ApplicationPro Flyer English
•
0 likes•198 views
ApplicationPro blocks unwanted applications and prevents the use of unlicensed software. Further details: http://cynapspro.com/US/products/applicationpro
Report
Share
Report
Share
Download to read offline
Recommended
CryptionPro Hdd Flyer English

CryptionPro HDD® protects confidential data through automatic and efficient hdd encryption.
Further details: http://cynapspro.com/US/products/cryptionpro-hdd
PowerPro Flyer English

More security at no additional cost? PowerPro cuts energy costs and reports suspicious activity.
Further Details: http://cynapspro.com/US/products/powerpro
Icomm agentless-architecture

Agentless Backup is Not a Myth.
The Asigra solution requires no agents, which inherently makes it easier to install and
support than other backup and recovery solutions.
Backup and recovery software typically requires agents that are installed onto the servers
that a system administrator wants to back up. Even in a modest-sized environment,
agent management can become extremely complex when an administrator is forced to
deal with different operating systems and revision levels. The complexity of agent management
is further complicated by the growing number of applications that also require
agents running on the same servers. This proliferation of agents and its associated drain
on CPU resources is often referred to as “agent pollution”.
Norman Patch and Remediation

Norman Patch and
Remediation Advanced
provides:
• Rapid, accurate and secure
patch management
• Automated collection, analysis
and delivery of patches
• Security for your organization
from worms, trojans, viruses and other malicious threats
• Single consolidated solution
for heterogeneous environments
provides effective management
at a significantly reduced TCO
Techarex networks introduces disaster recovery as a service (draas) in united...

Techarex Networks Launches Disaster Recovery as a Service (DRAAS) in United States.
Microsoft System center Configuration manager 2012 sp1

Microsoft System center Configuration manager 2012 sp1
Recommended
CryptionPro Hdd Flyer English

CryptionPro HDD® protects confidential data through automatic and efficient hdd encryption.
Further details: http://cynapspro.com/US/products/cryptionpro-hdd
PowerPro Flyer English

More security at no additional cost? PowerPro cuts energy costs and reports suspicious activity.
Further Details: http://cynapspro.com/US/products/powerpro
Icomm agentless-architecture

Agentless Backup is Not a Myth.
The Asigra solution requires no agents, which inherently makes it easier to install and
support than other backup and recovery solutions.
Backup and recovery software typically requires agents that are installed onto the servers
that a system administrator wants to back up. Even in a modest-sized environment,
agent management can become extremely complex when an administrator is forced to
deal with different operating systems and revision levels. The complexity of agent management
is further complicated by the growing number of applications that also require
agents running on the same servers. This proliferation of agents and its associated drain
on CPU resources is often referred to as “agent pollution”.
Norman Patch and Remediation

Norman Patch and
Remediation Advanced
provides:
• Rapid, accurate and secure
patch management
• Automated collection, analysis
and delivery of patches
• Security for your organization
from worms, trojans, viruses and other malicious threats
• Single consolidated solution
for heterogeneous environments
provides effective management
at a significantly reduced TCO
Techarex networks introduces disaster recovery as a service (draas) in united...

Techarex Networks Launches Disaster Recovery as a Service (DRAAS) in United States.
Microsoft System center Configuration manager 2012 sp1

Microsoft System center Configuration manager 2012 sp1
NIC2012 - System Center Endpoint Protection 2012

System Center Endpoint Protection 2012 slides from presentation at NIC2012 13-14.Jan 2012 in Oslo
Microsoft System Center Configuration Manager 2012 R2 Installation

And here is the file I have distributed to my friends of net-workers. This PDF file explains the installation of Active Directory, SQL Server 2008, SQL Server 2012 and finally the step by step installation of the System Center Configuration Manager 2012 R2. This document also describes the prerequisite configuration required for the successful completion of installation of SCCM 2012 R2.
NIST Definition of Cloud Computing

Recommendations of the National Institute
of Standards and Technology
CENTRALIZED MANAGEMENT APPLIANCES

CMX100 centralized management appliances allow customers
to monitor and manage up to 100 Array Networks APV or AG
appliances to reduce the time and cost of IT administration.
DATA STORAGE REPLICATION aCelera and WAN Series Solution Brief

aCelera and WAN Series WAN Optimization Controllers: Accelerating storage backup, replication and recovery over the WAN, efficiently and cost-effectively.
Application Virtualization presentation

Discusses a technique in virtualization called application level virtualization.
What is My easy center 2.0 for SCCM ?

Over the several years of experience on the Microsoft product SCCM, Easy Center Corp leveraged this expertise by focusing in the development of My Easy Center software. A new console to administer, easily and securely, the computer management key tool of Microsoft.
SCOM: The Unsung Hero of the System Center Suite April 24, 2013

System Center Operations Manager is a big deal.
On April 24th, Erik Gilreath discussed SCOM and uncovered: why SCOM is so rarely installed, why that's a mistake, easy steps to install, what you should be doing with it, and what it can do that other people's products can't.
System Center Configuration Manager-The Most Popular System Center Component 

System Center Configuration Manager-The Most Popular System Center Component C/D/H Technology Consultants
RTE_Extremadura

Historia reciente de la Implantación de las TIC en la Comunidad Autónoma de Extremadura
More Related Content
What's hot
NIC2012 - System Center Endpoint Protection 2012

System Center Endpoint Protection 2012 slides from presentation at NIC2012 13-14.Jan 2012 in Oslo
Microsoft System Center Configuration Manager 2012 R2 Installation

And here is the file I have distributed to my friends of net-workers. This PDF file explains the installation of Active Directory, SQL Server 2008, SQL Server 2012 and finally the step by step installation of the System Center Configuration Manager 2012 R2. This document also describes the prerequisite configuration required for the successful completion of installation of SCCM 2012 R2.
NIST Definition of Cloud Computing

Recommendations of the National Institute
of Standards and Technology
CENTRALIZED MANAGEMENT APPLIANCES

CMX100 centralized management appliances allow customers
to monitor and manage up to 100 Array Networks APV or AG
appliances to reduce the time and cost of IT administration.
DATA STORAGE REPLICATION aCelera and WAN Series Solution Brief

aCelera and WAN Series WAN Optimization Controllers: Accelerating storage backup, replication and recovery over the WAN, efficiently and cost-effectively.
Application Virtualization presentation

Discusses a technique in virtualization called application level virtualization.
What is My easy center 2.0 for SCCM ?

Over the several years of experience on the Microsoft product SCCM, Easy Center Corp leveraged this expertise by focusing in the development of My Easy Center software. A new console to administer, easily and securely, the computer management key tool of Microsoft.
SCOM: The Unsung Hero of the System Center Suite April 24, 2013

System Center Operations Manager is a big deal.
On April 24th, Erik Gilreath discussed SCOM and uncovered: why SCOM is so rarely installed, why that's a mistake, easy steps to install, what you should be doing with it, and what it can do that other people's products can't.
System Center Configuration Manager-The Most Popular System Center Component 

System Center Configuration Manager-The Most Popular System Center Component C/D/H Technology Consultants
What's hot (20)
Microsoft System Center Configuration Manager 2012 R2 Installation

Microsoft System Center Configuration Manager 2012 R2 Installation
DATA STORAGE REPLICATION aCelera and WAN Series Solution Brief

DATA STORAGE REPLICATION aCelera and WAN Series Solution Brief
Riding the wave towards customer centricity aziz amirali 3_p

Riding the wave towards customer centricity aziz amirali 3_p
SCOM: The Unsung Hero of the System Center Suite April 24, 2013

SCOM: The Unsung Hero of the System Center Suite April 24, 2013
System Center Configuration Manager-The Most Popular System Center Component 

System Center Configuration Manager-The Most Popular System Center Component
Viewers also liked
RTE_Extremadura

Historia reciente de la Implantación de las TIC en la Comunidad Autónoma de Extremadura
Trabajo digital en la plataforma HELVIA con DESCARTES, EDA 2007

Ponencia de José Luis
Alcón Camas (IES Las Aguas, Sevilla) y José Manuel Huertas Fernández (IES
Gonzalo Nazareno, Dos Hermanas, Sevilla), durante el XII Congreso de Enseñanza y Aprendizaje de las Matemáticas, celebrado en Sevilla del 10 al 13 de octubre de 2008, y organizado por la SAEM Thales.
Tarjetas digitales 2.0

Flavors.me y About.me son ejemplos de tarjetas de presentación digital. Una excelente forma de darse a conocer en el ciberespacio.
Viewers also liked (20)
Trabajo digital en la plataforma HELVIA con DESCARTES, EDA 2007

Trabajo digital en la plataforma HELVIA con DESCARTES, EDA 2007
que realiza el personal cuando entra un paciente al hospital

que realiza el personal cuando entra un paciente al hospital
Conceptos generales de las ecuaciones difernciales de primer grado

Conceptos generales de las ecuaciones difernciales de primer grado
Similar to ApplicationPro Flyer English
DevicePro Flyer English

DevicePro® prevents the loss of data through open ports and external storage media.
Further Details: http://cynapspro.com/US/products/devicepro
HMI/SCADA 리스크 감소

HMI/SCADA 리스크 감소
돌발적인 가동중지를 최소화하고 조직을 보호할 수 있는 핵심 단계
Decrease your HMI/SCADA risk
Key steps to minimize unplanned downtime and protect your organization
Ten questions to ask before choosing SCADA software

http://www.trihedral.com - When creating SCADA specifications, engineering firms must focus on meeting the immediate start-up and operational requirements of the SCADA system. This often means specifying products with which they are familiar. The engineer wants to ensure that the new system meets all start-up requirements at a reasonable price. It is often difficult to look past the immediate project and consider long range plans, cost of system maintenance, and keeping your SCADA application current with evolving technology. The following questions may help you ensure that these decisions will optimize your long-term SCADA strategy.
Comparison Review Forticlient x Kaspersky.pdf

See this side-by-side comparison of FortiClient vs. Kaspersky Endpoint Security for Business based on preference data from user reviews. FortiClient rates 4.4/5 stars with 200 reviews. By contrast, Kaspersky Endpoint Security for Business rates 4.3/5 stars with 183 reviews. Each product's score is calculated with real-time data from verified user reviews, to help you make the best choice between these two options, and decide which one is best for your business needs.
CIS Control Solution Guide 

This guide was developed by TBL Network’s team of engineers and partners with the understanding that there are many ways to solve for the CIS controls. Our team has thoughtfully mapped solutions that work together to meet the controls.
Webinar NETGEAR - Come Netgear può aiutare a mitigare gli effetti del Ransomware

Cosa è e come agisce il Ransomware, le azioni da intrapprendere e cosa Netgear può favorire la mitigazione della minaccia. Snapshot istantanee illimitate a livello blocco dati e ReadyRecover, la soluzione di backup appliance per ottenere full backup ogni 15 minuti di ogni sistema windows in Azienda.
Anti Key Logging And Real Time Encryption Software

Anti Key Logging and Real Time Encryption software for protection of computers from hacking by key recording software. See More At: http://www.greymatterindia.com/software-for-real-time-encryption-and-anti-key-logging
AV-Comparatives’ 2017 business software review

The review looks at security products for business Windows endpoints, focusing the following:
- EDR features
- Management Console
- Windows client (desktop and server) protection software
What is Application & Server Virtualisation

Application virtualisation, specifically, is about encapsulating software programs from the underlying operating system on which they operate. Virtualised applications are not installed as such. They are tricked into thinking they are directly connected to an OS in the traditional sense. A “virtualisation layer” is installed in the operating system to intercept all
HOW-CLOUD-IMPLEMENTATION-CAN-ENSURE-MAXIMUM-ROI.pdf

The evolution of cloud technology has helped many laboratories to increase their productivity and reliability by digitalising and automating their operations. Digitalising here means easily migrating their data saved in the form of old paper notebooks and spreadsheets to computerized storage and management systems.
BMC - Response to the SolarWinds Breach/Malware

BMC response to the SolarWinds Breach
Critical compromise to the Solarwinds Orion platform has created an immediate need to respond to the threat from a likely state sponsored actor (Russia)
Similar to ApplicationPro Flyer English (20)
Ten questions to ask before choosing SCADA software

Ten questions to ask before choosing SCADA software
Webinar NETGEAR - Come Netgear può aiutare a mitigare gli effetti del Ransomware

Webinar NETGEAR - Come Netgear può aiutare a mitigare gli effetti del Ransomware
Anti Key Logging And Real Time Encryption Software

Anti Key Logging And Real Time Encryption Software
HOW-CLOUD-IMPLEMENTATION-CAN-ENSURE-MAXIMUM-ROI.pdf

HOW-CLOUD-IMPLEMENTATION-CAN-ENSURE-MAXIMUM-ROI.pdf
More from cynapspro GmbH
Cynapspro Endpoint Data Protection 2011 - Step By Step Anleitung DevicePro un...

Dieses Dokument soll Ihnen eine Schritt für Schritt Unterstützung zur Erstinstallation und Inbetriebnahme der cynapspro Endpoint Data Protection bieten. Sie erhalten die Möglichkeit in kürzester Zeit eine Vielzahl an Funktionen dieser Endpoint Protection Lösung kennenzulernen und einzurichten.
Die Lösungen ApplicationPro, CryptionPro, CryptionPro HDD, DevicePro, ErasePro und PowerPro bieten weit mehr Funktionen als in dieser Step-By-Step Anleitung erwähnt. Jedoch sind viele Funktionen optional und werden daher im Bedienungsleitfaden (http://handbuch.cynapspro.com) oder Installationsleitfaden (http://installation.cynapspro.com) genauer erläutert.
Ziel dieses Dokumentes ist Ihnen eine Art Best Practices Guide bzw. ein How-To zu bieten.
Cynapspro endpoint data protection 2011 step by-step anleitung device pro und...

Dieses Dokument soll Ihnen eine Schritt für Schritt Unterstützung zur Erstinstallation und Inbetriebnahme der cynapspro Endpoint Data Protection bieten. Sie erhalten die Möglichkeit in kürzester Zeit eine Vielzahl an Funktionen dieser Endpoint Protection Lösung kennenzulernen und einzurichten.
Die Lösungen ApplicationPro, CryptionPro, CryptionPro HDD, DevicePro, ErasePro und PowerPro bieten weit mehr Funktionen als in dieser Step-By-Step Anleitung erwähnt. Jedoch sind viele Funktionen optional und werden daher im Bedienungsleitfaden (http://handbuch.cynapspro.com) oder Installationsleitfaden (http://installation.cynapspro.com) genauer erläutert.
Ziel dieses Dokumentes ist Ihnen eine Art Best Practices Guide bzw. ein How-To zu bieten.
cynapspro endpoint data protection 2010 - technical specifications

Technical datasheet of the cynapspro endpoint data protection 2010. Includes DevicePro, CryptionPro, CryptionPro HDD, ApplicationPro, ErasePro, PowerPro
cynapspro endpoint data protection - user guide

User Guide of cynapspro Endpoint Data Protection 2010
cynapspro endpoint data protection - installation guide

Installation Guide of cynapspro Endpoint Data Protection 2010
cynapspro endpoint data protection 2010 - Bedienungsleitfaden

Handbuch der cynapspro Endpoint Data Protection. Erläuterungen zu DevicePro, CryptionPro, CryptionPro HDD, ErasePro, PowerPro und ApplicationPro.
Weitere Informationen über die cynapspro Endpoint Data Protection 2010 finden Sie unter http://cynapspro.com/DE/
Cynapspro data endpoint protection - Anbindung von Drittsysteme

Leitfaden zur XML-Verwaltungsschnittstelle von Fremdsystemen der cynapspro Endpoint Data Protection 2010.
Weitere Informationen über die cynapspro Endpoint Data Protection 2010 finden Sie unter http://cynapspro.com/DE/
cynapspro data endpoint protection 2010 - Installationsleitfaden

Installationsleitfaden der intuitiven und effizienten cynapspro Data Endpoint Protection 2010.
Weitere Informationen über die cynapspro Endpoint Data Protection 2010 finden Sie unter http://cynapspro.com/DE/
CryptionPro HDD Flyer deutsch

Mit CryptionPro HDD® erhalten Sie einen umfassenden Schutz für Ihre mobilen Rechner. Nicht autorisierter Zugriff auf das Notebook und somit auf die gespeicherten Daten oder gar der Zugang zum Firmennetzwerk über das Notebook werden verhindert. Gelangt das Notebook in unerwünschte Hände, sind die Daten selbst bei einem Ausbau der Festplatte geschützt. CryptionPro HDD® stellt über einen erweiterten Zugangsschutz (Pre-Boot Authentisierung) und Festplattenverschlüsselung (soft- und hardware-basiert) den perfekten Schutz für alle mobil gespeicherten Daten sicher.
DevicePro Flyer deutsch

DevicePro® kontrolliert den Datentransfer auf und von allen externen Speichermedien, über Ports, WiFi oder CD/DVD!
CryptionPro HDD Flyer deutsch

Cryptionpro HDD schützt Ihre vertraulichen Daten durch Festplattenverschlüsselung.
PowerPro Flyer deutsch

Verwalten Sie zentralgesteuert die Energieverwaltung Ihrer Unternehmensrechner und senken somit Energieverbrauch, CO2 Ausstoß und Energiekosten in Ihrem Firmennetzwerk.
ErasePro Flyer deutsch

Ermöglichen Sie Ihren Mitarbeiter, Daten unkompliziert aber sicher zu vernichten. Löschen Sie Dateien, Ordner oder Partitionen mit einem Mausklick per DOD, DOD II, BSI Standard (VSITR), oder Peter Gutmann Methode direkt über Ihrem Kontextmenü (z.B. im Windows-Explorer).
ApplicationPro Flyer deutsch

Verwalten Sie mit der Anwendungskontrolle 'ApplicationPro' zentralgesteuert per Black- oder Whitlistverfahren, welche Mitarbeiter bestimmte Programme erlaubt oder gesperrt bekommen.
Weitere Informationen erhalten Sie unter http://cynapspro.com
Screenshots von DevicePro 2009

Screenshots der Device Management Lösung DevicePro 2009 des Herstellers cynapspro.
Weitere Informationen über die cynapspro Endpoint Data Protection 2010 finden Sie unter http://cynapspro.com/DE/
Screenshots von DevicePro 2009

Screenshots der Device Management Lösung DevicePro 2009 des Herstellers cynapspro.
Weitere Informationen über die cynapspro Endpoint Data Protection 2010 finden Sie unter http://cynapspro.com/DE/
DevicePro Ultimate 2009 - Efficient Data Loss Prevention Solution

DevicePro 2009
intuitive device management in real-time
no AD group policies or schema extensions required!
CryptionPro 2009
individual encryption of external mass storage media on a file by file basis
CryptionPro 2009 HDD
soft- and hardware based hard disc encryption with pre-boot-authentication (UserID with password, token or SmartCard)
ApplicationPro 2009
protects your clients through white list based application control
You will find further informationen here: http://cynapspro.com/
DevicePro Ultimate 2009 - Die Loesung - Ihre Vorteile - Das Unternehmen

Meist entstehen Datenverluste durch Mitarbeiter unabsichtlich und ohne krimineller Absicht. Mitarbeiter kopieren sich Daten z.B. auf externe Speichermedien, welche nicht ausreichend gegen Datenklau bzw. Datenverlust geschützt sind.
Gegen solche Risiken schützen Device Management Lösungen in Zusammenhang mit Verschlüsselungskomponenten. Somit können Sie den Einsatz von Speichermedien durch Mitarbeiter gezielt kontrollieren. Die Daten von Mitarbeiter, welche externe Datenträger verwenden dürfen, werden automatisch im Hintergrund auf Speichermedien verschlüsselt, so dass Fremde nichts mit den Daten anfangen können. Evtl. empfielt sich hierbei noch ein Monitoring des Datentransfers auf externe Devices. Eine solche Lösung bietet die Software DevicePro Professional 2009.
Weitere Informationen über die cynapspro Endpoint Data Protection 2010 finden Sie unter http://cynapspro.com/DE/
More from cynapspro GmbH (19)
Cynapspro Endpoint Data Protection 2011 - Step By Step Anleitung DevicePro un...

Cynapspro Endpoint Data Protection 2011 - Step By Step Anleitung DevicePro un...
Cynapspro endpoint data protection 2011 step by-step anleitung device pro und...

Cynapspro endpoint data protection 2011 step by-step anleitung device pro und...
cynapspro endpoint data protection 2010 - technical specifications

cynapspro endpoint data protection 2010 - technical specifications
cynapspro endpoint data protection - installation guide

cynapspro endpoint data protection - installation guide
cynapspro endpoint data protection 2010 - Bedienungsleitfaden

cynapspro endpoint data protection 2010 - Bedienungsleitfaden
Cynapspro data endpoint protection - Anbindung von Drittsysteme

Cynapspro data endpoint protection - Anbindung von Drittsysteme
cynapspro data endpoint protection 2010 - Installationsleitfaden

cynapspro data endpoint protection 2010 - Installationsleitfaden
DevicePro Ultimate 2009 - Efficient Data Loss Prevention Solution

DevicePro Ultimate 2009 - Efficient Data Loss Prevention Solution
DevicePro Ultimate 2009 - Die Loesung - Ihre Vorteile - Das Unternehmen

DevicePro Ultimate 2009 - Die Loesung - Ihre Vorteile - Das Unternehmen
Recently uploaded
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

ここ3000字までしか入らないけどタイトルの方がたくさん文字入ると思います。
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI

Enchancing adoption of Open Source Libraries. A case study on Albumentations.AIVladimir Iglovikov, Ph.D.
Presented by Vladimir Iglovikov:
- https://www.linkedin.com/in/iglovikov/
- https://x.com/viglovikov
- https://www.instagram.com/ternaus/
This presentation delves into the journey of Albumentations.ai, a highly successful open-source library for data augmentation.
Created out of a necessity for superior performance in Kaggle competitions, Albumentations has grown to become a widely used tool among data scientists and machine learning practitioners.
This case study covers various aspects, including:
People: The contributors and community that have supported Albumentations.
Metrics: The success indicators such as downloads, daily active users, GitHub stars, and financial contributions.
Challenges: The hurdles in monetizing open-source projects and measuring user engagement.
Development Practices: Best practices for creating, maintaining, and scaling open-source libraries, including code hygiene, CI/CD, and fast iteration.
Community Building: Strategies for making adoption easy, iterating quickly, and fostering a vibrant, engaged community.
Marketing: Both online and offline marketing tactics, focusing on real, impactful interactions and collaborations.
Mental Health: Maintaining balance and not feeling pressured by user demands.
Key insights include the importance of automation, making the adoption process seamless, and leveraging offline interactions for marketing. The presentation also emphasizes the need for continuous small improvements and building a friendly, inclusive community that contributes to the project's growth.
Vladimir Iglovikov brings his extensive experience as a Kaggle Grandmaster, ex-Staff ML Engineer at Lyft, sharing valuable lessons and practical advice for anyone looking to enhance the adoption of their open-source projects.
Explore more about Albumentations and join the community at:
GitHub: https://github.com/albumentations-team/albumentations
Website: https://albumentations.ai/
LinkedIn: https://www.linkedin.com/company/100504475
Twitter: https://x.com/albumentationsGraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
Mind map of terminologies used in context of Generative AI

Mind map of common terms used in context of Generative AI.
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Recently uploaded (20)
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...

みなさんこんにちはこれ何文字まで入るの?40文字以下不可とか本当に意味わからないけどこれ限界文字数書いてないからマジでやばい文字数いけるんじゃないの?えこ...
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI

Enchancing adoption of Open Source Libraries. A case study on Albumentations.AI
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
Mind map of terminologies used in context of Generative AI

Mind map of terminologies used in context of Generative AI
Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx

Secstrike : Reverse Engineering & Pwnable tools for CTF.pptx
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
ApplicationPro Flyer English
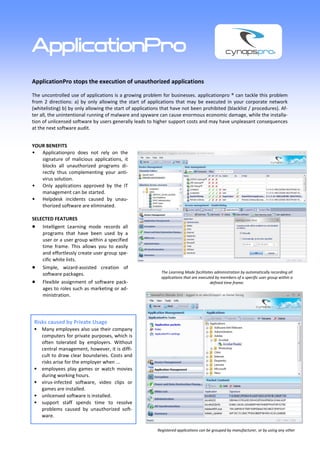
- 1. ApplicationPro ApplicationPro stops the execution of unauthorized applications The uncontrolled use of applications is a growing problem for businesses. applicationpro ® can tackle this problem from 2 directions: a) by only allowing the start of applications that may be executed in your corporate network (whitelisting) b) by only allowing the start of applications that have not been prohibited (blacklist / procedures). Af- ter all, the unintentional running of malware and spyware can cause enormous economic damage, while the installa- tion of unlicensed software by users generally leads to higher support costs and may have unpleasant consequences at the next software audit. YOUR BENEFITS Applicationpro does not rely on the signature of malicious applications, it blocks all unauthorized programs di- rectly thus complementing your anti- virus solution. Only applications approved by the IT management can be started. Helpdesk incidents caused by unau- thorized software are eliminated. SELECTED FEATURES Intelligent Learning mode records all programs that have been used by a user or a user group within a specified time frame. This allows you to easily and effortlessly create user group spe- cific white lists. Simple, wizard-assisted creation of software packages. The Learning Mode facilitates administration by automatically recording all applications that are executed by members of a specific user group within a Flexible assignment of software pack- defined time frame. ages to roles such as marketing or ad- ministration. Risks caused by Private Usage Many employees also use their company computers for private purposes, which is often tolerated by employers. Without central management, however, it is diffi- cult to draw clear boundaries. Costs and risks arise for the employer when ... employees play games or watch movies during working hours. virus-infected software, video clips or games are installed. unlicensed software is installed. support staff spends time to resolve problems caused by unauthorized soft- ware. Registered applications can be grouped by manufacturer, or by using any other
- 2. cynapspro Endpoint Data Protection cynapspro develops software solutions for reliable endpoint data protection in the enterprise network and covers the following areas: DevicePro prevents data loss through open ports and external storage devices. CryptionPro encrypts and protects your company data on mobile storage media – fully automated. CryptionPro HDD protects your company data by en- crypting the hard drive. ApplicationPro blocks unwanted applications and prevents the use of unlicensed software. ErasePro ensures that deleted files are not recover- able. PowerPro cuts energy costs and reports suspicious activity. The following features distinguish all cynapspro pected data abuse or loss, cynapspro knows which solutions: files have been accessed, by whom and when. Intuitive Management Console Minimal System Requirements The single user-friendly Management Console is Apart from a SQL database (the free MSDE or SQL largely self-explanatory and only a minimum of train- Server 2005 Express edition are fully sufficient), there ing is required. The clear and concise structure allows is no additional software required, such as the IIS the compilation of complex setting with just a few Server or .NET client. Consequently, no new vulner- mouse clicks. abilities are introduced by installing additional back office software and memory and CPU utilization is Real-Time Management minimal. All changes to access permissions will be immediately pushed out to the clients and stored in the cynapspro Secure Kernel Driver Technology database. Users don’t need to restart their machines The secure cynapspro® kernel driver technology is or even connect to the company network in order to loaded into the operating system during the boot upgrade their usage rights. sequence and thus ensures that the service running on the client is not visible to the end user. It can only Rights Management at Group Level, User Level or be stopped or uninstalled by an authorized Adminis- Computer Level trator. Reduce your administrative effort. Manage individual access rights directly with the respective users, Integration with Third Party Applications groups or computers. An XML interface allows the allocation of access per- missions from an existing customer Helpdesk or Ser- Synchronization of User Directories vice Desk implementation in a fully automated way, Existing users and user group definitions from Micro- leveraging existing processes, approval workflows, soft Active Directory or Novell eDirectory are im- notifications and management reports. There will be ported by the cynapspro server thus reducing the no need for service desk workers to use an additional workload for defining user groups for Access Client console. Lists (ACLs) as well as the sources of error. Distributed Environments Full Audit Log Several mutually replicating cynapspro servers pro- Password-protected, detailed access statistics with vide load balancing capabilities in enterprise environ- filter and sort order functionality. In case of sus- ments. Free Trial Version Contact On the cynapspro website, we offer a full version cynapspro GmbH of our software for download, including a free 5- Am Hardtwald 1 user license. D-76275 Ettlingen Please contact us if you are interested in testing Tel.: +49 7243 / 945-250 our software in a larger environment. Email: contact@cynapspro.com Internet: www.cynapspro.com March 2010 - Copyright cynapspro GmbH 2010—All rights reserved.
