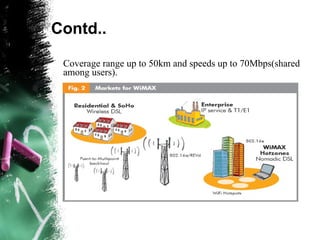
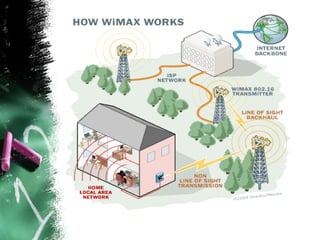
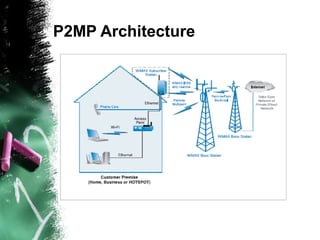
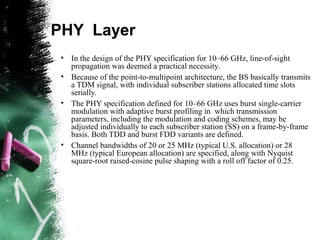
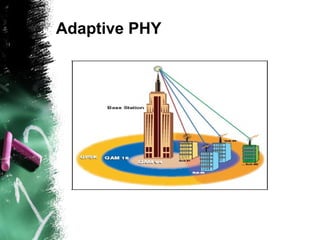
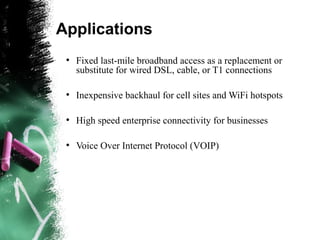
WiMAX is a wireless technology that can provide broadband access over long distances. It uses wireless transmission in the 2-11 GHz range to connect users to a base station up to 50 km away. From the base station, users can access the internet and other public networks at speeds up to 70 Mbps shared among users. WiMAX allows both line-of-sight and non-line-of-sight connections using adaptive burst profiles. It has the potential to provide high-speed wireless internet access to areas not reached by cables and DSL.