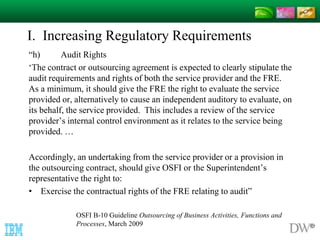
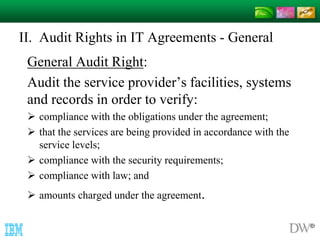
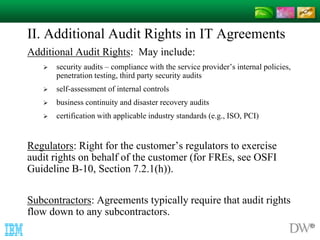
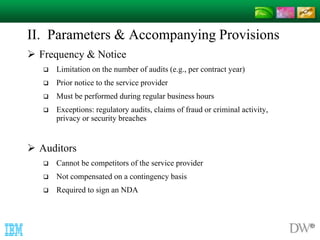
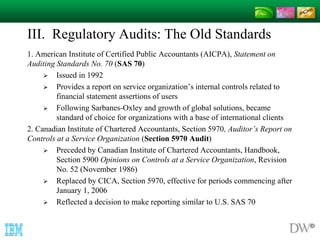
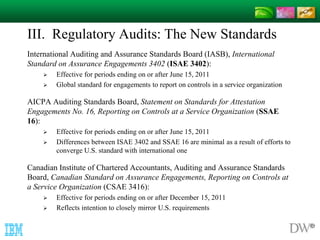
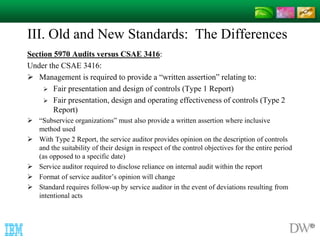
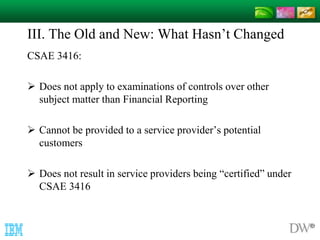
The document discusses audit rights in IT agreements, emphasizing their importance due to growth in the IT outsourcing industry and increasing regulatory requirements. It outlines the rights of both service providers and customers regarding audits, detailing specific types of audits, parameters for conducting audits, as well as implications for cloud computing. The document also reviews changes in auditing standards, highlighting the evolution from previous standards to current practices, including the global convergence towards new auditing frameworks.