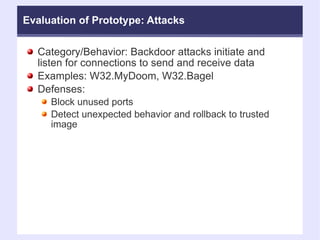
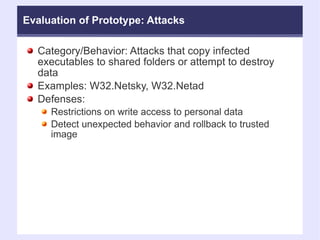
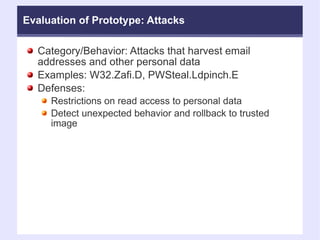
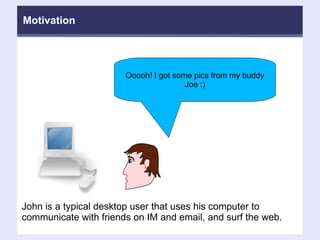
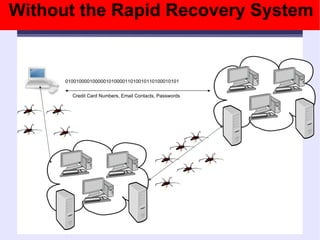
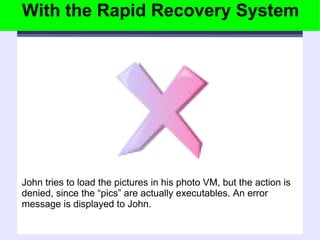
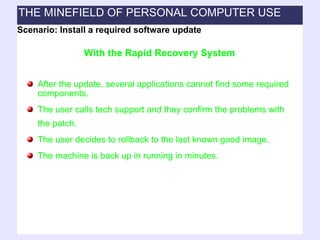
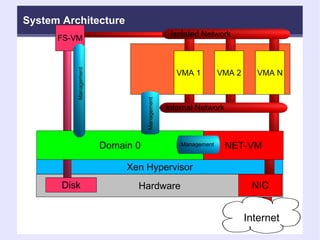
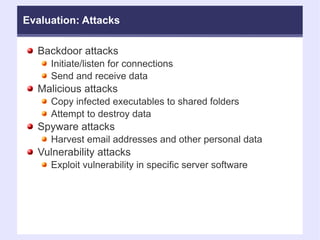
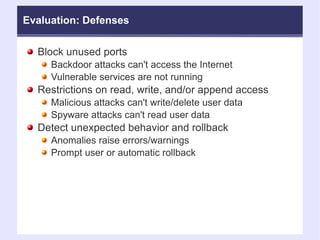
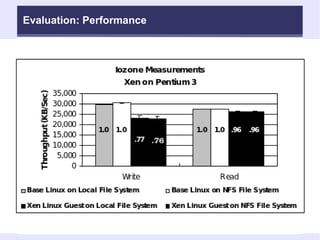
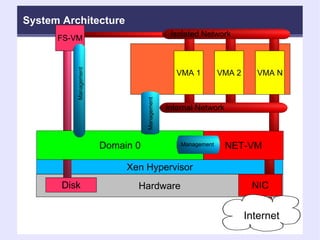
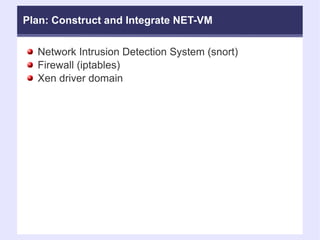
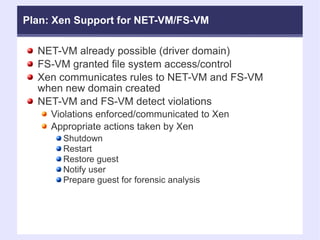
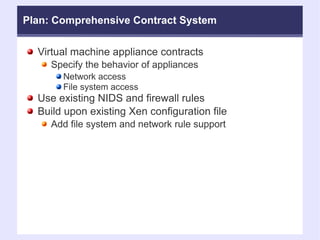
The document discusses the motivation, goals, background, architecture, evaluation plan, and plan of work for a system called the Rapid Recovery System that aims to provide strong protection of user data and rapid recovery from attacks through the use of virtual machine isolation and rollback capabilities. The system would isolate user data and applications into separate virtual machines with strict access controls to prevent malware from compromising data or taking control of the system, and allow quick restoration to previous known-good states. Evaluation of the system would assess its effectiveness against various attack scenarios, performance overhead, and ability to facilitate forensic analysis after attacks.
!["Very sophisticated tools are commercially available in black markets... This has made [the Internet] more attractive for organized crime: [criminals] no longer have to be geeks." - James Lewis "Although security awareness continues to improve, hackers and malicious code authors are releasing threats faster than ever before, with approximately 200 per cent more malicious threats per day than two years ago." - Stuart McClure (2006) "Over one third [of IT Companies] were hit by a denial-of-service attack while over 44 percent had experienced either a pharming or cache poisoning attack." - 2007 Secure64 Survey Motivation](https://image.slidesharecdn.com/atc-nyfridaytalk20080808-110828224445-phpapp02/85/Atc-ny-friday-talk_20080808-5-320.jpg)

![Plan: File System Rule Language # Example file system rule set for an email client. fs_rule = [ 'id=1, read, 1024, 5' ] # read at most 1024 bytes of data in 5 seconds fs_rule = [ 'id=2, append, 1024, 3' ] # append at most 1024 bytes of data in 3 seconds. fs_rule = [ 'id=3, write, 320, 3' ] # write at most 320 bytes in 3 seconds # The email mount point is accessible to the email client, and fs_rules # with id=1 and id=2 are applied disk = [ 'fsvm:/mnt/email, /home/user/mail,fs_rule=1:2' ] # The email mount point is accessible to the email client, and fs_rules # with id=1 and id=3 are applied. disk = [ 'fsvm:/mnt/email, /home/user/attachments,fs_rule=1:3' ]](https://image.slidesharecdn.com/atc-nyfridaytalk20080808-110828224445-phpapp02/85/Atc-ny-friday-talk_20080808-47-320.jpg)
![Plan: Network Rule Language #Email client example continued network_rule = ['id=1, iptables, file=/etc/iptables/email_client'] network_rule = ['id=2, snort, file=/etc/snort/rules/email_client'] vif = [ 'rate=2Mb/s, network_rule=1:2' ]](https://image.slidesharecdn.com/atc-nyfridaytalk20080808-110828224445-phpapp02/85/Atc-ny-friday-talk_20080808-48-320.jpg)