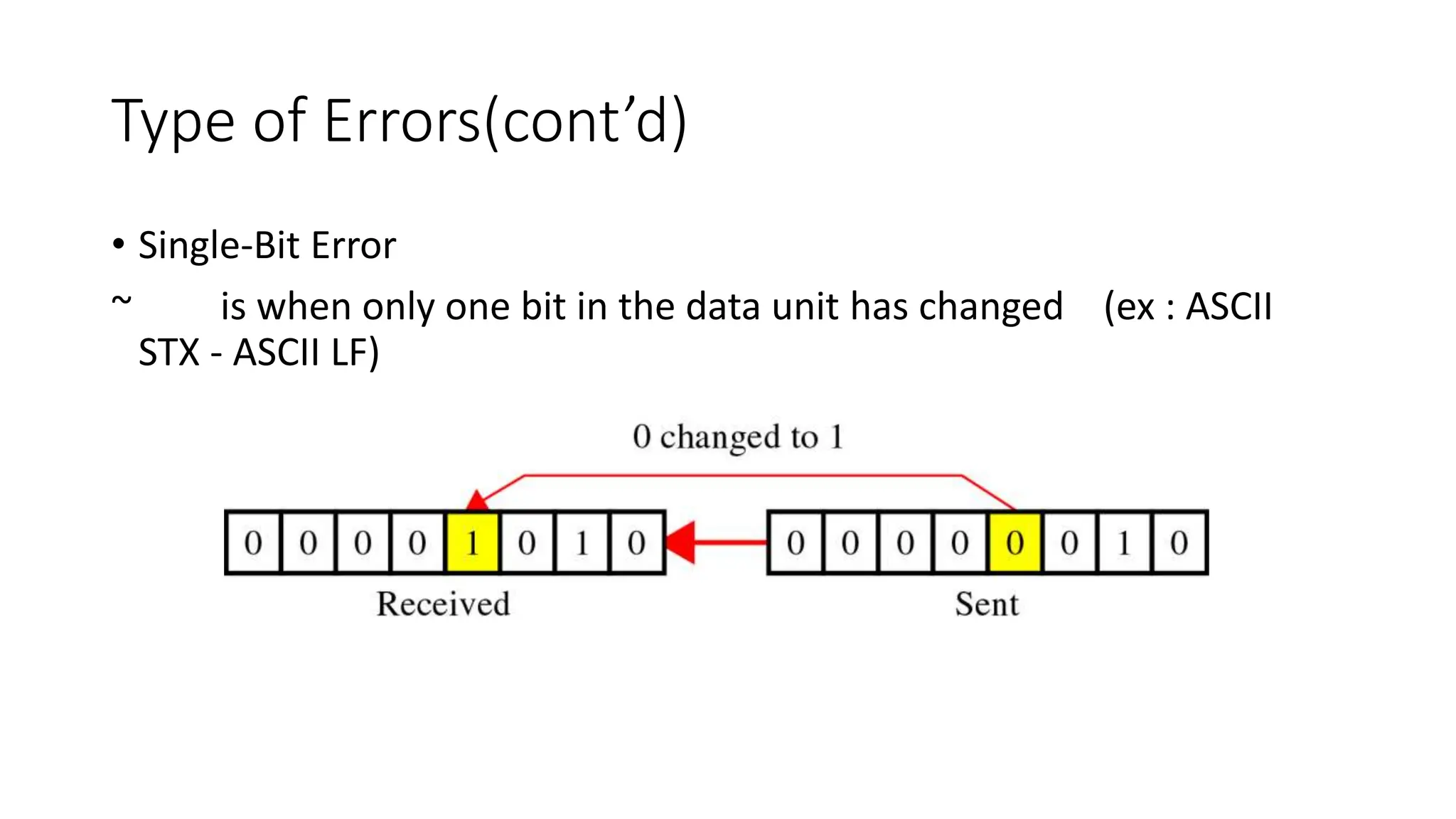
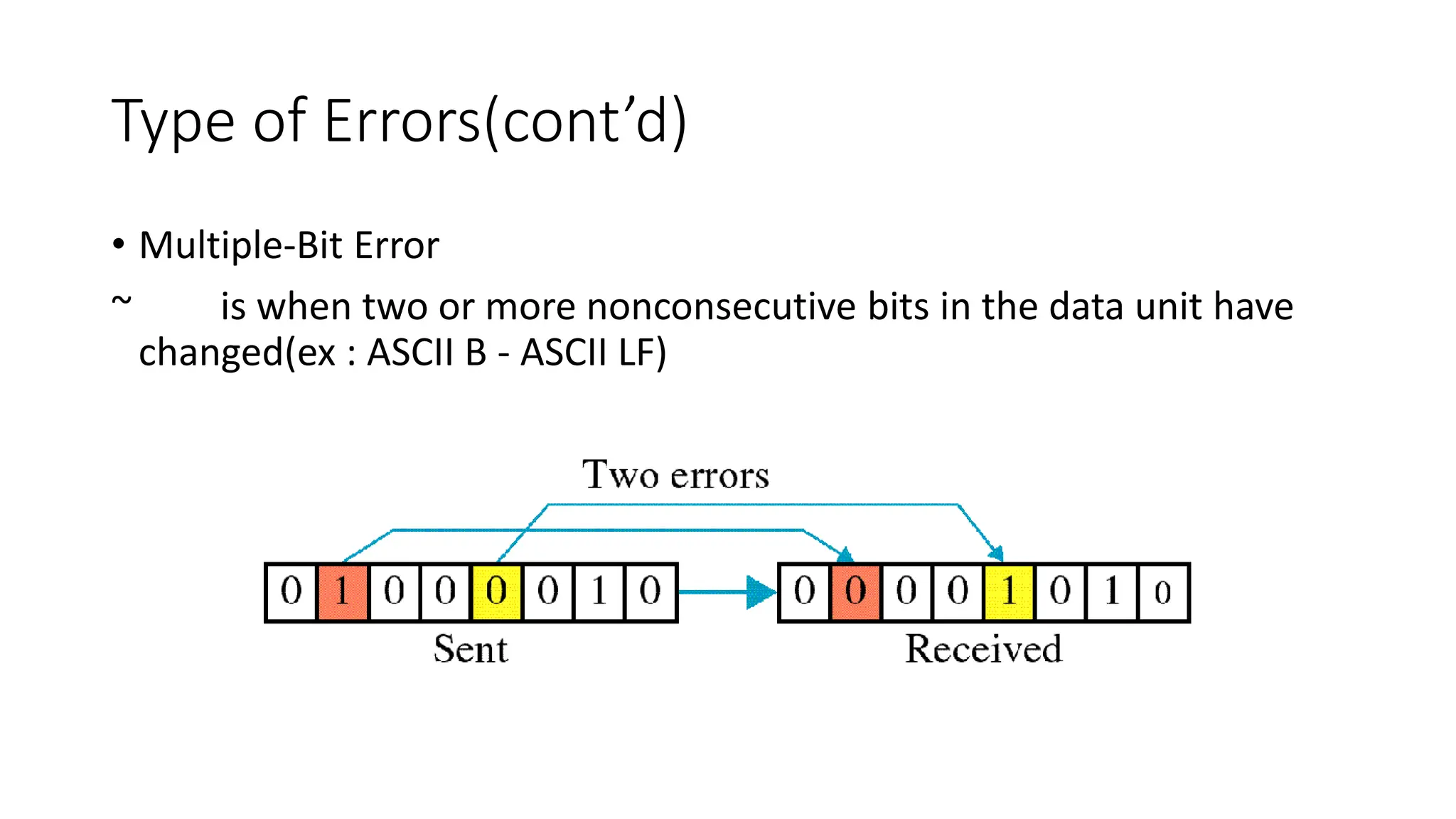
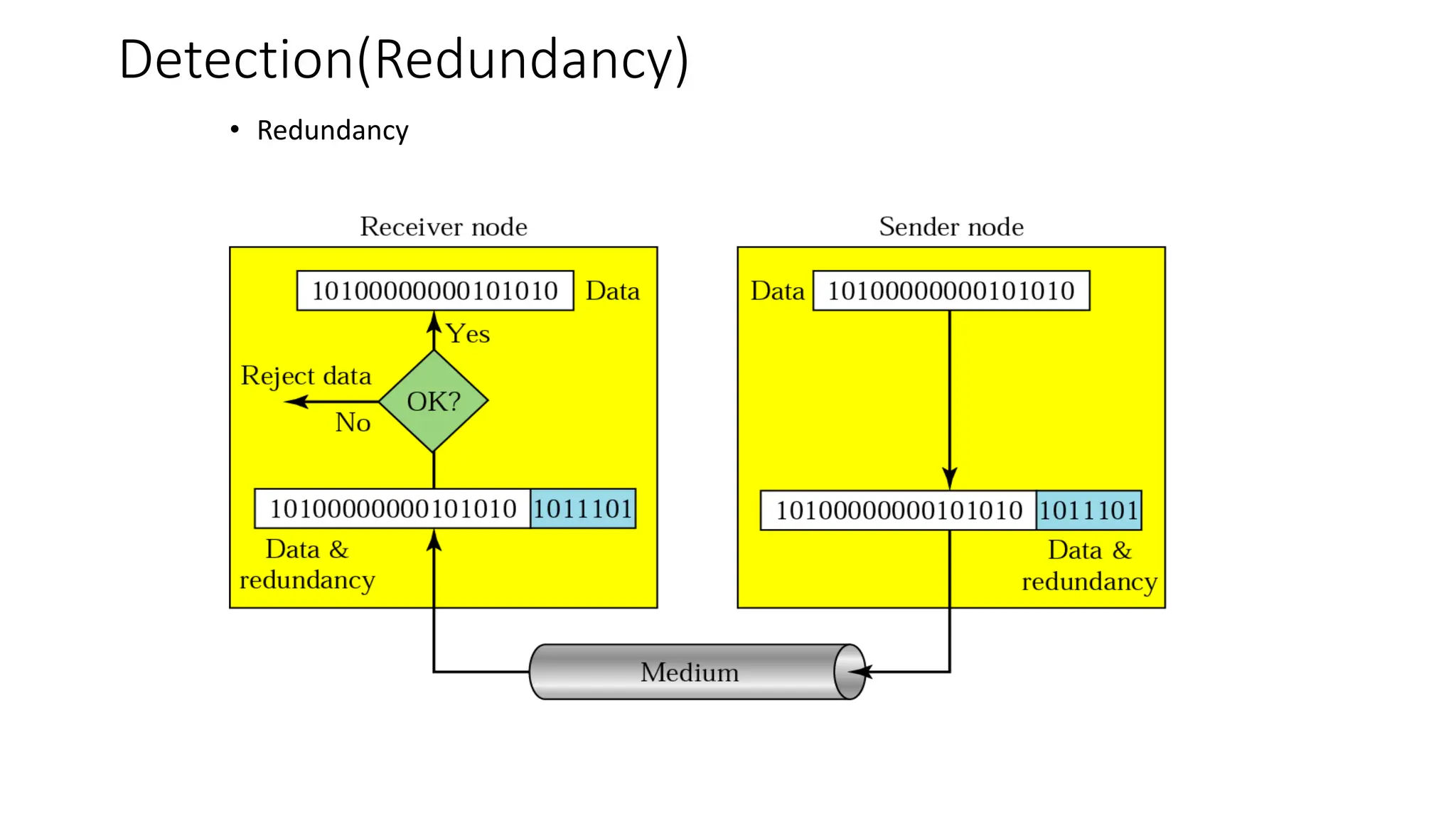
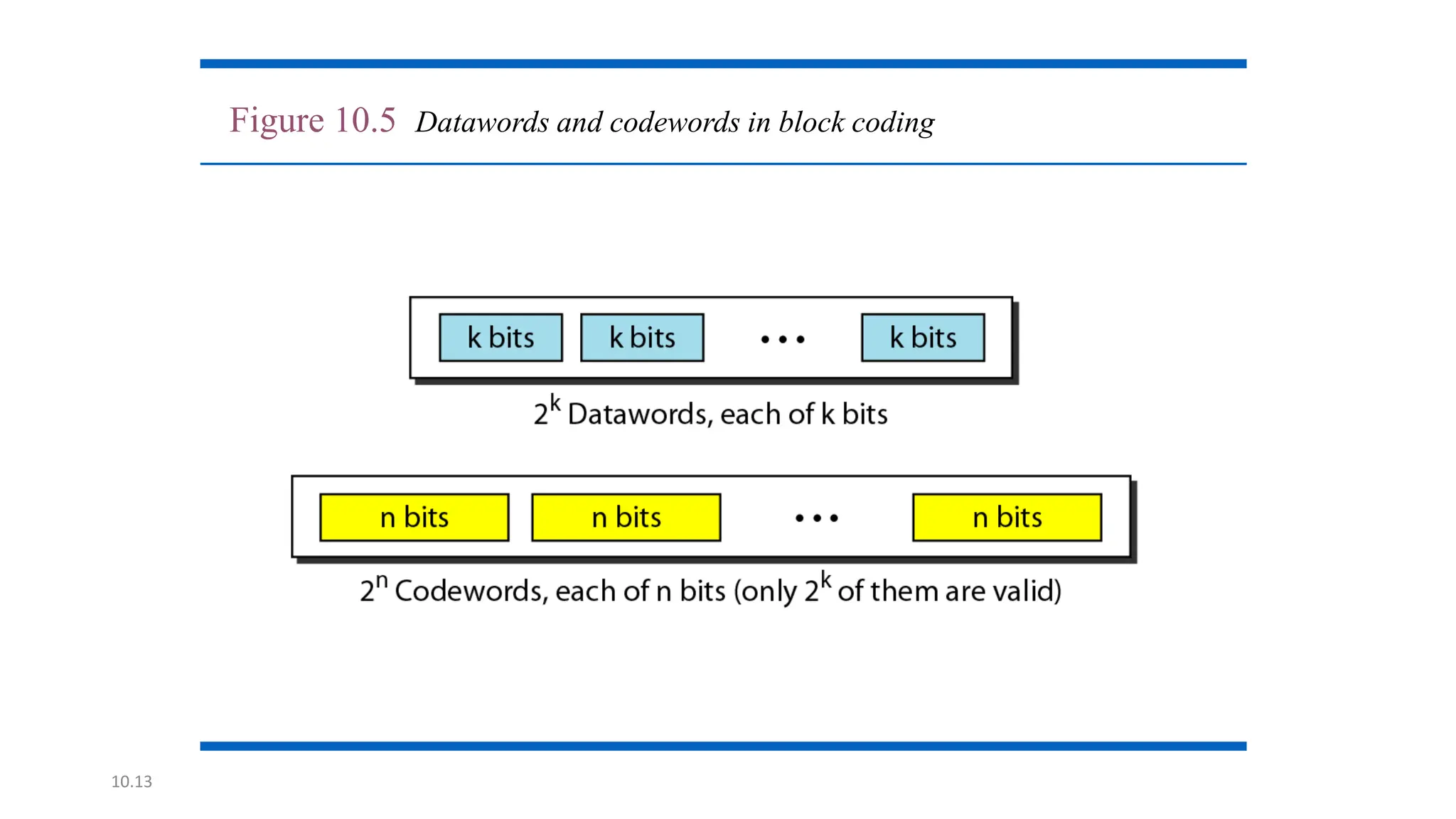
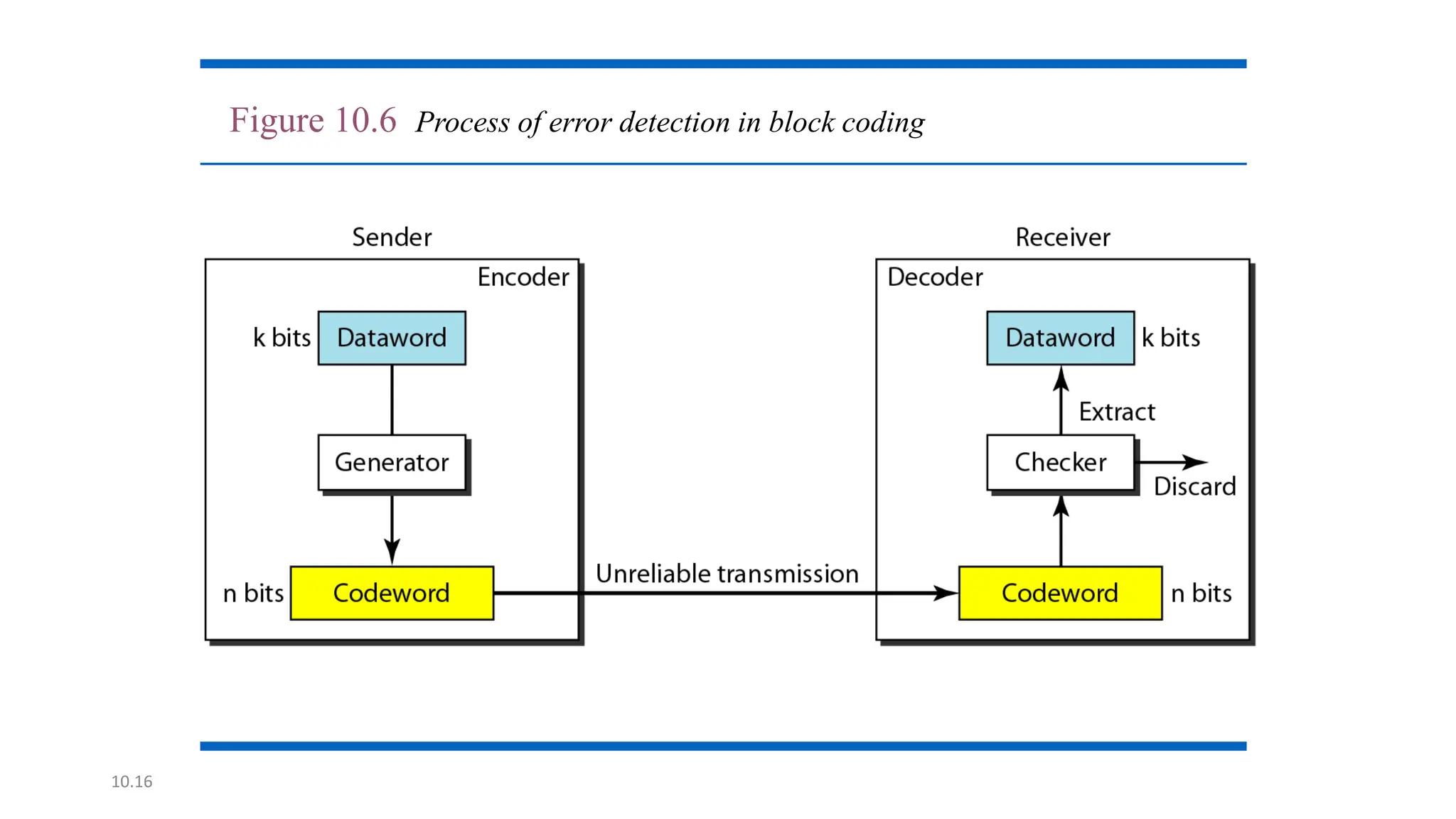
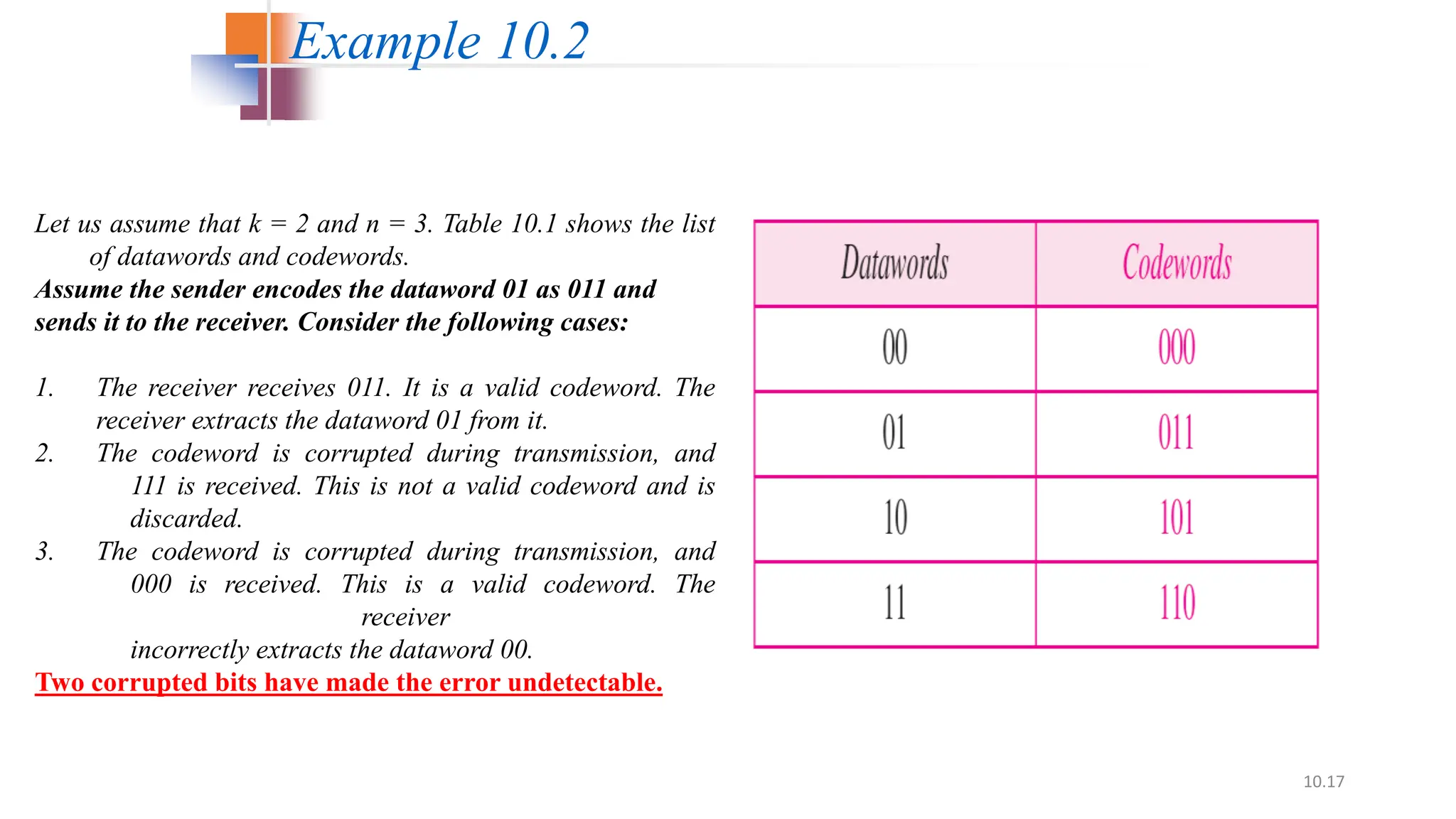
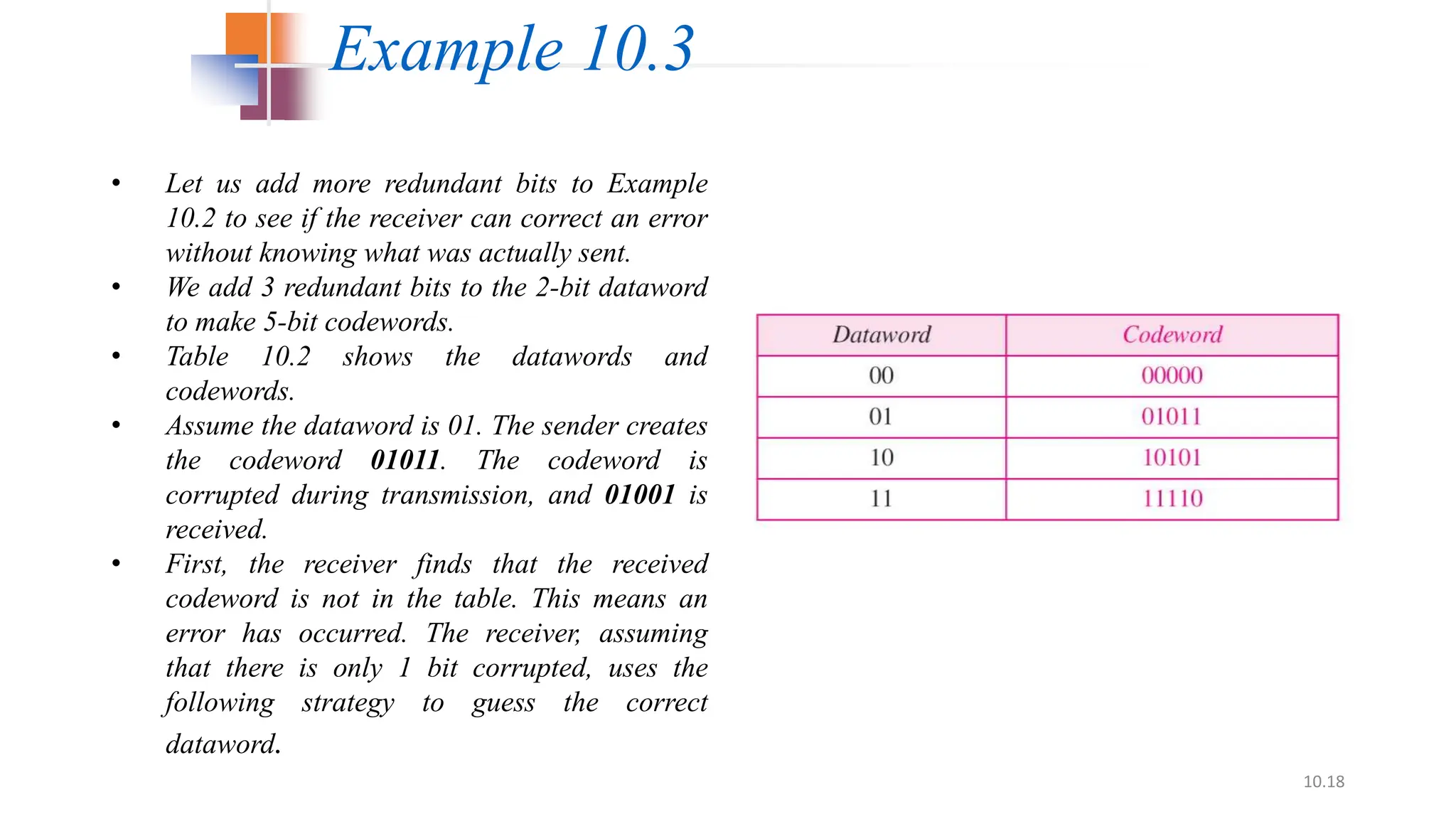
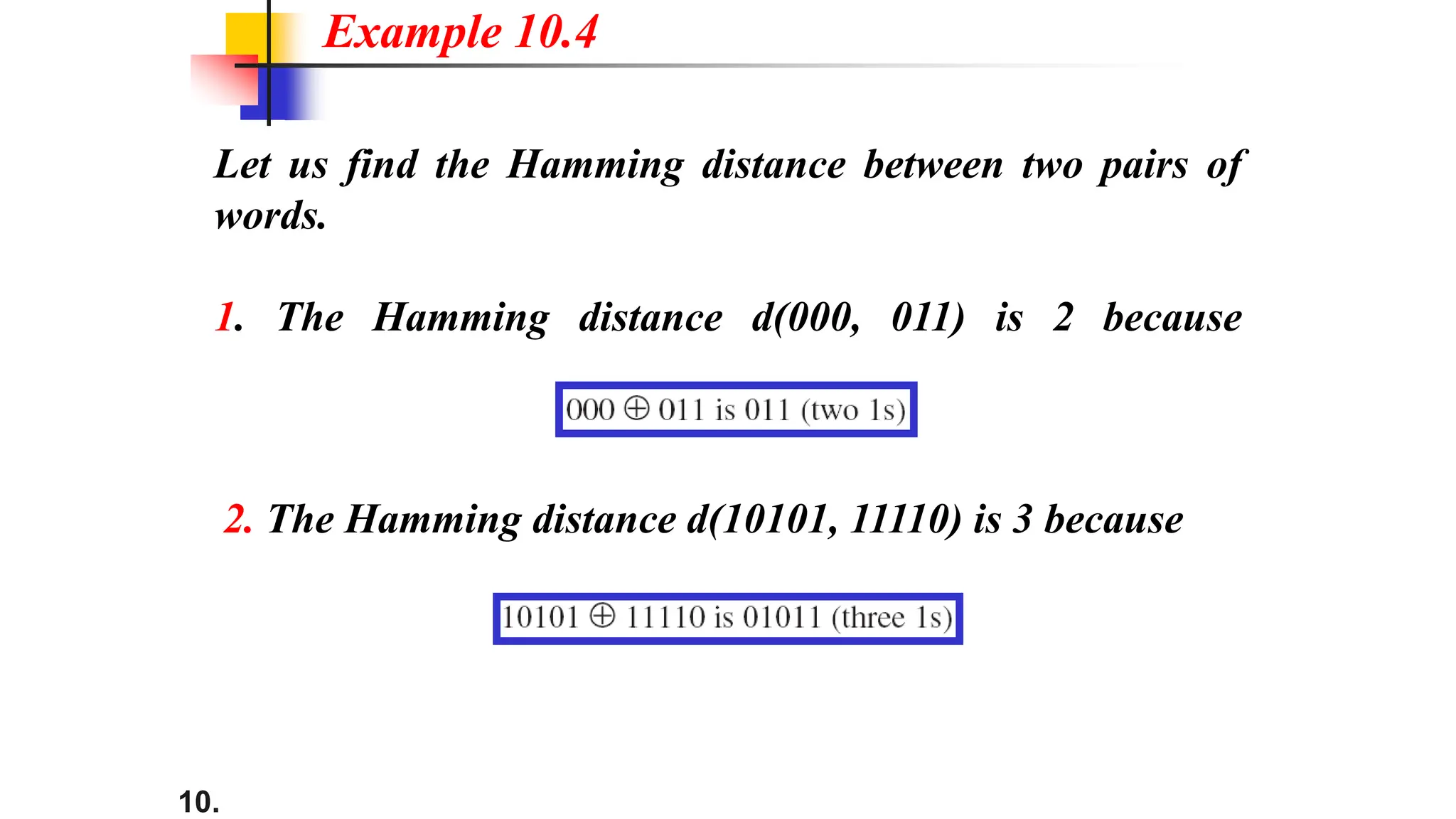
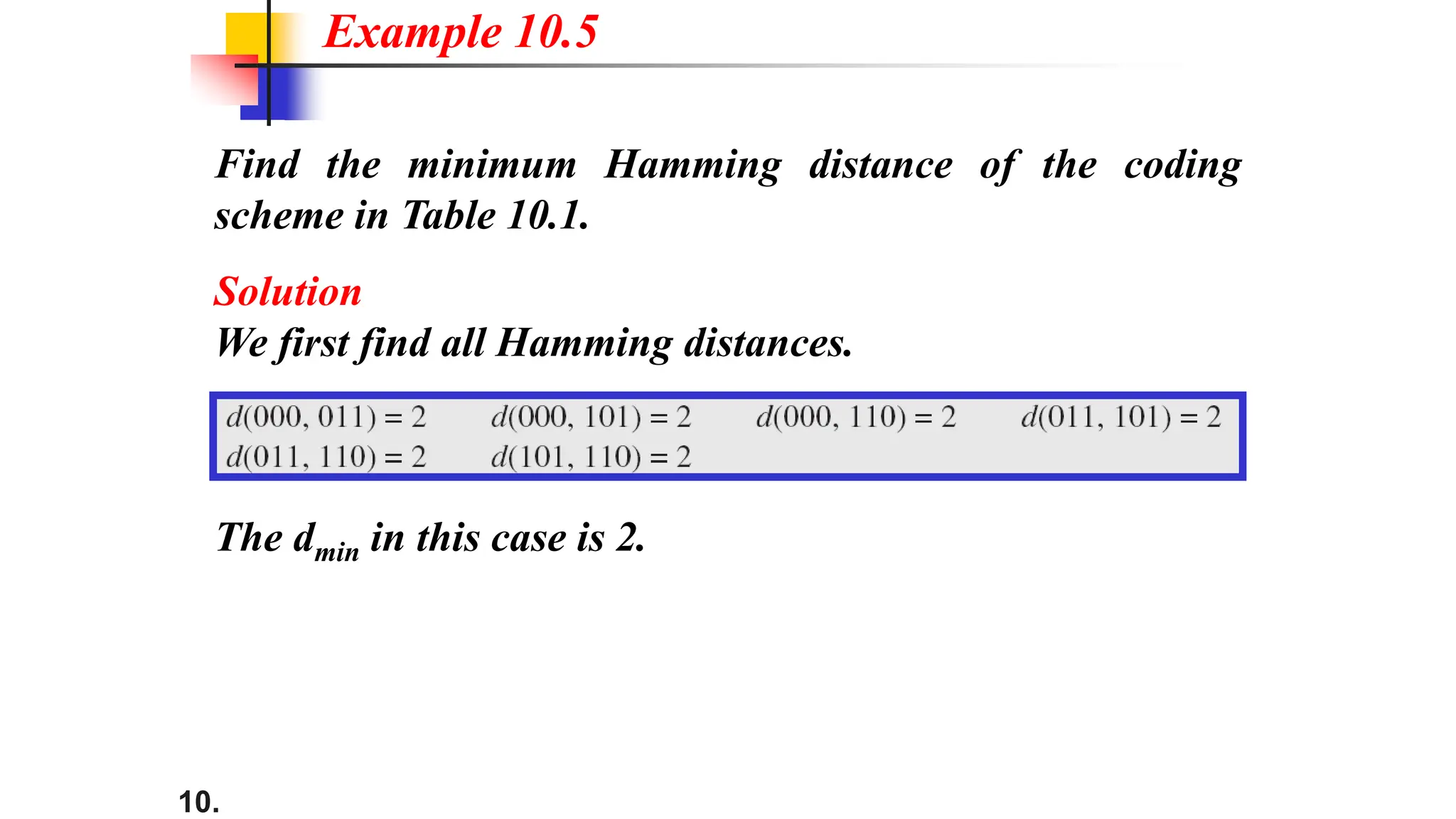
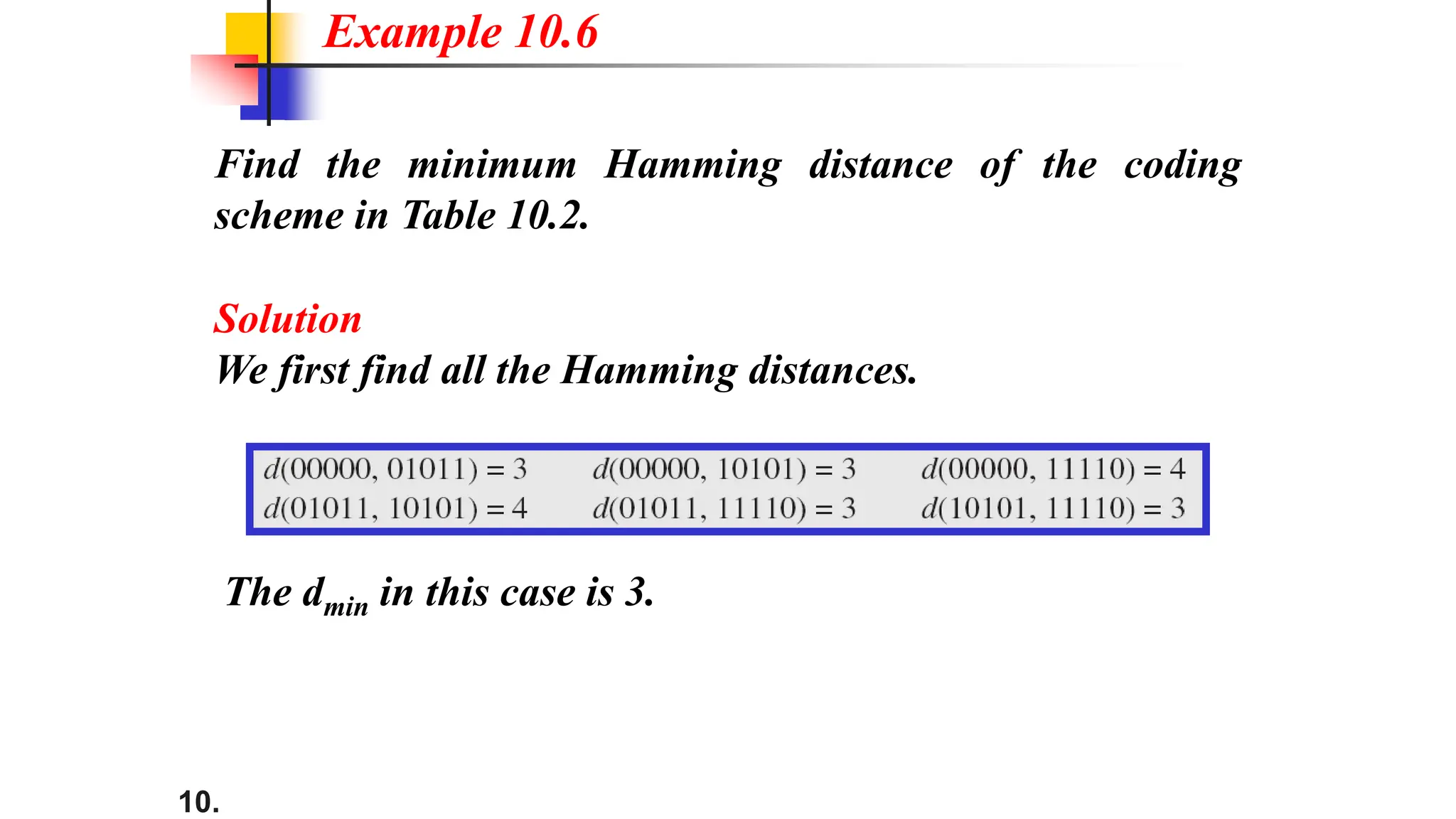
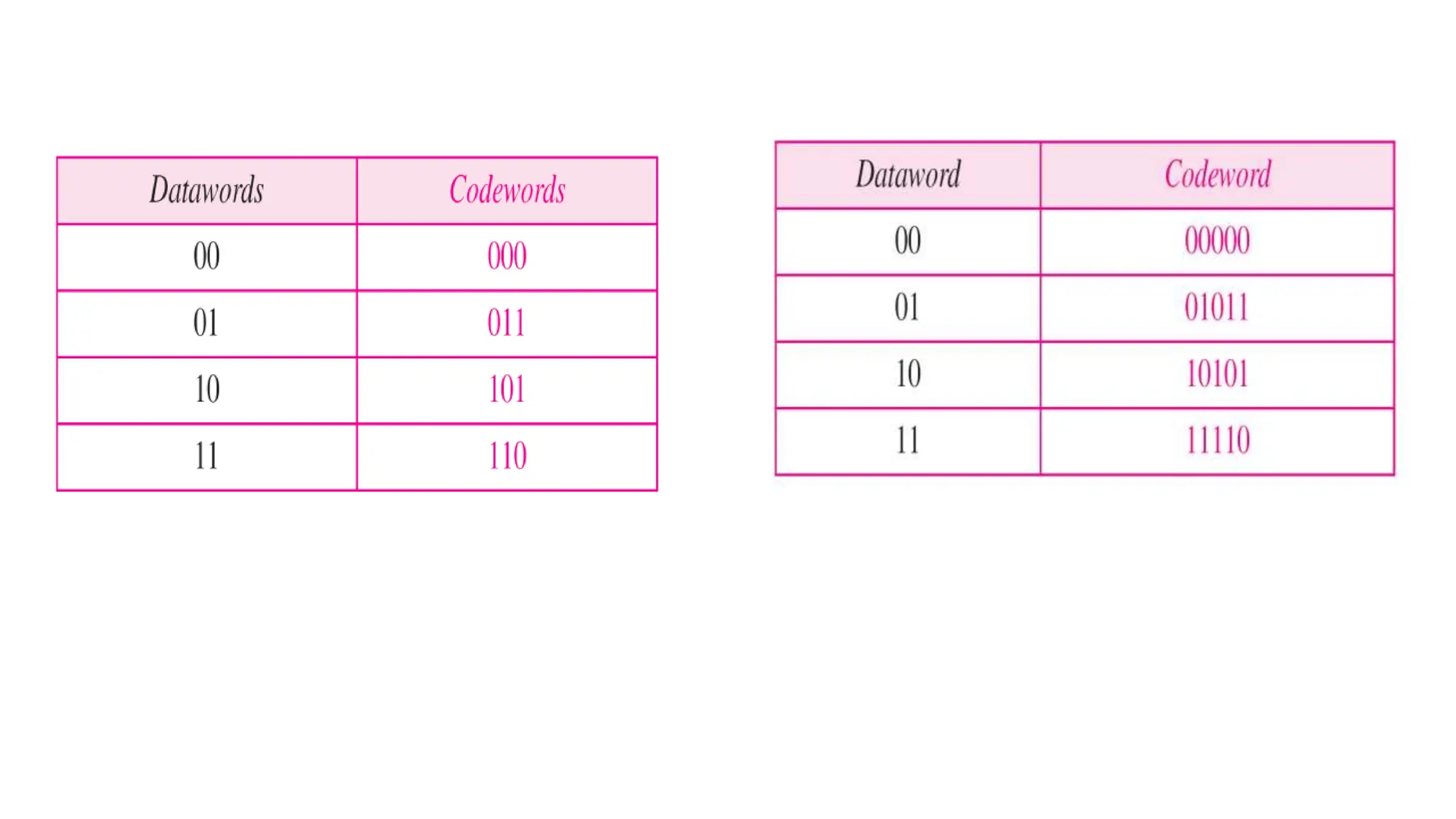
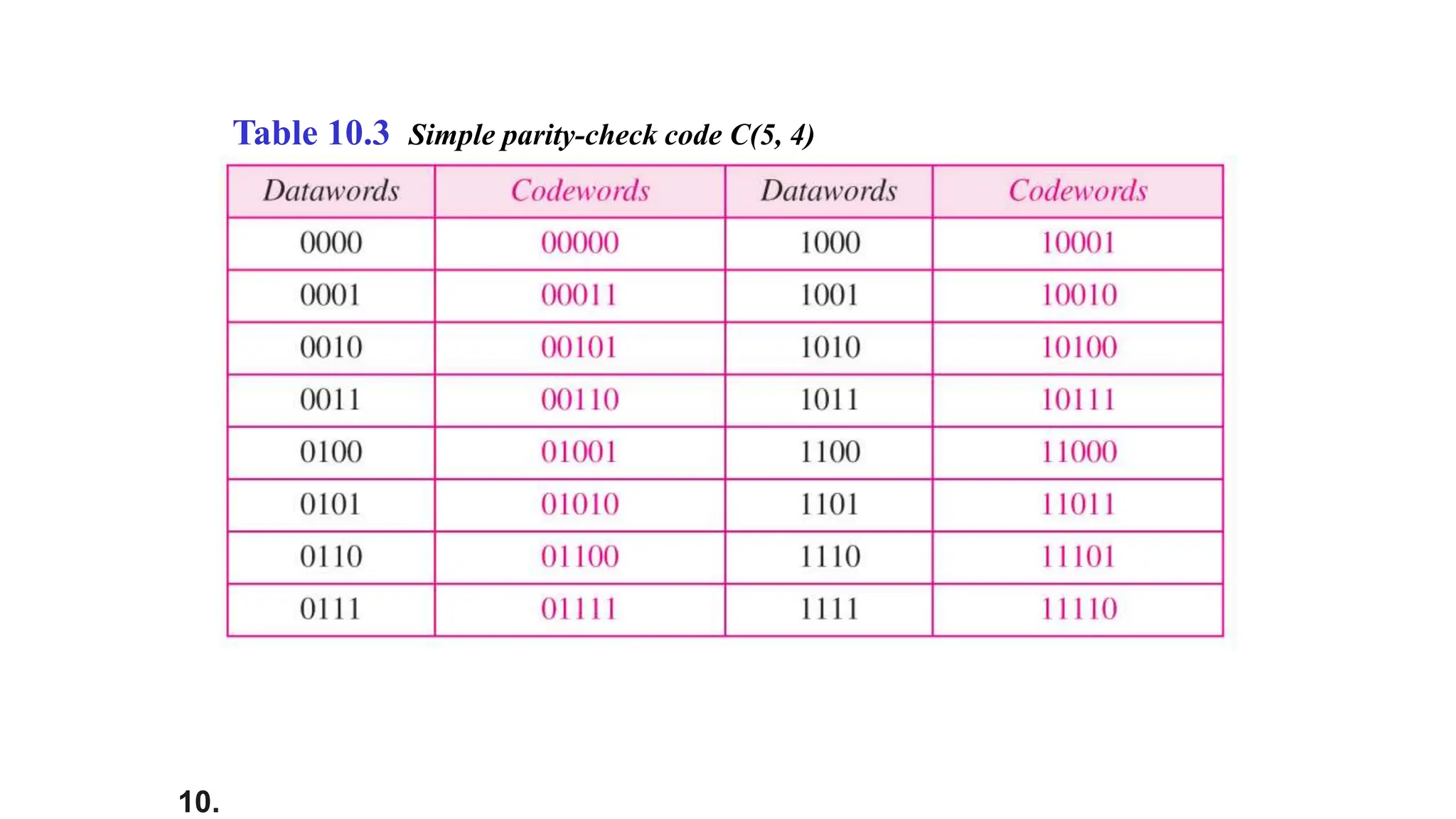
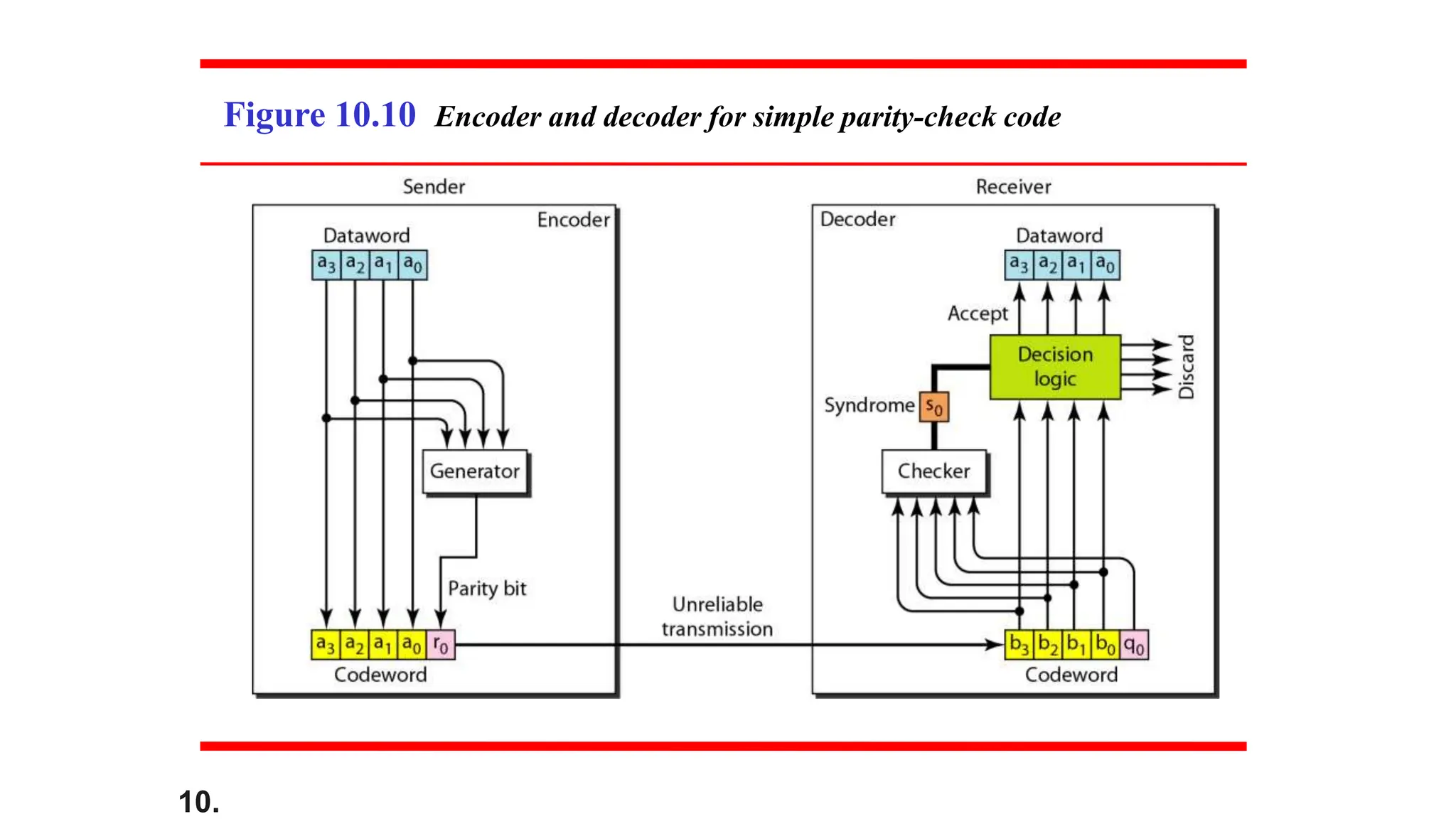
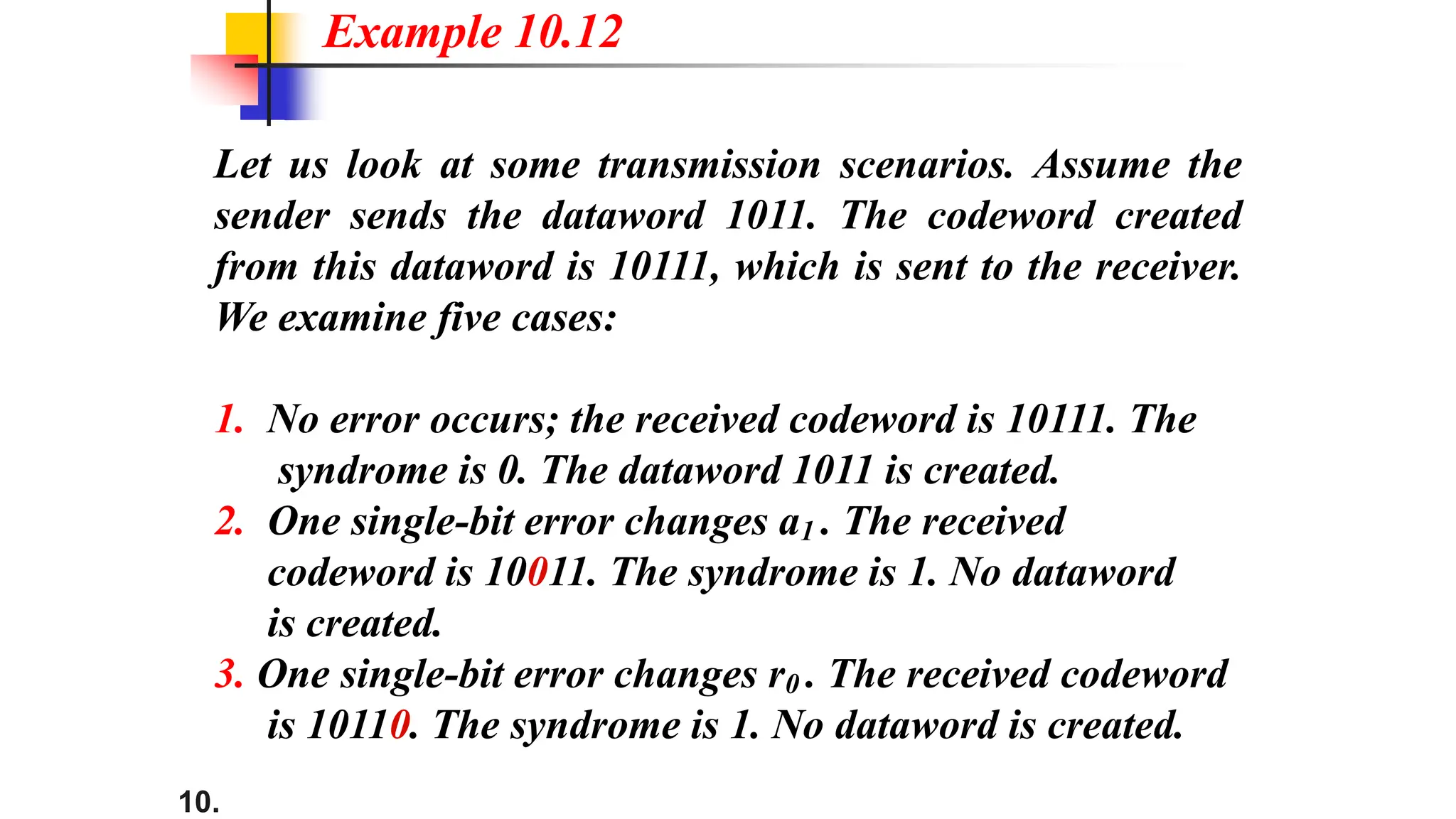
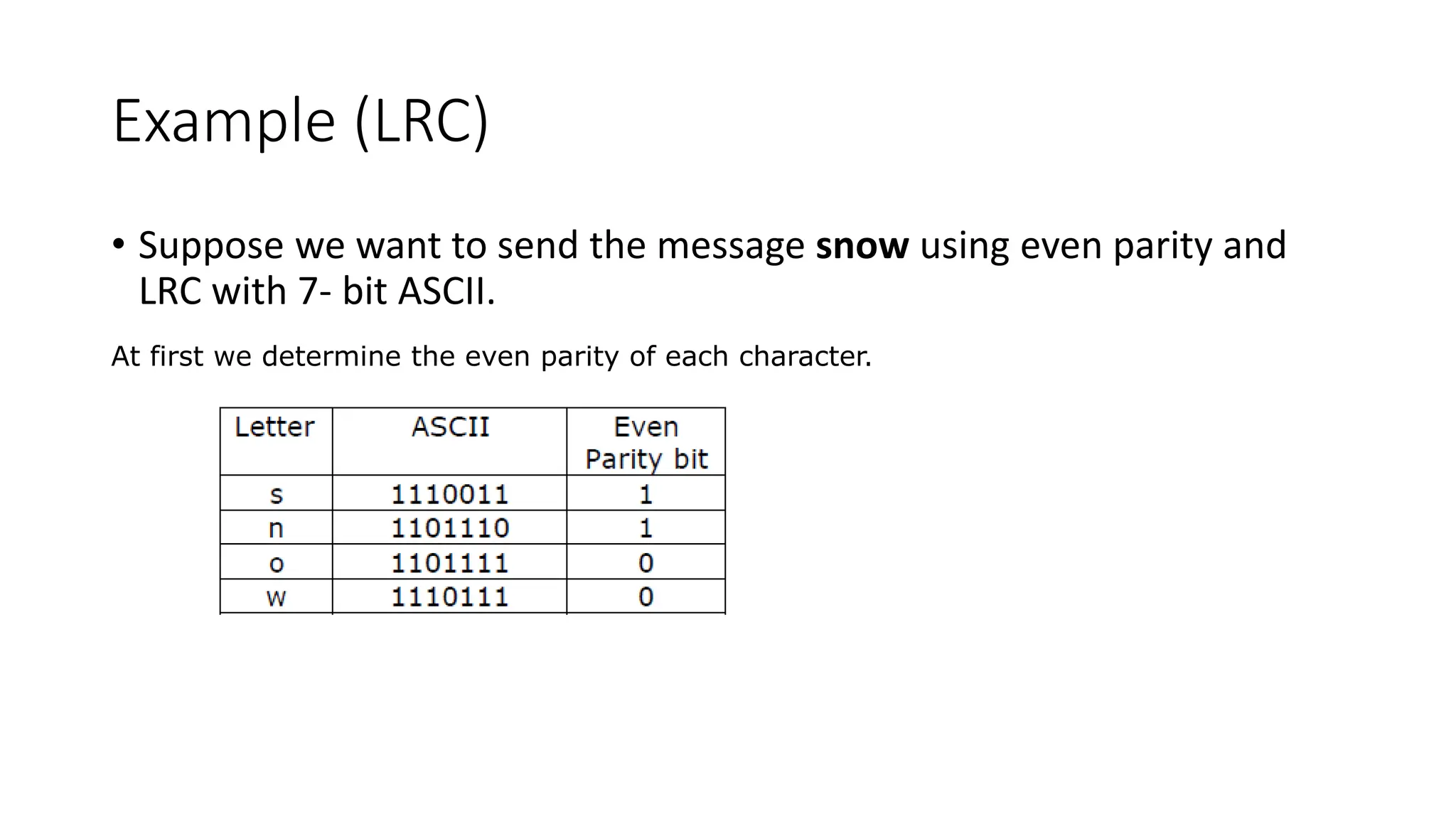
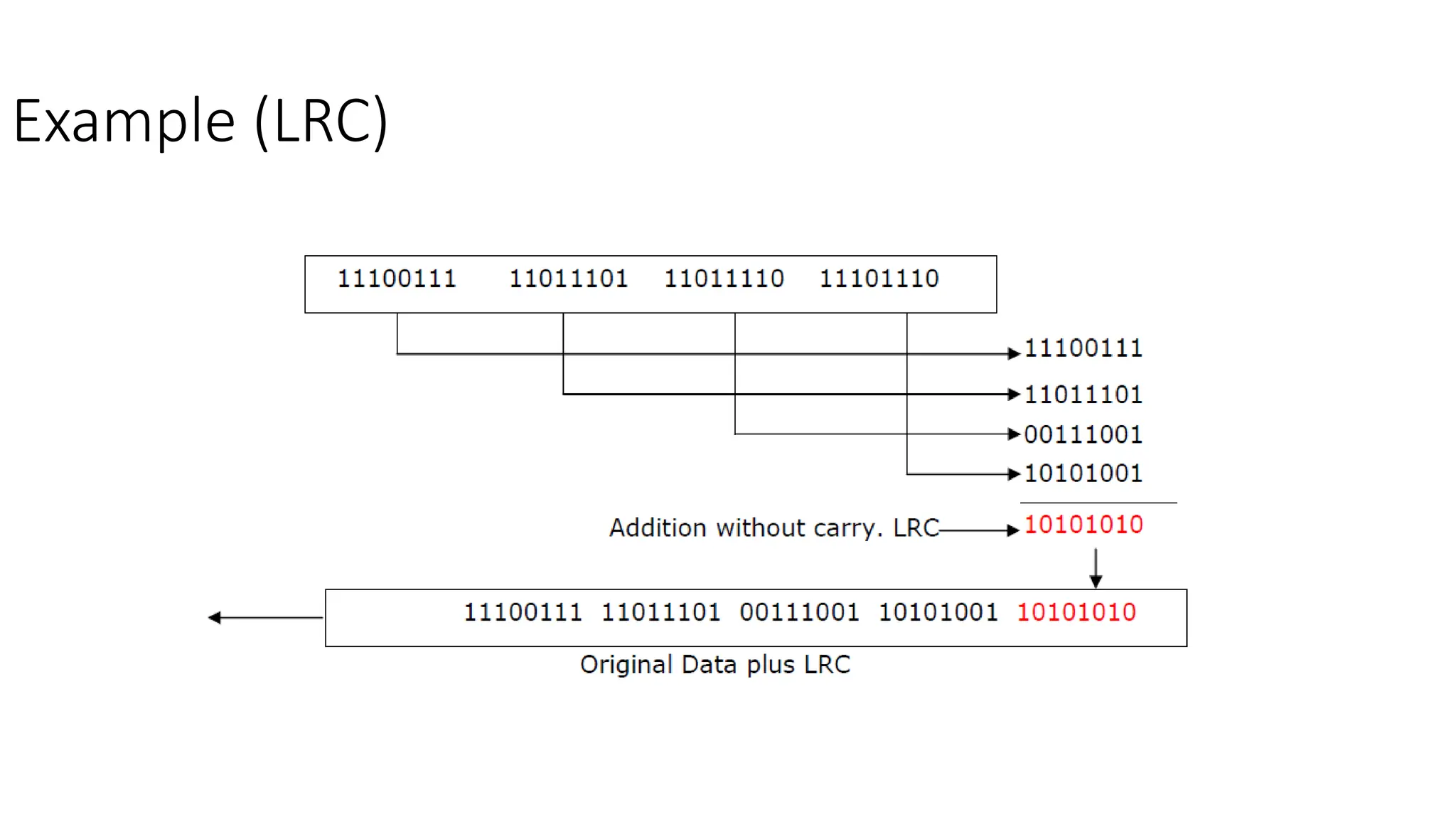
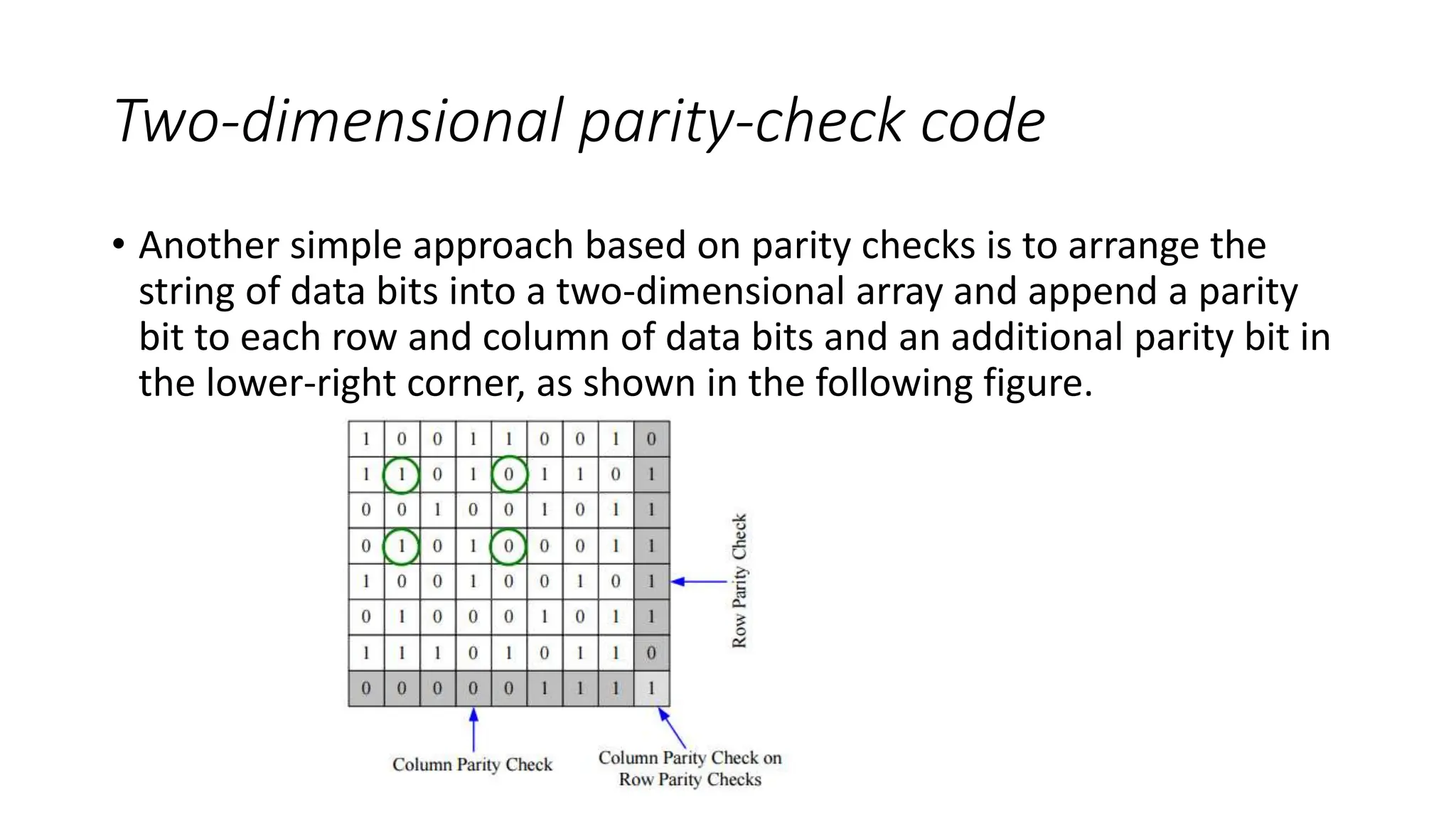
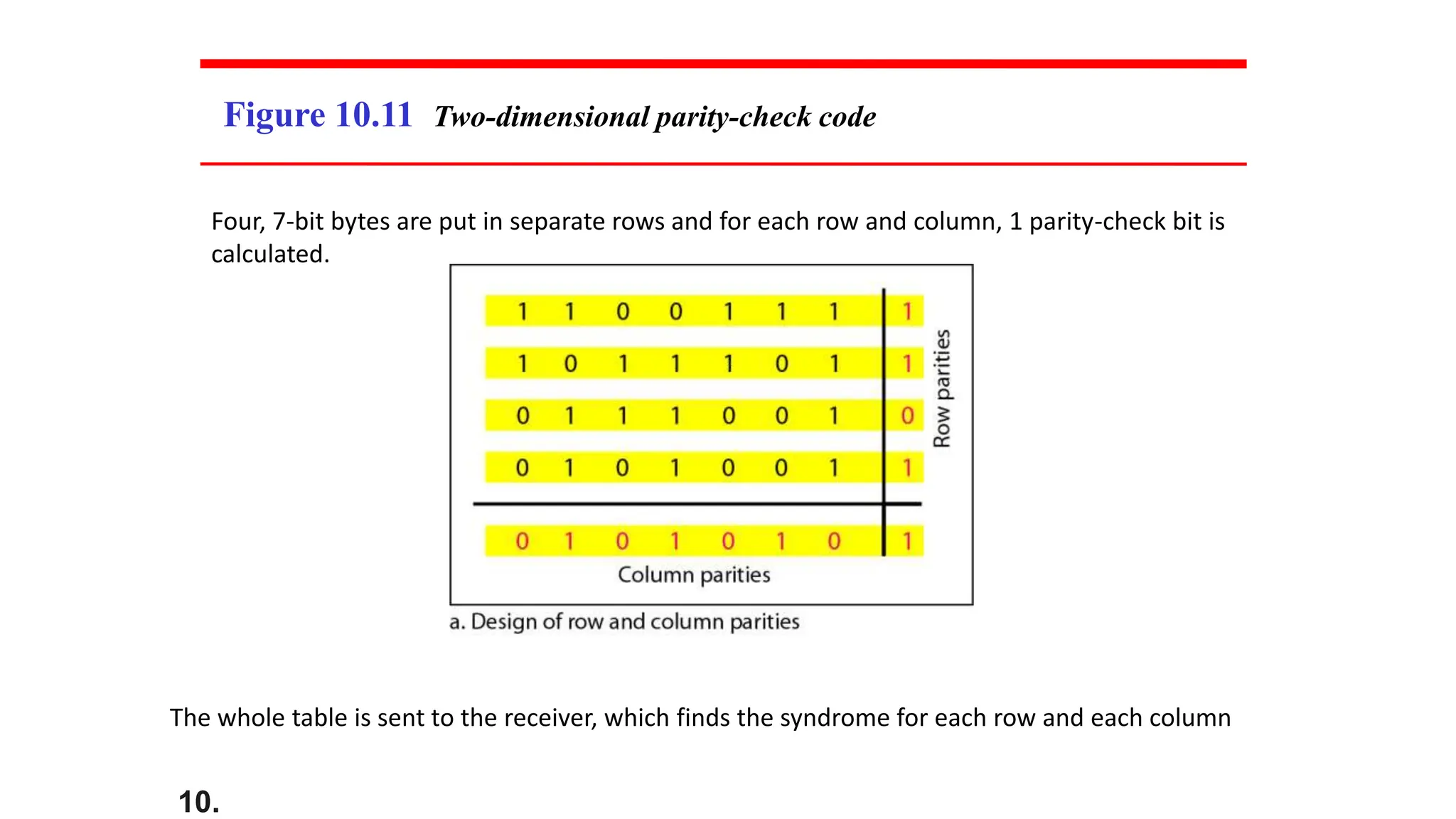
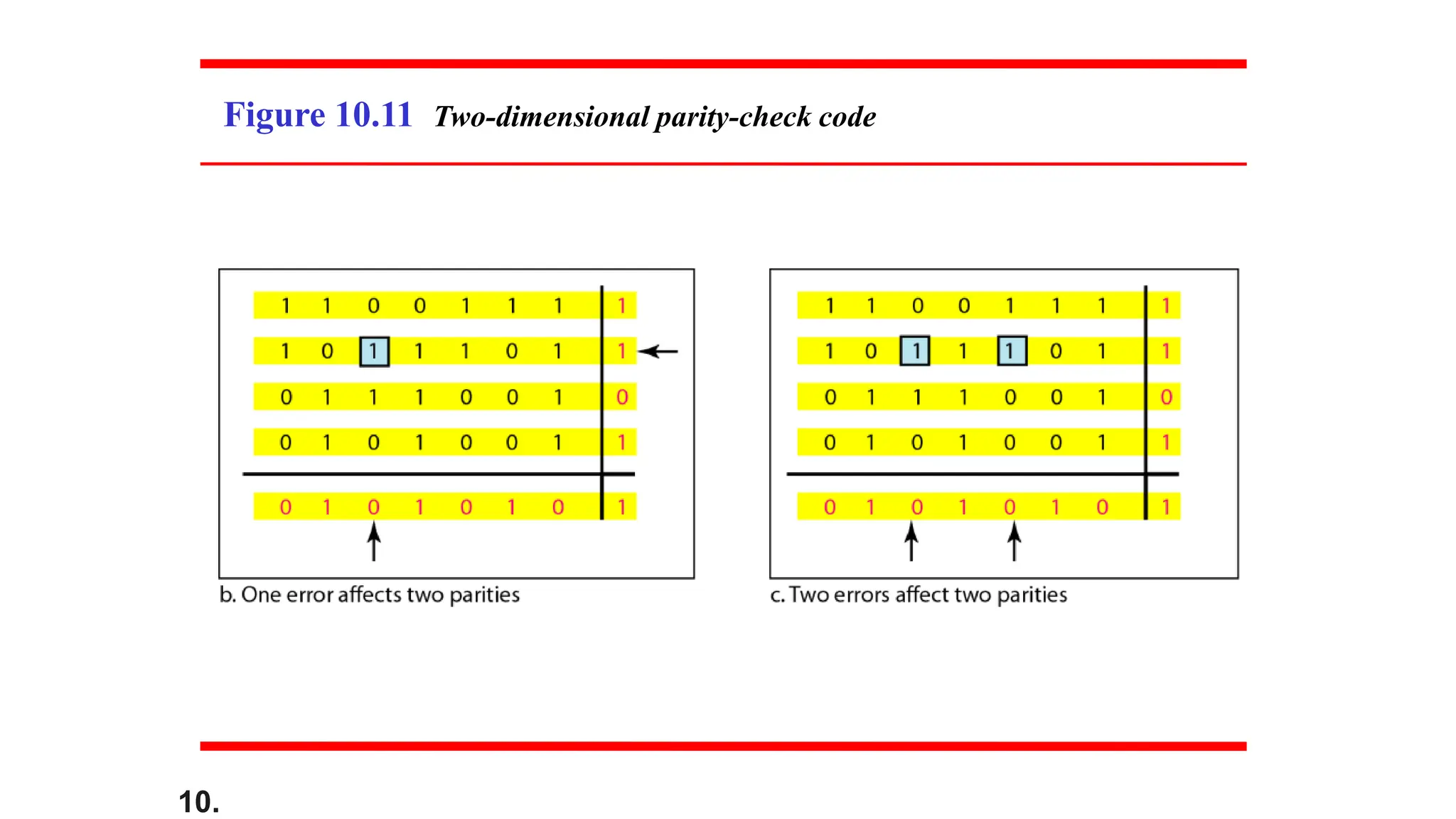
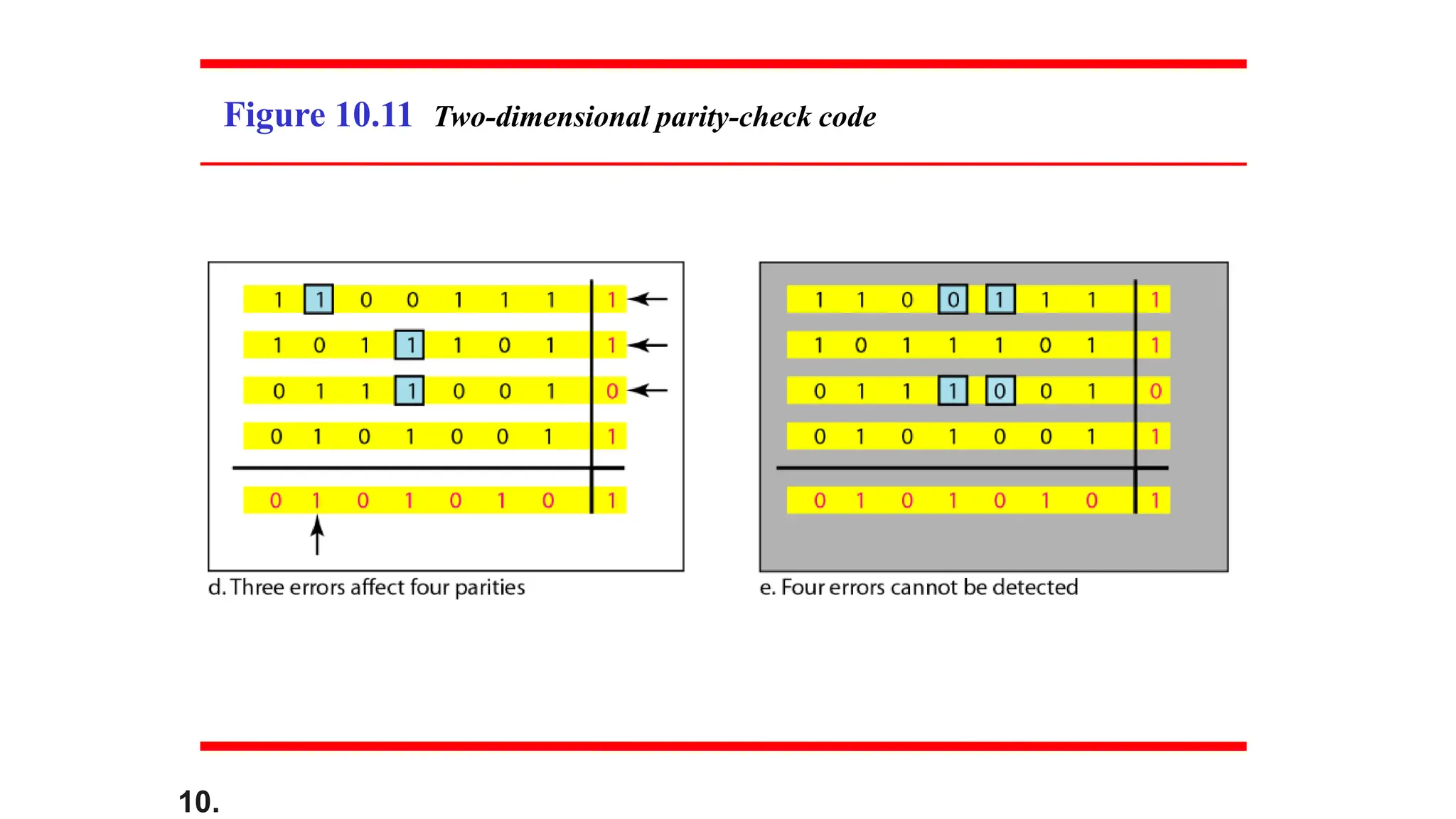
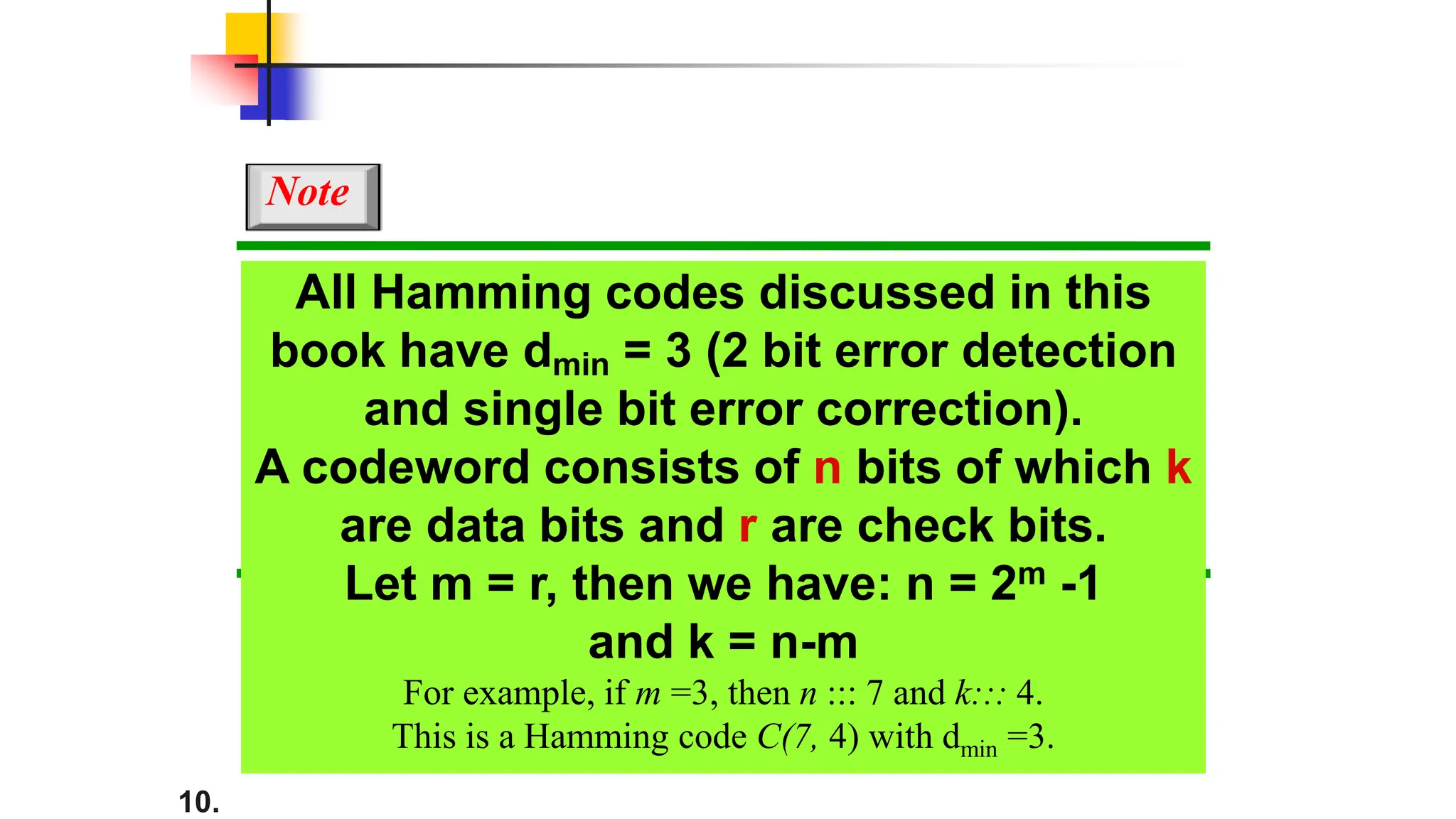
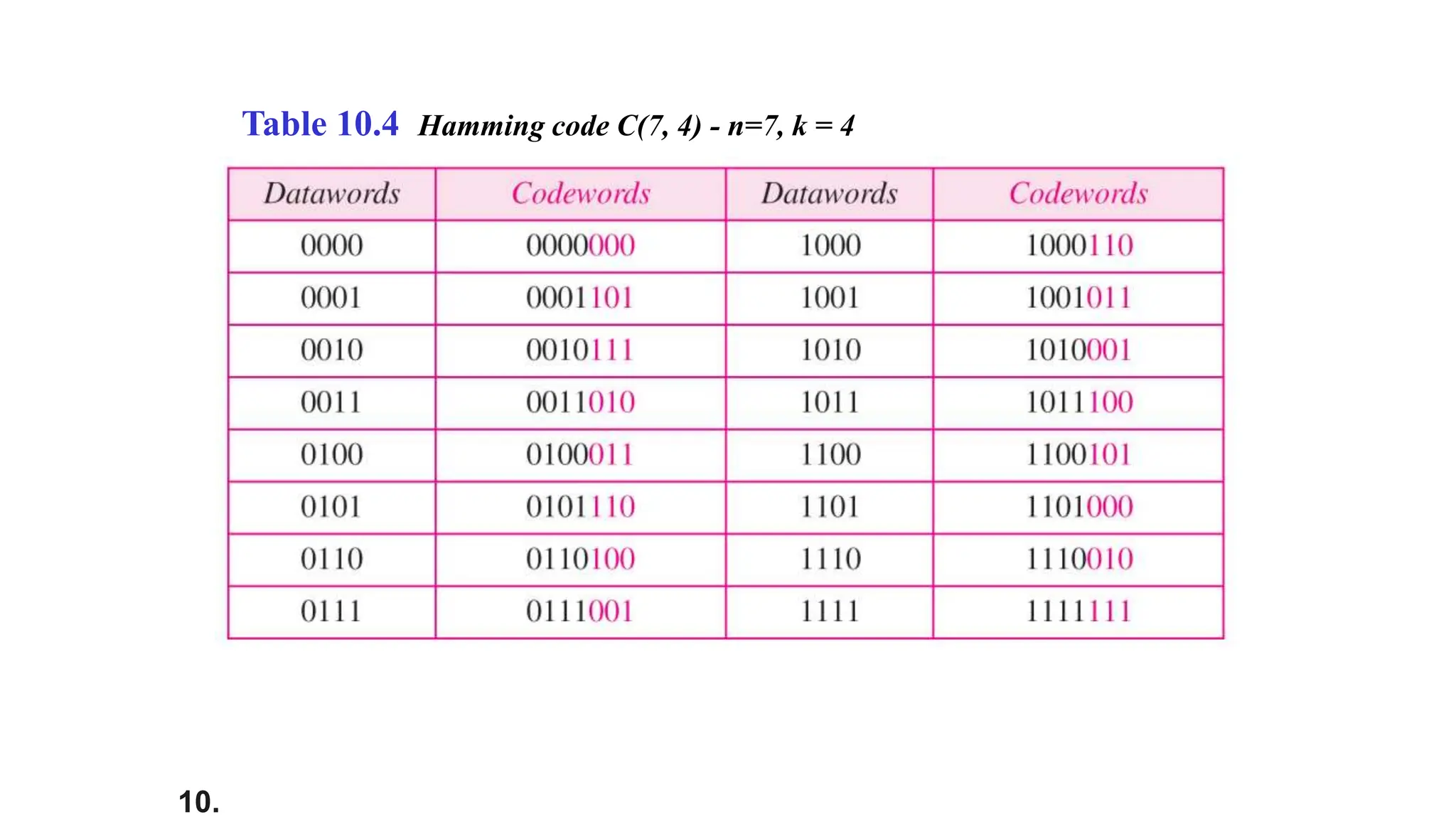
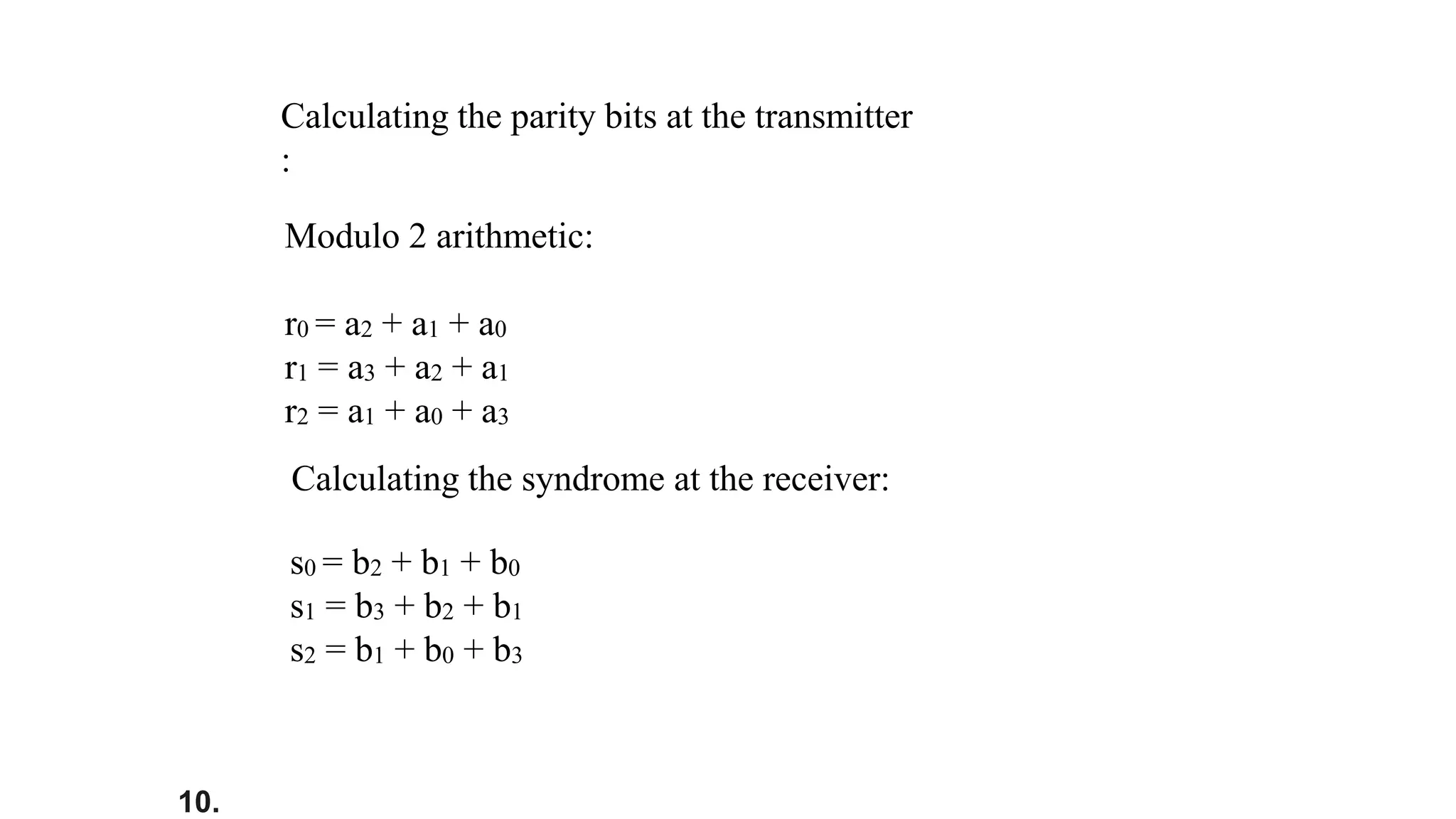
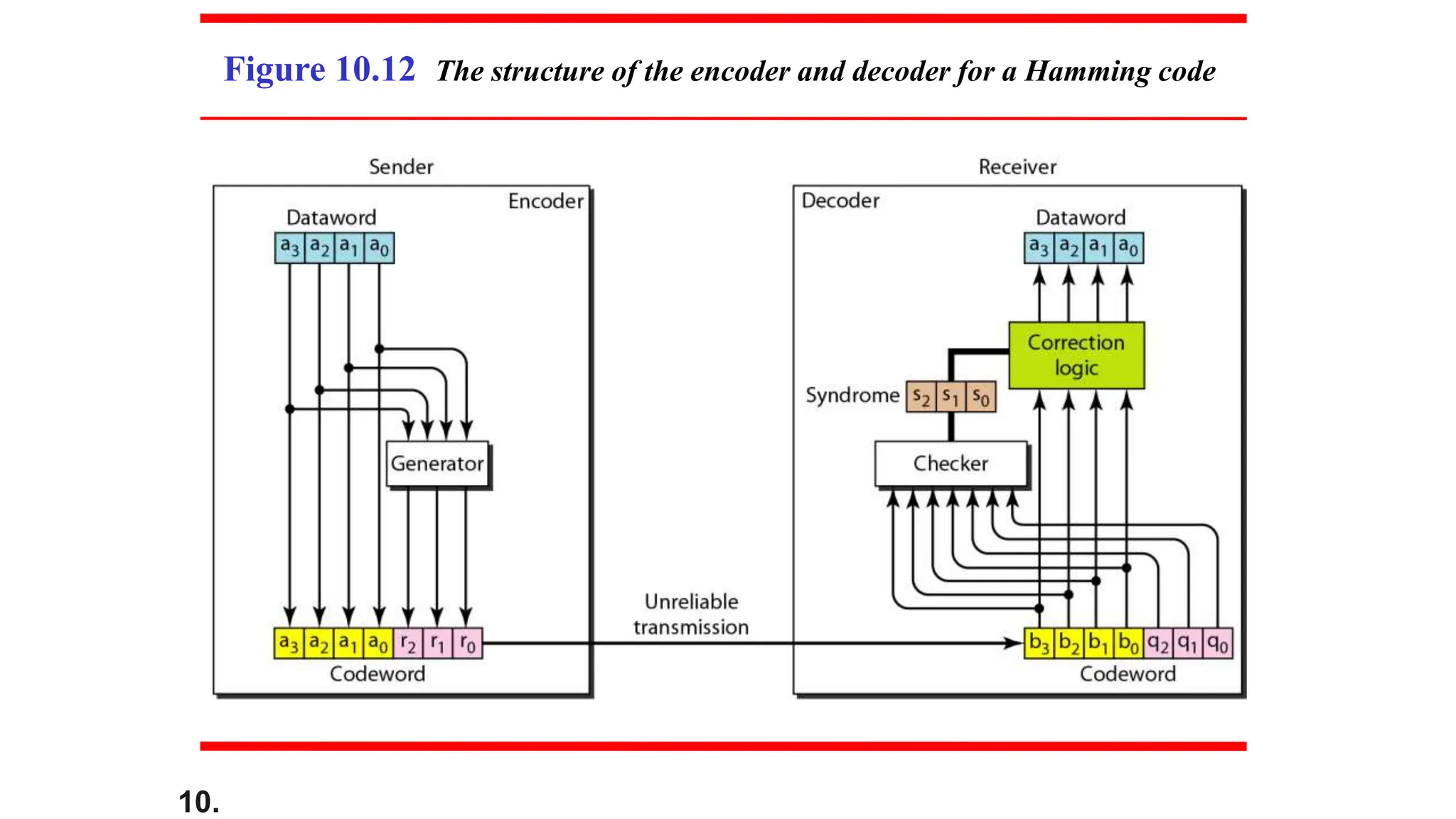
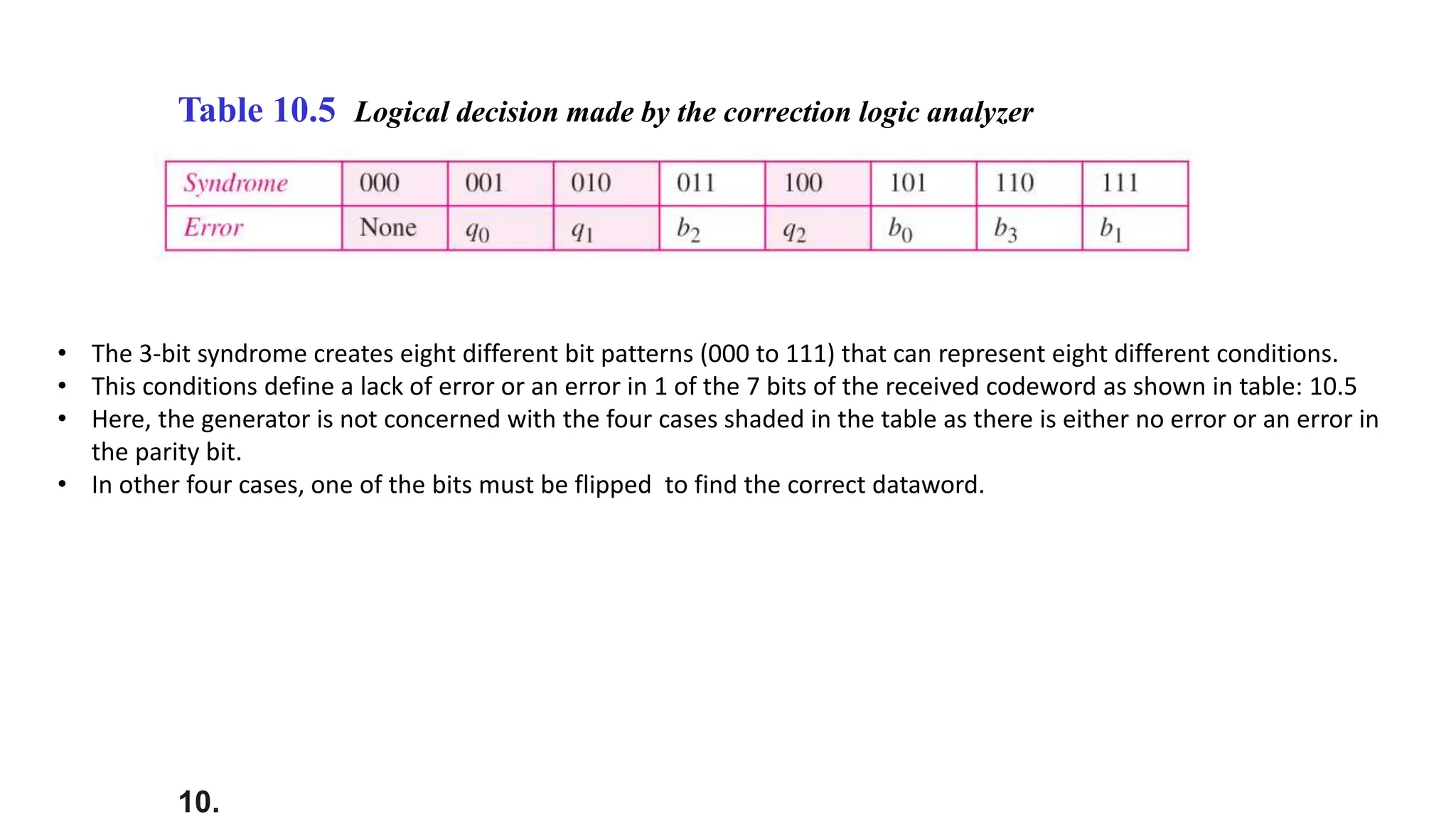
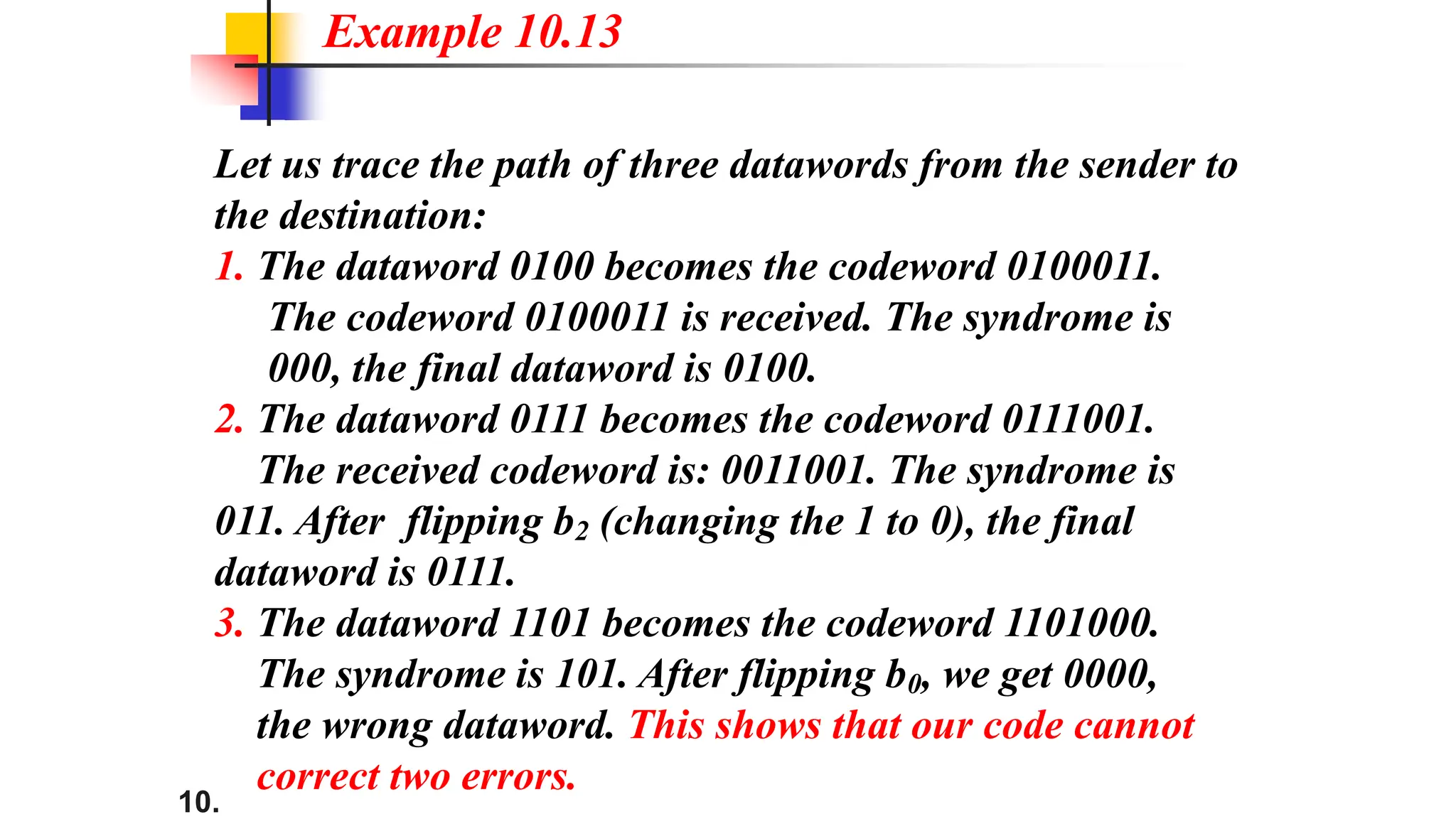
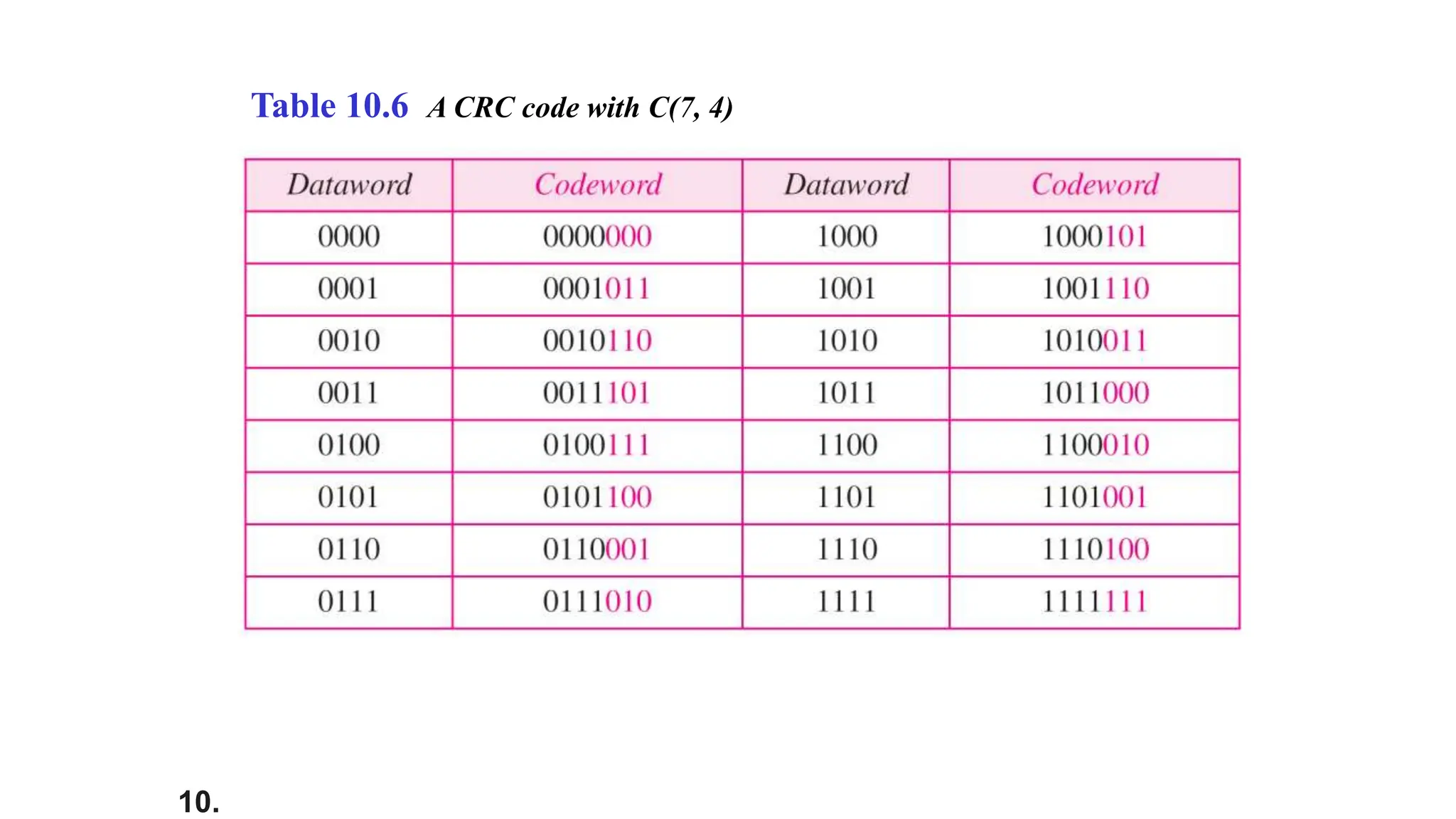
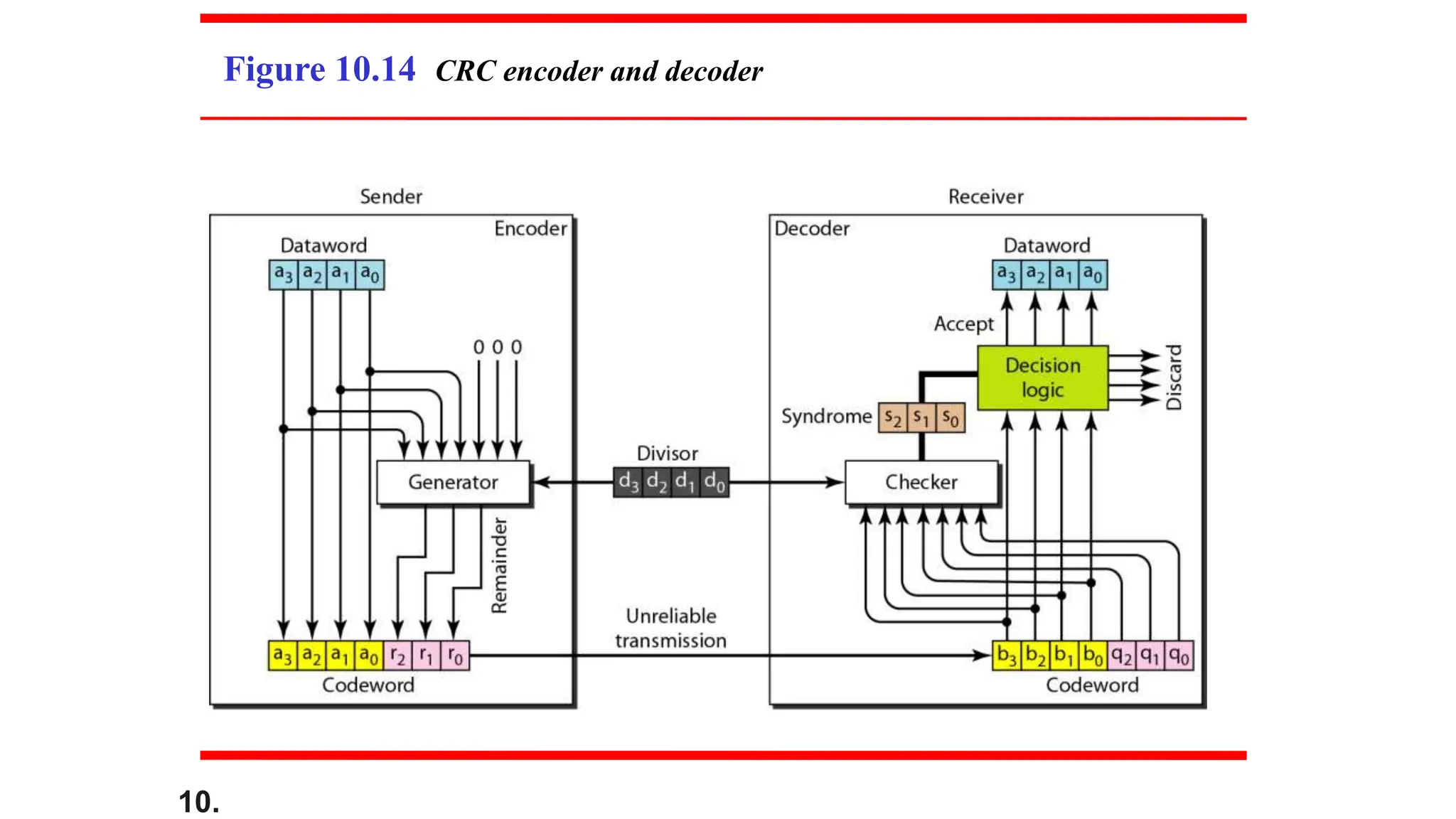
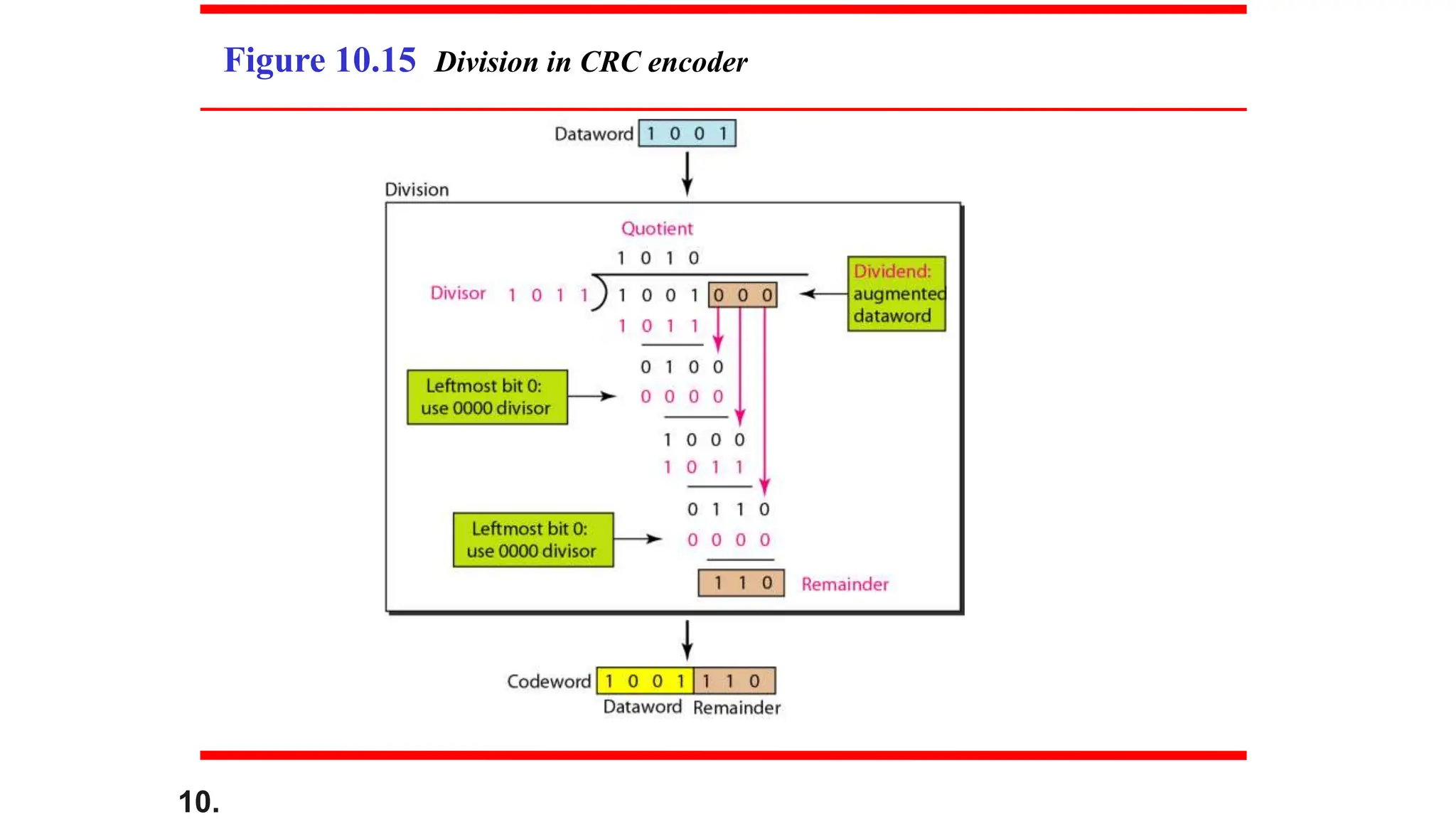
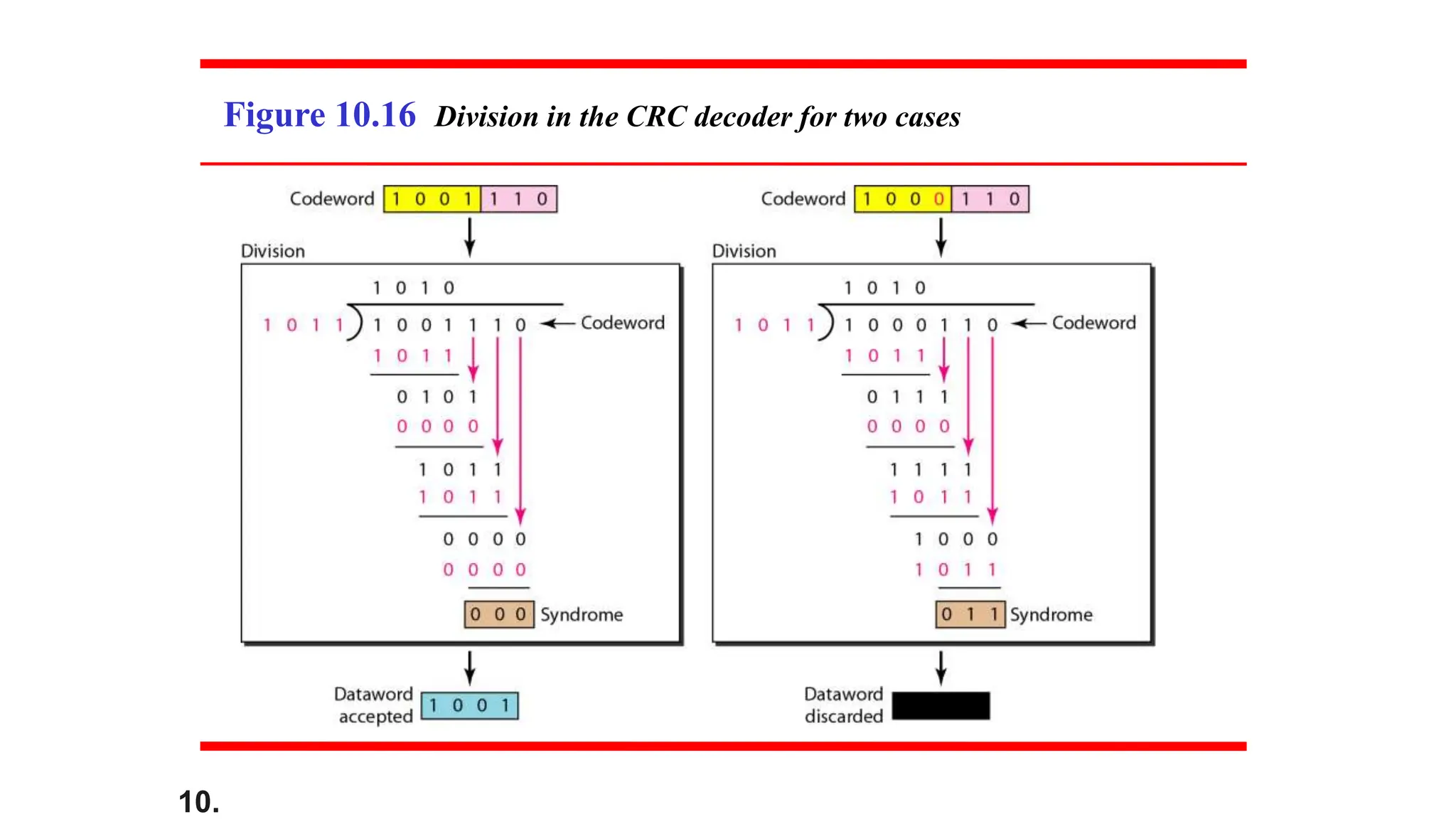
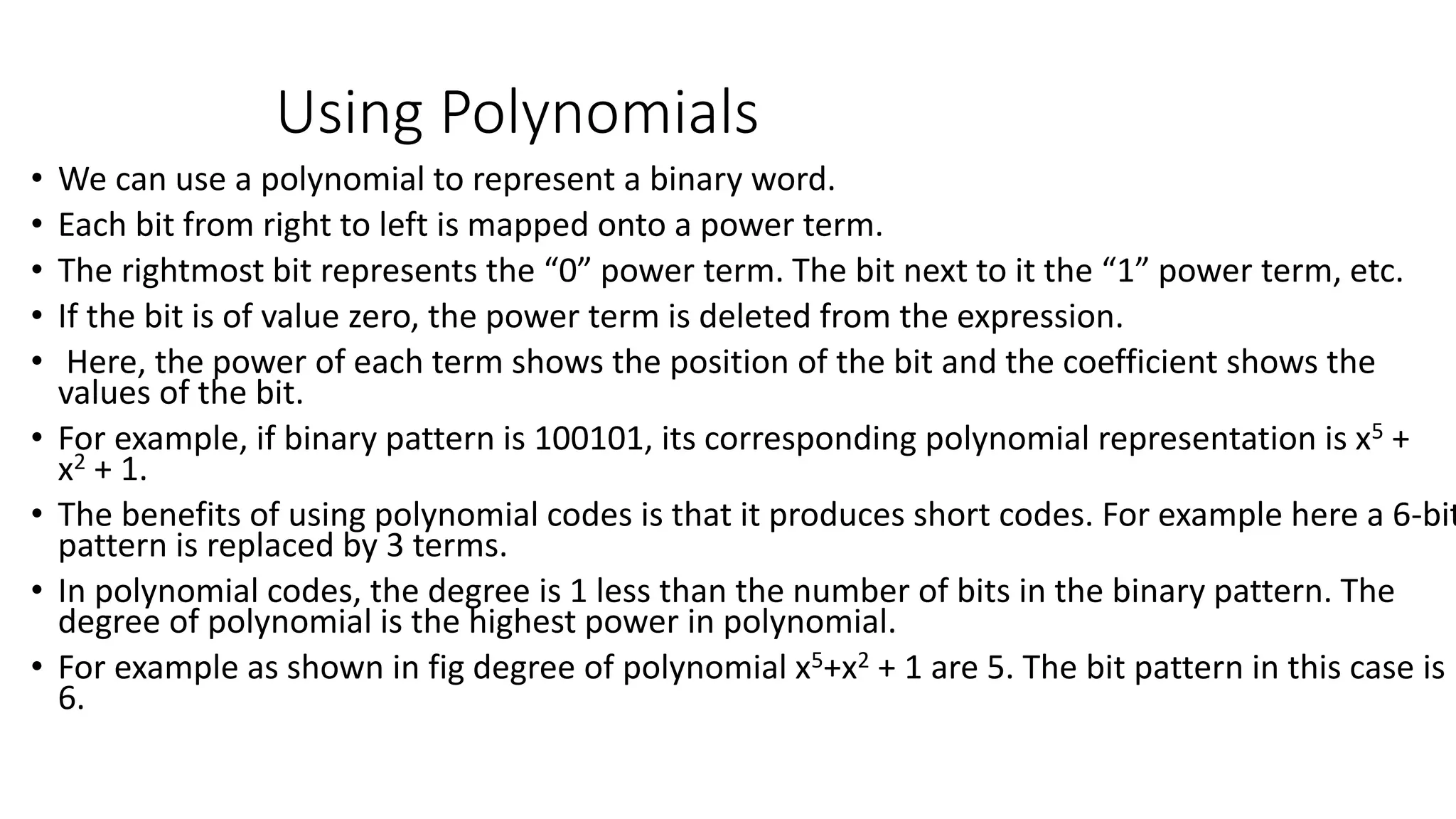
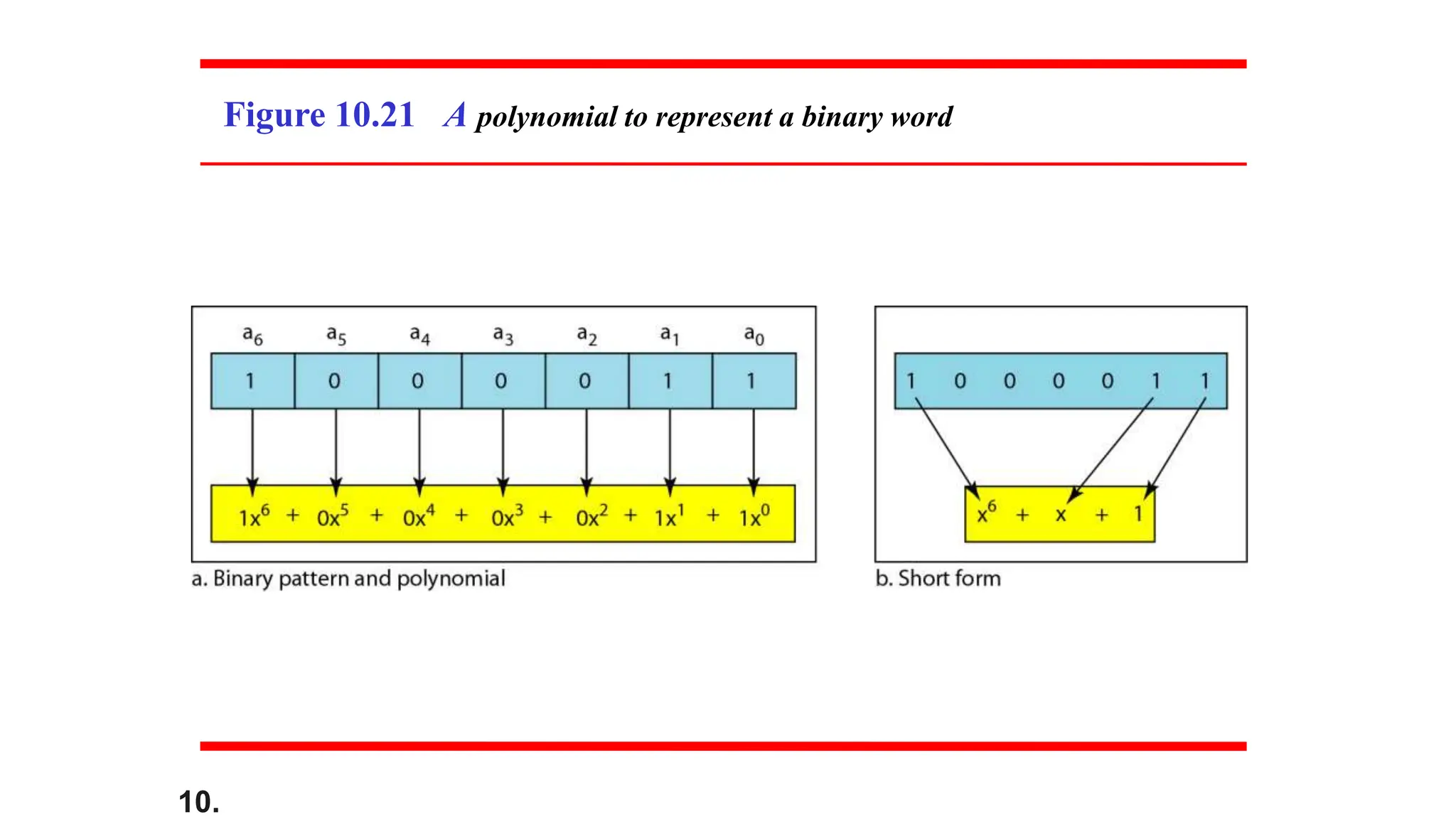
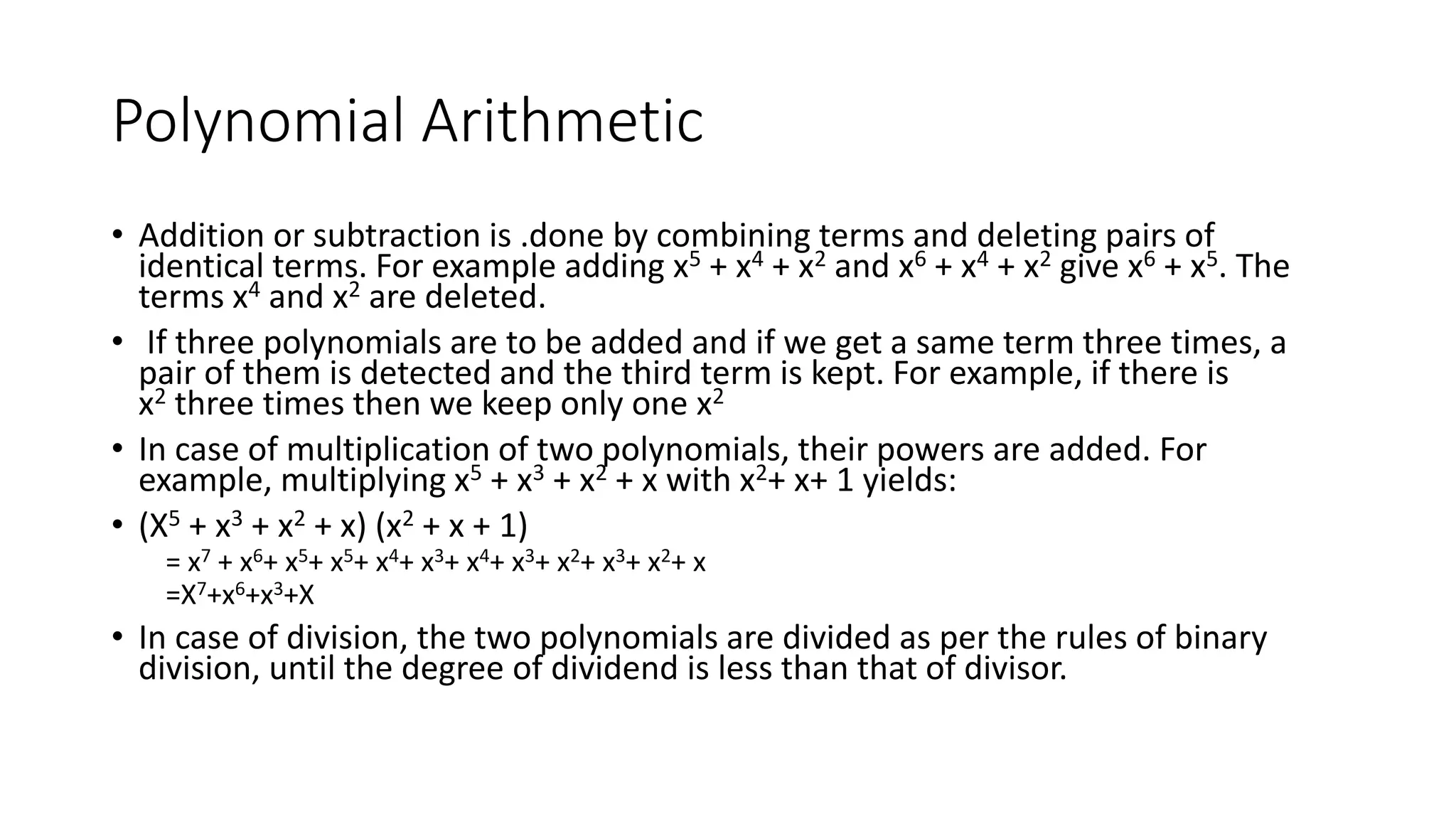
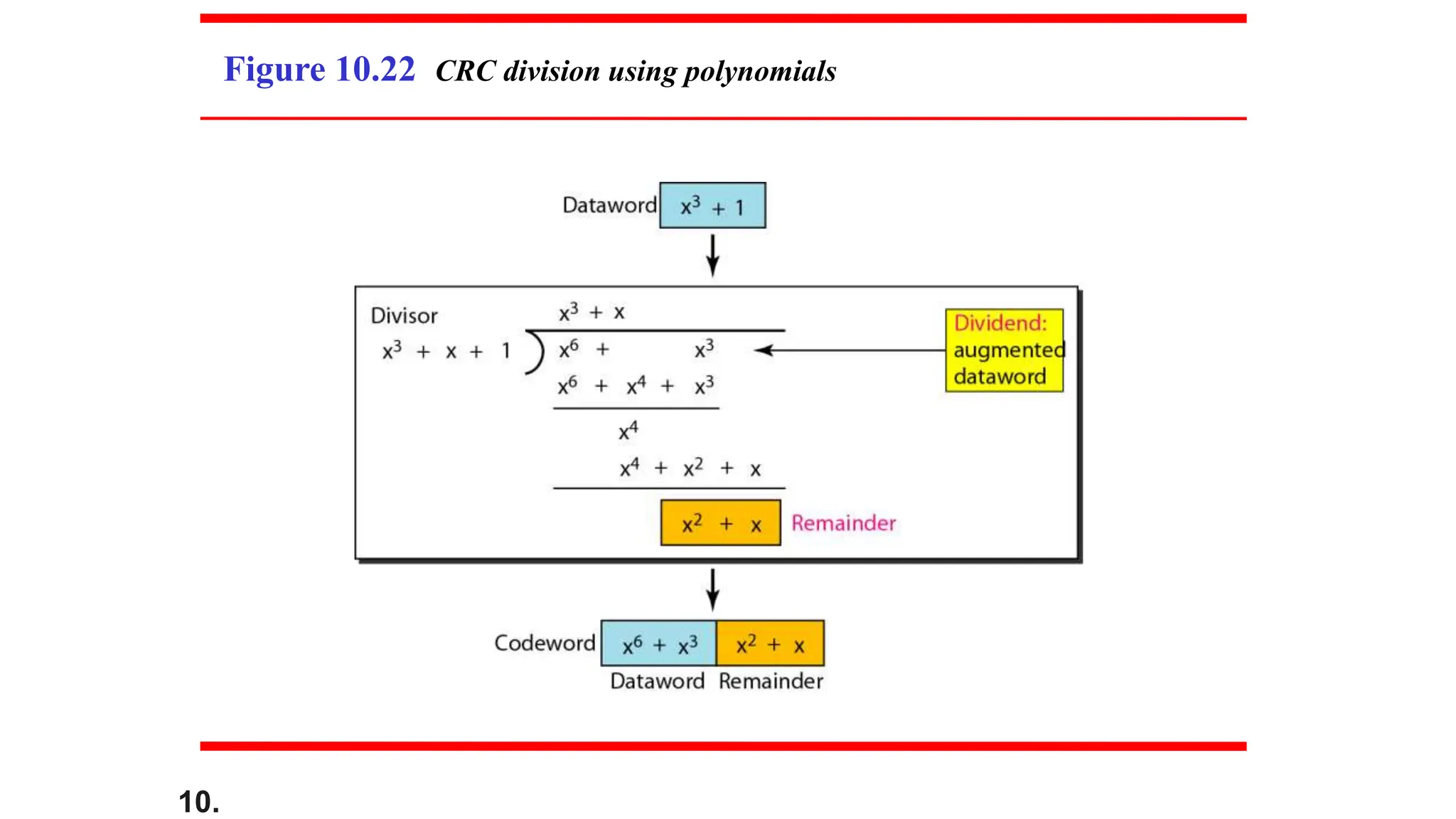
This document discusses error detection and correction. It begins by defining different types of errors that can occur like single-bit and multiple-bit errors. It then discusses concepts like redundancy and error detection vs correction. Specific error detection and correction techniques are covered such as block coding, forward error correction vs retransmission, linear block codes including Hamming codes and cyclic redundancy checks (CRC). Worked examples are provided to illustrate key concepts.