Embed presentation
Downloaded 12 times





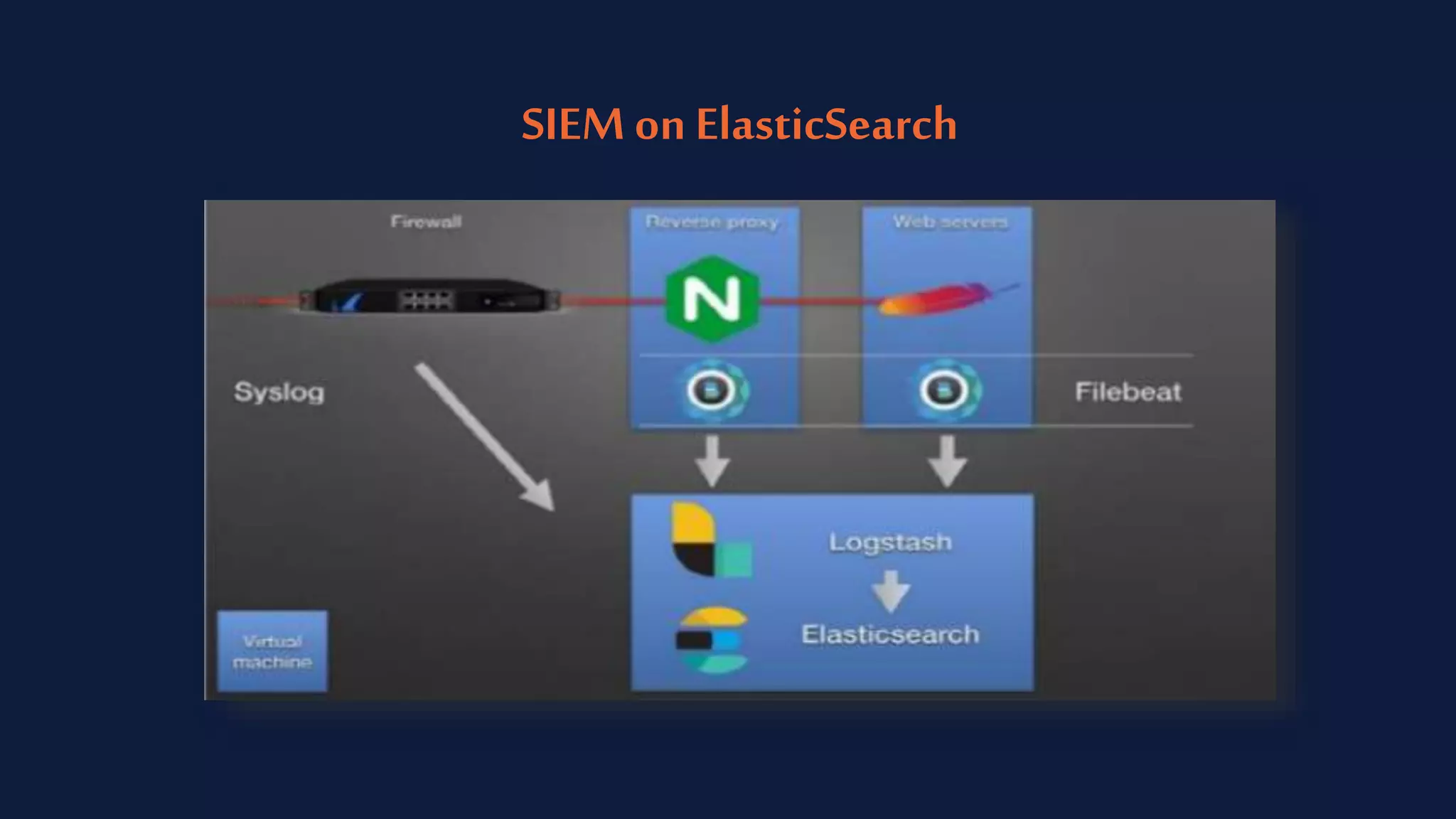

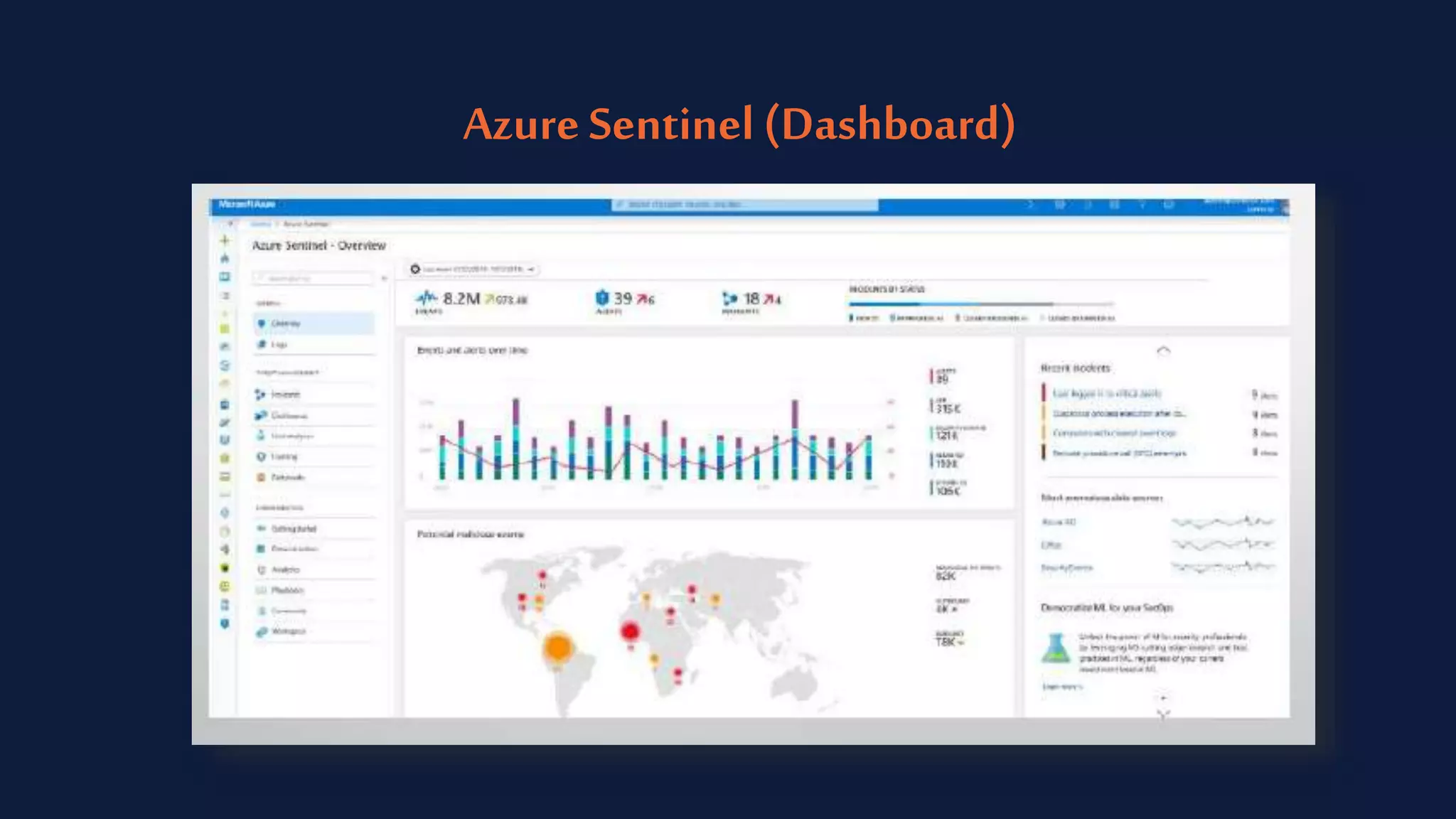

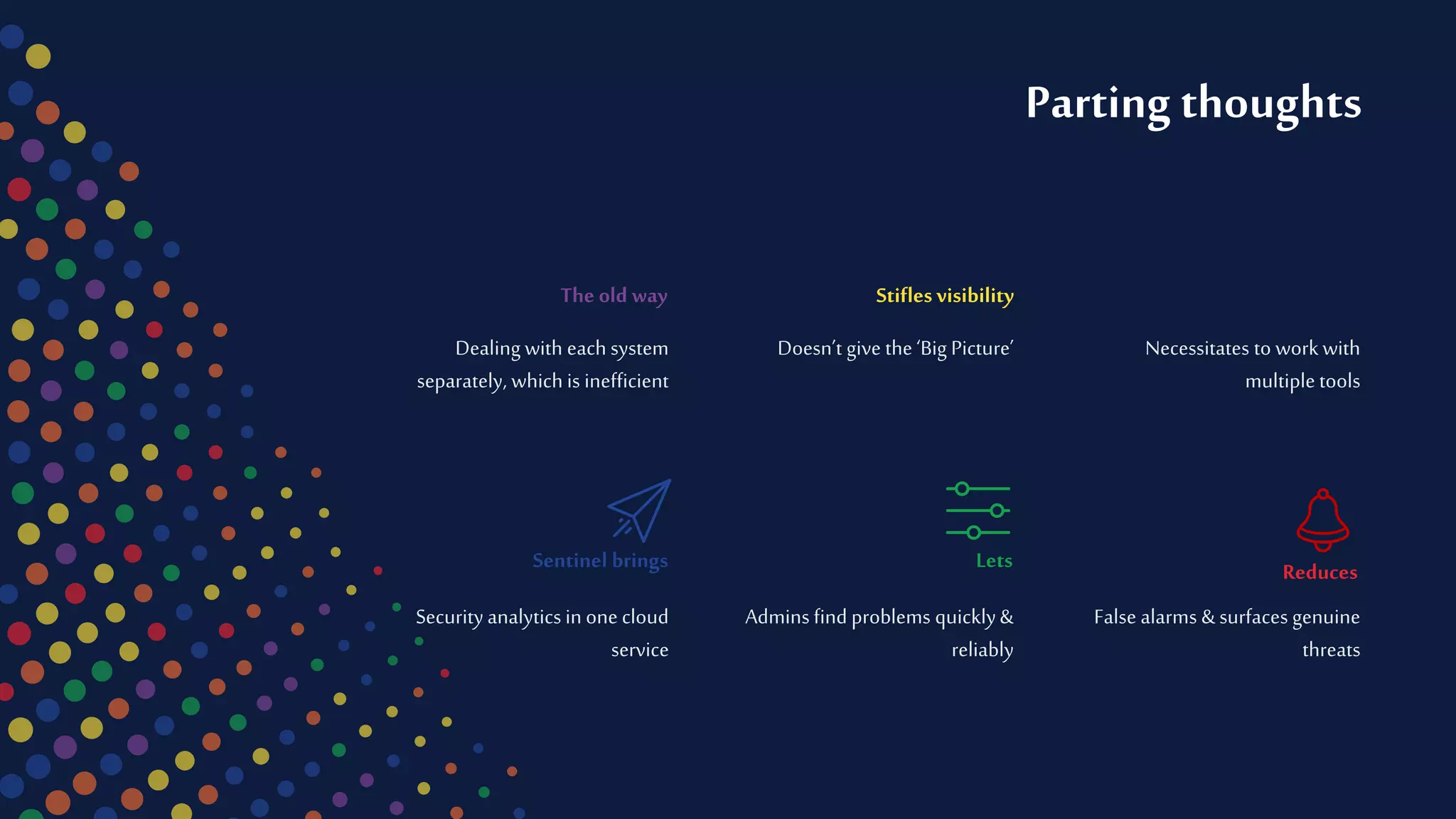


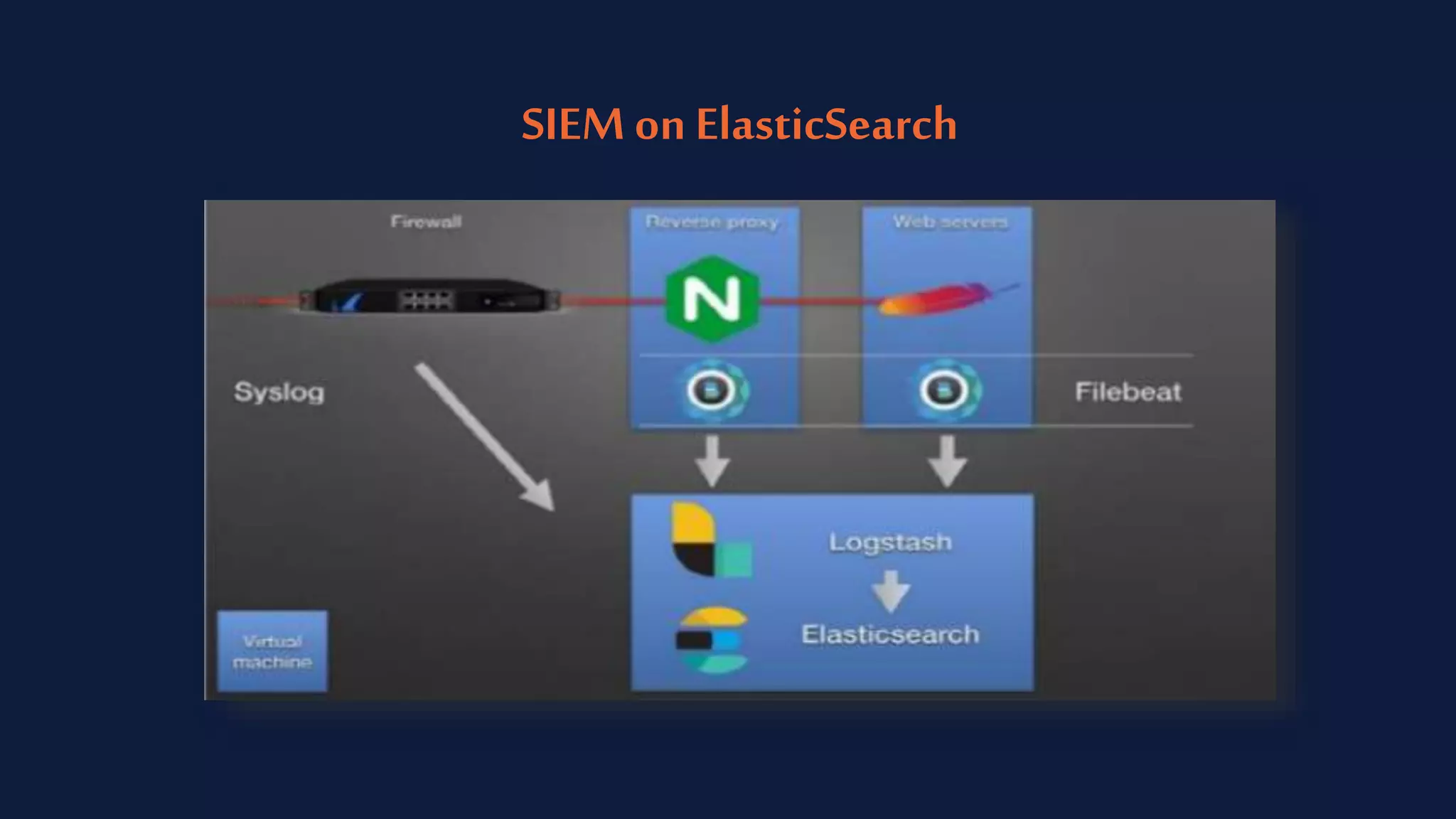
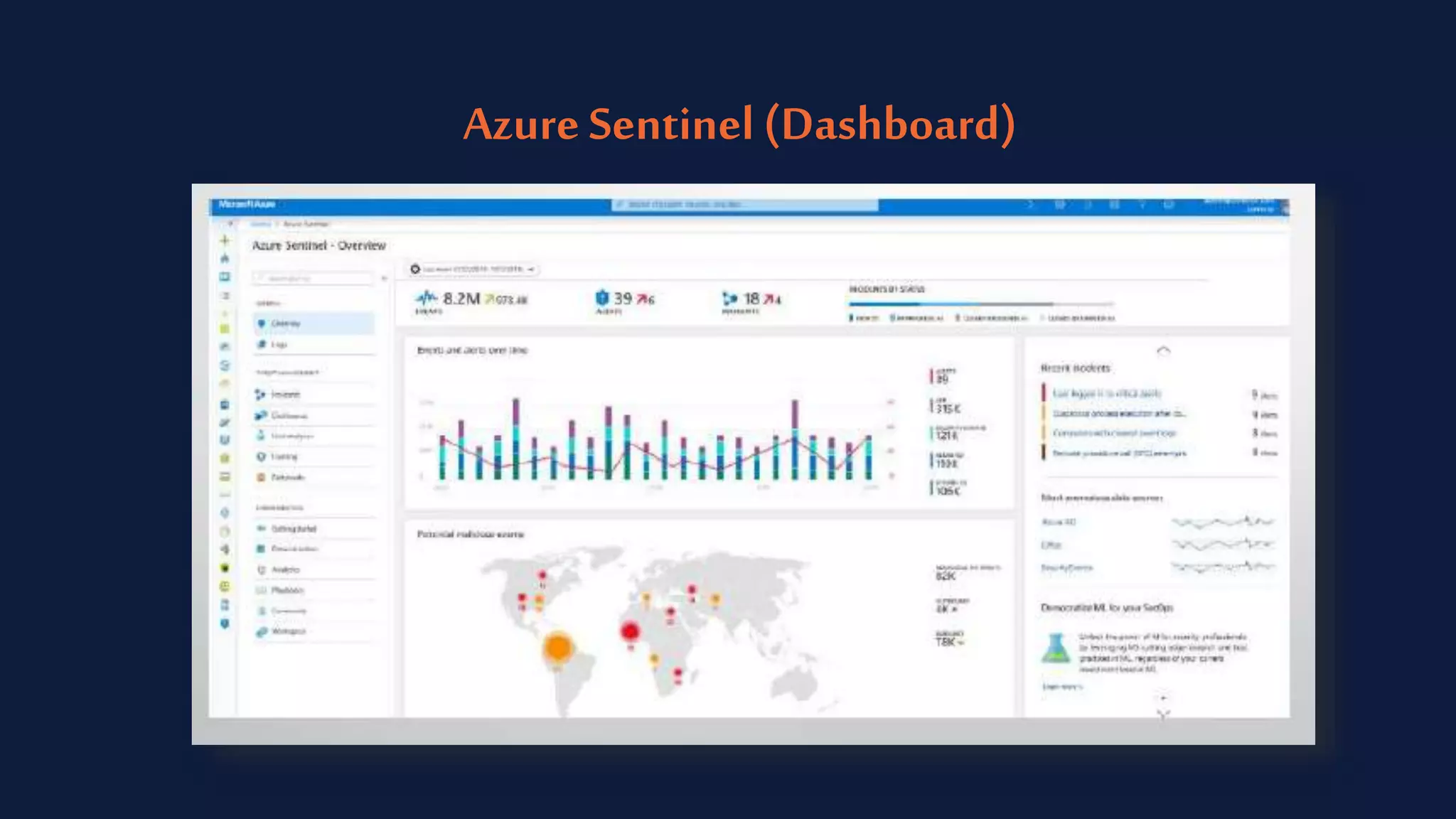
Azure Sentinel is a cloud-native SIEM tool within Microsoft Azure that leverages AI and security analytics to enhance threat detection and response across organizational networks. It integrates data from various sources but faces challenges with false alarms and the need for efficient incident management. The tool is designed to improve visibility and streamline security operations while remaining compliant with security and governance processes.