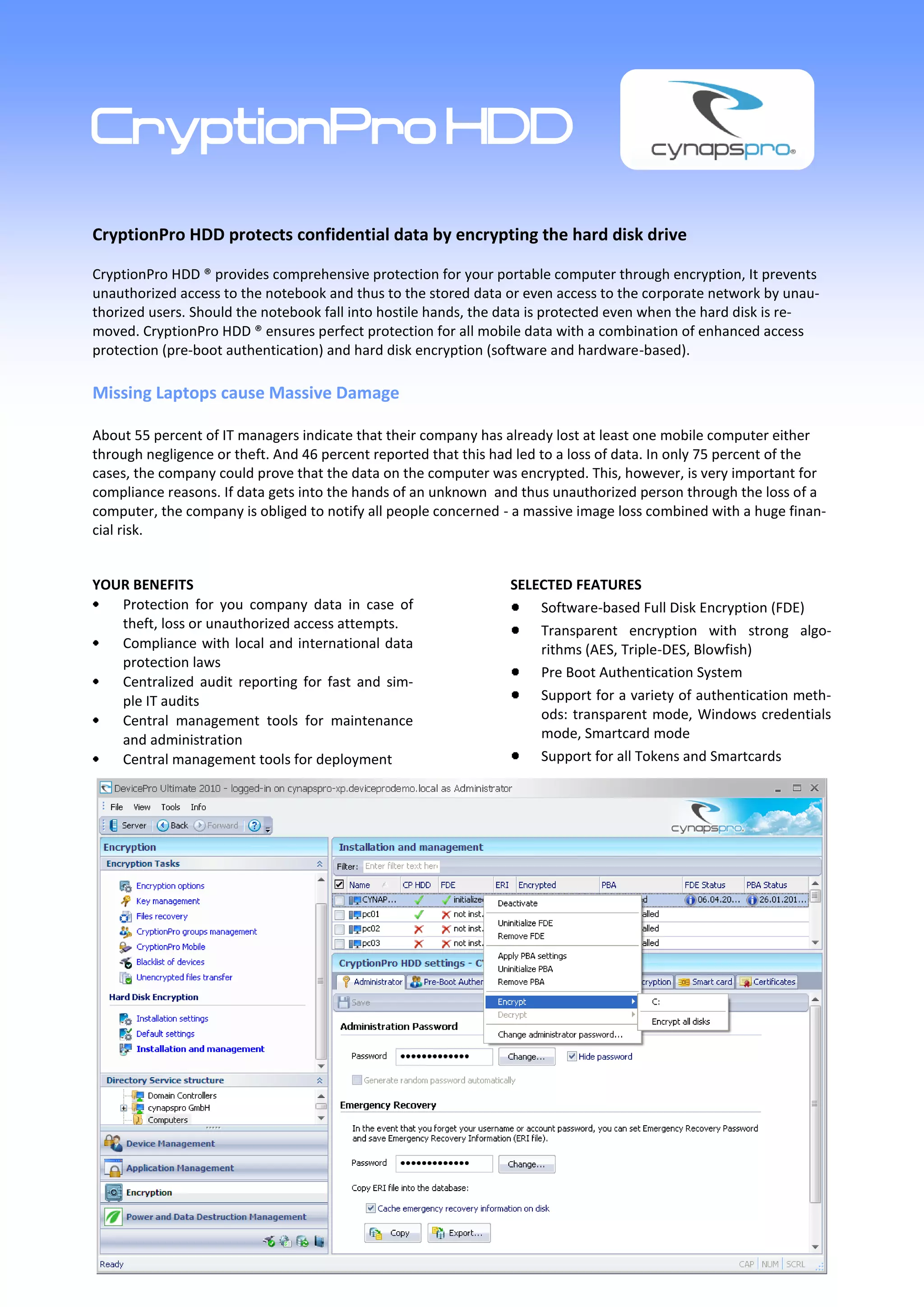
CryptionPro HDD provides encryption for hard drives to protect confidential data from unauthorized access, particularly in cases of theft or loss. The software features pre-boot authentication, compliance with data protection laws, and a user-friendly management console for centralized control. CynapsPro also offers additional solutions for endpoint data protection, including device control, application blocking, and file deletion assurance.