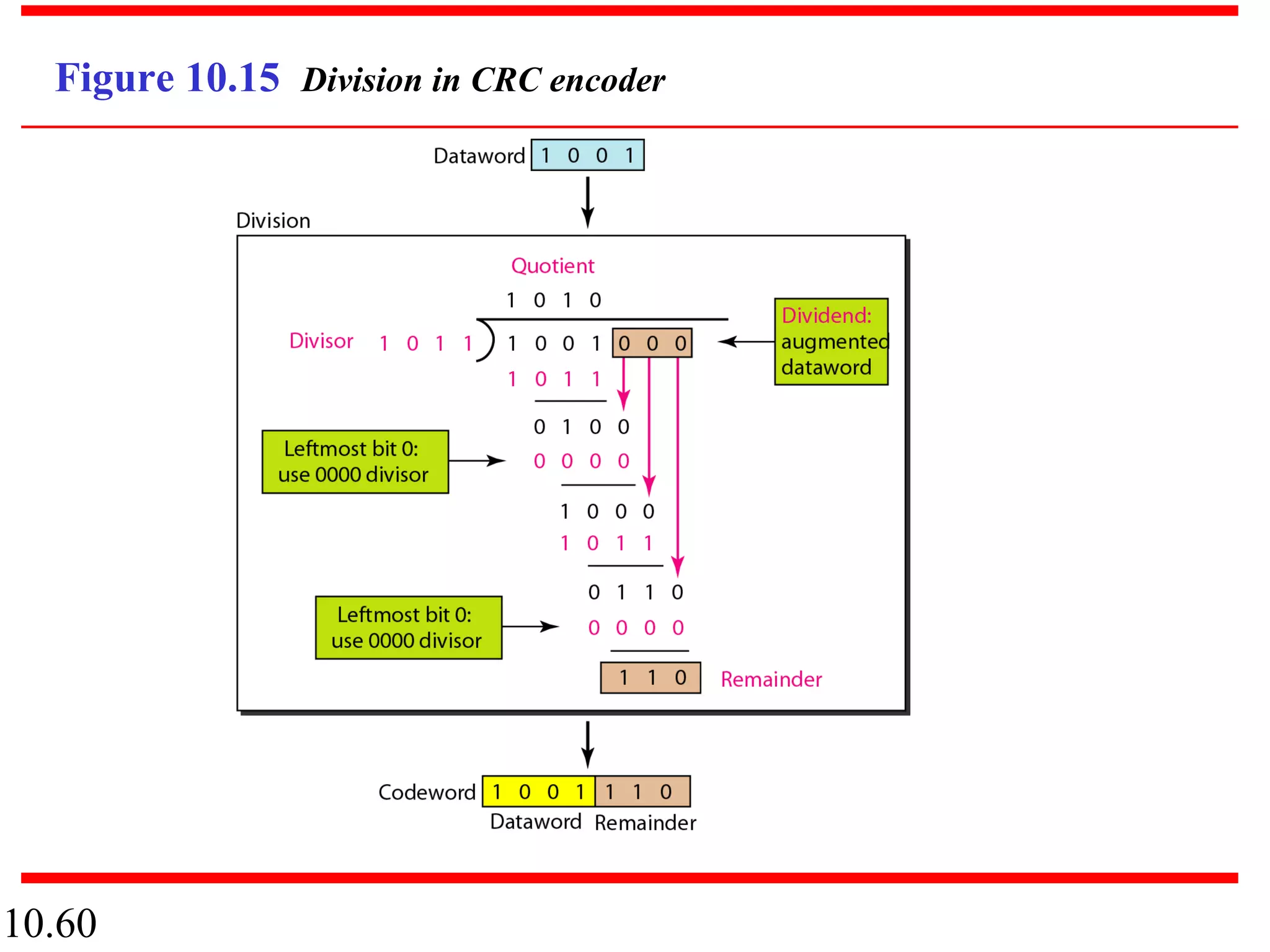
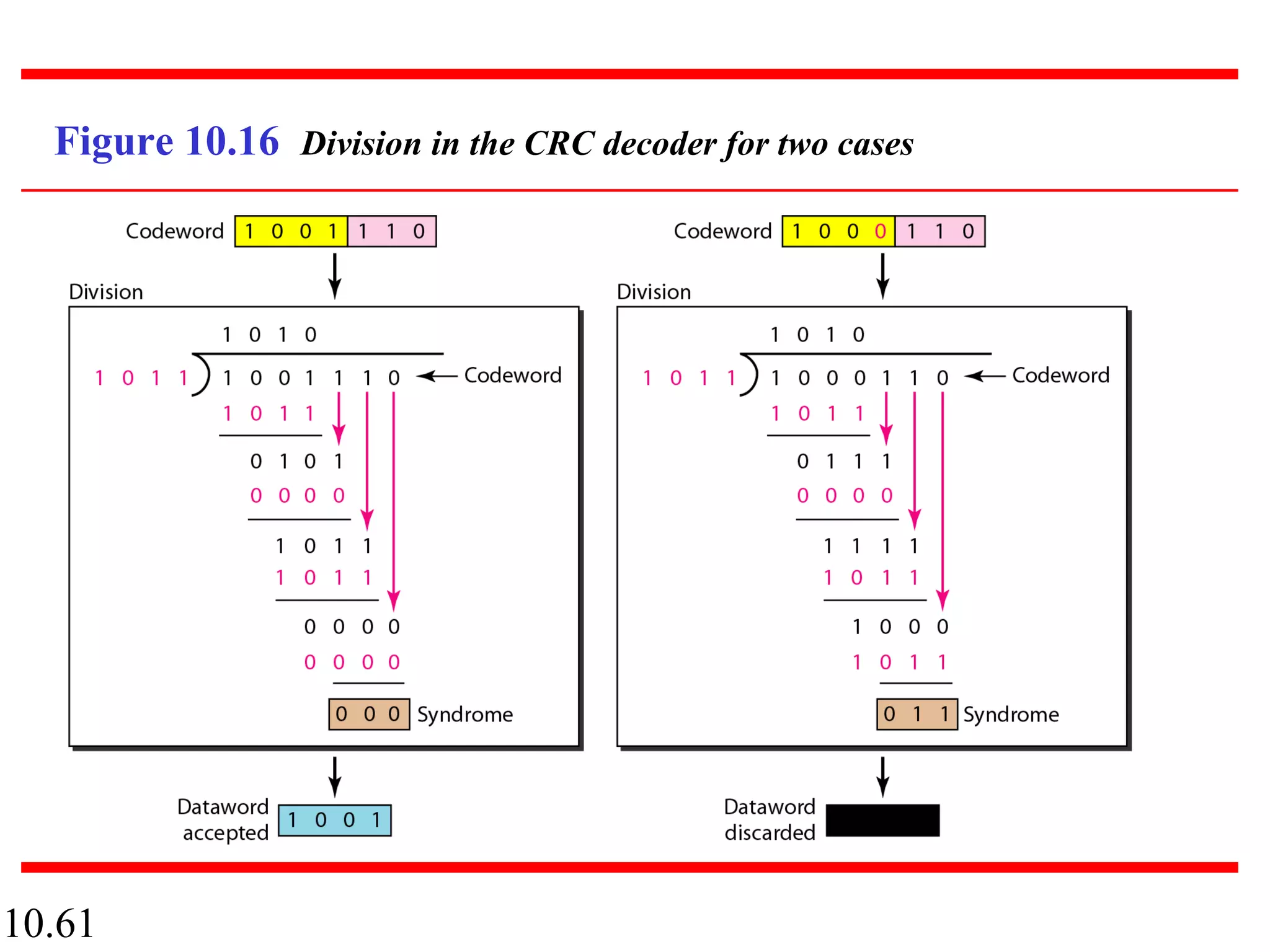
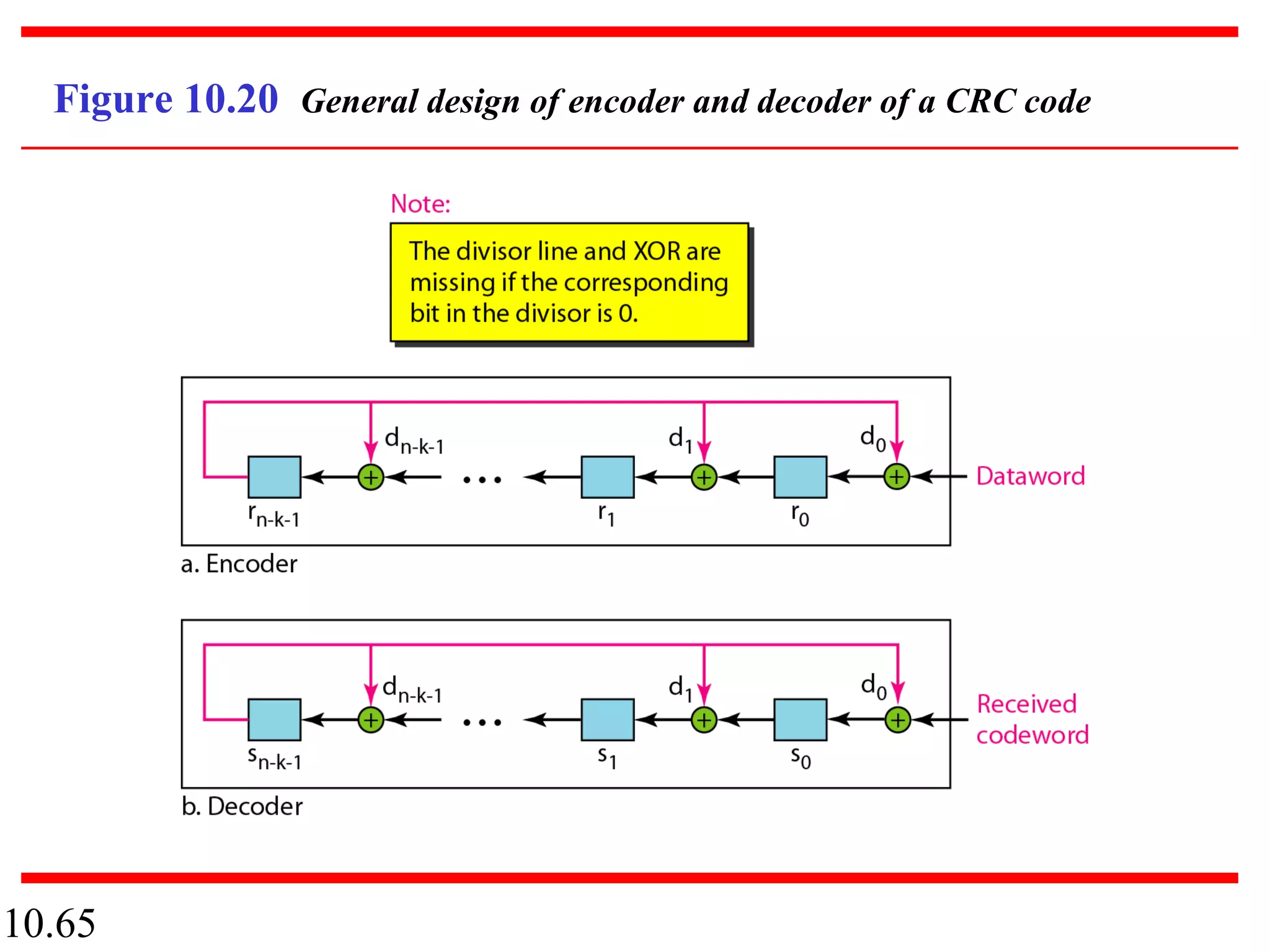
This document discusses error detection and correction in digital communications. It begins with an introduction to different types of errors that can occur like single-bit errors and burst errors. It explains that redundancy is needed to detect or correct errors. It then discusses various block coding techniques used for error detection and correction including linear block codes, cyclic codes, and cyclic redundancy checks. Specific error correcting codes like Hamming codes and parity checks are explained through examples. The key aspects of error detection capability, minimum Hamming distance, and generator polynomials in cyclic codes are covered.