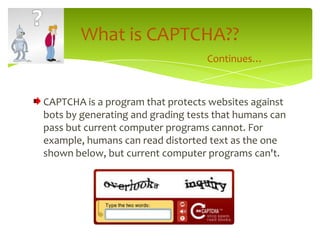
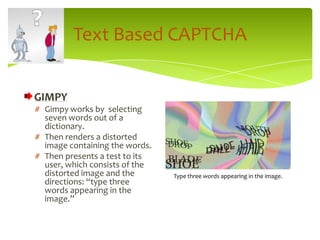
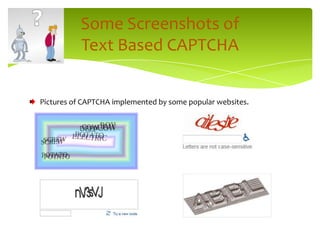
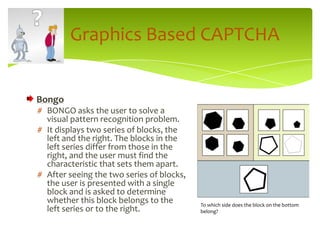
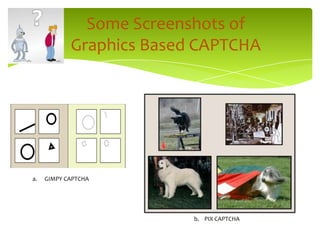
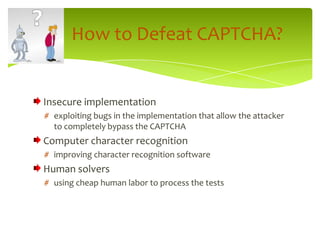
The document provides an overview of CAPTCHAs, which are programs designed to differentiate humans from bots by presenting tests that humans can pass but computers cannot. It outlines the history of CAPTCHAs, their various applications, and different types of CAPTCHAs, including text-based, graphics-based, and audio-based. Additionally, it discusses challenges in breaking CAPTCHAs and references key literature on the topic.