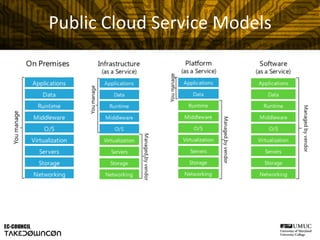
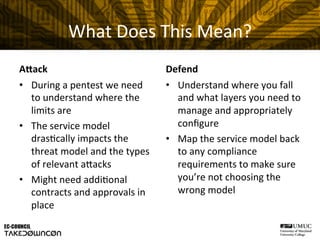
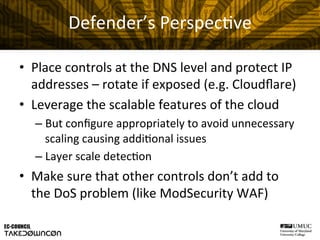
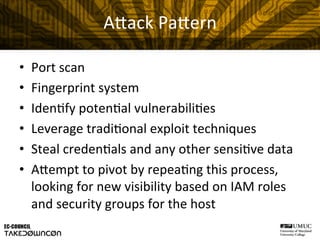
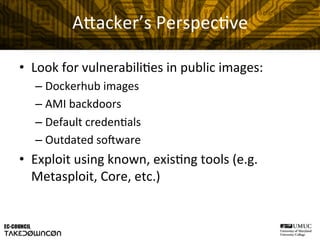
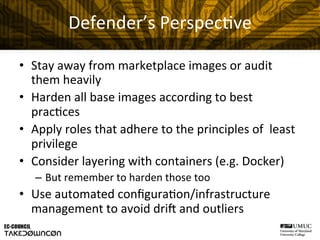
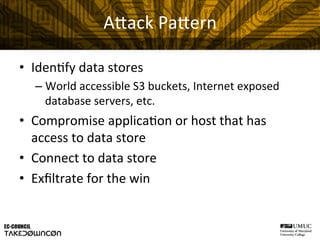
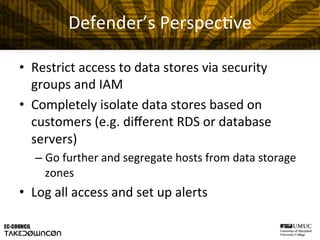
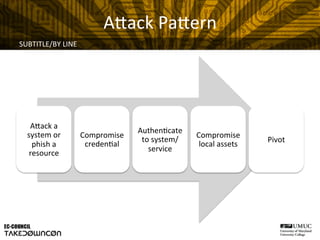
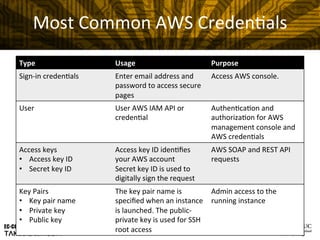
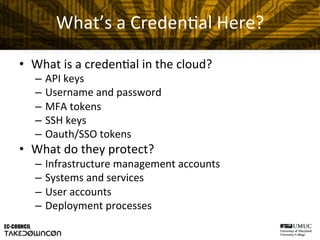
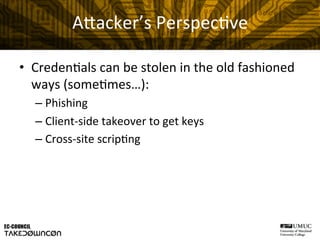
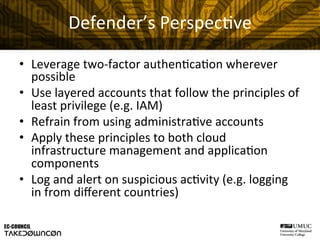
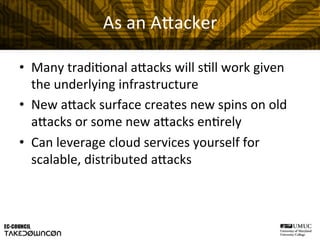
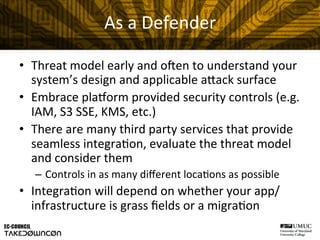
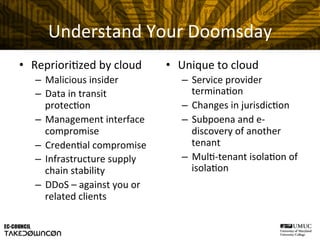
This document discusses attack and defense considerations in the public cloud. It begins with an introduction of the speaker and an overview of shared responsibility models in the cloud. It then explores specific attack scenarios like denial of service attacks, host takeovers, data exfiltration, and credential theft. For each attack, it describes the attacker's perspective and techniques as well as recommendations for defenders. The goal is to help both attackers and defenders understand security challenges in the public cloud.