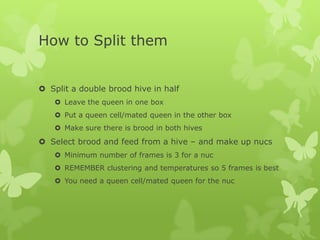
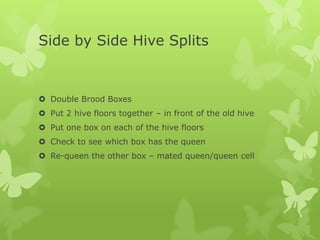
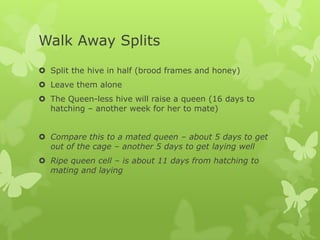
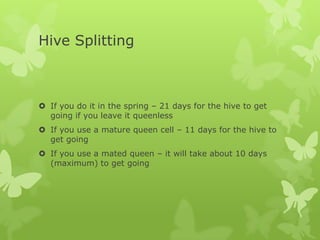
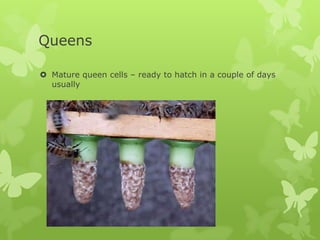
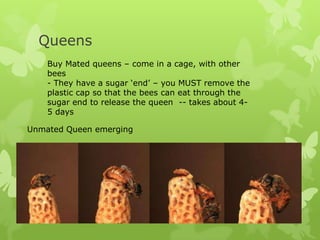
The document discusses the processes of bee swarming and hive splitting, emphasizing the types of swarms, methods for catching them, and considerations for successful hive splits. It outlines important factors such as swarm size and location, the timing of splits, and the necessity of ensuring both new hives thrive with adequate food and healthy brood. The document also highlights safety measures and the use of bait hives for managing swarms.