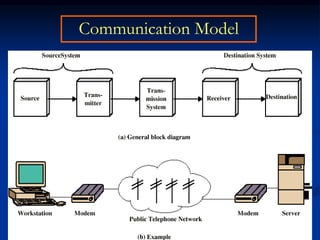
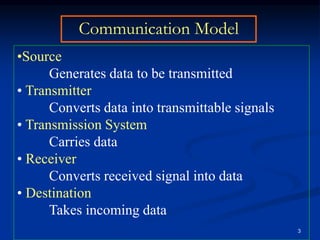
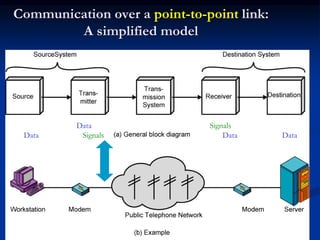
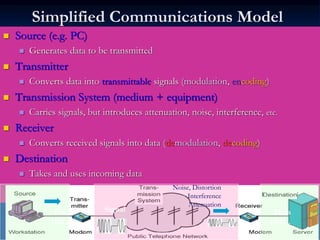
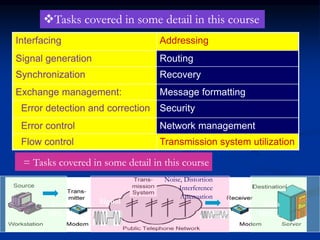
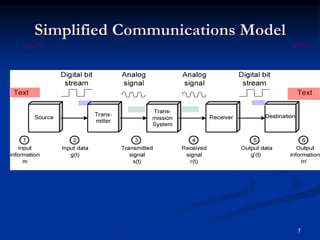
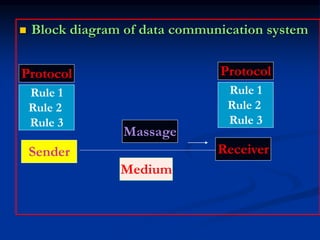
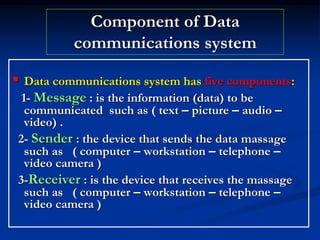
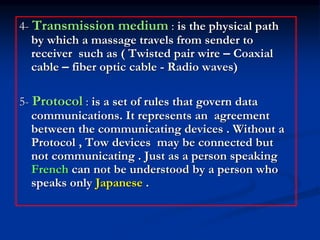
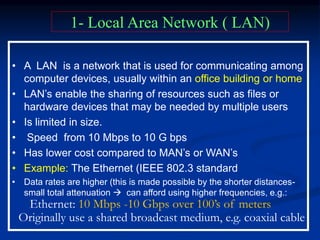
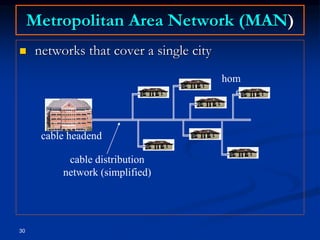
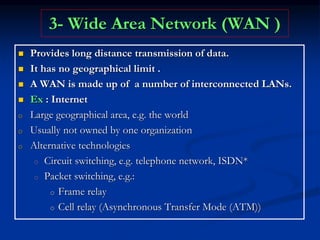
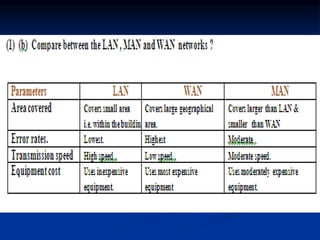
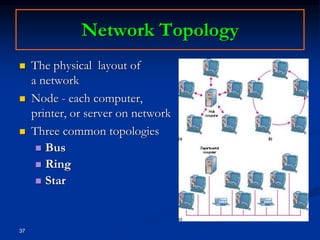
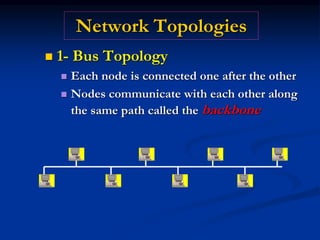
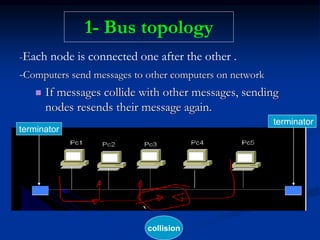
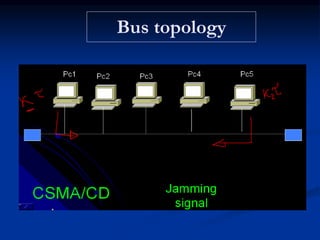
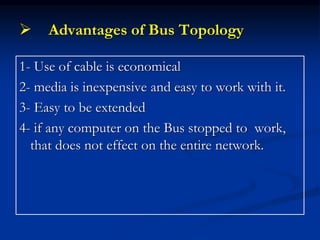
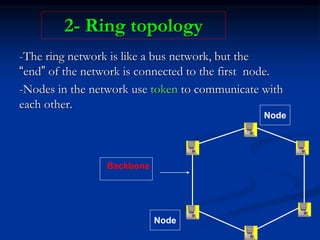
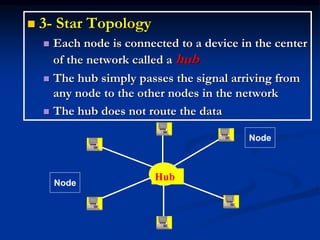
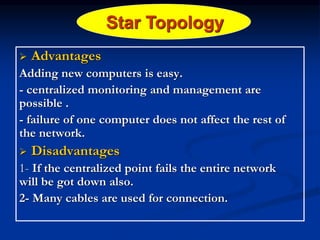
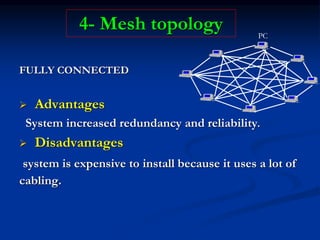
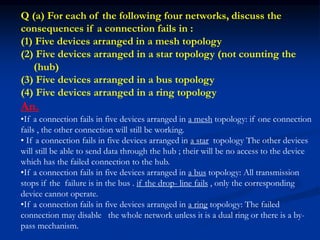
This document provides an overview of data communication systems and computer networks. It discusses the basic components of a communication system including the message, sender, receiver, transmission medium, and protocols. It then describes different types of network topologies including bus, star, ring, and mesh. The document also defines local, metropolitan, and wide area networks and how they differ in size and scope. Finally, it discusses some important network concepts like protocols, standards, and the organizations that develop standards to ensure interoperability.