The document discusses a seminar report on a novel algorithm developed to solve text-based CAPTCHAs by simultaneously handling segmentation and character recognition through machine learning. This approach overcomes limitations of traditional sequential methods, which often fail due to complex distortion techniques such as negative kerning. The research aims to inform future CAPTCHA designs by demonstrating potential weaknesses in current systems and advocating for stronger alternatives.
![ABSTRACT
Over the last decade, it has become well-established that a captchas ability to with-
stand automated solving lies in the difficulty of segmenting the image into individual
characters. The standard approach to solve captchas automatically has been a se-
quential process wherein a segmentation algorithm splits the image into segments
that contain individual characters, followed by a character recognition step that uses
machine learning. While this approach has been effective against particular captcha
schemes, its generality is limited by the segmentation step, which is hand-crafted to
defeat the distortion at hand.
No general algorithm is known for the character collapsing anti-segmentation tech-
nique used by most prominent real world captcha schemes. Here a novel approach
to solve captchas in a single step that uses machine learning to attack the segmen-
tation and the recognition problems simultaneously is formulated. Performing both
operations jointly allows the algorithm to exploit information and context that is
not available when they are done sequentially. At the same time, it removes the need
for any hand-crafted component, making the approach generalize to new captcha
schemes where the previous approach cannot.
Many websites use captchas, or Completely Automated Public Turing tests to tell
Computers and Humans Apart, to block automated interaction with their sites. For
example, G mail uses captchas to block access by automated spammers, eBay[12]
uses captchas to improve its marketplace by blocking bots from flooding the site
with scams, and Facebook uses captchas to limit creation of fraudulent profiles used
to spam honest users or cheat at games. The most widely used captcha schemes use
combinations of distorted characters and obfuscation techniques that humans can
recognize but that may be difficult for automated scripts. captchas are sometimes
called reverse Turing tests, because they are intended to allow a computer to deter-
mine whether a remote client is human or machine.](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-2-2048.jpg)


![Chapter 1
Introduction
A captcha stand for Completely Automated Public Turing test to tell Computers
and Humans Apart [8]is a type of challenge-response test used in computing to de-
termine whether or not the user is human. From the abbreviation it was clear that
captcha is a Turing test. Turing test is a test a machines intelligence level, to know
whether the machines intelligence reaches up to the level of humans. captcha was
found in 2000 by Luis von Ahn, Manuel Blum and Nicholas J. Hopper of Carnegie
Mellon University and John Langford of IBM[14]. We know that captcha is used to
determine whether user is machine or human but this was old concept. With the
implementation of the captcha breaking system as mentioned in the reference paper
most of the captchas can be decode by the algorithm designed by the authors. So in
order to undergo Turing Test captcha is old fashion now stronger method or captcha
has to be designed. This captcha breaking system can break most of the captcha in
various web application systems
The standard approach to solve captcha automatically (i.e. by a computational de-
vice) is by sequential processing. This Sequential processing consists of two major
functions they are Segmentation [32] and Recognition. The segmentation algorithm
splits the image into segments that contain individual characters. The recognition
algorithm uses machine learning to recognize a single character. After recogniz-
ing all the character the machine can generate the perfect decoded format of the
captcha. After segmentation of captcha, Recognition is performed that is why it
is called sequential processing. This approach is effective only against a particular
set of captcha schemes. In some captcha schemes the sequential processing will
fail at segmentation step. These exceptional captcha schemes follow hand-crafted
to technique. There is no general algorithm known for the character segmentation
process for hand real world captcha schemes. Due to this drawback the traditional
sequential processing failed.
Here the discussion is about the algorithm which is not sequential but simultane-
ous processing. That is the two major functions Segmentation and Recognition are
executed simultaneously over the captcha. Performing both operations jointly allows
the algorithm to get full information for machine learning and context which was
not available when sequential Algorithm was used. It also removes the hand-crafted
schemes, making this approach the generalized approach to new captcha schemes
where the previous approach cannot.
Many websites use captchas, Gmail uses captchas[7] to block spam access, eBay uses
1](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-5-2048.jpg)
![Generic Solving of Text-based captchas
captchas to prevent flooding into the site with scams, and Facebook uses captchas
to limit creation of system based fake profile generation. users or cheat at games.
The most widely used captcha schemes use combinations of distorted characters and
obfuscation techniques that humans can recognize but that may be difficult for au-
tomated scripts. Captchas are sometimes called reverse Turing tests, because they
are intended to allow a computer to determine whether a remote client is human or
machine[15]. The effectiveness and universality of the results suggests that combin-
ing segmentation and recognition is the next evolution of automated captcha solving,
and can suppress the sequential approach used in earlier works. After comparing
the accuracy of the algorithm with the accuracy of humans it was found that purely
text based captchas[16] may be nearing their end, and provides early steps toward
rethinking how reverse Turing tests can be performed securely.
Dept. of Computer Science & Engg. 2 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-6-2048.jpg)
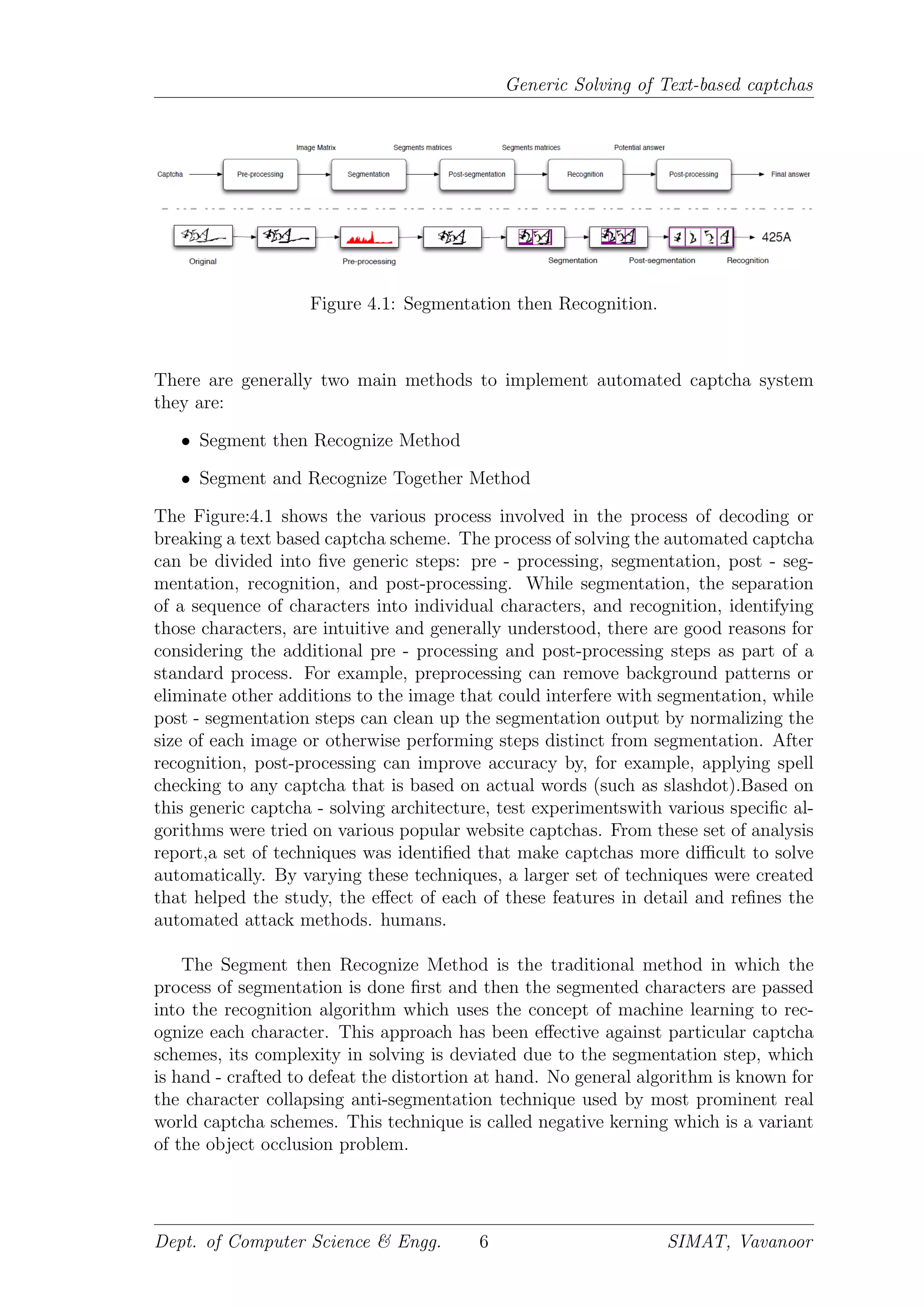
![Chapter 4
Approaches and Data Set
4.1 Approach
As mentioned earlier in the Introduction part, that this algorithm is only applicable
for text based captcha as a result the discussion of the topic is only related to the
text based captcha system. The text based captchas[13] are treated as an image.
As the captcha is an image the various image processings techniques are used to un-
dergone. In this section we will discuss the various approaches made in past and the
approach made to implement automated captcha solving system and its limitations.
In order to implement the automated captcha the entire process of automation
consist of two main process they are:
• Segmentation - Segmentation is the process of partitioning a digital image
into multiple segments (sets of pixels, also known as superpixels). The goal
of segmentation is to simplify and/or change the representation of an image
into something that is more meaningful and easier to analyze.Image segmen-
tation is typically used to locate objects and boundaries (lines, curves, etc.)
in images. Here this process is used for dividing the characters of the captcha
in to different individual characters is called segmentation. This process is
the most difficult and complex to design. It also uses the concepts of Image
processing as the captcha is an image. Practically it is said that there is no
effective algorithm which does the process of segmentation accurately.
• Recognition - Recognition is a field that includes methods for acquiring, pro-
cessing, analyzing, and understanding images and, in general, high-dimensional
data from the real world in order to produce numerical or symbolic infor-
mation. The process of recognizing each distorted individual character (seg-
mented character) with the help of machine learning is called recognition.
The concept of machine learning is used in recognition because it was found
that the machine learning algorithms consistently outperform humans for sin-
gle character recognition. Due to the presence of the Image recognition the
algorithm becomes more smarter and intelligent
5](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-9-2048.jpg)
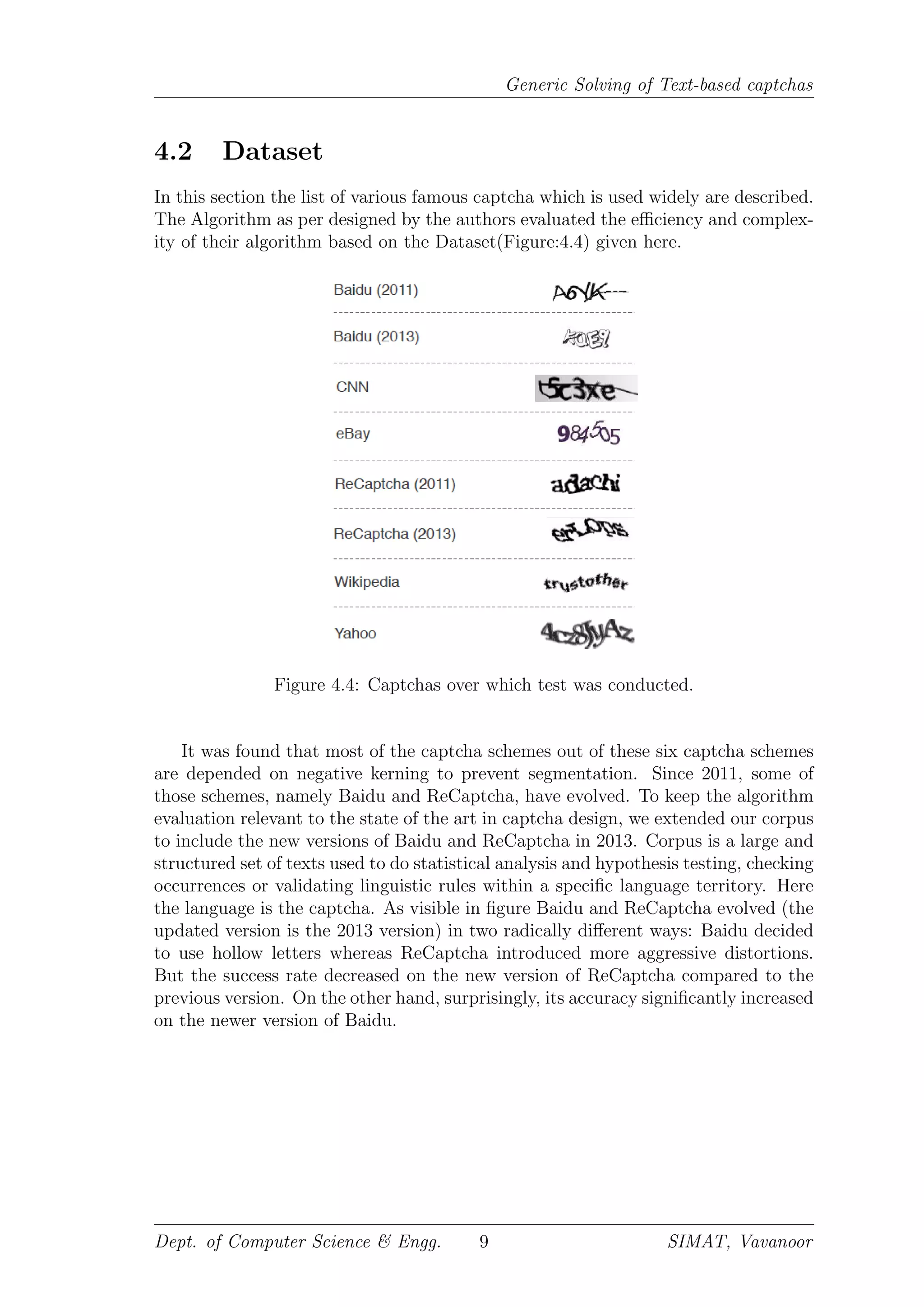
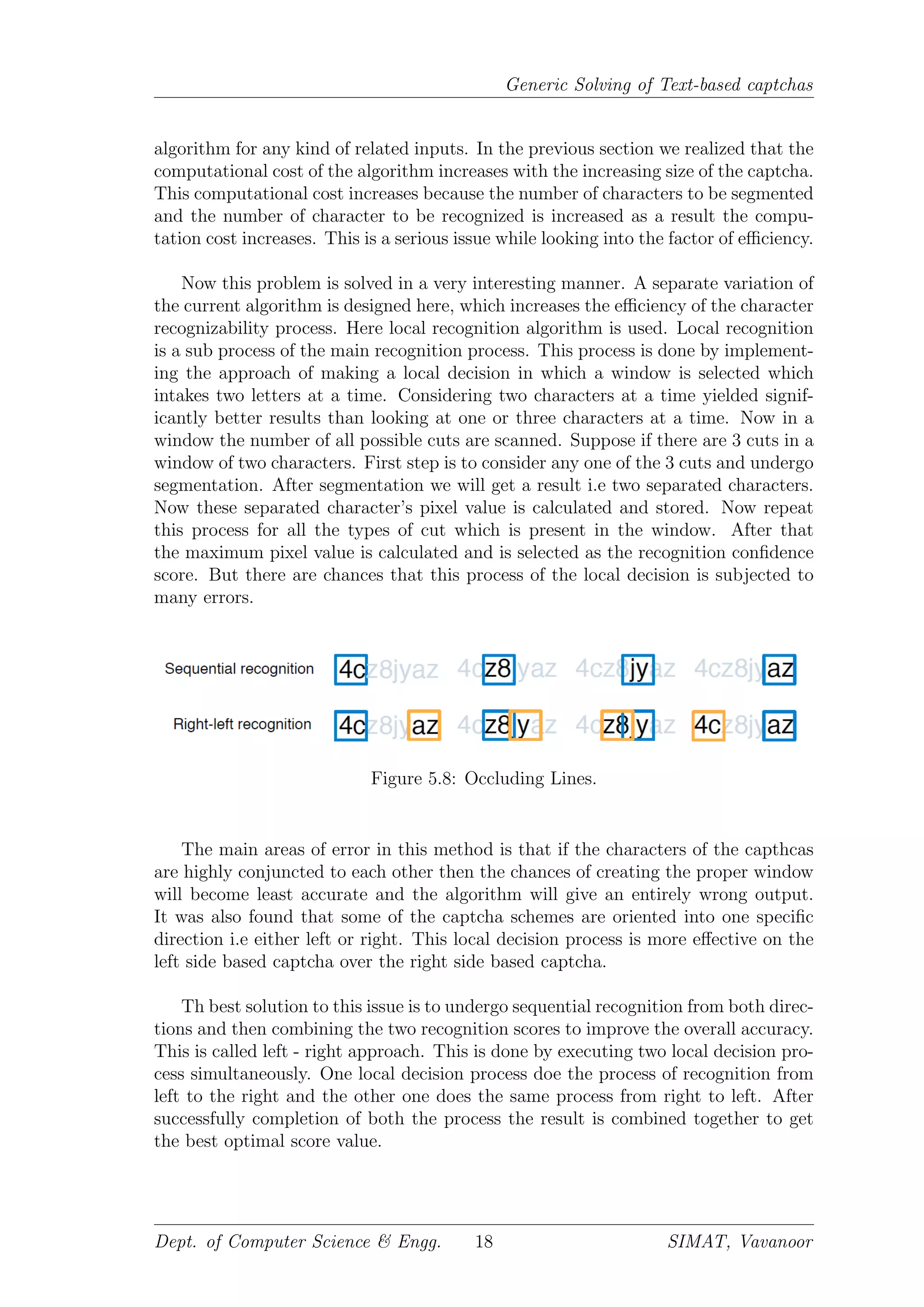
![Generic Solving of Text-based captchas
(a) captcha with no noise
and distortion
(b) captcha with cut
through lines
(c) captcha with color and
distortion
Figure 4.2: Various Distortion in Negatively Kerned captcha.
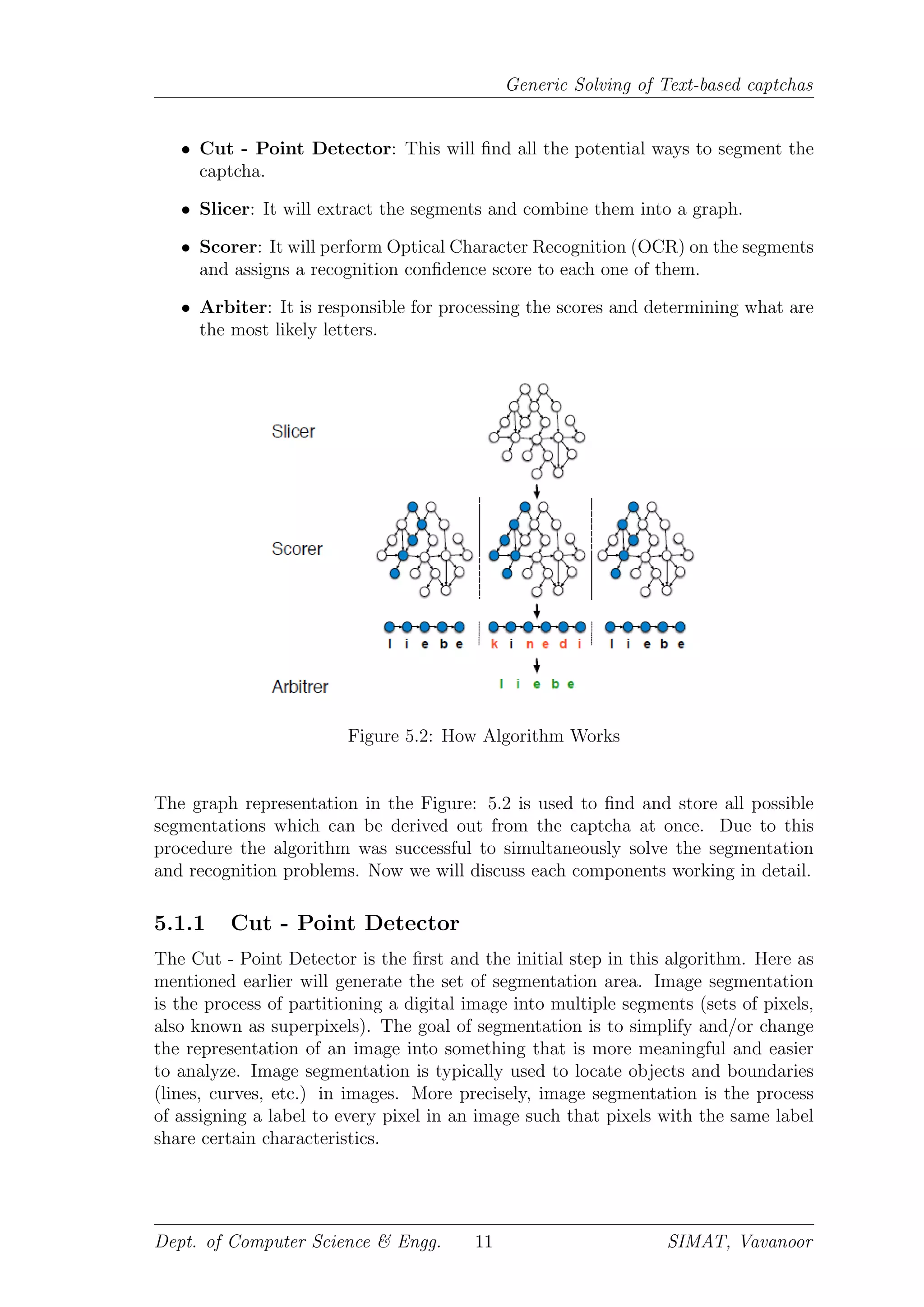
Negative Kerning (Figure:4.2) is a character collapsing technique in which the
space between the characters are removed and each characters are occluded with
the neighboring character. The process of occluding means to joint or to attach the
characters. Along with the process of occluding characters in the negative kerning
process some extra noises, distortion and randomization are also added to prevent
side channel attack. This adding up of noises is in the form of adding colors, dis-
torted cutting through text lines in order to make the captcha more complex. Side
channel attack is the process of recognizing the captcha content from the process
of continuous learning of each character in captcha and predict the result. When
noises are added up in the Negatively Kerned captcha then it will be difficult for
undergoing side channel attack[19].
The Figure:4.2a shows the captcha which undergone negative kerning but there
was no noise[11], no occluding lines and no external distortions are added up. The
Figure:4.2b shows the captcha on which negative kerning and occluding lines are
added up to make more distortions and causing confusion. The Figure:4.2c shows a
simple captcha with distortions in the form of color, occluding lines and dots, here
no negative kerning is implemented. Negative kerning is considered the most secure
method for preventing segmentation because it has successfully withstood years of
attacks. Almost all of the most prominently used captcha schemes rely on it. The
other method of choice to prevent segmentation, which seems to have fallen out
of fashion after a successful wave of attacks, is to use occluding lines. A captchas
ability to withstand automated solving lies in the difficulty of segmenting the image
into individual characters rather than recognizing the characters themselves. Which
means that the segmentation process is the difficult part in the automated captcha
system. Up till now there have been two approaches/works which have been formu-
lated for automated captcha solving:
The first type of attack is to undergo side channel attack for all type of captcha.
In this method the segmentation algorithm will does the task of dividing the captcha
into different characters along with the consecutive distortion faced by the particular
character. The machine learning part will then try to remove the distortion or pre-
dict the character and generate the output. But this approach is not much favorable
because the defender can easily defend the captcha by making the captcha difficult
for segmentation and if the segmentation was carried out then also the output will
not be proper. So as a result this attack approach cannot be applied over all the
captchas.
The second type of attack focuses on finding weaknesses in the distortion algo-
rithms of particular captcha schemes. A specially designed segmentation algorithm
Dept. of Computer Science & Engg. 7 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-11-2048.jpg)
![Generic Solving of Text-based captchas
is designed by the attacker which works on the principle of image processing and
morphological segmentation. This is used to remove the distortion. The image pro-
cessing algorithm is provided with the features to recognize the twisted and turns in
the captcha text. So based on the twist and turns in the captcha the image process-
ing algorithm will undergo the process to make it into understandable format. The
morphological segmentation does the task of filling the missing data based on the
relevant information obtained from the image processing part. While this attack was
also a failure. This approach was only applicable over the reCaptcha 2011 scheme.
Later in 2013, a group or researchers examined hollow captcha, specifically and were
able to solve all of the captcha schemes by extending the segmentation process then
recognize approach that involves nine consecutive steps.
Up till now research in captcha solving has followed the exploit - patch cycle.
The exploit - patch method was tried on the best 15 captcha scheme shown in
Figure:4.3 In the exploit - patch cycle the attacker finds a flaw in a particular
anti - segmentation technique, and then the defender tries to patch it, the process
of removing the flaw int the anti - segmentation technique or moves on to a new
one. The limitation of the segment then recognize approach has been the attacker’s
ability to find new flaws. This proposed algorithm can overcomes this limitation by
segmenting and recognizing the captcha simultaneously, thus removing the need for
manually discovered heuristics to segment captchas [1].
Figure 4.3: 15 Best Captchas over which test was conducted.
Dept. of Computer Science & Engg. 8 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-12-2048.jpg)
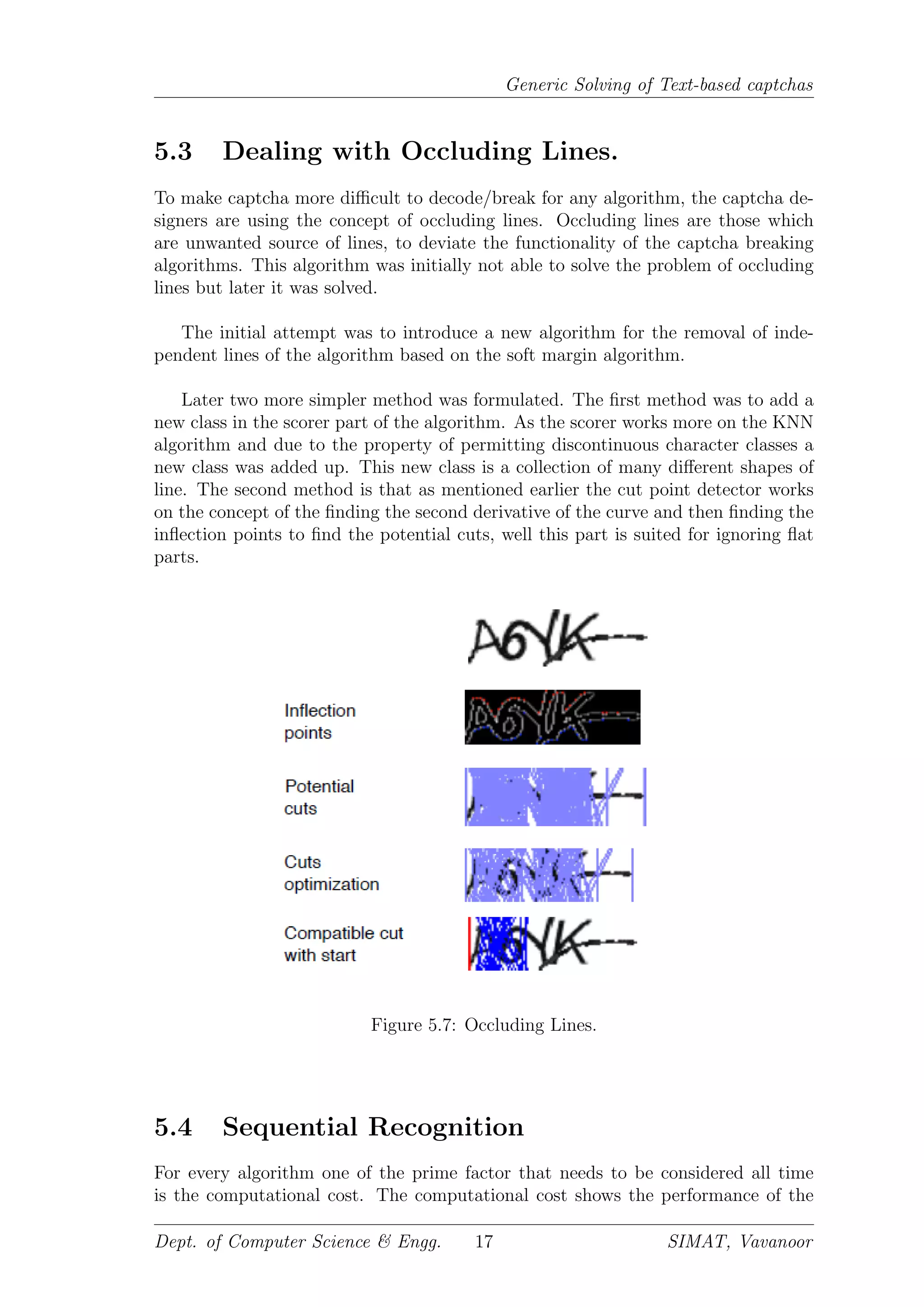
![Generic Solving of Text-based captchas
So in order to undergo the segmentation we need two points(pixels), to construct
a line segment, for segmentation. This two points can be obtained by characters ex-
amining the second derivative of the curve generated by following the bottom pixels
of the captcha, and the curve generated by following the top pixels of the captcha.
Now we got two set of curves, first curve is the second derivative of the top pixels of
captcha and the second curve is the second derivative of the bottom pixels of captcha.
Now in both the curves we have to mark the points for undergoing segmentation.
These points can be obtained by finding the Inflection points [31] on the curve. The
inflection point is a point on a curve at which the curve changes from being concave
(concave downward) to convex (concave upward), or vice versa. So we will get a
set of inflection points on the first curve and the second curve. The set of inflection
points on the first curve is marked as red color and the set of inflection points in
bottom is marked in blue color.
Now after getting the points to generate the cuts the process of finding all possible
cut lines is initiated. Now each cut is constructed by connecting the inflection points
- one from the top, and one from the bottom. On doing this process for the entire
curve we will get a set of cuts called as the Potential Cut. And this Potential Cuts
are marked over the captcha. Now this captcha containing the Potential cuts are
given as input to the Slicer.
Figure 5.3: Example of the algorithm successfully applied to a Yahoo captcha
Dept. of Computer Science & Engg. 12 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-16-2048.jpg)
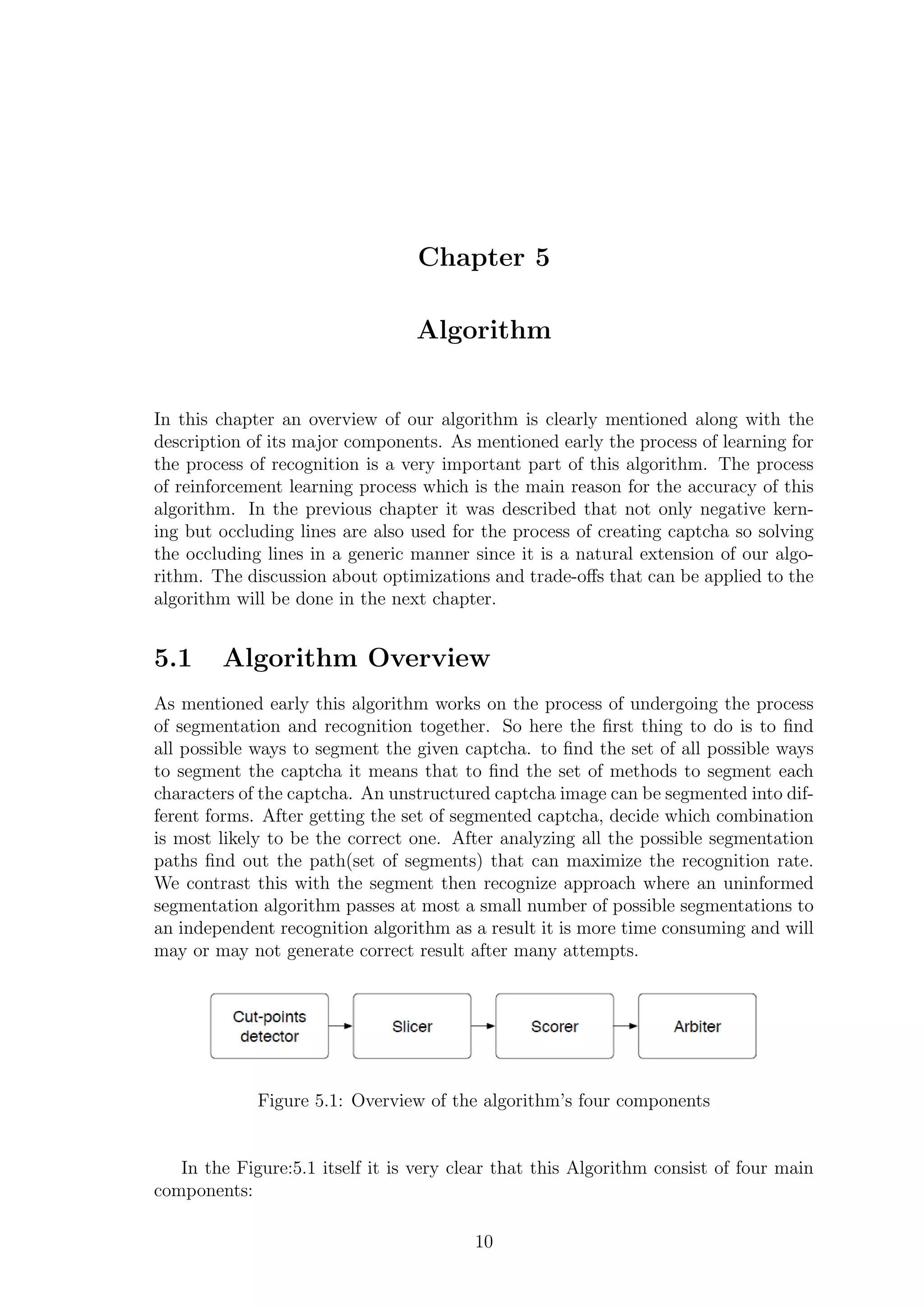
![Generic Solving of Text-based captchas
5.1.2 Slicer
The Slicer is provided with a captcha containing potential cuts marked over it as
input. The slicer applies some heuristics [30] to extract the meaningful potential
segments based on the cut points and builds the graph as shown in Figure: 5.4. A
potential segment is considered meaningful if the two cuts that define its left and
right boundaries are sufficiently far apart, yet not too far apart. The process of
formation of graph (Figure:5.5) is a real unique process. In this algorithm the entire
text based captcha is divided into a set of window consisting of 2 characters at a
time. So as shown in the Fig. we can see the Characters A and B are the two char-
acters of the captcha and resides in the window. This window consist of 4 potential
cuts which was found in the previous step.
Now the process of taking the content in the segments region is initiated. Initially
the algorithm takes the region within the segment 0 and 1, where 0 and 5 are the
borders of the window treated as a segment. The content is analyzed and a weight
is assigned to the recognized part along with the possible character. Moving to the
next cut i.e the region between the segments 1 and 2, this region doesn’t gives a
meaningful segment as a result it is discarded. After getting all the values a graph
is traversed with the segments as the nodes and the vertices’s are with the possible
character and the weight assigned. Based on this graph the best cut can be found
here cut 3 because region from 0 to 3 and 3 to 5 gives nearly same character and
same weight value In simple terms it means that a cut or segment is said to be po-
tential if the distance towards the black pixels from the segment pixel is sufficiently
far yet not too far.
Figure 5.4: Cut Optimization
So naturally if the number of potential cuts increases the computation time also
increases. It was found that using this algorithm it took 9 hours to undergo Slicing
over a captcha containing 12 characters. So to remove this draw back the only
remedy is to decrease the number of cuts in the Potential Cut set. So for optimizing
this algorithm a new approach is formulated which works by pruning(removing)
near- duplicate and improbable cuts from the set of potential cut points.First, we
removed all the cuts that have an angle > 30. Then we examined the ratio of
white pixels to black pixels to eliminate cut lines that pass through too many black
pixels, since they are most likely cutting through the middle of a letter. Finally we
Dept. of Computer Science & Engg. 13 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-17-2048.jpg)
![Generic Solving of Text-based captchas
Figure 5.5: Graph creation in Slicer
compared the pixel intensities of the left and right boundaries to estimate whether
the cut marks a transition between two letters.
5.1.3 Scorer
The scorer does the task of assigning a score value for each character which got seg-
mented. The scorer traverse the graph of potential segments and applies OCR and
then assign a confidence value. In the previous step the algorithm generates per-
fectly segmented character they are called the potential segments. Now the Scorer
will scan or analyze these segments and generate a score for the character. After
generating the score using KNN algorithm the class to which the potential segment
belongs is found out.
The KNN algorithm [29] known as k Nearest Neighbor algorithm. This algo-
rithm is an classification algorithm, it works on the principle of making an element
belongs to a class from the set of classes by measuring the distance k from each class
in the feature space. But here modified version of KNN algorithm is used.
First after getting the potential segments in the captcha, at pixel level the score
value is calculated for the corresponding character and then based on the overall
confidence value it assigns a recognition confidence score. This recognition confi-
dence score is used as the source for the KNN algorithm and its value is checked
with the surrounding class values. The class contain set of similar characters, like for
example A,4 belong to same class similarly 0,O belong to same class. The same class
elements have a nearly same value because their character appearance are alike. So
allocating each captcha value to a particular class is the prime task done here.
Segments are processed at the pixel level, as this has been demonstrated to be
the best approach for text recognition. Here the KNN algorithm is more preferable
because of the following factors : computation at pixel level, noise resistance and
computational speed. The noise resistance arises from using a relatively small k
(less than 10) in our KNN to identify the nearest neighbors. This is essential in our
case because most of the potential segments generated by the slicer are meaningless
and belong to the garbage class.
Dept. of Computer Science & Engg. 14 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-18-2048.jpg)
![Generic Solving of Text-based captchas
A metric distance function is a function that defines a distance between elements
of a set. It was realized that the problem was assigning an equal weight to each pixel
regardless of its position in the segment or its gray scale value. It turns out that
pixels on the edge of segments are less meaningful than pixels in the center precisely
because they are shared between characters that have been collapsed together. We
achieved very good results on all captcha schemes by assigning higher weight to
pixels nearer the center of the segment, and to darker ones.
5.1.4 Arbiter
The arbiter is the final component of this algorithm. The arbiter does the task
of taking in the input from the Scorer, that is the recognition confidence score ,
and will check it with the trained accurate values of the class members and then
generate the solution of that segment. The scorer will generate the result that the
given segment of character will belong to which class. Now the arbiter does the job
of accessing all the data in that particular class and analyzing each one with the
segmented character.
For this method here the approach of ensemble learning approach is used. The
Ensemble learning [27] is a technique for combining many weak learners in an
attempt to produce a strong learner. The term ensemble is usually reserved for
methods that generate multiple hypotheses using the same base learner. So the
class will contain all set of segmented character set on the basis of their confidence
score. So based on the requirement the algorithm’s approach will deeply study the
input and tries its maximum to reach to the solution.
5.2 Reinforcement Learning
Reinforcement Learning [28] is an important part of this algorithm. Reinforcement
learning is an area of machine learning inspired by behaviorist psychology, con-
cerned with how software agents can probably take actions in an environment so as
to maximize reward. So as a result we can say that reinforcement learning can also
make the algorithm more smarter and clever. Reinforcement learning is based on
the concept of ”making understand first and then react”, so like wise here also we
can use this approach in the algorithm too.
The traditional way to train a character classifier is to provide a set of labeled
captchas which are already segmented and then let the classifier learn to recognize
each character from those segments using the labels. So here providing the labeled
segmented captcha is an intelligent process.In this process it is assumed that the
classifier is given with the correct number of segments - one for each letter in the
captcha. Now based on this labeled capthca the algorithm will learn the various
approaches or schemes used in the traditional text based captcha and then it will
generate the solution. In the ”segment then recognize” approach, this assumption
holds because the segmentation is handled by a vision algorithm that is not part of
Dept. of Computer Science & Engg. 15 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-19-2048.jpg)

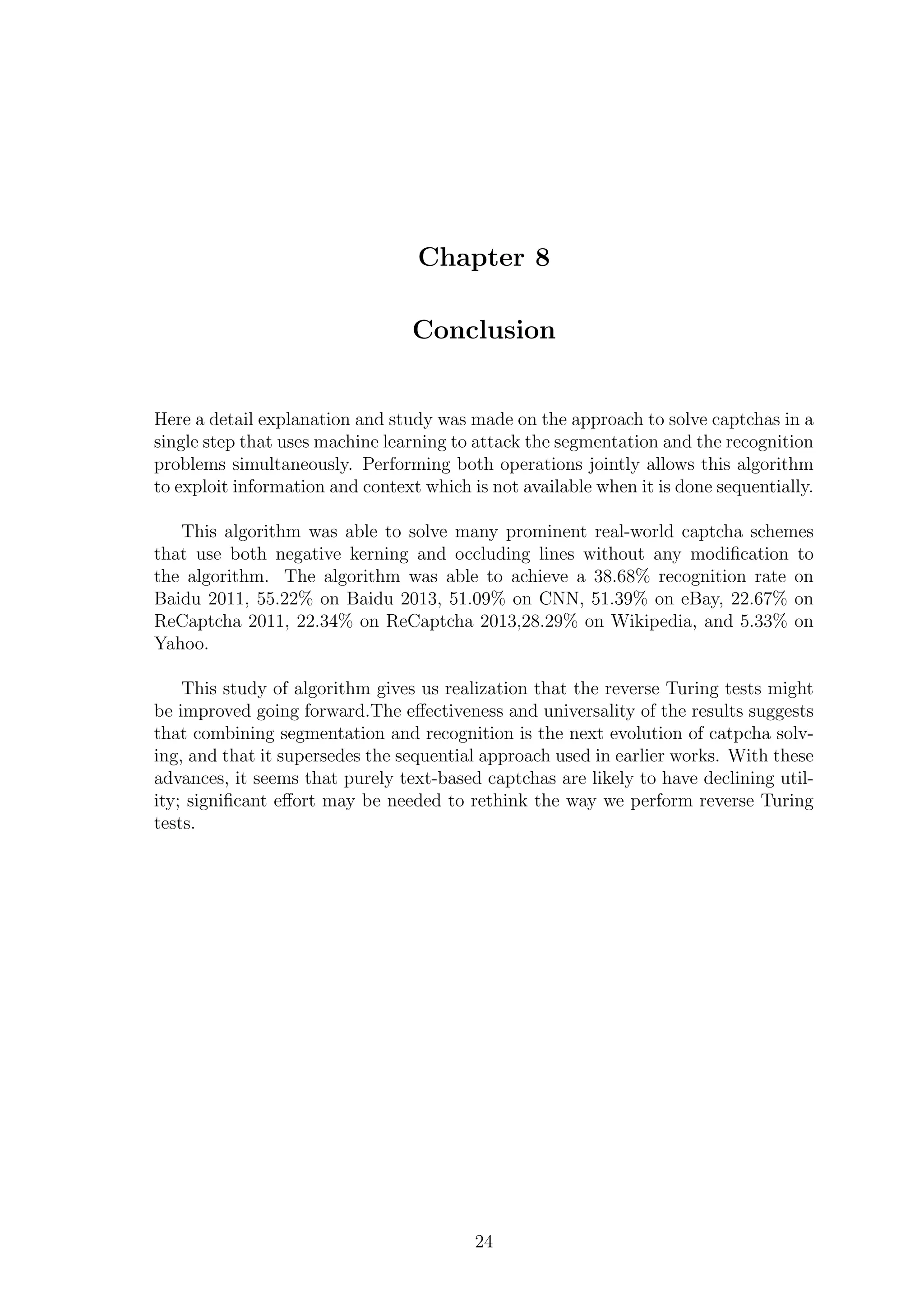
![Chapter 6
Areas of Improvement
The segmentation and recognition simultaneously approach, holistic [9] is being
formulated for the first time here. Though this algorithm produces good results, it
is just the first rough implementation.This chapter describes about the some of the
most promising directions for improvement.
6.1 Learn the KNN weights
During the algorithm it was discussed that the kNN algorithm is used to classify the
characters. The current implementation uses a single manually chosen set of weights
for the KNN distance computation that performed well on the set of captcha scheme
provided initially . It is believed that automatically learning of those weights for each
captcha scheme would improve accuracy, particularly for schemes that use unusual
fonts or specific distortions. It is believed that it is possible to accomplish this fully
unsupervised, similar to the cut-point detector and slicer phases of our algorithm.
6.2 Improve cut-point elimination
The computation time is directly related to the number of potential segments, the
first optimization was to come up with heuristics to reduce the number of cut points
considered by the cut point detector. This optimization works by pruning near-
duplicate and improbable cuts from the set of potential cut points. First, remove
all the cuts that have an angle >30. Then examine the ratio of white pixels to black
pixels to eliminate cut lines that pass through too many black pixels, since they
are most likely cutting through the middle of a letter. Finally we compared the
pixel intensities of the left and right boundaries to estimate whether the cut marks
a transition between two letters. Finding a better set of heuristics that are both
generic and more precise is an open question.
6.3 Additional Occlusion
As pointed out earlier, Baidu and CNN captcha schemes use occluding lines with low
curvature. While results on these captcha schemes are very good and ur algorithm
properly detects lines, future work should investigate in depth how various types of
19](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-23-2048.jpg)
![Generic Solving of Text-based captchas
lines, e.g., sine waves that have a high curvature, impact the recognition rate. It
should also consider other types of occlusion, e.g., blobs. To date, we have not found
real world captcha schemes that employ this type of occlusion; perhaps occlusion of
this type presents usability challenges that make it impractical for humans.
6.4 Explore deep neural networks
A primary contribution of this work is to completely demonstrate the effectiveness
of performing segmentation and recognition simultaneously. Accordingly, a consid-
eration was also made on other algorithms that are able to process captchas in a
holistic manner. In particular, with collaborators, a experiment was conducted to
experiment with deep convolution neural networks, similar to those in [17]. These
experiments have confirmed the benefits of a unified approach, and have achieved
captcha-solving results that equal or improve upon those presented in this paper.
For certain ReCaptcha data sets, these new results show such dramatic improvement
in accuracy, while using large-scale training sets, that they suggest that deep neu-
ral networks may hold a substantial advantage over humans for solving text-based
captchas [18].
Dept. of Computer Science & Engg. 20 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-24-2048.jpg)
![Chapter 7
Future Works of captcha system
With the demonstration (through research publications) that character recognition
CAPTCHAs are vulnerable to computer vision based attacks, some researchers have
proposed alternatives to character recognition, in the form of image recognition
CAPTCHAs which require users to identify simple objects in the images presented.
The argument is that object recognition is typically considered a more challenging
problem than character recognition, due to the limited domain of characters and
digits in the English alphabet. This is the reason why captcha is taken as an image
rather than a set of characters. When captchas were invented, the designers real-
ized that with the passage of time one of two things would happen: either captchas
would remain an invaluable way to differentiate humans and computers, or very high
quality OCR would become readily available.
Here the entire description was based on solving the text based captcha. And
it was found that the end of using text based captcha has approached as it is quite
simple to decode. In this algorithm by using the concept of segmentation and recog-
nition together many of the captcha were able to decode successfully. So it is direct
that in near future, by updating this algorithm one can achieve 100% decoding of
the text based captcha. Due to all such reason the need for new type of reverse
Turing test is higher.
The first potential method is simply to find a more difficult problem in computer
vision. Incorporating video or requiring the user to perform a higher order cog-
nitive task such as circling or rotating an object. Due to the failure of the text
based captcha the new captcha schemes that arrived where the audio and the video
captcha. But the audio captcha resulted into a failure as it was able to decrypted
using an output of speech to text recognizer. The video captcha can also be decoded
successfully by taking the frame pictures of the video and then analyze each frame
and decode the captcha.
Datta et al. published a paper in the ACM Multimedia ’05 Conference, named
IMAGINATION (IMAge Generation for INternet AuthenticaTION), proposing a
systematic way to image recognition captchas.According to that paper a set of im-
ages are distorted in such a way that state-of-the-art image recognition approach
will fail to recognize them. But this captcha was able to be solved with quite diffi-
culty by the humans.[20]
21](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-25-2048.jpg)
![Generic Solving of Text-based captchas
Microsoft have developed Animal Species Image Recognition for Restricting Ac-
cess (ASIRRA) which ask users to distinguish cats from dogs. Microsoft had a beta
version of this for websites to use.?? Microsoft claim ”Asirra is easy for users; it
can be solved by humans 99.6% of the time in under 30 seconds. Anecdotally, users
seemed to find the experience of using Asirra much more enjoyable than a text-based
CAPTCHA.” This solution was described in a 2007 paper to Proceedings of 14th
ACM Conference on Computer and Communications Security (CCSIts). However,
this project was closed in October 2014 and is no longer available. Asirra captcha
(Figure:7.1a), which asked users to distinguish between cats and dogs. Less than a
year after its release it was successfully broken using a classifier trained to recognize
image textures.
The MintEye captcha (Figure:7.1b) scheme was a moder version of captcha
scheme where a image is distorted and the user has to undistorted the image and
make it back as a perfect figure[6].This schema relies on undistorted an image was
broken by a very simple attack based on Sobel operators that only required 23 lines
of Python[5]. Due to this this schema was also rejected
Mitra et. al. have suggested using emergent images as an alternative way to encode
(a) Asirra captcha (b) MintEye captcha
Figure 7.1: Captcha Future.
information in video that might be robust against computer vision algorithms. A
short post on emergent images, still or moving images where objects at first only
appear with effort and concentration, but once recognized are very easy to see again
even after several months or years. In effect once a user have recognized the object
he/she remember it forever[23]. Emergence refers to the unique human ability to
aggregate information from seemingly meaningless pieces, and to perceive a whole
that is meaningful.
Recently game - based captchas have been developed[4]. However implementing
this idea as proven to be difficult, as the game captcha schemes for the leading game
captcha provider Are you a human have been broken[22]. This captcha system works
on the concept of giving the user a game to complete and reach the target goal. The
game is a simple design and only humans can solve it.However implementing this
idea as proven to be more difficult.
NuCaptcha is an early fraud detection service which utilities behavior analytics to
provision threat appropriate, animated video captcha. NuCaptcha is developed and
operated by Canadian-based firm, NuData Security. Static image-based captchas
are routinely used to prevent automated sign-ups to websites by using text or im-
Dept. of Computer Science & Engg. 22 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-26-2048.jpg)
![Generic Solving of Text-based captchas
ages of words disguised so that optical character recognition (OCR) software has
trouble reading them[10]. However, in common captcha systems, users often fail to
correctly solve the captcha 7% - 25% of the time.NuCaptcha uses animated video
technology that it claims make puzzles easier for humans to solve, but harder for
bots and hackers to decipher[24].
Cognitive Behavior : Another method, to compute whether the user is a human
or system is on the basis of the computation speed of the respective brains, i.e speed
of brain of human in solving to the ratio of the speed in solving by a computer is
relatively faster[25]. So based on this time variation in solving the captcha one can
recognize who is human and who is a system.
Leveraging reputation: In addition to considering how a reverse Turing test is
solved, captcha providers could consider the identity of the solver, for example the
IP address, the geographic location, etc. If a good enough proof of identity can be
established, providers can use this reputation to adapt the difficulty of the reverse
Turing test.
Dept. of Computer Science & Engg. 23 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-27-2048.jpg)
![Bibliography
[1] Elie Bursztein, Jonathan Aigrain, Angelika Moscicki, John C. Mitchell,”The
End is Nigh: Generic Solving of Text-based CAPTCHAs”’,2013.
[2] P. Golle. Machine learning attacks against the asirra captcha. In ACM CCS
2008, 2008.
[3] R. Gossweiler, M. Kamvar, and S. Baluja. Whats up captcha? a captcha based
on image orientation. In World Wide Web, 2009.
[4] Are you human ? http://areyouahuman.com/.
[5] Breaking the minteye image captcha in 23 lines of python. Blog post
http://www.jwandrews.co.uk/2013/01/breakingthe-minteye-image-%captcha-
in-23-lines-of-python.
[6] Minteye captcha. website: http://www.minteye.com/, 2013.
[7] A. S. E. Ahmad, J. Yan, and M. Tayara. The robustness%of google captchas.
Technical report, Newcastle University, 2011.
[8] E. Athanasopoulos and S. Antonatos. Enhanced captchas: Using animation
to tell humans and computers apart. In IFIP International Federation for
Information Processing, 2006.
[9] P. Baecher, N. Buscher, M. Fischlin, and B. Milde. Breaking recaptcha: A
holistic approach via shape recognition. In Future Challenges in Security and
Privacy for Academia and Industry, pages 5667. Springer, 2011.
[10] E. Bursztein. How we broke the nucaptcha video scheme and what we propose
to fix it. blog post http://elie.im/blog/security/howwe-broke-the-nucaptcha-
videoscheme-%and-what-we-propose-tofix- it/, February 2012.
25](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-29-2048.jpg)
![Generic Solving of Text-based captchas
[11] E. Bursztein, R. Bauxis, H. Paskov, D. Perito, C. Fabry, and J. C. Mitchell.
The failure of noisebased non-continuous audio captchas. In Security and
Privacy, 2011.
[12] E. Bursztein and S. Bethard. Decaptcha: breaking 75% of eBay audio
CAPTCHAs. In Proceedings of the 3rd USENIX conference on Offensive
technologies, page 8. USENIX Association, 2009.
[13] E. Bursztein, M. Martin, and J. Mitchell. Text-based captcha strengths and
weaknesses. In Proceedings of the 18th ACM conference on Computer and
communications security, CCS 11, pages 125138, New York, NY, USA, 2011.
ACM.
[14] E. Bursztein, A. Moscicki, C. Fabry, S. Bethard, D. Jurafsky, and J. C.
Mitchell. Easy does it: More usable captchas. CHI, 2014.
[15] K. Chellapilla, K. Larson, P. Simard, and M. Czerwinski. Computers beat
humans at single character recognition in reading based human interaction
proofs (hips). In CEAS, 2005.
[16] K. Chellapilla and P. Simard. Using machine learning to break visual human
interaction proofs (HIPs). Advances in Neural Information Processing
[17] Systems, 17, 2004. Q. V. Le, M. Ranzato, R. Monga, M. Devin, K. Chen, G. S.
Corrado, J. Dean, and A. Y. Ng. Building high-level features using large scale
unsupervised learning. In ICML, 2011.
[18] I. J. Goodfellow, Y. Bulatov, J. Ibarz, S. Arnoud, and V. Shet. Multi-digit
number recognition from street view imagery using deep convolution neural
networks. arXiv preprint arXiv:1312.6082, 2013.
[19] J. Yan and A. El Ahmad. A Low-cost Attack on a Microsoft CAPTCHA. In
Proceedings of the 15th ACM conference on Computer and communications
security, pages 543554. ACM, 2008.
[20] ”Imagination Paper”. Infolab.stanford.edu. Retrieved 2013-09-28.
[21] ”Asirra is a human interactive proof that asks users to identify photos of cats
and dogs”.
Dept. of Computer Science & Engg. 26 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-30-2048.jpg)
![Generic Solving of Text-based captchas
[22] Spamtech. Cracking the areyouahuman captcha.
http://spamtech.co.uk/software/bots/cracking-the-
areyouhumancaptcha/,2012.
[23] N. J. Mitra, H.-K. Chu, T.-Y. Lee, L.Wolf, H. Yeshurun, and D. Cohen-Or.
Emerging images. ACM Transactions on Graphics, 28(5), 2009. to appear.
[24] Y. Xu, G. Reynaga, S. Chiasson, J.-M. Frahm, F. Monrose, and P. van
Oorschot. Security and usability challenges of moving-object captchas: Decod-
ing codewords in motion. In Usenix Security, 2012.
[25] C. Cruz-Perez, O. Starostenko, F. Uceda-Ponga, V. Alarcon-Aquino, and L.
Reyes-Cabrera. Breaking recaptchas with unpredictable collapse: heuristic
character segmentation and recognition. In Pattern Recognition, pages 155165.
Springer, 2012.
[26] C. Cortes and V. Vapnik. Support-vector networks. Machine learn-
ing,Septmenber 2014.
[27] Opitz, D.; Maclin, R. (1999). ”Popular ensemble methods: An empirical
study”. Journal of Artificial Intelligence Research 2014.
[28] Sutton, Richard S. (1984). Temporal Credit Assignment in Reinforcement
Learning (PhD thesis). University of Massachusetts, Amherst, MA.
[29] Altman, N. S. (1992). ”An introduction to kernel and nearest-neighbor
nonparametric regression”. The American Statistician 46, September 2014
[30] Pearl, Judea (1983). Heuristics: Intelligent Search Strategies for Computer
Problem Solving. New York, Addison-Wesley, December 2014.
[31] http://www.encyclopediaofmath.org/index.php/Point of inflection, Jan-
uary,2015.
[32] Barghout, Lauren, and Lawrence W. Lee. ”Perceptual information processing
system.” Paravue Inc. U.S. Patent Application 10/618,543, filed July 11, 2014.
Dept. of Computer Science & Engg. 27 SIMAT, Vavanoor](https://image.slidesharecdn.com/slideshare-150122081110-conversion-gate02/75/Generic-Solving-Of-Text-Based-Captcha-31-2048.jpg)