Embed presentation
Downloaded 17 times




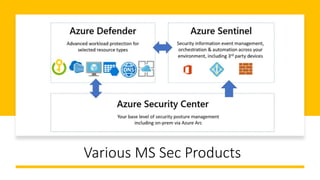
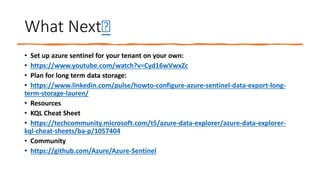
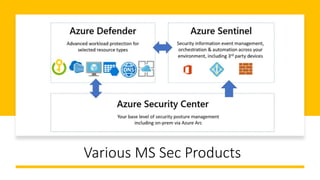
The document provides an overview of Azure Sentinel, a cloud-native SIEM solution, emphasizing its advantages for security operations within an expanding digital estate. It outlines key functionalities such as data collection, anomaly detection, investigation, and response. Additionally, it includes resources for self-setup, long-term data storage planning, and community support links.