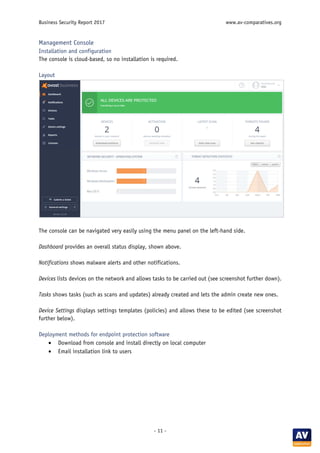
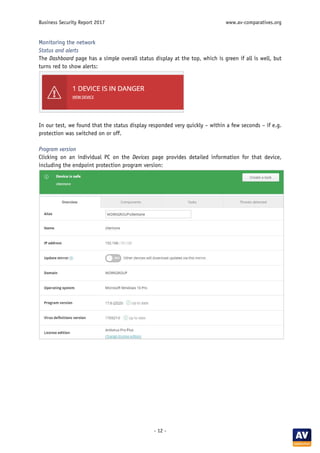
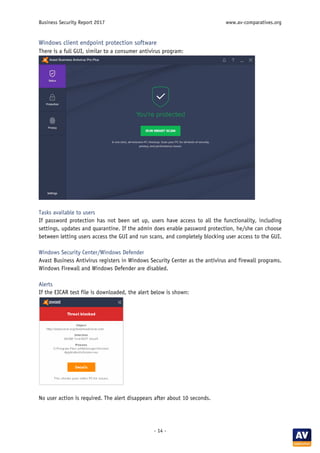
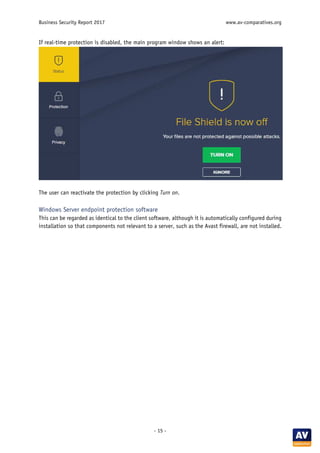
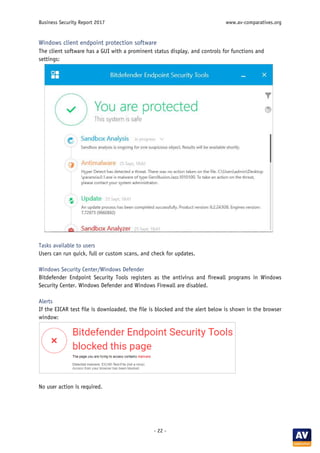
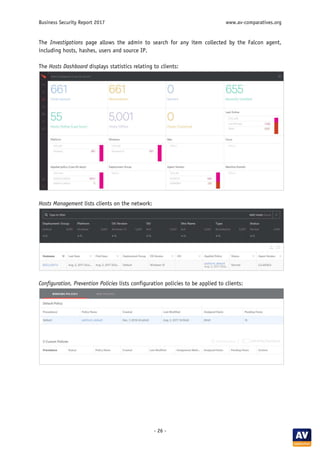
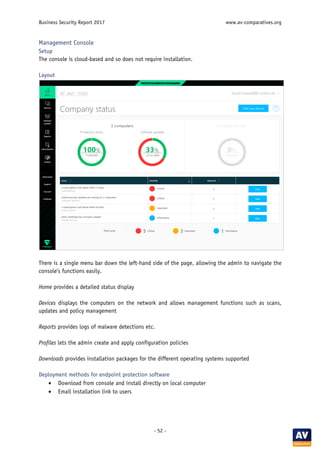
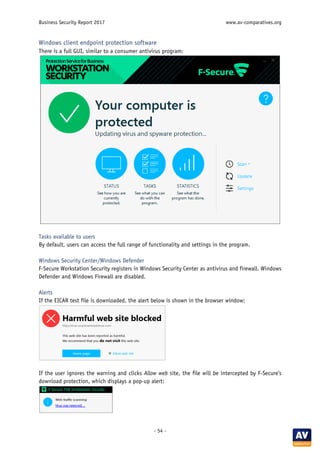
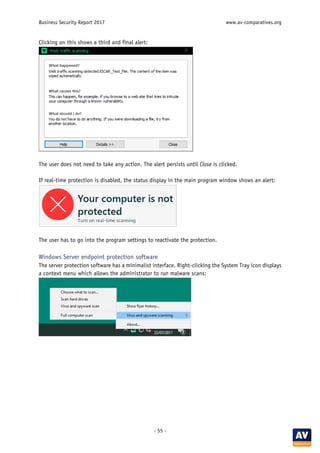
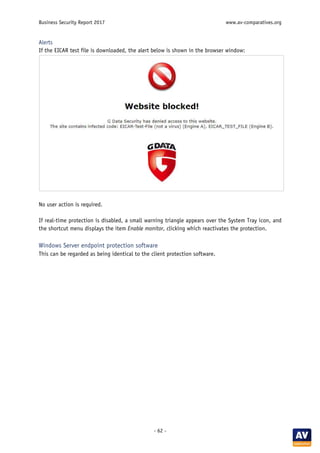
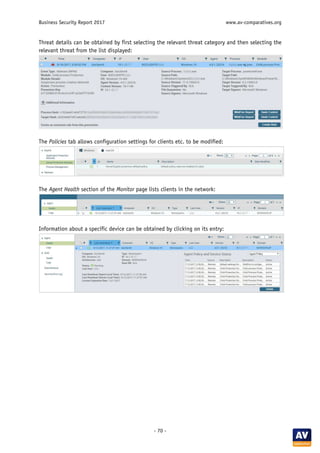
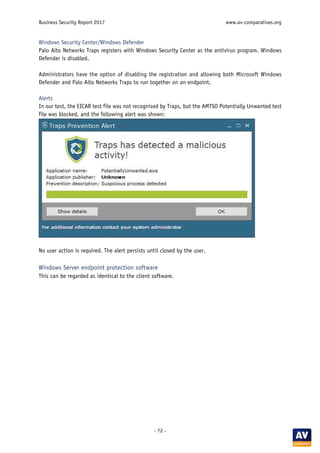
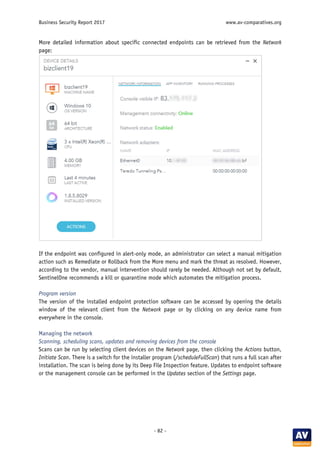
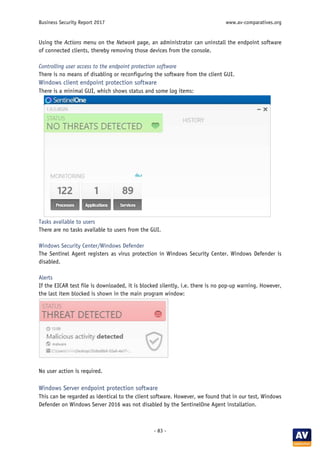
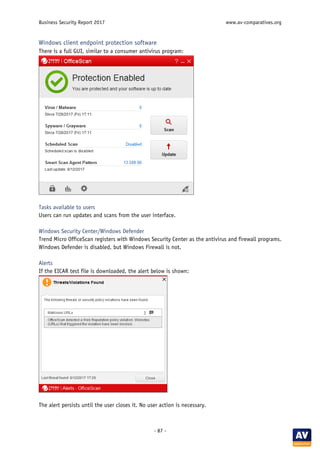
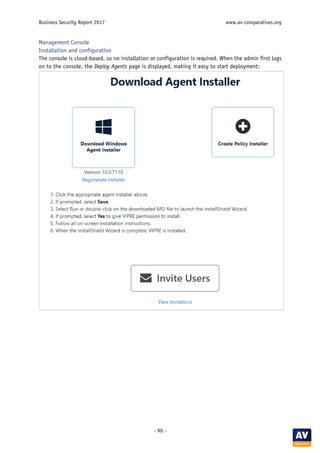
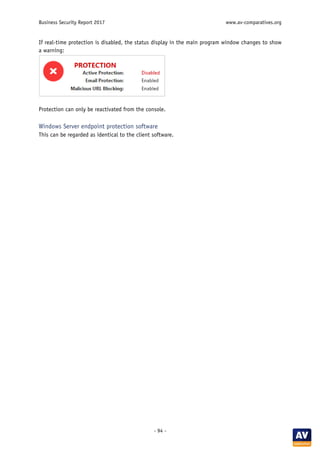
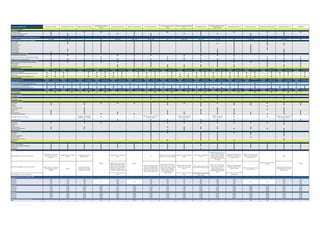
The 2017 Business Security Report by AV-Comparatives evaluates various managed security products designed for Microsoft Windows networks, covering their installation, deployment, and user interfaces. The report highlights the features of each product and ranks them based on their effectiveness in malware protection, with all reviewed products achieving high standards and receiving the Approved Business Product Award. The review also discusses management consoles, deployment methods, and the suitability of products for different business sizes and IT capabilities.